漏洞概要
关注数(24)
关注此漏洞
漏洞标题:蚂蜂窝某接口撞库泄露用户登录凭据(有账号证明)
提交时间:2015-05-07 08:57
修复时间:2015-06-21 10:42
公开时间:2015-06-21 10:42
漏洞类型:设计缺陷/逻辑错误
危害等级:高
自评Rank:18
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-05-07: 细节已通知厂商并且等待厂商处理中
2015-05-07: 厂商已经确认,细节仅向厂商公开
2015-05-17: 细节向核心白帽子及相关领域专家公开
2015-05-27: 细节向普通白帽子公开
2015-06-06: 细节向实习白帽子公开
2015-06-21: 细节向公众公开
简要描述:
撞库扫号攻击已经是Top 10 Security Risks for 2014之一.撞库以大量的用户数据为基础,利用用户相同的注册习惯(相同的用户名和密码),尝试登陆其它的网站。2011年,互联网泄密事件引爆了整个信息安全界,导致传统的用户+密码认证的方式已无法满足现有安全需求。泄露数据包括:天涯:31,758,468条,CSDN:6,428,559条,微博:4,442,915条,人人网:4,445,047条,猫扑:2,644,726条,178:9,072,819条,嘟嘟牛:13,891,418条,7K7K:18,282,404条,共1.2亿条。不管你的网站密码保护的多好,但是面对已经泄露的账号密码,撞库扫号防御还是一个相当重要的环节。
详细说明:
主站登录接口。对登录接口的调用没有进行限制。 其实是有限制的。超过一定次数弹验证码并且会进一步封IP。但是触发条件很高。大概要10000次才会触发验证码???? 登录接口抓包如下:
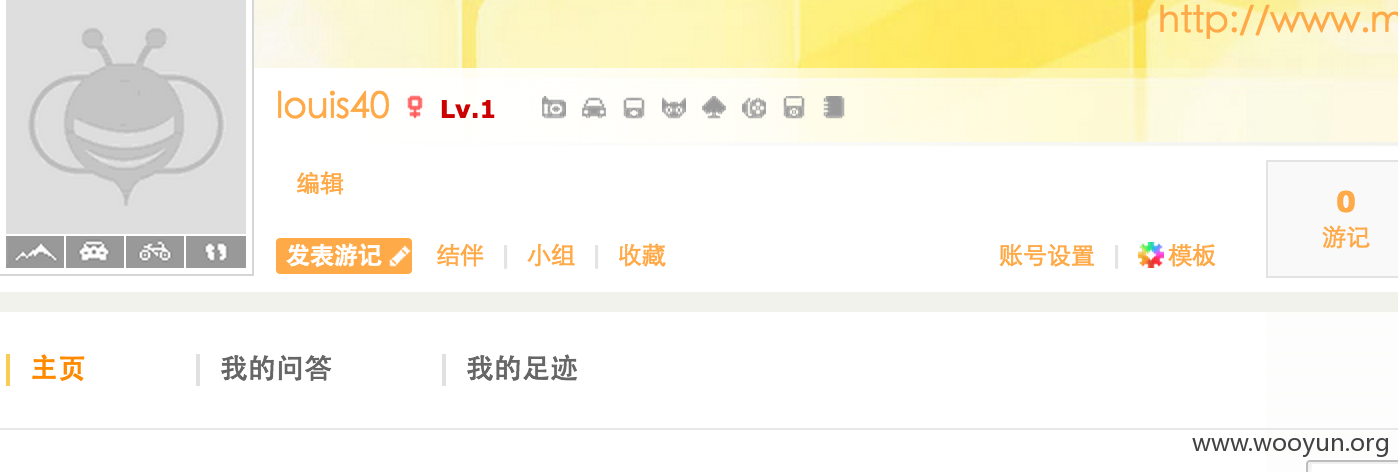
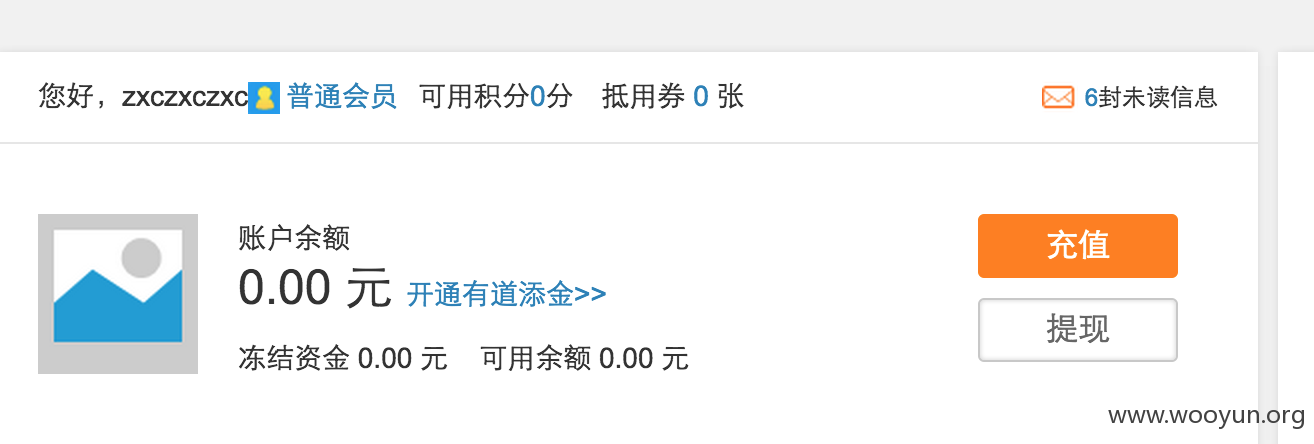
漏洞证明:
修复方案:
撞库防御参考资料:http://stayliv3.github.io/2015/04/15/%E6%92%9E%E5%BA%93%E6%94%BB%E5%87%BB%E9%98%B2%E5%BE%A1%E6%96%B9%E6%A1%88/
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2015-05-07 10:40
厂商回复:
非常感谢反馈 我们在解决中
最新状态:
暂无