漏洞概要
关注数(24)
关注此漏洞
漏洞标题:众泰汽车OA系统SQL注入可入内网
提交时间:2015-05-31 12:15
修复时间:2015-07-19 14:22
公开时间:2015-07-19 14:22
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-05-31: 细节已通知厂商并且等待厂商处理中
2015-06-04: 厂商已经确认,细节仅向厂商公开
2015-06-14: 细节向核心白帽子及相关领域专家公开
2015-06-24: 细节向普通白帽子公开
2015-07-04: 细节向实习白帽子公开
2015-07-19: 细节向公众公开
简要描述:
OA系统,里面应该有很多员工信息吧(*^__^*)
详细说明:
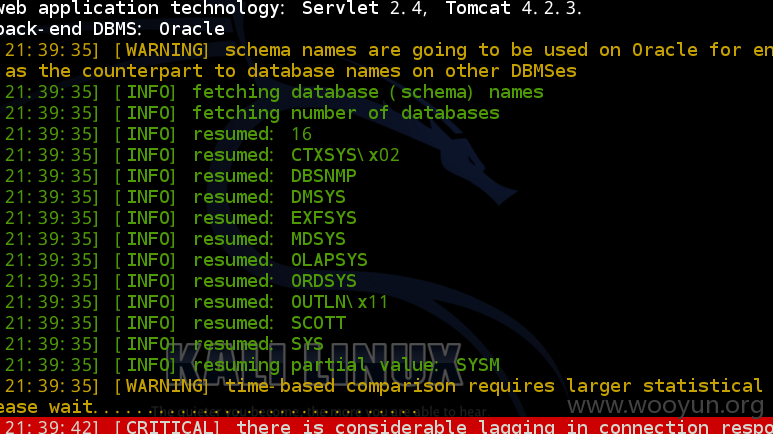
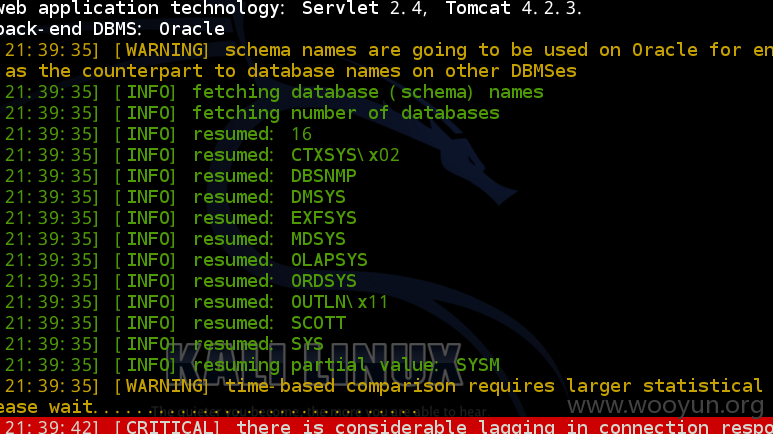
http://oa.zotye.com/main/login.jsp
登录框post注入,post.txt如下:
漏洞证明:
延时注入慢的也是醉了,数据神马的,你们应该更清楚,,
修复方案:
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-06-04 14:21
厂商回复:
感谢白帽子漏洞提交,已提交技术人员进行处理。 确认晚了
最新状态:
暂无