北京江伟时代科技有限公司开发的地址灾害监测系统web端存在通用sql注入漏洞和任意上传
**.**.**.**:8080/login.jsp 此处有注入,登陆抓包即可
**.**.**.**:8088/ 这个端口也有注入,但是有验证码,白天跑不出来,但是晚上可以跑出来,估计是晚上数据通信比较少吧
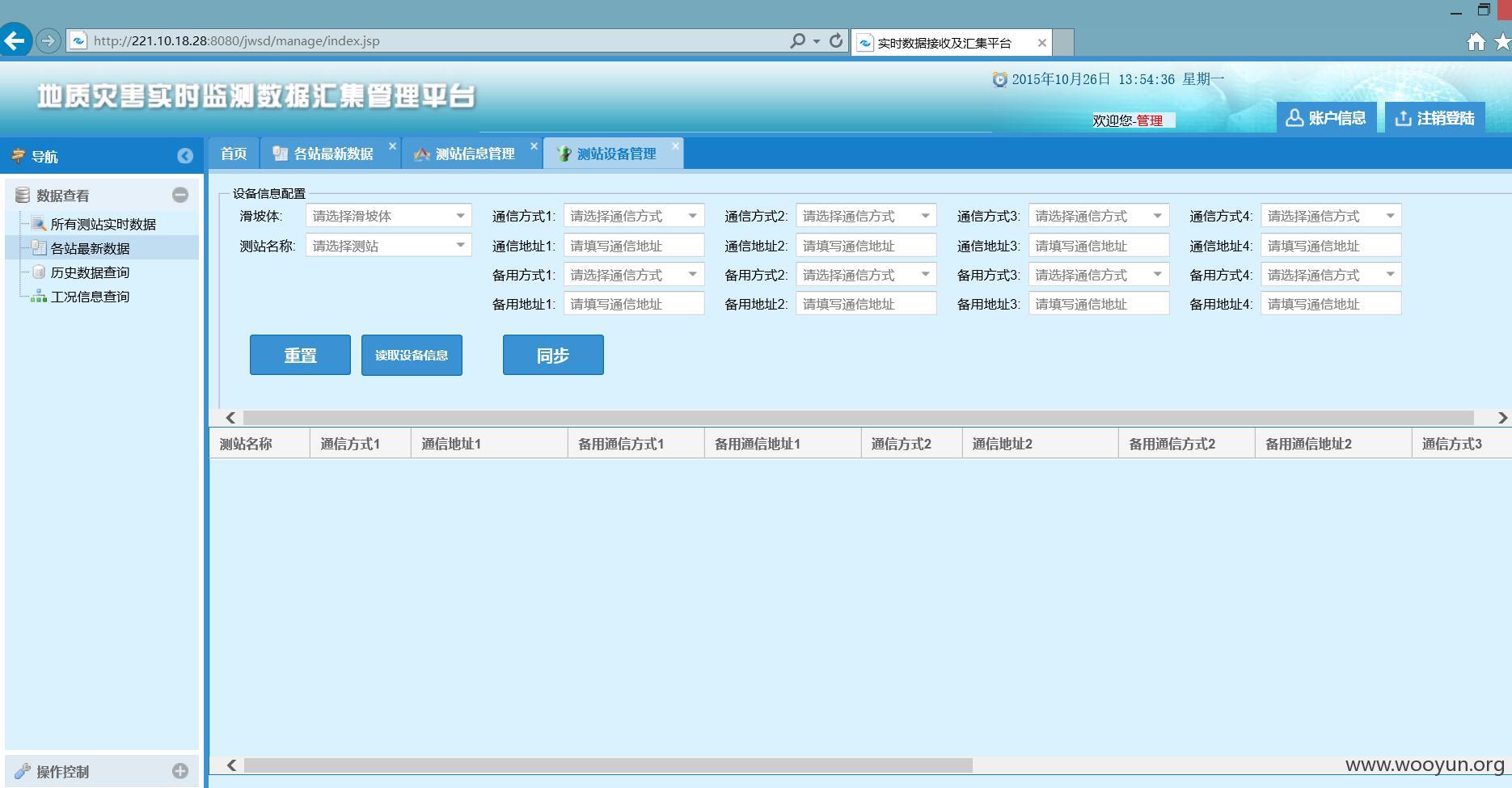
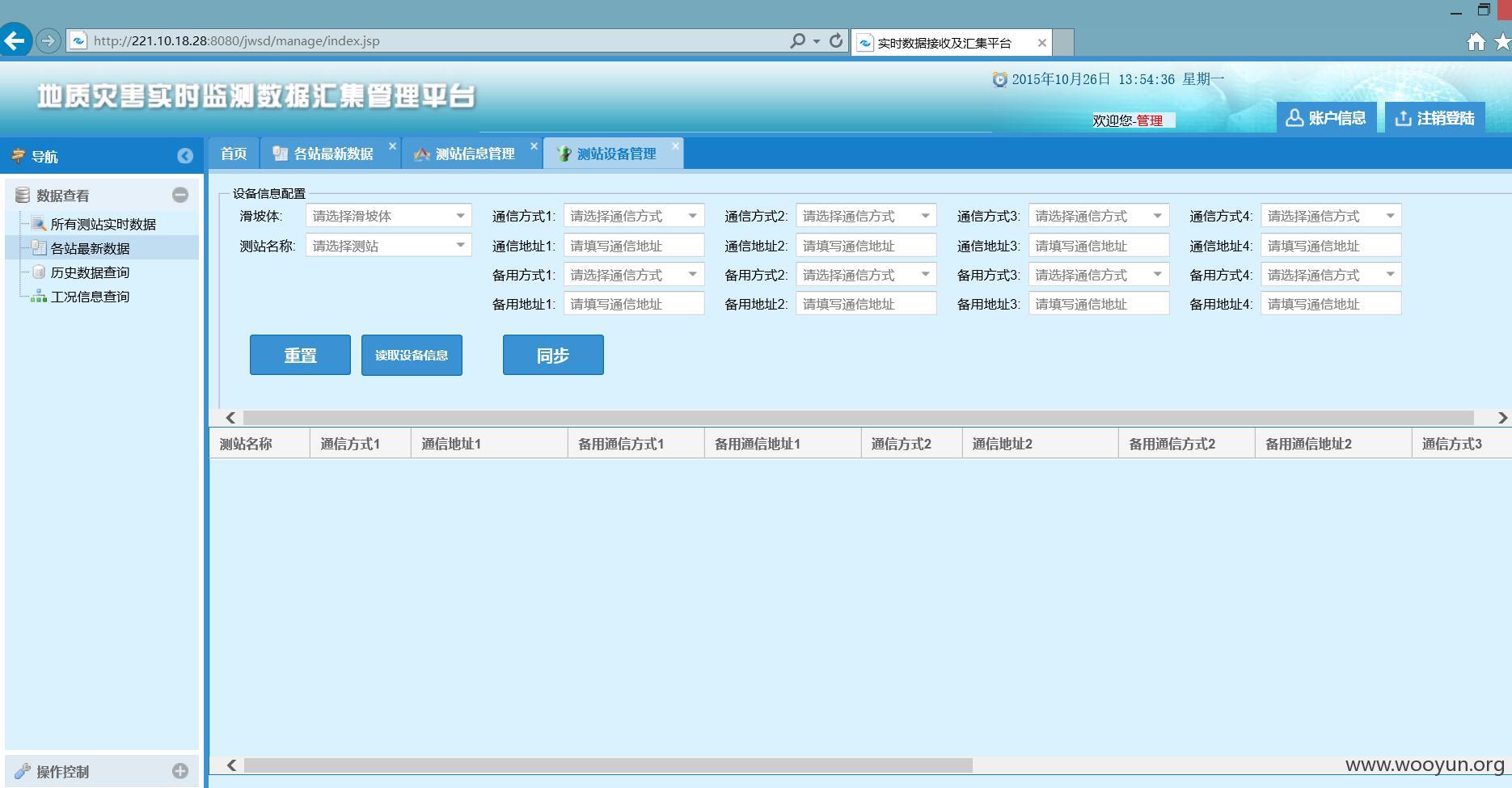
登录后台看看

可以注出数据,但是表太多,有时候不知道哪个表是存用户名的表
