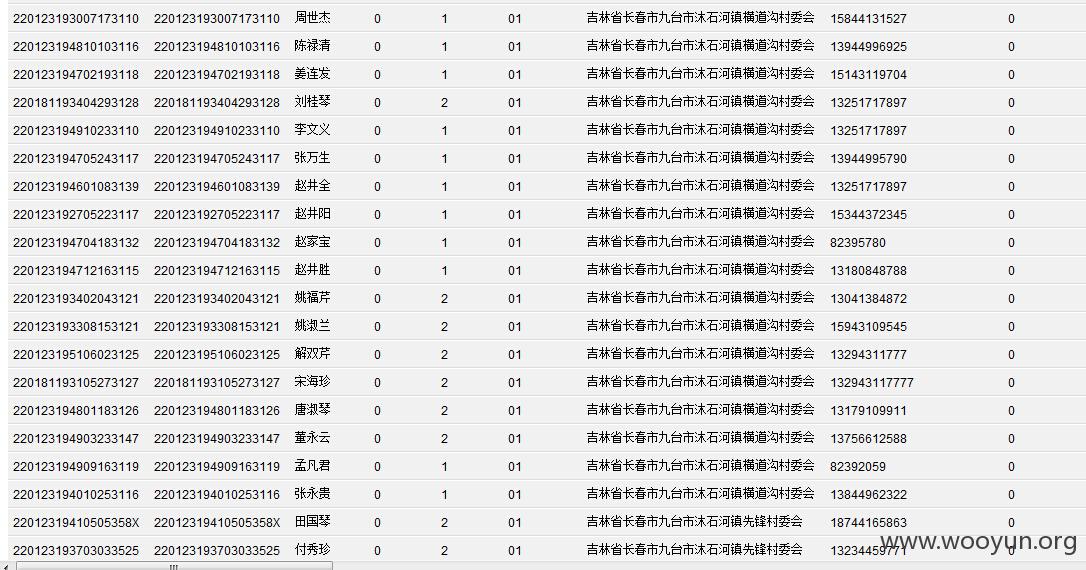
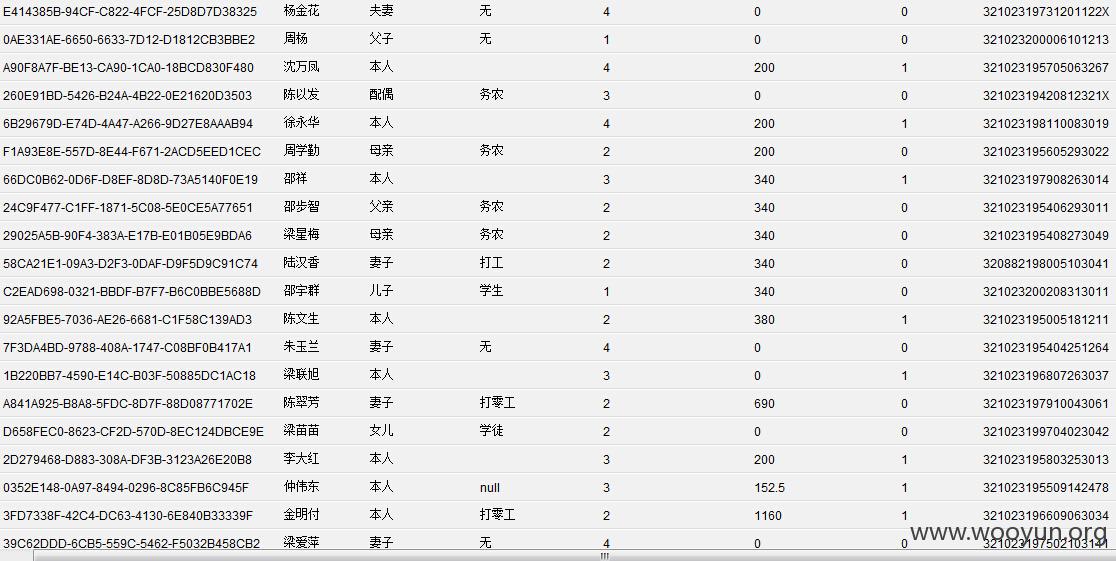
家庭经济状况信息比对系统
**.**.**.**:7001/adp/login_new.jsp
**.**.**.**:7001/console/login/LoginForm.jsp
weblogic/12345678
