漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0123543
漏洞标题:PHP云人才系统最新版1处SQL注入(union select)
相关厂商:php云人才系统
漏洞作者: 龟兔赛跑
提交时间:2015-06-30 11:05
修复时间:2015-09-28 11:10
公开时间:2015-09-28 11:10
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-30: 细节已通知厂商并且等待厂商处理中
2015-06-30: 厂商已经确认,细节仅向厂商公开
2015-07-03: 细节向第三方安全合作伙伴开放
2015-08-24: 细节向核心白帽子及相关领域专家公开
2015-09-03: 细节向普通白帽子公开
2015-09-13: 细节向实习白帽子公开
2015-09-28: 细节向公众公开
简要描述:
PHP云人才系统最新版1处SQL注入(union select),无需登陆,可取任意数据。
官网demo测试。
详细说明:
最新版全局过滤函数修改:config/db.safety.php
里面把"00000000"直接过滤为了"", 为UNION注入提供了方法。
UNION select写成UNI00000000ON%20sel00000000ect就没问题了,经过gpc2sql后,就又变成了UNION select。 UNI00000000ON%20se00000000lect => gpc2sql => UNION select 剩下的就是绕过safesql()的check,和360的check。
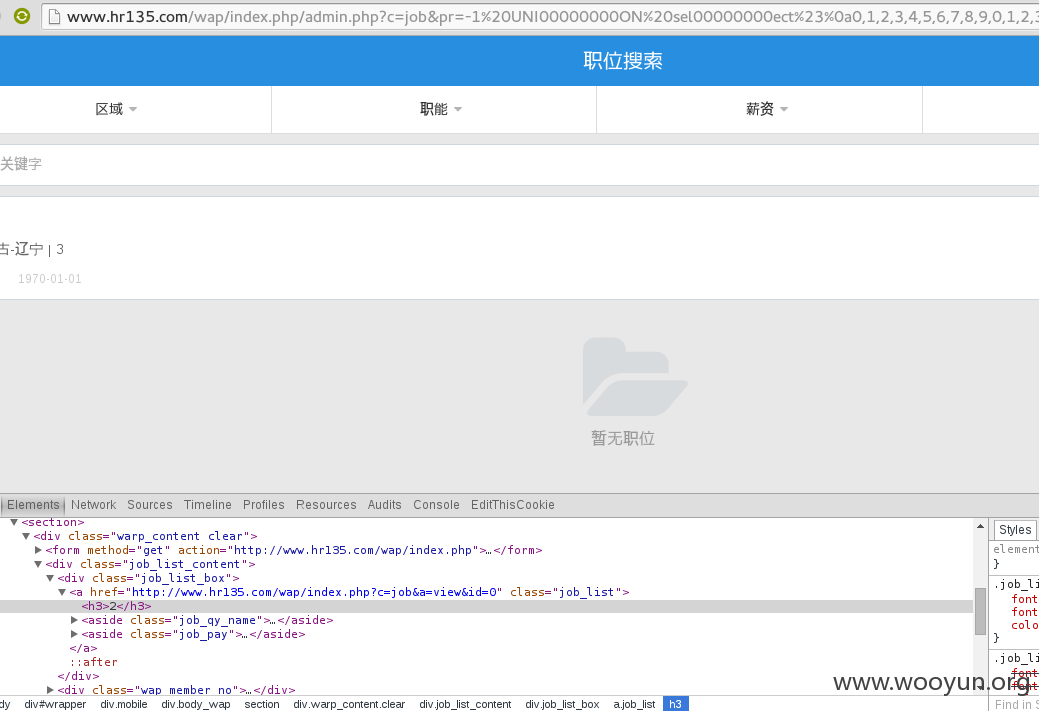
对于safesql,check 'union select'的正则表达式为"UNION.+?SELECT(\\\\(.+\\\\)|\\\\s+?.+?)", 那么用"UNION SELECT%23%0a"就能绕过。 对以360的check则更容易,例如URL为:'wap/index.php', 则访问'wap/index.php/admin.php'即可绕过。 好了,我们先通过一处SQL注入尝试UNION,构造的URL为:
直接出UNION SELECT的数据。
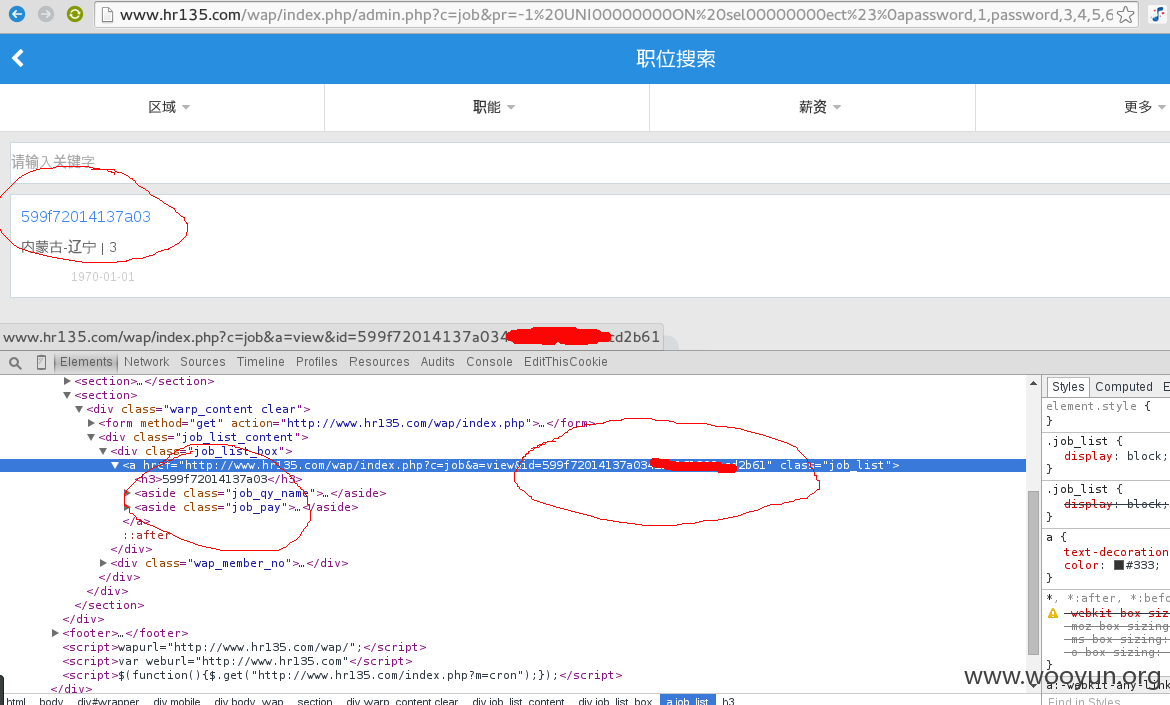
构造URL直接取管理员密码:
漏洞证明:
修复方案:
1.修复SQL注入
2."00000000" => "OOOOOOOO"
版权声明:转载请注明来源 龟兔赛跑@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-06-30 11:08
厂商回复:
感谢提供!
最新状态:
暂无