到其公司官网看一下,发现有很多地质局都是用的这套系统,但是一般这套系统是没有域名的,只能通过特殊方法搜索

下面搜了一些
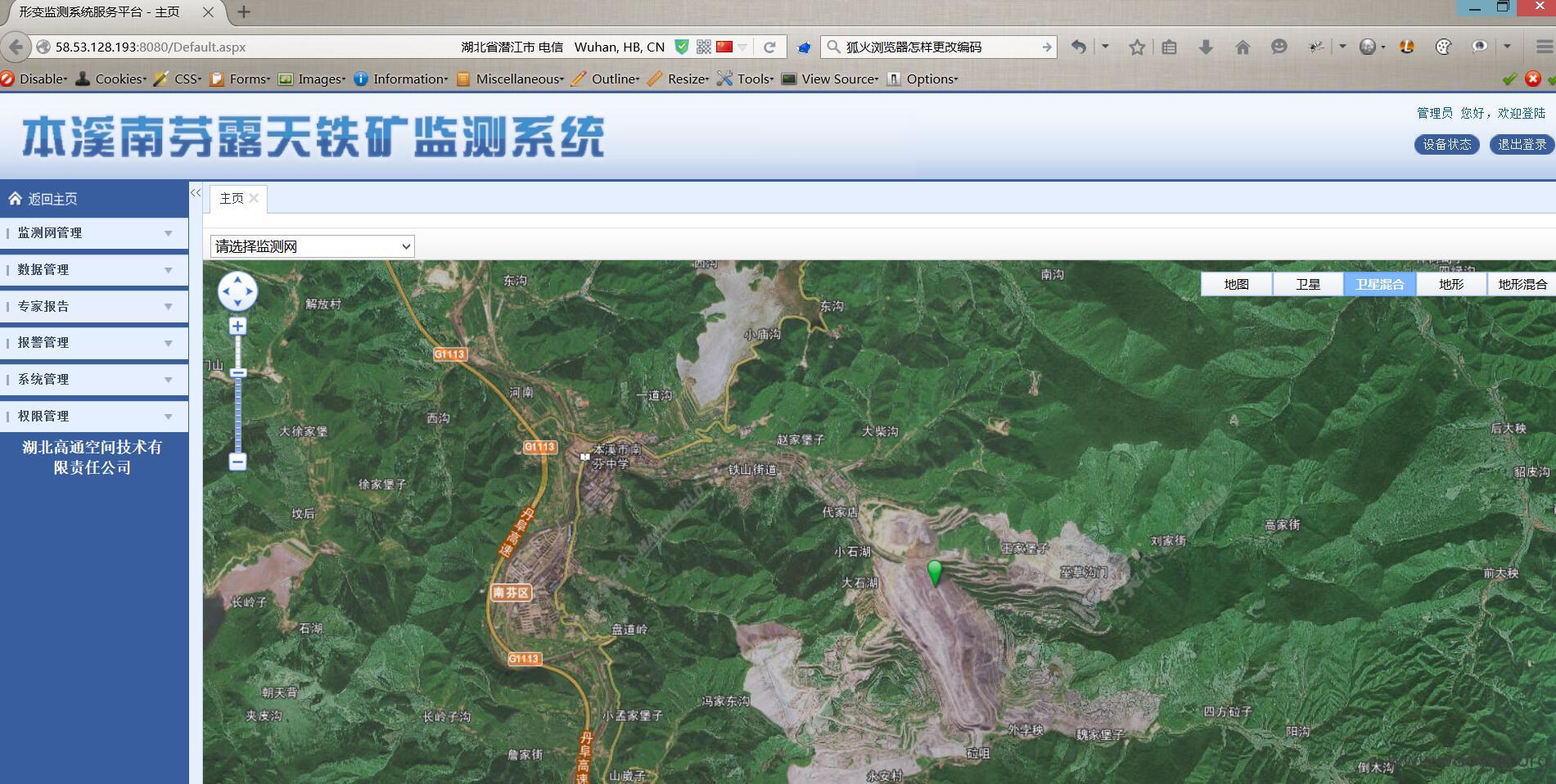
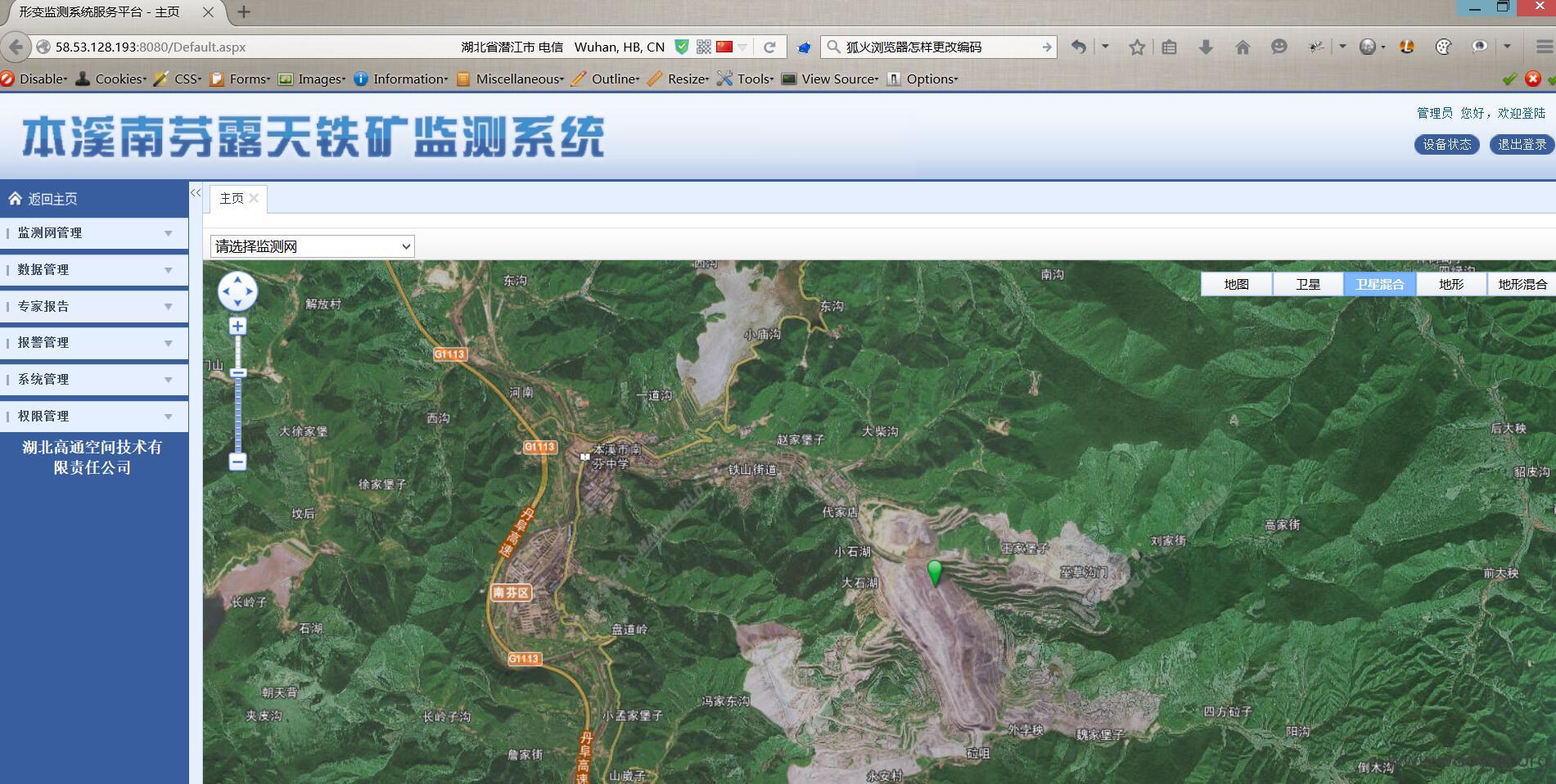