可以上传一个war格式的马 拿到shell
**.**.**.**:7001/ma/ma3.jsp
E:/java_soft/oracle/Middleware/user_projects/domains/base_domain/config/jdbc/datasourceADP-9272-jdbc.xml
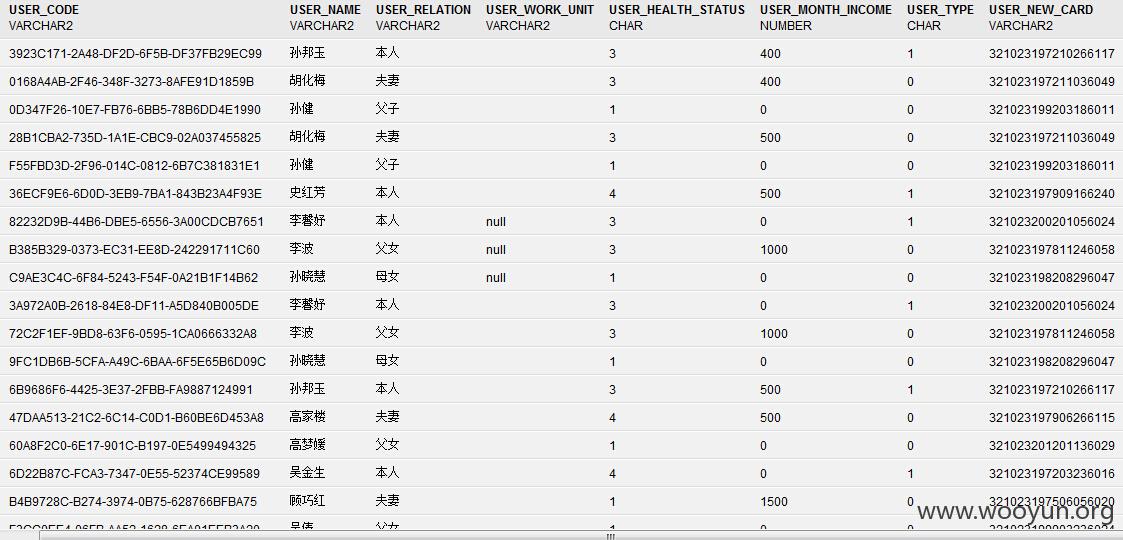
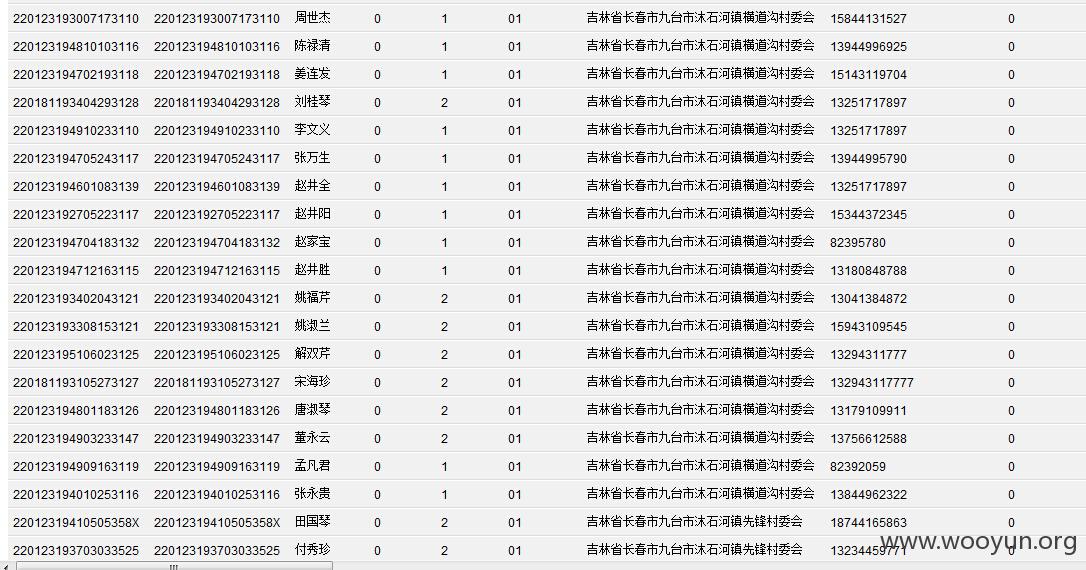
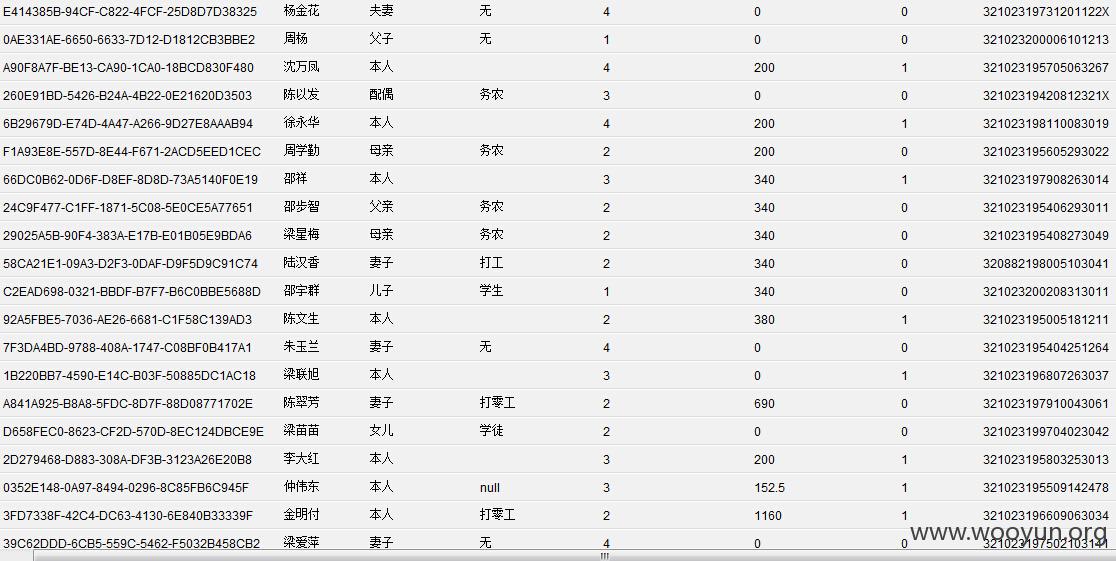
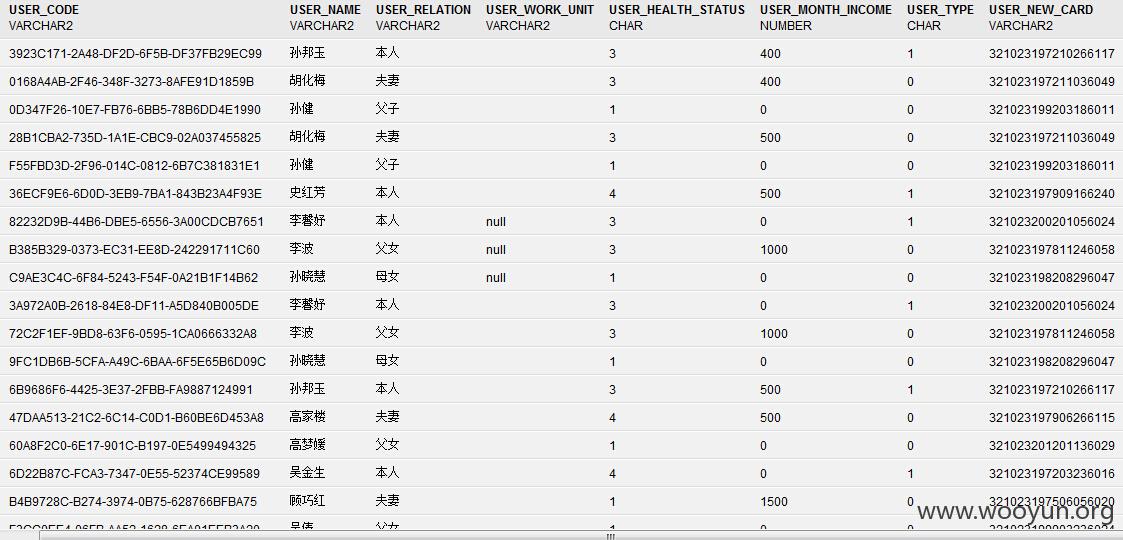
好多用户信息哦~~~