漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0150606
漏洞标题:华数某站SQL注入涉及21裤(已shell可进行域渗透)
相关厂商:华数数字电视传媒集团有限公司
漏洞作者: mango
提交时间:2015-10-30 14:04
修复时间:2015-12-14 18:00
公开时间:2015-12-14 18:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-30: 细节已通知厂商并且等待厂商处理中
2015-10-30: 厂商已经确认,细节仅向厂商公开
2015-11-09: 细节向核心白帽子及相关领域专家公开
2015-11-19: 细节向普通白帽子公开
2015-11-29: 细节向实习白帽子公开
2015-12-14: 细节向公众公开
简要描述:
~~~~
详细说明:
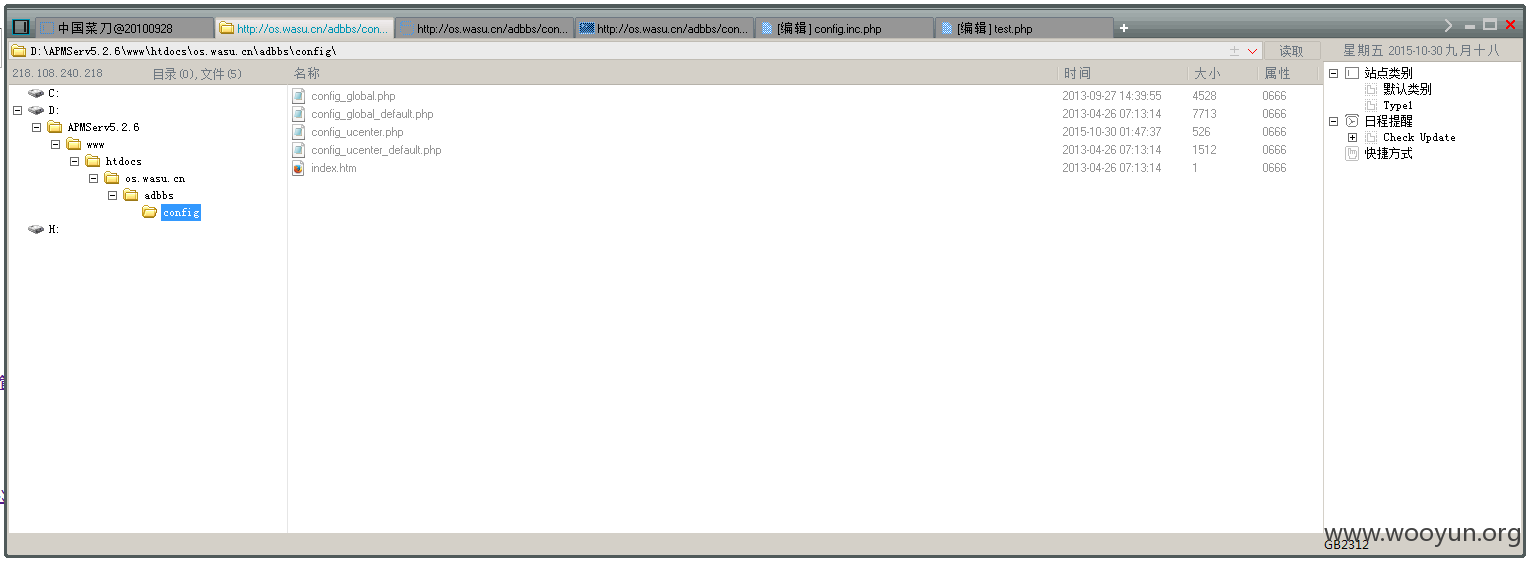
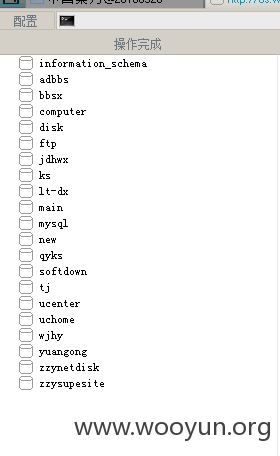
漏洞证明:
进行抓密码~~~
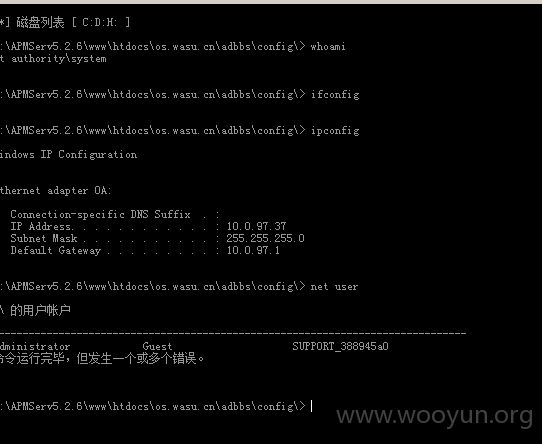
在域内(可能是域管)~~~开下代理应该能进行域渗透~
修复方案:
~~彻底审查SQL注入~
版权声明:转载请注明来源 mango@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:7
确认时间:2015-10-30 17:58
厂商回复:
正在处理
最新状态:
暂无



![N~(9V41CE_0]Y5K~5$$K7B8.png](http://wimg.zone.ci/upload/201510/3013295226f1c9085035606db46159f003b282c7.png)
![W}4MXXC_BM1QH]`~BCCI[4J.png](http://wimg.zone.ci/upload/201510/30133055c43c1435d8de9eefd14d66aae73a31cf.png)