**.**.**.**:8080/Default.aspx
**.**.**.**:81
**.**.**.**:8080/login.aspx
**.**.**.**:8090/login.jsp
**.**.**.**:8090/jwsd/manage/index.jsp
**.**.**.**:8090/login.jsp
**.**.**.**:8080/login.jsp
**.**.**.**:8081/login.jsp 这个版本用的比较新,但是仍然有注入
**.**.**.**:8081/login.jsp
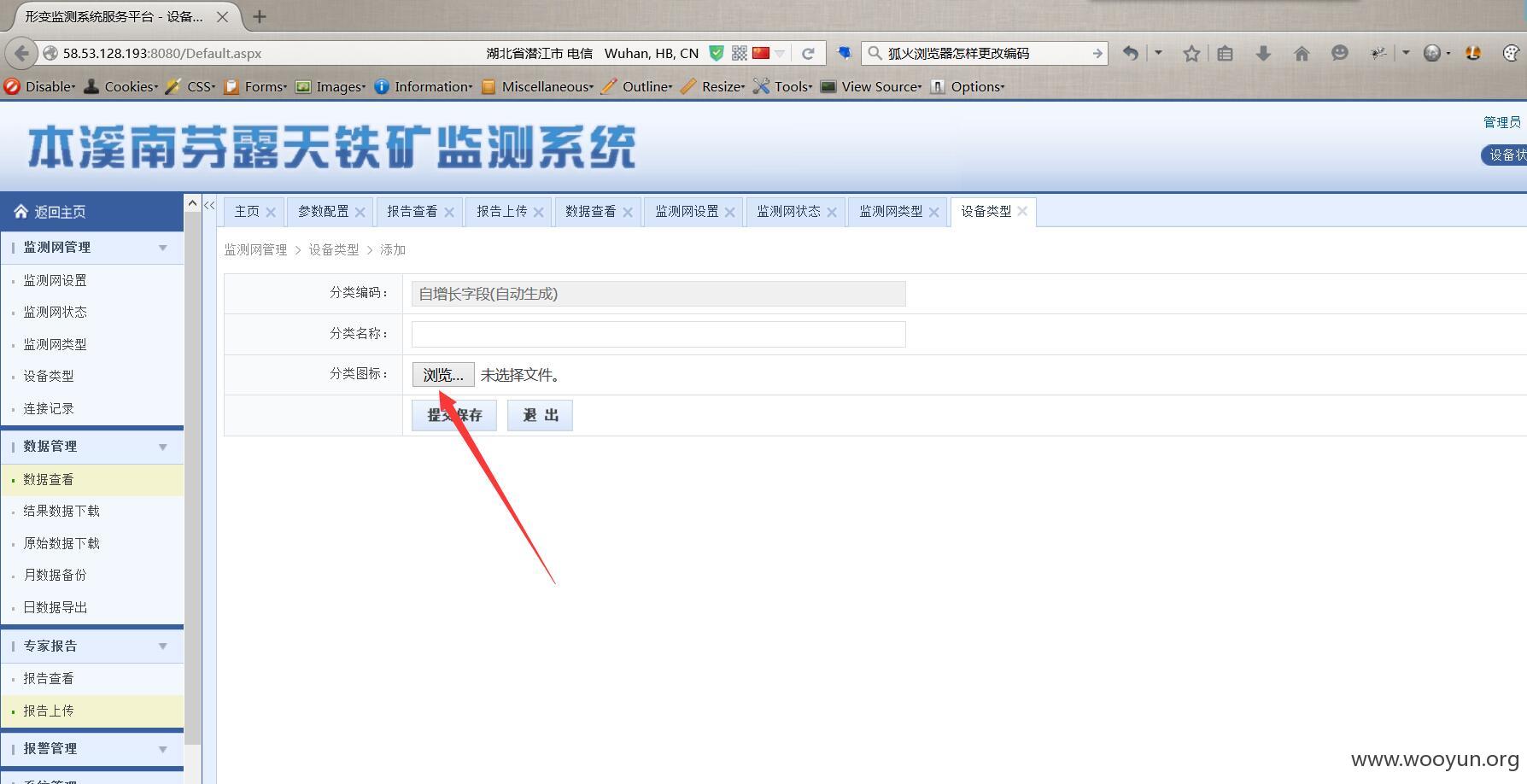
其中一个登录进去了,验证一下上传
**.**.**.**:8080/Login.aspx 以这个为例 admin 123456(虽然有些是弱口令吧,但是都有注入)

