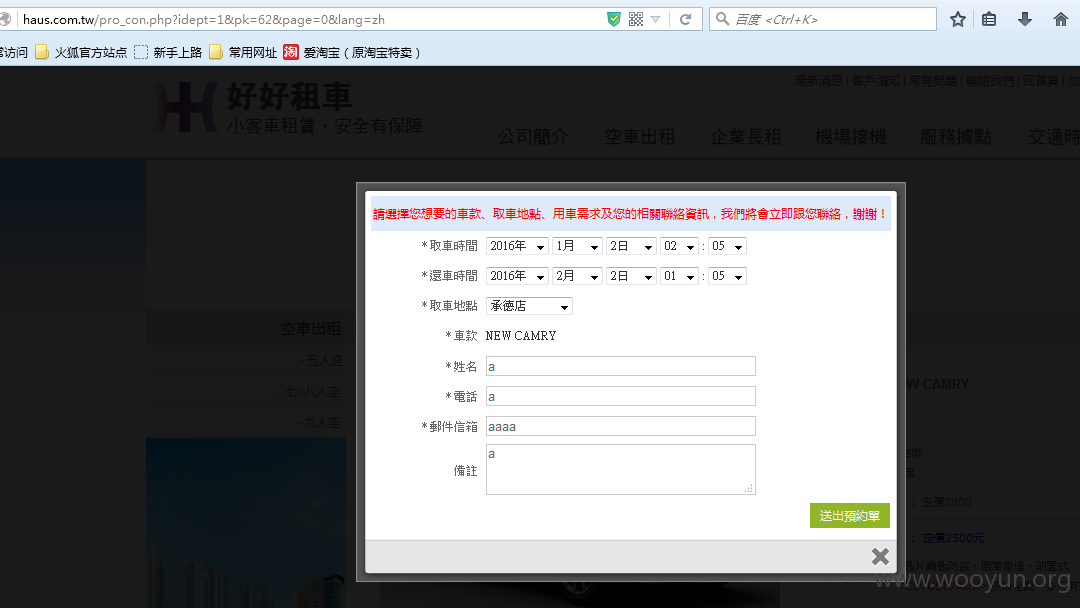
http://**.**.**.**/pro_con.php?idept=1&pk=62&page=0&lang=zh
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2015-11-30 11:41
厂商回复:
感謝通報
最新状态:
2016-01-12:HITCON 於接獲通報後除 email 該網站所示之服務信箱外,亦曾致電該網站負責人告知此漏洞,但對方至漏洞公開時仍無回應。
2016-02-20:HITCON 於接獲通報後除 email 該網站所示之服務信箱外,亦曾致電該網站負責人告知此漏洞,但對方至漏洞公開時仍無回應。