RICS(Royal Institution of Chartered Surveyor)-- 英国皇家特许测量师学会,是世界最大的房地产、建筑、测量和环境领域的综合性专业团体,是为全球广泛认可的拥有“物业专才”之称的世界顶级专业性学会。
RICS(皇家特许测量师学会)是一个国际专业人士学会。我们在金砖四国得到全面发展,并得到全球市场和政府部门的一致认可,在全球146个国家拥有超过100,000多名合格会员和80,000多名学生和培训生,我们的办事处遍及全球27个城市.

target url:
http://**.**.**.**/train.php?cur=notice_detail&id=52&from=singlemessage&isappinstalled=0
选择检测的参数是 id
大量会员信息泄露(上万),不晓得里边有没有专业人士RICS,好像很厉害的样子
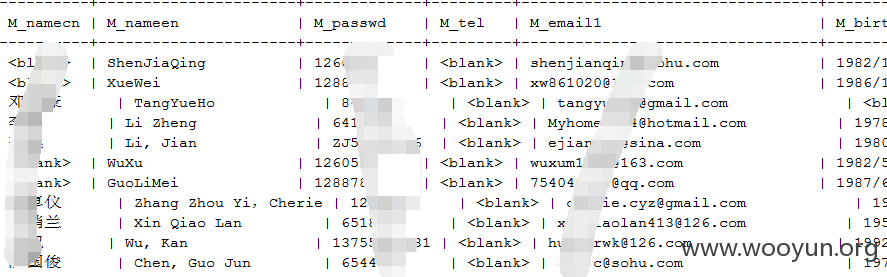
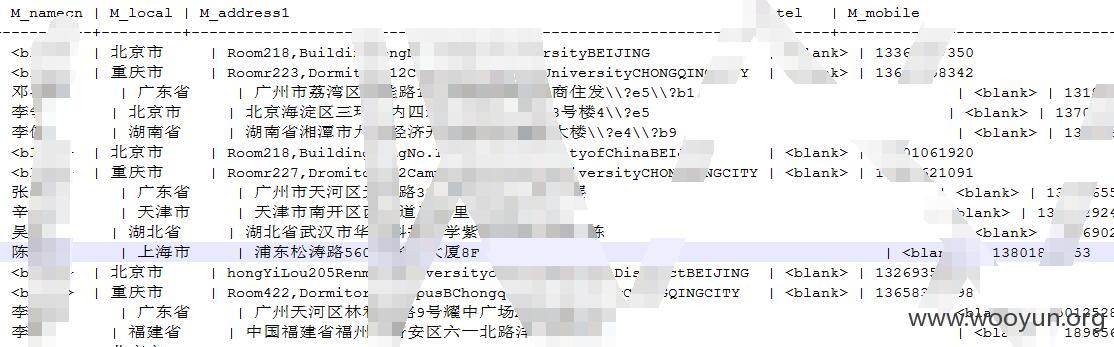
个人信息(账号密码,email电话, 生日住址等等)
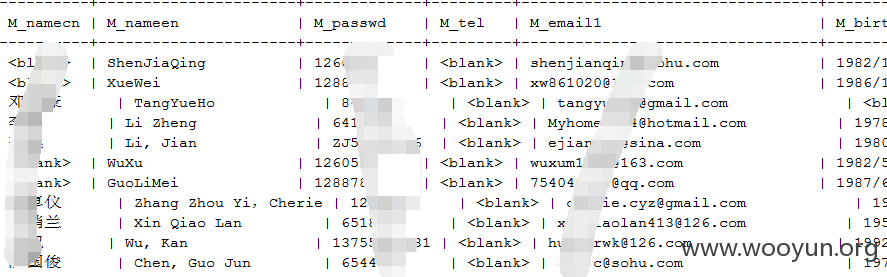
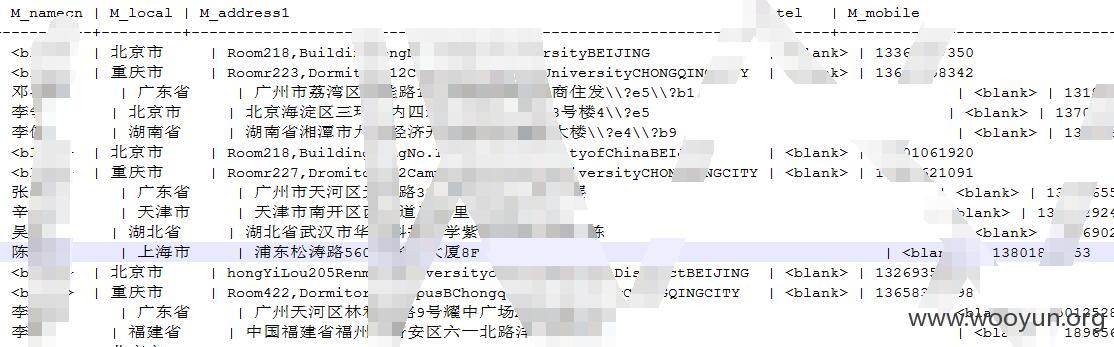
admin _infomation