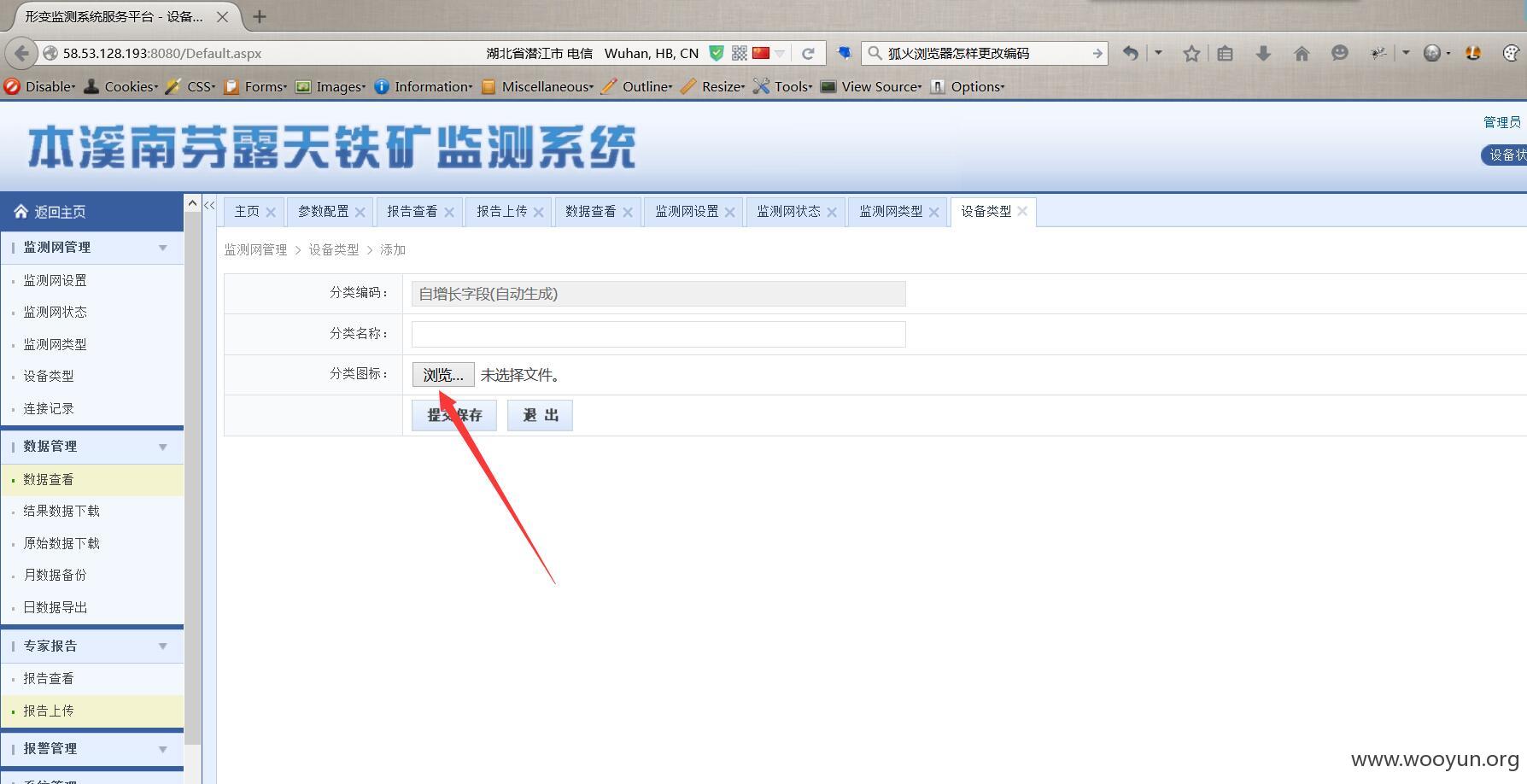
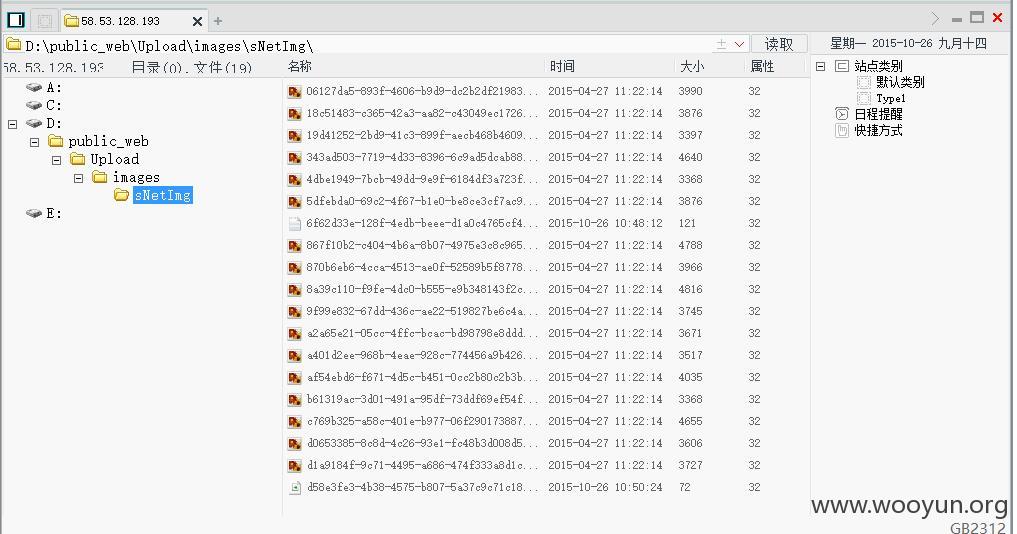
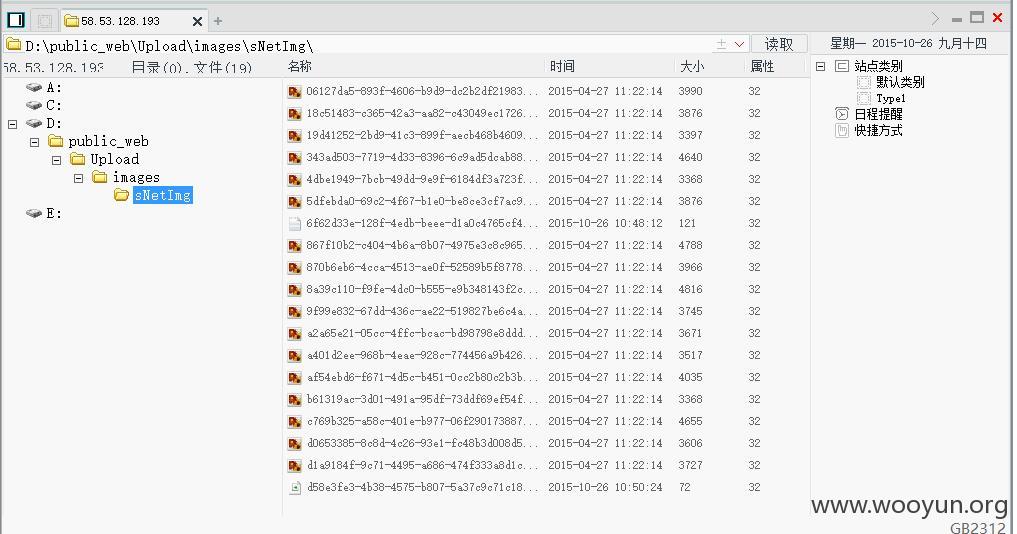
未做任何过滤
getshell证明一下,就不提取权了